All posts tagged "Security"
-
 4.8KSurveillance
4.8KSurveillanceFacebook to end facial recognition and delete billions of records
Facebook has announced that it will shut down its Facial Recognition System and delete the templates of over 1 billion people stored...
-

 5.1KData Security
5.1KData SecurityResearcher found 70% Wi-Fi networks in Tel Aviv are hackable
While examining Wi-Fi networks in Tel Aviv, Israel, 70% or around three-quarters of home and small-scale office Wi-Fi network passwords were vulnerable...
-

 4.7KData Security
4.7KData SecurityTrojan Source attack lets hackers exploit source code
Trojan Source attack impacts all popular programming language compilers, such as C, C++, C#, Java, JavaScript, Python, Rust, and Go. A research...
-

 1.4KHow To
1.4KHow To10 Free and Best OSINT Tools 2021
OSINT or Open source intelligence refers to information about businesses or people that can be collected from online sources. However, it requires...
-

 2.9KCyber Crime
2.9KCyber CrimeNew malware lures fake Chrome update to attack Windows PCs
The prime target of this malware campaign is unsuspecting users on Windows 10. Rapid7 Managed Detection and Response team has shared details...
-

 392Geek
392GeekFacebook sues Ukrainian man for scraping and selling 178m users’ data
Facebook tracked down the programmer after he mistakenly used his contact information on email and job portals. On October 21, 2021, Facebook...
-
 5.0KData Security
5.0KData SecurityNew Linux kernel memory corruption bug causes full system compromise
Researchers dubbed it a “straightforward Linux kernel locking bug” that they exploited against Debian Buster’s 4.19.0.13-amd64 kernel. In 2017, MacAfee researchers disclosed a...
-
 1.5KData Security
1.5KData SecurityWinRAR vulnerability allowed attackers to remotely hijack systems
The vulnerability in WinRAR trialware could be abused by a remote attacker for executing arbitrary code on any system thus, getting an...
-
 2.2KData Security
2.2KData SecurityGoogle details cookie stealer malware campaign targeting YouTubers
Google attributed the malware campaign to a group of attackers recruited via a Russian-language hacker forum. Google has disclosed details of a...
-

 4.7KHow To
4.7KHow ToHow to fix iPhone boot loop and iPhone black screen by yourself
iPhone boot loop has become more prominent following the recent iOS upgrades. Worse, you might even experience an iPhone black screen –...
-

 696Cyber Crime
696Cyber CrimeDDoS booter customers received warning letters by Dutch police
Apparently, the individuals who received the warning were identified as suspects and will be prosecuted for a cyber offense if they continue...
-

 4.8KCyber Crime
4.8KCyber CrimeHow using the purple team approach helps in addressing cybercrime
Automated purple teaming is one of the best ways to address cybercrime as it does not only test for the deficiencies in...
-

 4.2KSurveillance
4.2KSurveillanceWhat is a data breach & how to prevent one?
What is a data breach? A data breach is a security lapse where a non-authorized person can assess sensitive information without authorization....
-
 4.6KNews
4.6KNewsiPhone 13 Pro, Windows, Chrome, Linux and others pwned at Tianfu Cup
Tianfu Cup is the Chinese version of the Pwn2own in which hackers from Kunlun Lab managed to secure first place by hacking...
-
 1.9KData Security
1.9KData SecurityAmnesty Intl. accuses Indian cyber security firm of spyware attacks
According to Amnesty International, it found evidence that attackers testing the spyware were using the IP address of Indian cyber security firm...
-
 403Data Security
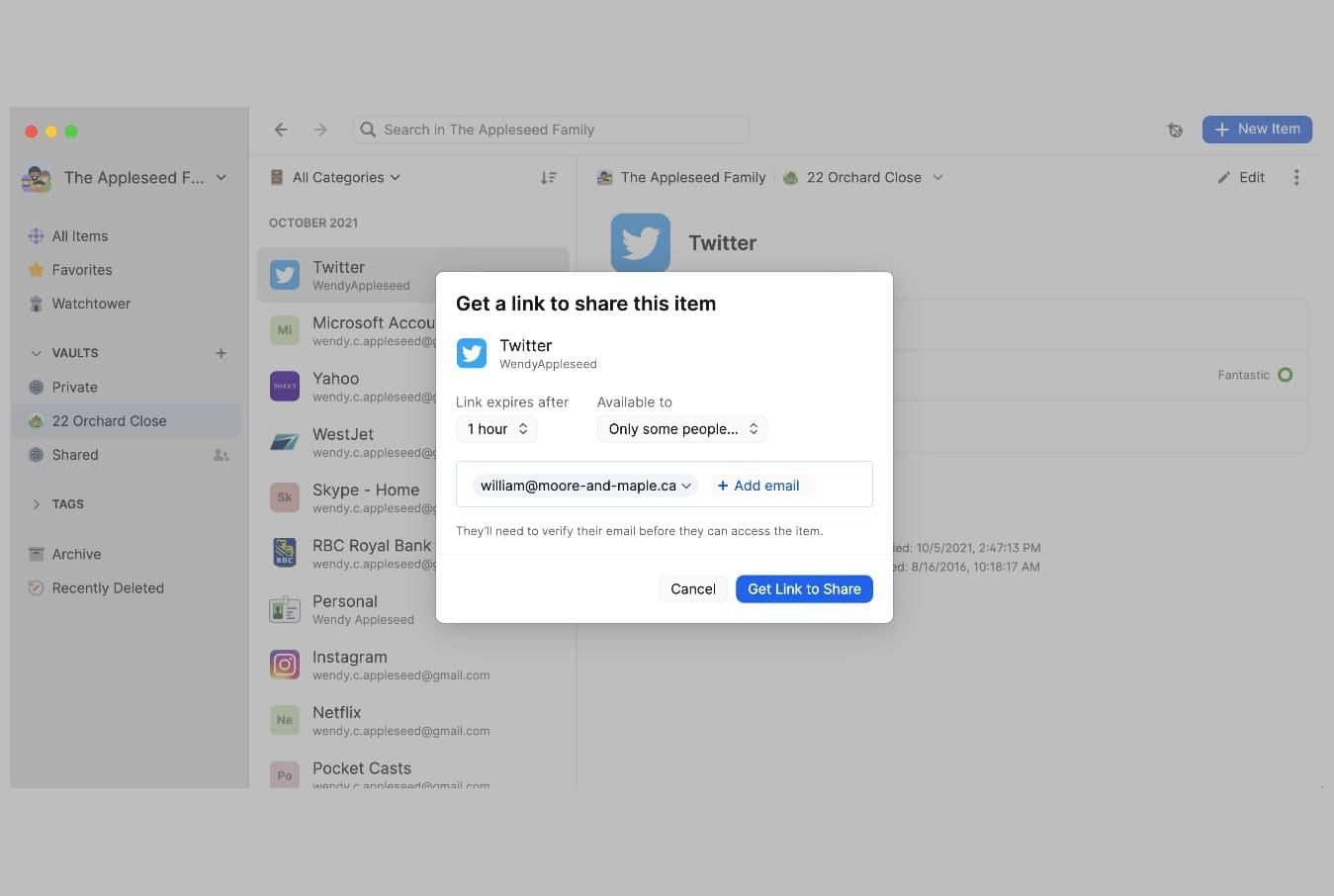
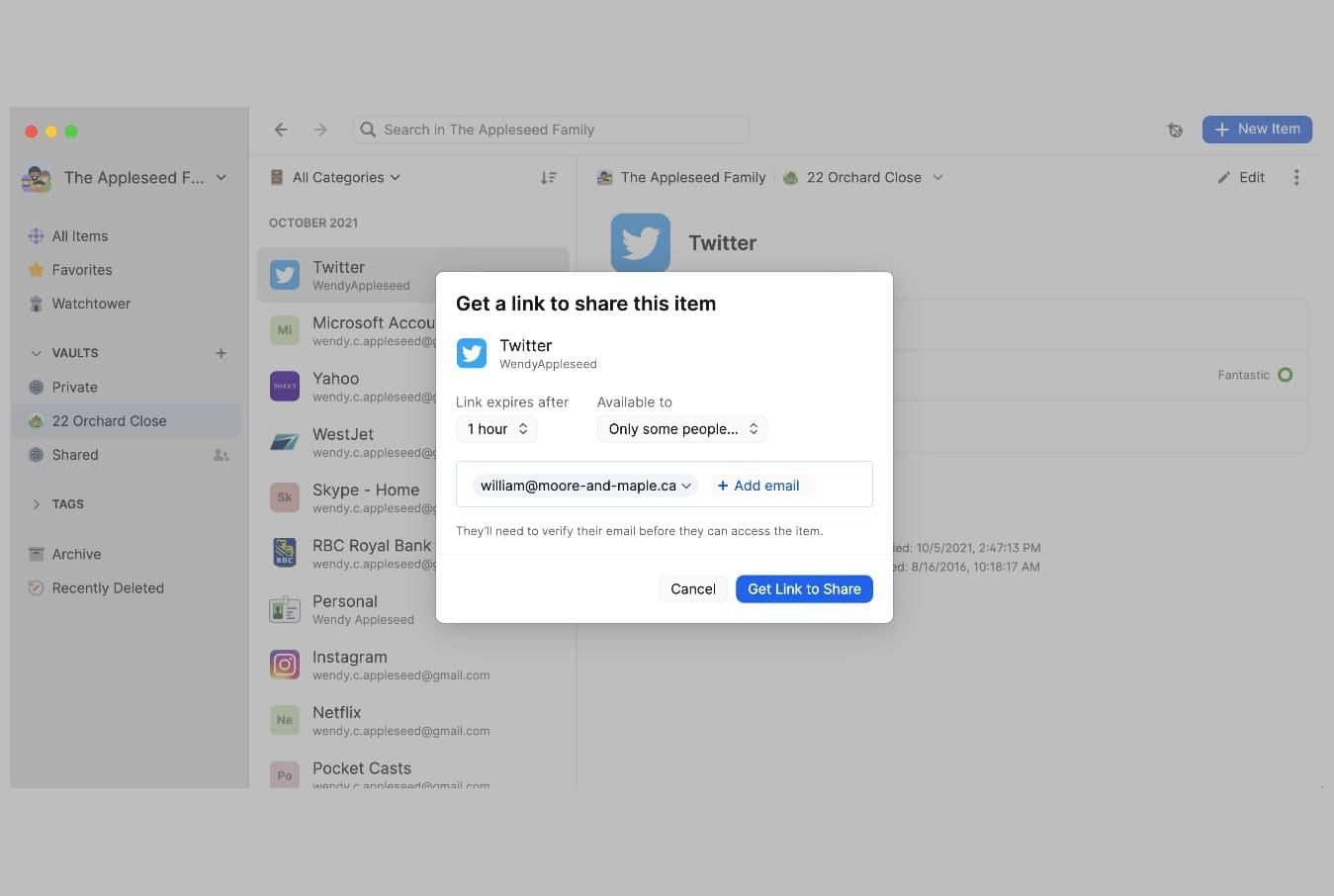
403Data SecurityPsst! tool by 1Password lets users share passwords using a link
1Password password manager has introduced a new tool called Password Secure Sharing Tool or Psst! that lets users share their passwords or...
-

 477Data Security
477Data SecurityOpenSea vulnerability allowed crypto stealing with malicious NFTs
Researchers investigated the issue in OpenSea after an increase in complaints about receiving and opening free airdropped NFTs to steal user funds....
-

 5.0KCyber Crime
5.0KCyber CrimeEx-army admin jailed for 12 years over US military health data theft
Frederick Brown, a medical data technician & administrator associated with the 65th Medical Brigade of the US Army caused millions of dollars...
-

 4.4KCyber Crime
4.4KCyber CrimeWhite House Dark Web Marketplace Shuts Down its Operations
The White House Dark Web Marketplace says “We are retiring!” The White House Dark Web marketplace will cease to exist as the...
-

 2.9KHow To
2.9KHow ToHow Can You Use A VPN On Netflix?
To watch Netflix securely and unlock its international catalog, you just need a reliable VPN – Let’s dig deeper. Netflix is one...
-

 735News
735NewsTwitch hacked- Source code and Streamer payment figures leaked
Twitch has undergone a massive hack resulting in leaking the source code for its unreleased streaming service, creator payout details, and other...






