All posts tagged "SIEM"
-

 3.7KCyber Attack
3.7KCyber AttackDetecting the “Next” SolarWinds-Style Cyber Attack
The SolarWinds attack, which succeeded by utilizing the sunburst malware, shocked the cyber-security industry. This attack achieved persistence and was able to...
-

 353Infosec
353InfosecIntrusion Detection System (IDS) and Its Detailed Working Function – SOC/SIEM
Detection Methods An IDS can only detect an attack. It cannot prevent attacks. In contrast, an IPS prevents attacks by detecting them...
-

 250Hacked
250HackedSIEM: What is Security Information and Event Management?
Managing your IT infrastructure can be incredibly difficult. This is why we have centrally managed systems like Active Directory, VMware’s vSphere, and...
-
 349News
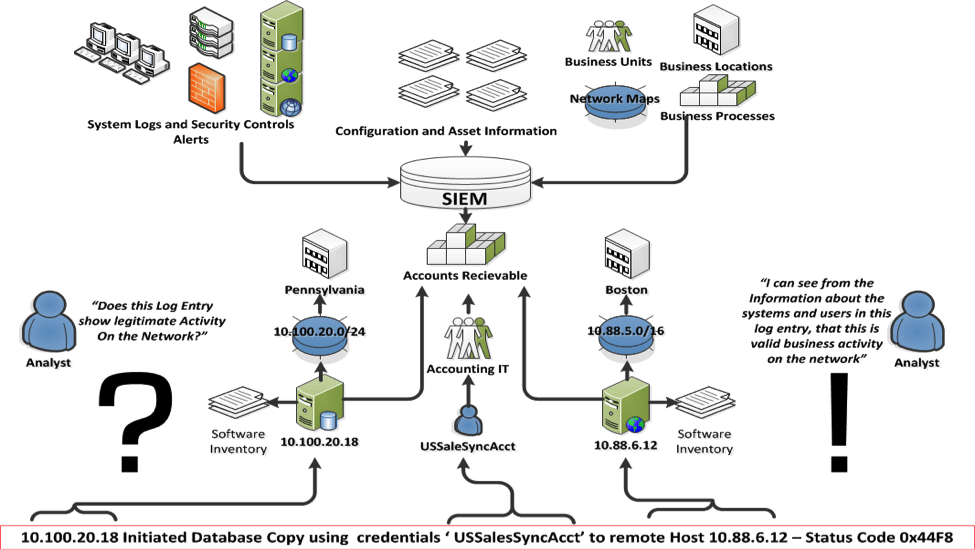
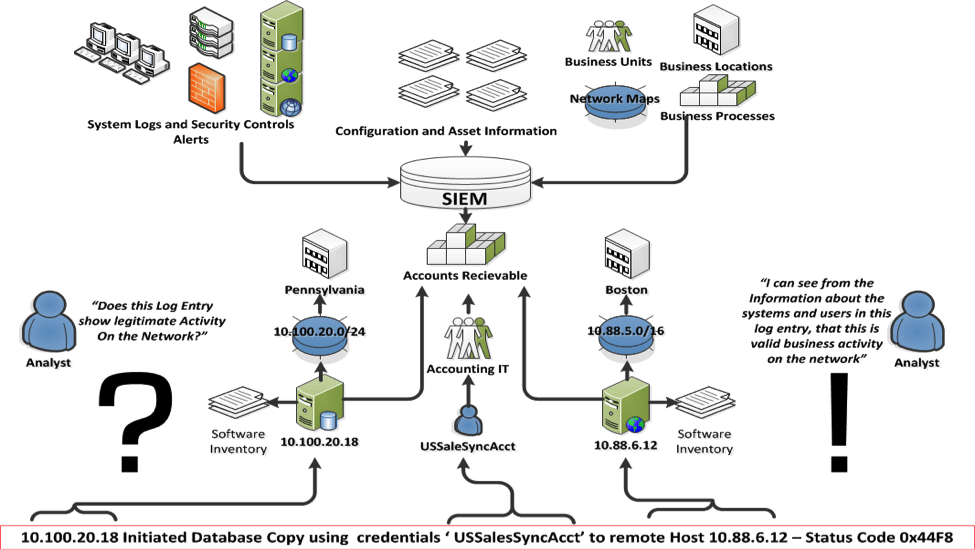
349NewsSecurity Information and Event Management (SIEM) – A Detailed Explanation
SIEM software products and services combine security information management (SIM) and security event management (SEM). They provide real-time analysis of security alerts...
-

 323Vulnerabilities
323VulnerabilitiesMultiple Vulnerabilities in IBM QRadar SIEM Allows Attackers to Escalate Privileges and to Execute Arbitrary Commands
Multiple Vulnerabilities found in IBM QRadar chained together allows a remote attacker to bypass authentication and to execute arbitrary commands with root...






