All posts tagged "ransomware"
-

 3.2KVulnerabilities
3.2KVulnerabilitiesHackers Actively Exploiting Cisco AnyConnect and GIGABYTE Drivers Vulnerabilities
Cisco has warned of active exploitation attempts targeting a pair of two-year-old security flaws in the Cisco AnyConnect Secure Mobility Client for...
-
 897Malware
897MalwareHive Ransomware Hackers Begin Leaking Data Stolen from Tata Power Energy Company
The Hive ransomware-as-a-service (RaaS) group has claimed responsibility for a cyber attack against Tata Power that was disclosed by the company less...
-

 1.2KMalware
1.2KMalwareOldGremlin Ransomware Targeted Over a Dozen Russian Entities in Multi-Million Scheme
A Russian-speaking ransomware group dubbed OldGremlin has been attributed to 16 malicious campaigns aimed at entities operating in the transcontinental Eurasian nation...
-

 3.1KMalware
3.1KMalwareBlack Basta Ransomware Hackers Infiltrate Networks via Qakbot to Deploy Brute Ratel C4
The threat actors behind the Black Basta ransomware family have been observed using the Qakbot trojan to deploy the Brute Ratel C4...
-

 3.1KMalware
3.1KMalwareNew Prestige Ransomware Targeting Polish and Ukrainian Organizations
A new ransomware campaign targeted the transportation and logistics sectors in Ukraine and Poland on October 11 with a previously unknown payload...
-

 1.4KMalware
1.4KMalwareNew Report Uncovers Emotet’s Delivery and Evasion Techniques Used in Recent Attacks
Threat actors associated with the notorious Emotet malware are continually shifting their tactics and command-and-control (C2) infrastructure to escape detection, according to...
-

 1.0KMalware
1.0KMalwareBlackByte Ransomware Abuses Vulnerable Windows Driver to Disable Security Solutions
In yet another case of bring your own vulnerable driver (BYOVD) attack, the operators of the BlackByte ransomware are leveraging a flaw...
-
 2.8KMalware
2.8KMalwareBlackCat Ransomware Gang Claims to Have Hacked US Department of Defense Contractor
NJVC has been added to the victim list of the BlackCat (ALPHV) ransomware gang. NJVC provides IT support to the US government’s...
-

 4.9KMalware
4.9KMalwareBlackCat Ransomware Attackers Spotted Fine-Tuning Their Malware Arsenal
The BlackCat ransomware crew has been spotted fine-tuning their malware arsenal to fly under the radar and expand their reach. “Among some...
-

 2.5KMalware
2.5KMalwareEuropol and Bitdefender Release Free Decryptor for LockerGoga Ransomware
A decryptor for the LockerGoga ransomware has been made available by Romanian cybersecurity firm Bitdefender in collaboration with Europol, the No More...
-
 3.2KMalware
3.2KMalwareLorenz Ransomware Exploit Mitel VoIP Systems to Breach Business Networks
The operators behind the Lornenz ransomware operation have been observed exploiting a now-patched critical security flaw in Mitel MiVoice Connect to obtain...
-

 1.8KMalware
1.8KMalwareQNAP Warns of New DeadBolt Ransomware Attacks Exploiting Photo Station Flaw
QNAP has issued a new advisory urging users of its network-attached storage (NAS) devices to upgrade to the latest version of Photo...
-

 3.3KMalware
3.3KMalwareResearchers Detail Emerging Cross-Platform BianLian Ransomware Attacks
The operators of the emerging cross-platform BianLian ransomware have increased their command-and-control (C2) infrastructure this month, a development that alludes to an...
-
 744Malware
744MalwareNew Golang-based ‘Agenda Ransomware’ Can Be Customized For Each Victim
A new ransomware strain written in Golang dubbed “Agenda” has been spotted in the wild, targeting healthcare and education entities in Indonesia,...
-

 1.0KMalware
1.0KMalwareCybercrime Groups Increasingly Adopting Sliver Command-and-Control Framework
Nation-state threat actors are increasingly adopting and integrating the Sliver command-and-control (C2) framework in their intrusion campaigns as a replacement for Cobalt...
-

 3.0KCyber Attack
3.0KCyber AttackThe Rise of Data Exfiltration and Why It Is a Greater Risk Than Ransomware
Ransomware is the de facto threat organizations have faced over the past few years. Threat actors were making easy money by exploiting...
-
 619Malware
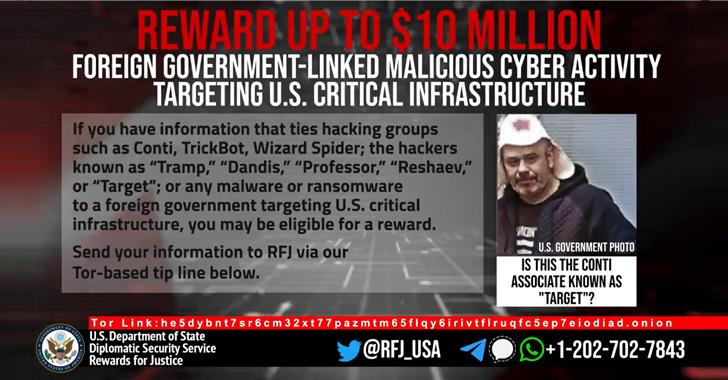
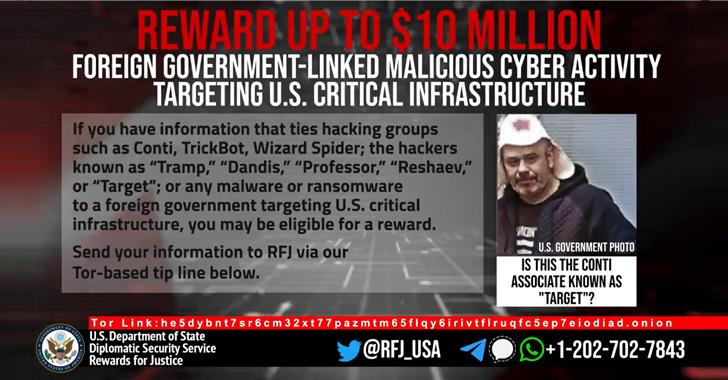
619MalwareU.S. Government Offers $10 Million Reward for Information on Conti Ransomware Gang
The U.S. State Department on Thursday announced a $10 million reward for information related to five individuals associated with the Conti ransomware...
-

 4.3KMalware
4.3KMalwareConti Cybercrime Cartel Using ‘BazarCall’ Phishing Attacks as Initial Attack Vector
A trio of offshoots from the notorious Conti cybercrime cartel have resorted to the technique of call-back phishing as an initial access...
-

 3.6KMalware
3.6KMalwareCisco Confirms It’s Been Hacked by Yanluowang Ransomware Gang
Networking equipment major Cisco on Wednesday confirmed it was the victim of a cyberattack on May 24, 2022 after the attackers got...
-
 635Malware
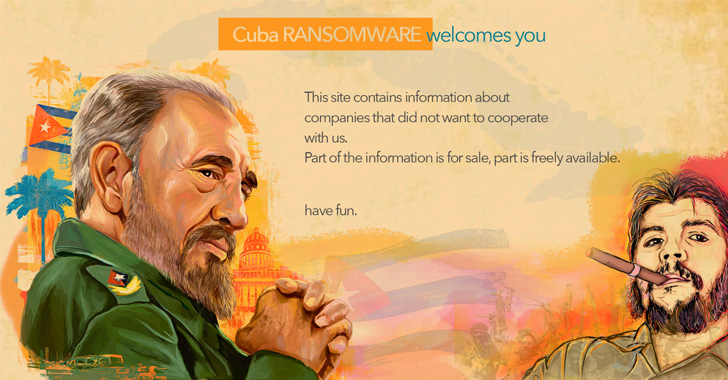
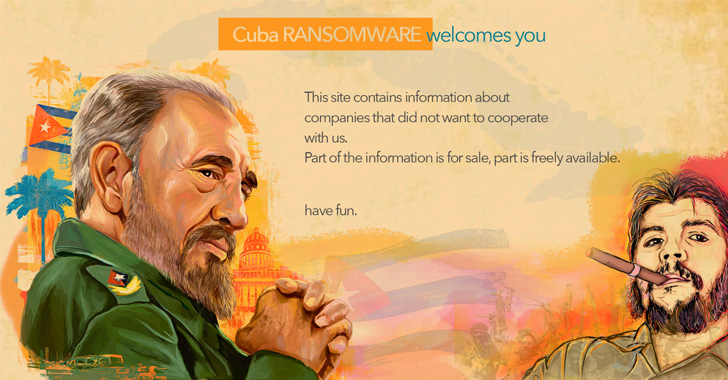
635MalwareHackers Behind Cuba Ransomware Attacks Using New RAT Malware
Threat actors associated with the Cuba ransomware have been linked to previously undocumented tactics, techniques and procedures (TTPs), including a new remote...
-

 3.4KMalware
3.4KMalwareWhat is ransomware and how can you defend your business from it?
Ransomware is a kind of malware used by cybercriminals to stop users from accessing their systems or files; the cybercriminals then threaten...






