All posts tagged "Security"
-

 197News
197NewsPro-Palestinian Hackers Took over Twitter Account of Israeli Ha’aretz Newspaper
Pro-Palestine activists Hacked Ha’aretz Newspaper’s Twitter Account and Posted: “Our martyrs’ mothers will drink your soldier’s blood.” The Twitter feed of Israeli...
-

 173Hacked
173HackedBaidu’s Corrupt SDK Puts 100 Million Android Users Open To Backdoor Attacks
Short Bytes: Baidu, the Chinese analogous to Google has distributed a software development kit (SDK), Moplus, which has reportedly made over 100...
-

 315Hacked
315HackedAndroid Malware Hides as MS Word File, Sends Data To Hacker
Short Bytes: Attackers are now using an android malware app which camouflages itself as a Microsoft Word document. The malware once triggered, scans...
-

 195Hacked
195HackedNow Chat Anonymously with Tor Instant Messenger
Short Bytes: The Tor Project has announced the release of the beta version of its Tor Messenger that allows you to chat...
-

 196Geek
196GeekFacebook, WhatsApp Users can be tracked down by hackers
A group of researchers have demonstrated how locations of Facebook and WhatsApp users can be exposed by a security flaw in 4G networks....
-

 197Hacked
197HackedGermany Suspects, Will Investigate Google and Facebook Over Data Transfers
Short Bytes: The European Union has many a times been apprehensive of the US-based tech companies, especially on the matters of privacy and...
-
 202Hacked
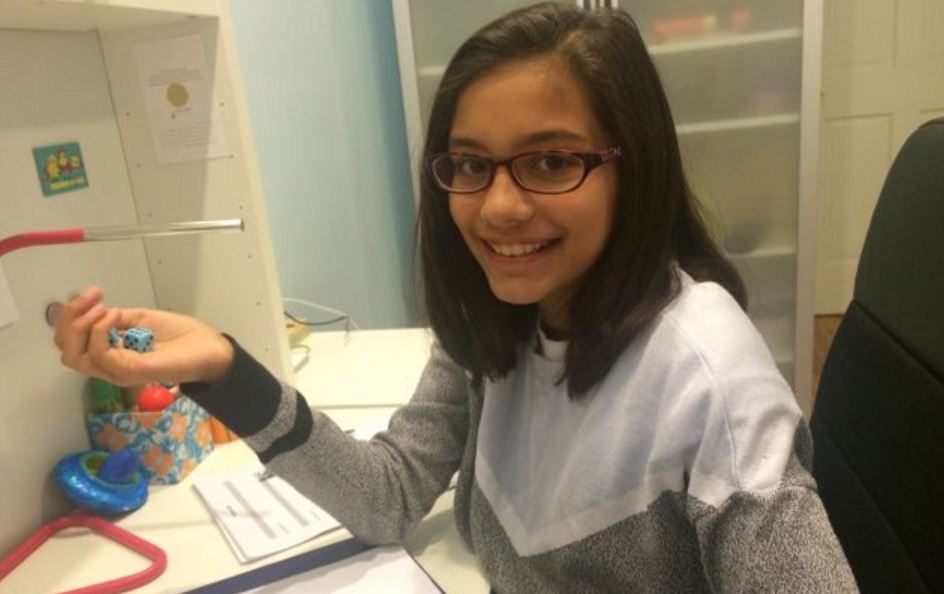
202HackedThis 11-year-old Girl is Selling Super Secure Passwords for $2 Each
Short Bytes: Mira Modi, an 11-year-old girl, has started a business of selling cryptographically secure passwords for $2 each. She generated Diceware...
-
 324News
324NewsUK’s largest Telecom Group TalkTalk Hacked, 4 Million Users at Risk
TalkTalk (UK’s largest broadband and mobile phones service provider) has possibly faced one of the biggest breaches in the history of cyber...
-

 170Surveillance
170SurveillancePrivacy Advocates Launch Anonymous Calling App
For those who seek privacy while working online, you now have a solution in “Warble,” an Anonymous calling app for Android, iOS...
-

 228Hacked
228HackedAre You Under the Attack of CCTV Botnet?
Short Bytes: Internet of Things are constantly being targeted by attackers to get the better off of the companies or individuals. CCTV...
-
 174Geek
174GeekSecurity Agencies Eager to Get Hold of User Data: Microsoft’s Transparency Report
Microsoft announced the launch of a new transparency website in order to provide free access to the transparency reports published by the...
-
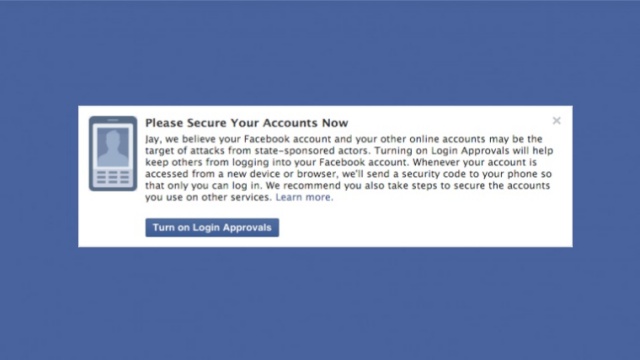
 134Geek
134GeekFacebook will notify you if the government is trying to get into your account
Facebook accounts are notorious for being hacked, either through poor passwords or phishing scams. So to help keep its users safe, the...
-

 262Hacked
262HackedYour Password Manager 1Password Leaks Your Account’s Important Metadata
Short Bytes: 1Password, a password manager feature has been found to leak traces of the user account’s metadata which could be exploited...
-
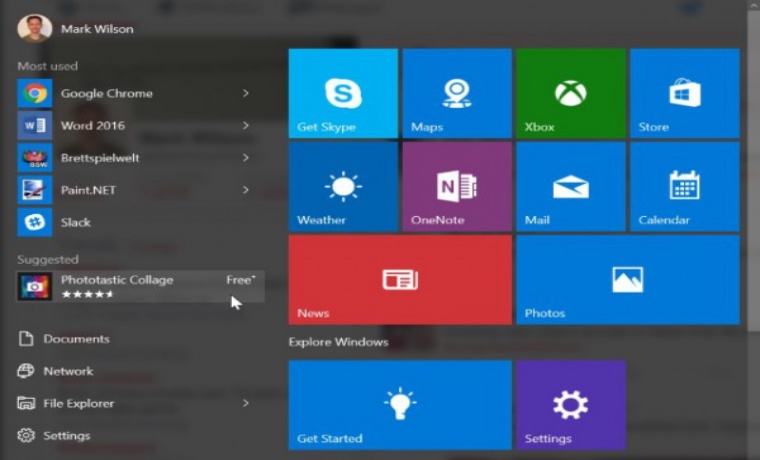
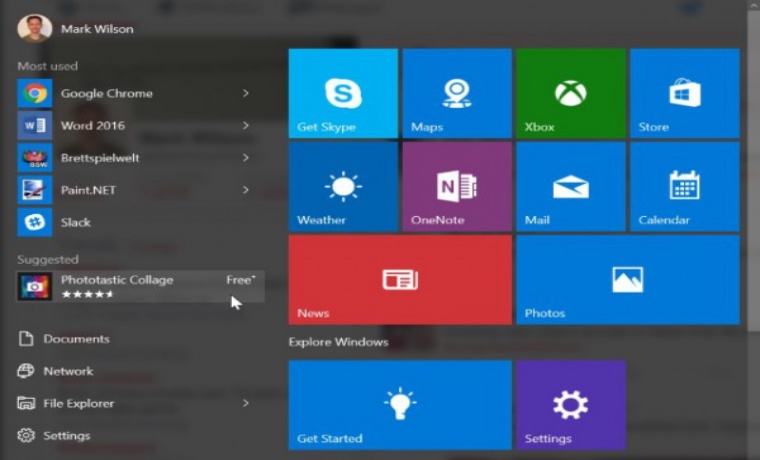 182Geek
182GeekWindows 10 Start Menu- Microsoft’s Chosen Platform for Displaying Online Ads
Microsoft’s Windows 10 is known for collecting personal data of its users, but who thought the firm will be forcefully displaying ads...
-
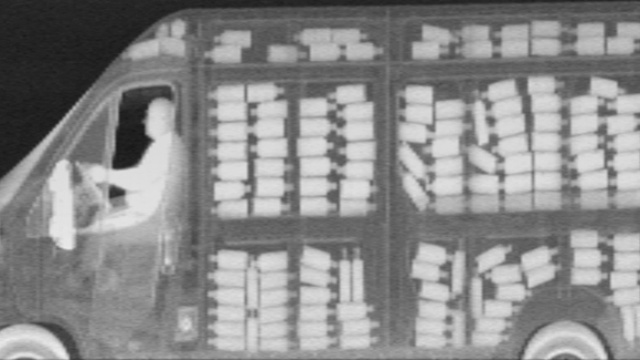
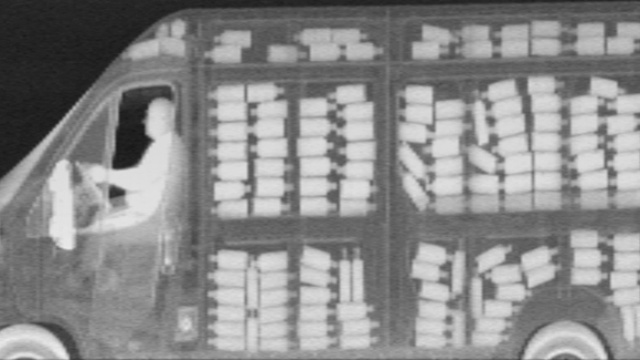 280Surveillance
280SurveillanceEverything in New York to be X-rayed as NYPD brings in X-ray vans
Extremely secretive spy vehicles equipped with X-ray facility, Z Backscatter, will now be seen patrolling the city streets — NYPD hasn’t disclosed...
-
 270Hacked
270HackedHere’s How Hackers Can Control Your Entire Digital Life in Minutes
Short Bytes: Continuing our “steps to effective security” series, we are here with a true story that tells about the basic security...
-
 252Hacked
252HackedCrypto Backdoor Isn’t The Only Way To Hack Into Your iPhone
Short Bytes: Crypto backdoor entry isn’t the only way for the cops to access your data. You think your iPhone is the...
-

 282Data Security
282Data SecurityHackers Can Steal Corporate Passwords Through Cisco’s WebVPN Service Backdoor
Researchers identified a flaw in Cisco’s WebVPN — Hackers managed to install backdoors via two methods on the service — This weakness...
-

 267News
267NewsSouth Korean subway system hacked, North Korea a possible culprit
The Subway system at the heart of Seoul, South Korea was hacked in 2014 and a local lawmaker claims that the culprit...
-

 181Data Security
181Data SecurityMeet The New Virus Protecting Routers From Hackers
For hackers, routers are an easy target, perhaps because they are seldom updated and virus-scanned and are also easily cracked. But shockingly,...
-

 290News
290NewsHackers show US Police Department Vehicles can be hacked
Security researchers Chris Valasek and Charlie Miller helped the world understand that late-model vehicles are vulnerable to cyber attacks. We have read...






