All posts tagged "Security"
-
 3.0KNews
3.0KNewsTelecom giant behind routing SMS discloses 5-year-long data breach
Syniverse, the targeted telecom firm, works with carriers like T-Mobile, Verizon, Twilio, and AT&T in routing SMS text messages exchanged between them...
-
 3.4KNews
3.4KNewsTwitch data breach resulted from server configuration error
Twitch Data Breach took place a couple of days ago when an anonymous hacker published a torrent file with 125 GB worth...
-

 1.4KData Security
1.4KData SecurityGriftHorse Android malware hit 10 million devices in 70 countries
GriftHorse malware uses malicious apps to subscribe victims to premium services that cost them $42 (£30 –€36) per month. The IT security...
-

 1.5KData Security
1.5KData SecurityApple AirTags can be used as trojan for credential hacking
According to security researcher Bobby Raunch, the attack exploits the way Lost Mode of AirTags is set up. Although Apple’s Bluetooth-enabled item...
-
 1.7KData Security
1.7KData SecurityHackers exploit 2FA flaw to steal crypto from 6,000 Coinbase users
Coinbase is working to reimburse the customers for the funds they have lost and help them regain control of their accounts. Coinbase...
-
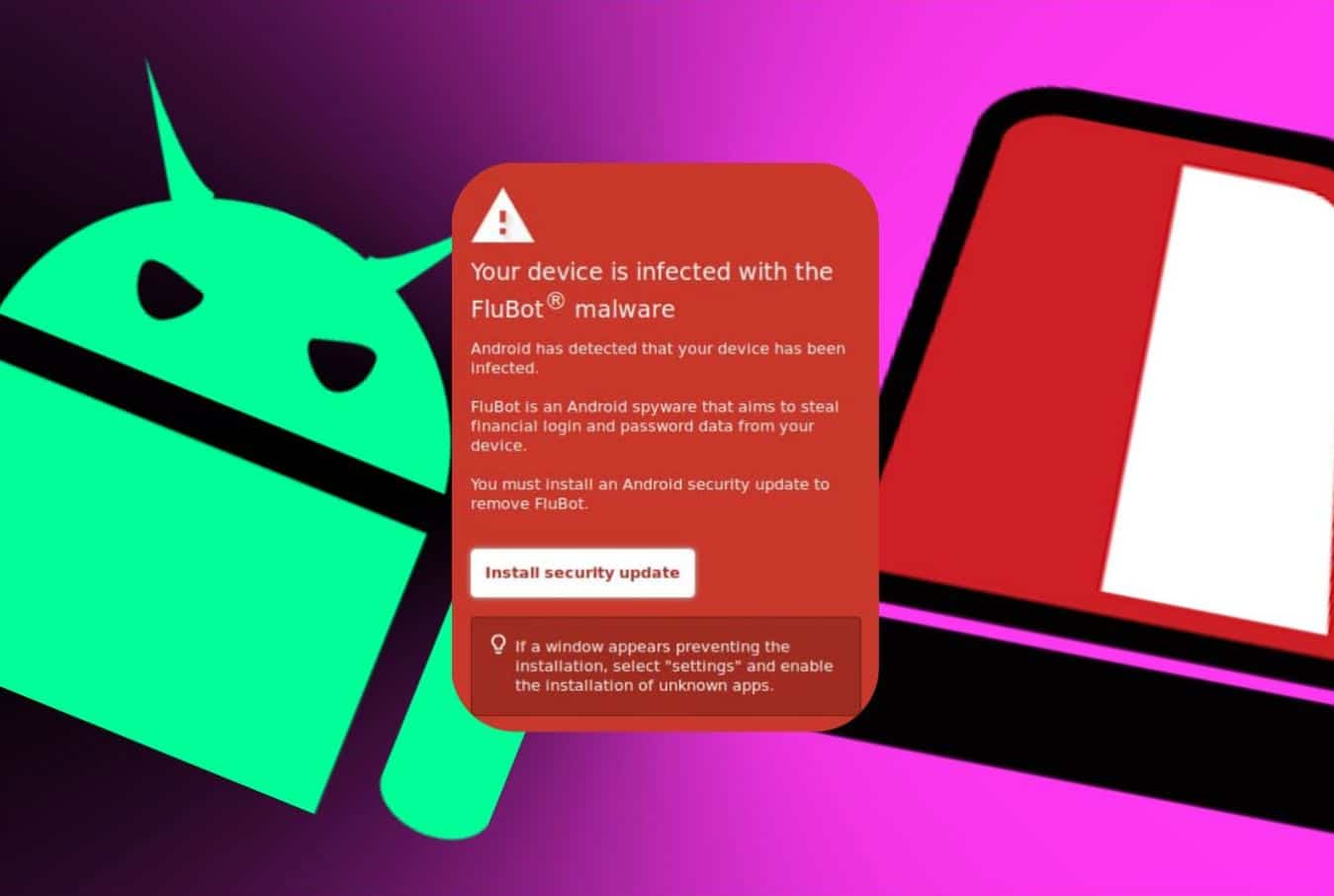
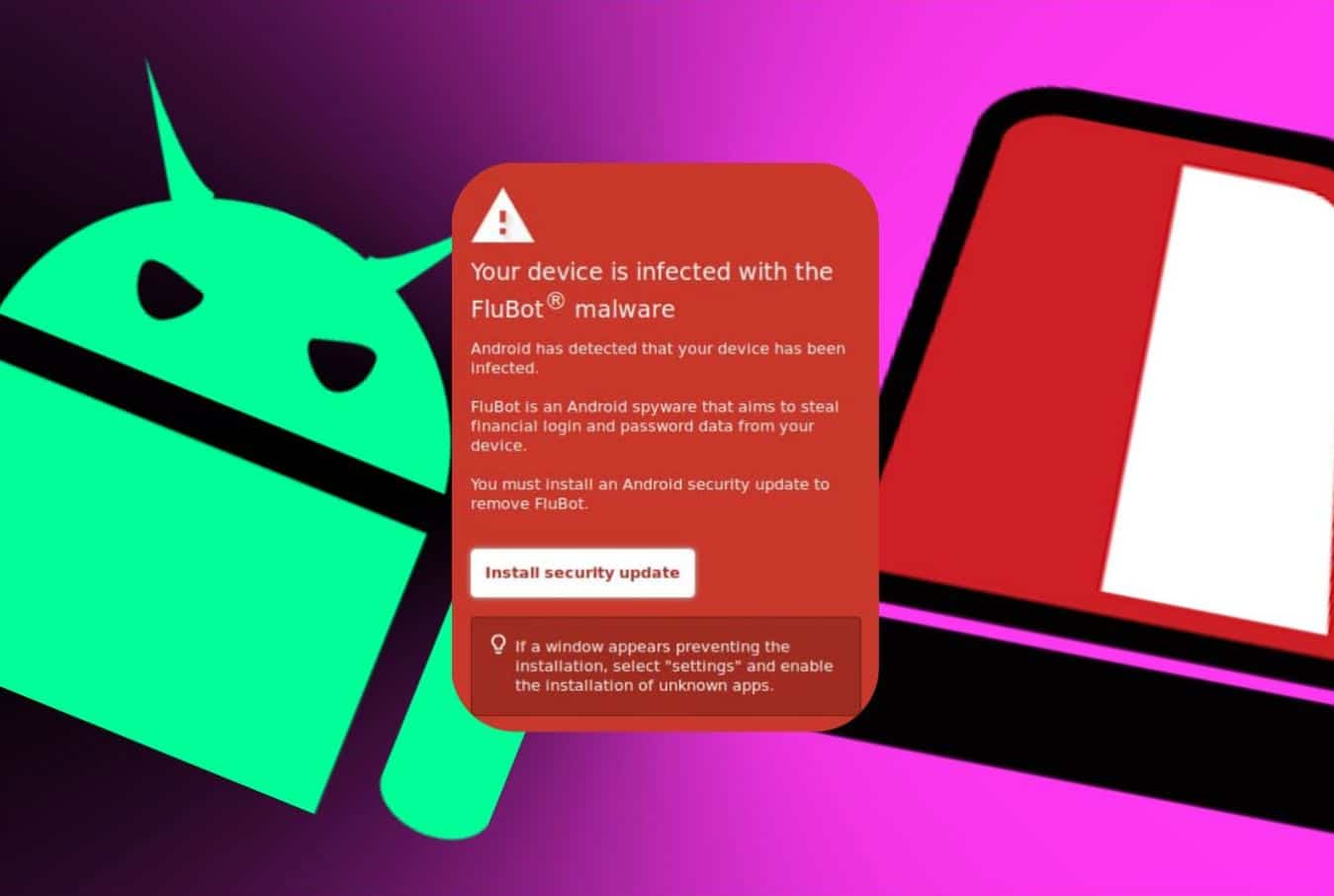 917Data Security
917Data SecurityAndroid flubot malware installs itself by faking security update
The security update is obviously phony but looks authentic that can deceive users into installing Flubot malware on their devices. New Zealand’s...
-

 5.0KData Security
5.0KData SecurityCybersecurity risk assessment: Does Your Company Need It?
Cyber security risk assessments are a framework for detecting, analyzing, and prioritizing operational risk – Let’s dig deeper into why your company...
-

 4.1KHow To
4.1KHow ToSecurity tips – How to protect your online trading account
According to a report from The Economic Times India, cybercriminals are targeting stock markets. Their modus operandi includes selling penny stocks from their...
-
 4.6KCyber Events
4.6KCyber EventsBandwidth.com is latest victim of nonstop DDoS attacks against VoIP
Bandwidth.com has been suffering DDoS attacks for the past 3 days nonstop. Bandwidth.com is the newest victim of DDoS attacks, explicitly targeting...
-
 2.0KGeek
2.0KGeekChoosing a web hosting service that’s right for your business
With a web hosting service, a small business can focus on what its website should look like, what information it wants to...
-

 5.2KCyber Crime
5.2KCyber CrimeHackers hit Russian ministry, rocket center using MSHTML vulnerability
Microsoft Office zero-day also dubbed MSHTML attack exploited to target Russian government including Interior ministry and State Rocket Center. Malwarebytes Intelligence team reports that...
-
 5.3KGeek
5.3KGeekUrgent Chrome security update released to patch widely exploited 0-day
The vulnerability (CVE-2021-37973) impacts 2 Billion Chrome users worldwide therefore update your browser right now to the latest version. On Friday 24th,...
-

 3.2KSurveillance
3.2KSurveillanceLithuania wants users to dump Chinese phones citing data collection
Lithuania’s Defense Ministry has released a warning, urging consumers to get rid of their Chinese phones and not to buy new ones....
-
 4.6KData Security
4.6KData SecurityDangers of DNS poisoning and how to prevent it
The cyberworld is constantly evolving, and with evolution comes new methods of committing crimes. DNS poisoning is one such threat that might...
-
 5.2KData Security
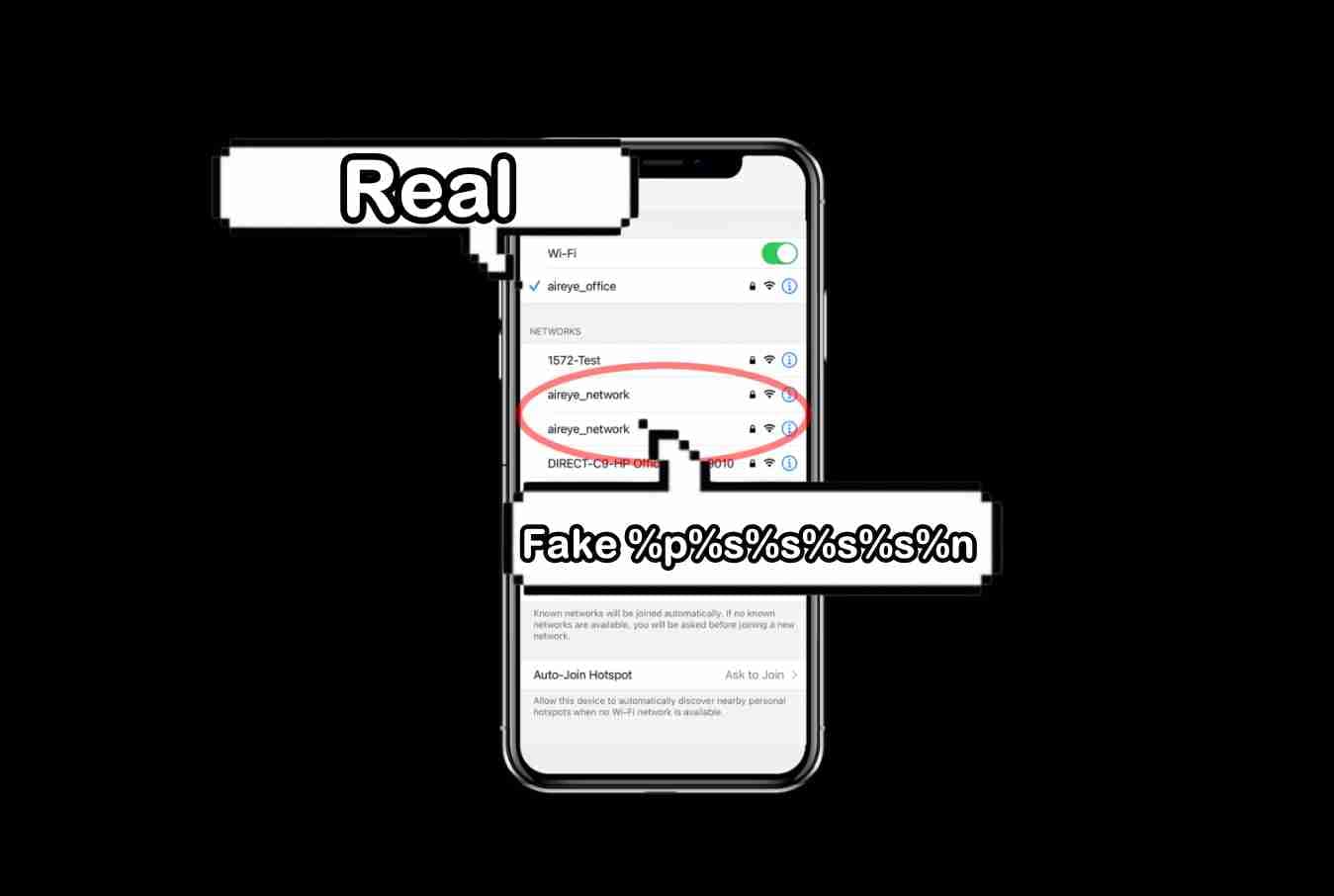
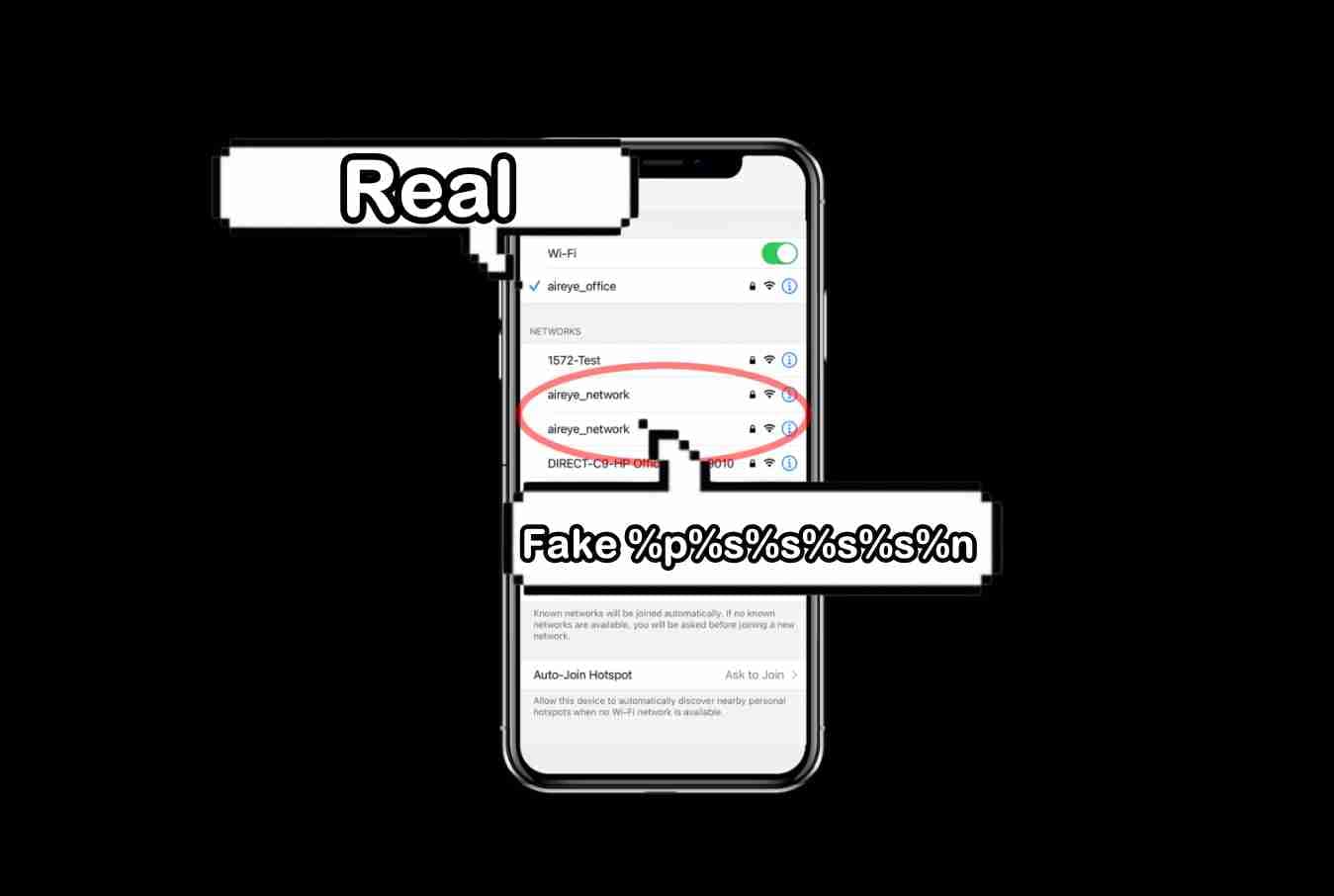
5.2KData SecuritySSID Stripping flaw lets hackers mimic real wireless access points
SSID Stripping has emerged as a significant threat because it impacts almost all software platforms, including MS Windows, macOS, Apple iOS, Ubuntu,...
-
 1.4KData Security
1.4KData SecurityFake TeamViewer download ads distributing new ZLoader variant
The infection chain starts when the victim clicks on an ad from Google on the search results page. SentinelLabs researchers have identified a...
-
 959Cyber Events
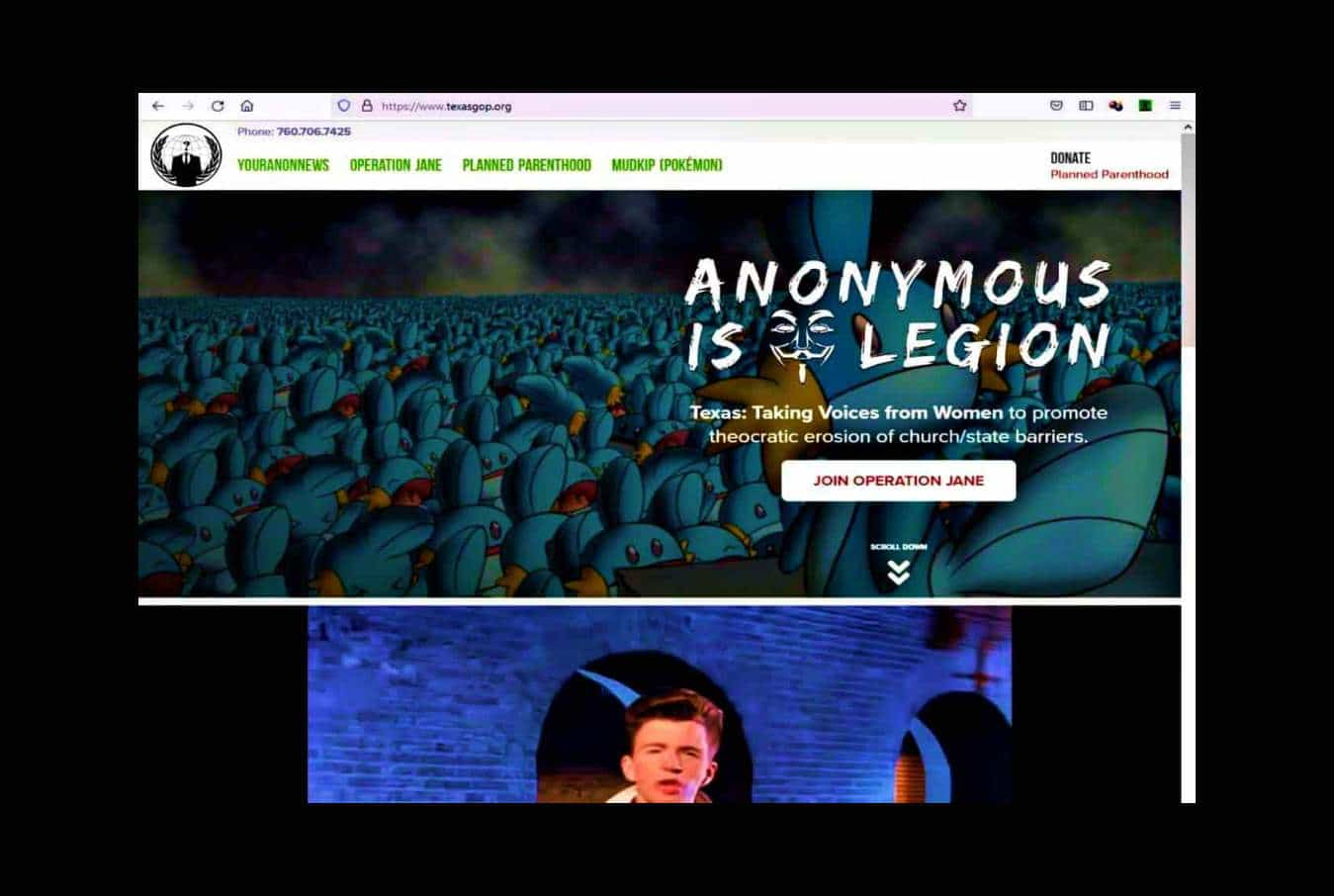
959Cyber EventsAnonymous hacks Texas Republican Party website against abortion law
The Texas Republican Party is now asking for donations to secure its website from further attacks from Anonymous and “Pro-abortion activists.” The...
-
 4.0KData Security
4.0KData SecurityDownload Kali Linux 2021.3 with Kali NetHunter on smartwatch, new tools
Kali Linux 2021.3, comes with a range of new pentest tools, improved virtualization support, and a brand-new OpenSSL configuration to enhance the...
-
 3.4KHow To
3.4KHow ToHow to use VPN to access blocked websites?
Governments and regimes across the globe use censorship as a tool to control the flow of information. This article highlights how one...
-

 2.2KCyber Crime
2.2KCyber CrimeVirginia National Guard suffers cyberattack as Marketo leaks data
Email accounts linked with Virginia National Guard were targeted in the cyberattack. According to details shared by the representative of the chief...
-
 1.3KNews
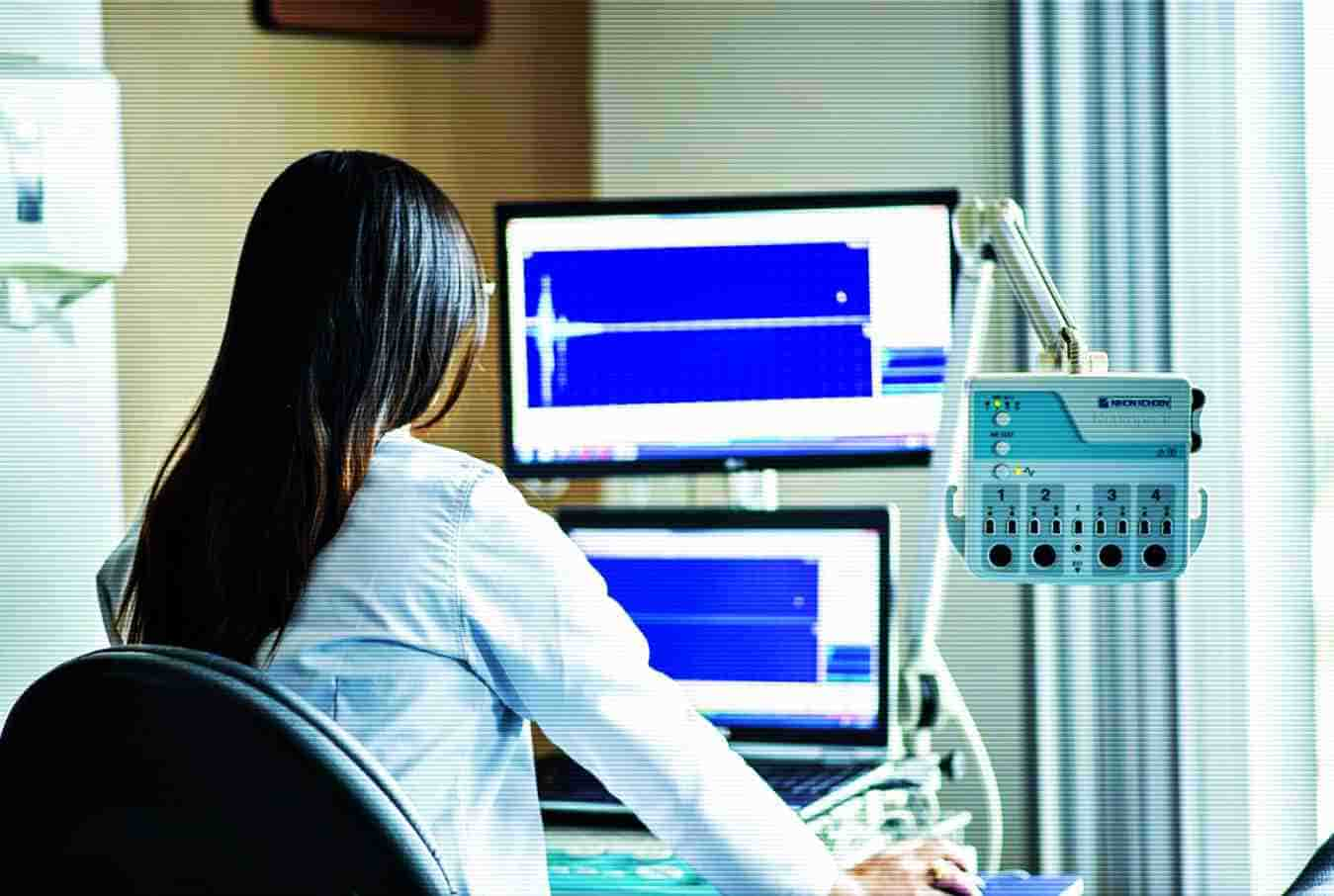
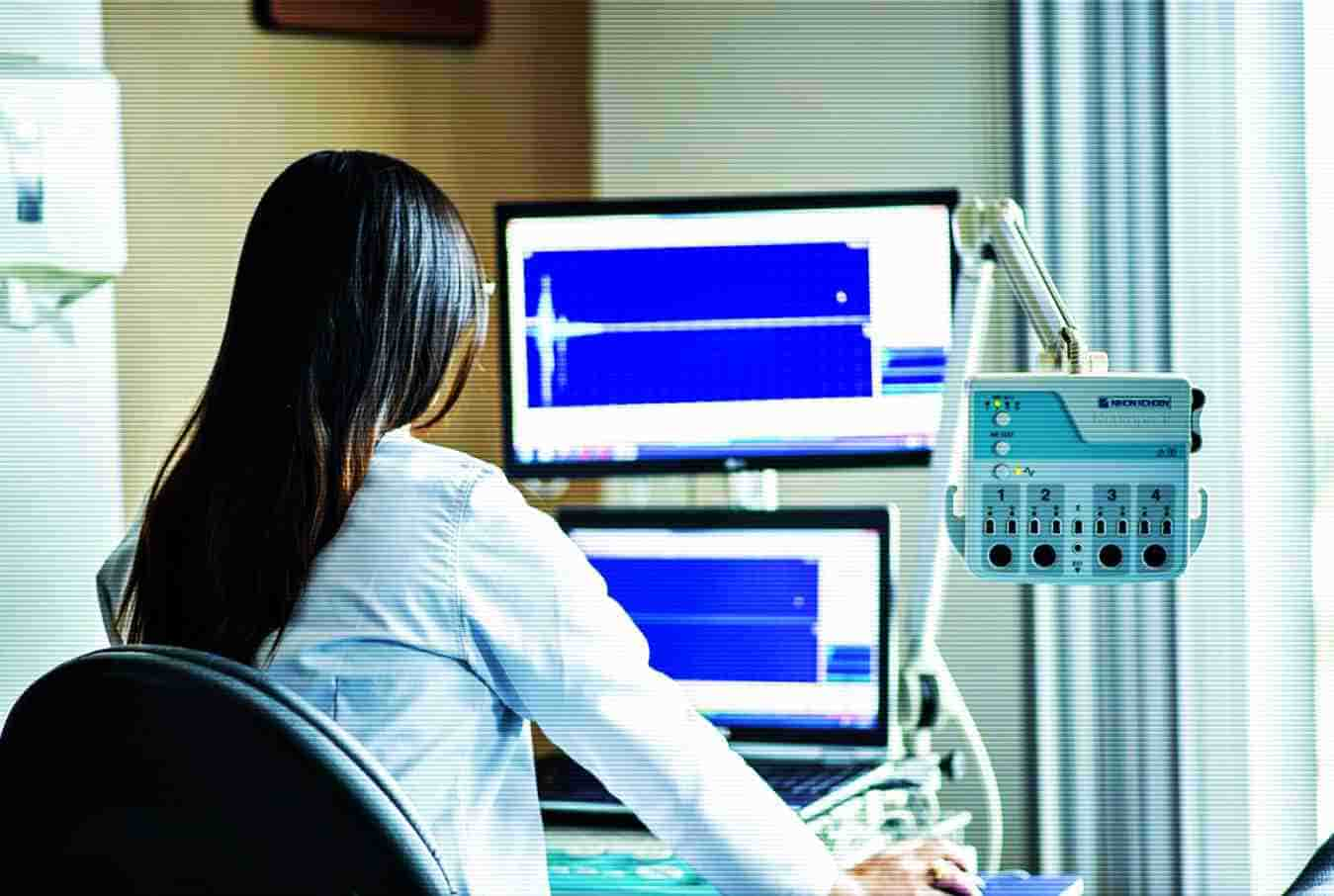
1.3KNewsShared clinical workstation security and access
The shared clinical workstations in the healthcare sector are often chaotic and messy. They are used by physicians for nearly everything, from...






