All posts tagged "SMB"
-
 459Malware
459MalwareOdix – An Enterprise-Grade File-Based Cyber Attack and Malware Protection to SMBs
Cybersecurity solutions provider odix has set its sights on bringing enterprise-grade cybersecurity to small to medium businesses (SMBs). The company specializes in...
-

 283News
283NewsIT Security Culture Evolution of Businesses Exposed
Security culture is the behavior in an organization that contributes to the protection of data, information, and knowledge, very useful today in...
-

 225News
225NewsWhy SMBs Need To Boost Their Cybersecurity
As data breaches and hacks of all kinds continue to happen on a daily basis, the trust of the internet users seems...
-
 336Malware
336MalwareNew Version of Trickbot Trojan Spread via Local SMB to Perform NetServer and LDAP Enumeration
A New version of Banking Trojan Trickbot Trojan “1000029″ Spreading Via new Module “worm64Dll” via Email Champaign that imitates as an invoice of...
-
 261Malware
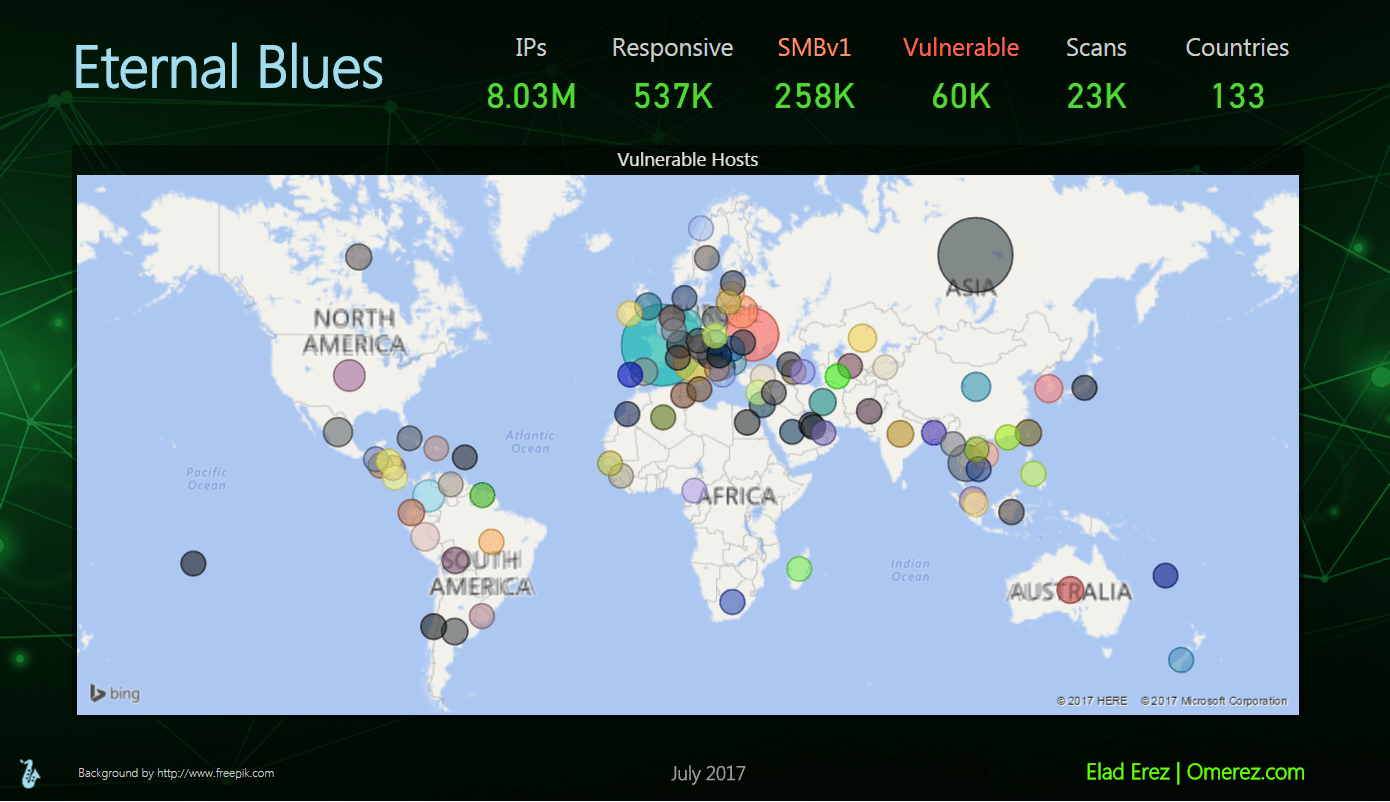
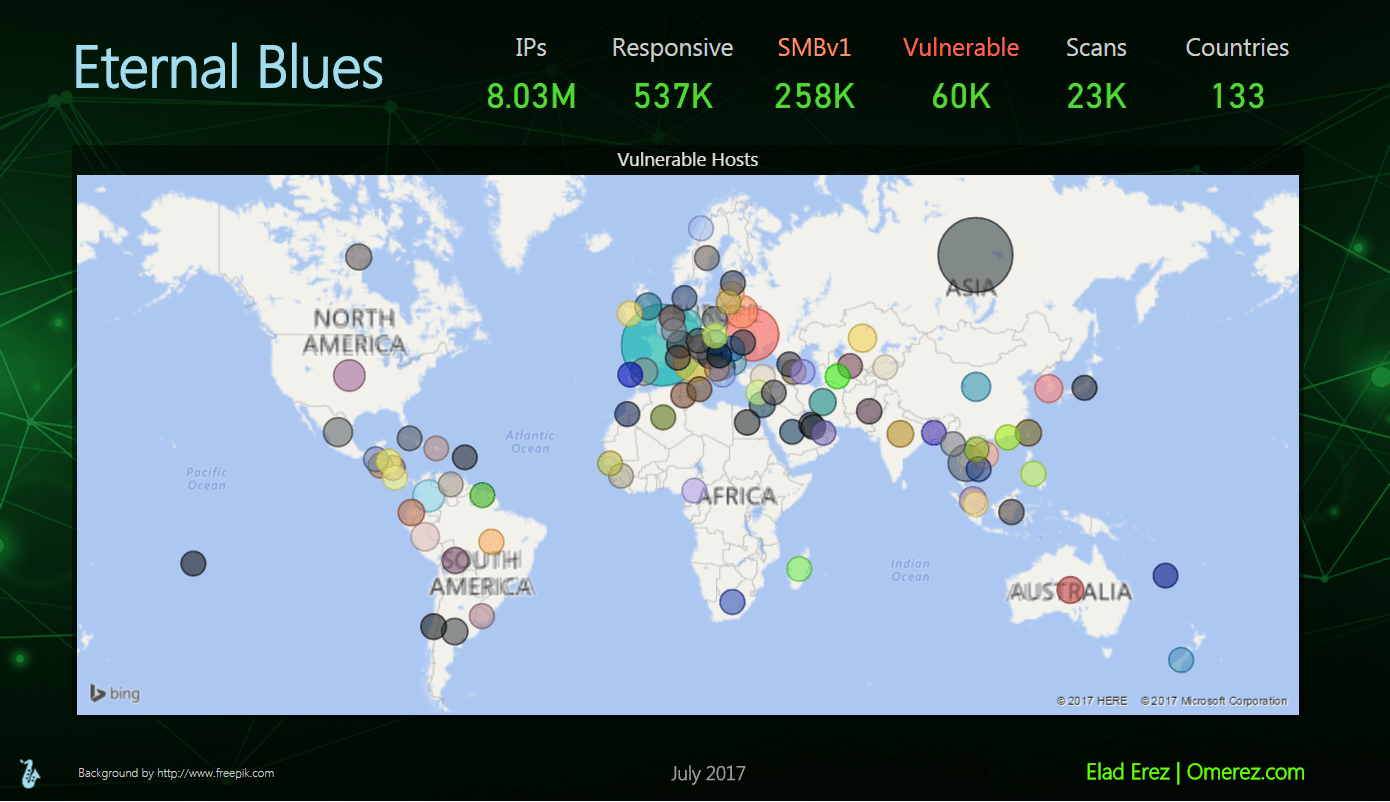
261MalwareStill More than 50,000 hosts are vulnerable to ETERNAL BLUE Exploit
Eternal Blues, a tool used in finding computers and Endpoints vulnerable to the NSA’s ETERNALBLUE exploit. All we need to do is...
-
 331Malware
331MalwareNew CIA Cyberweapon Malware “Pandemic” installed in Victims Machine and Replaced Target files where remote users use SMB to Download
One of the CIA Cyberweapon Called “Pandemic” Document Leaked by Vault 7 Projects of WikiLeaks.This Malware tool Specifically interact and run as...
-
 416Ransomware
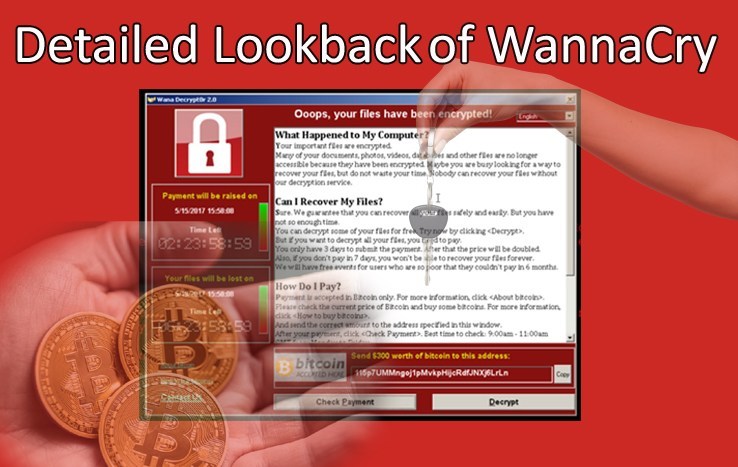
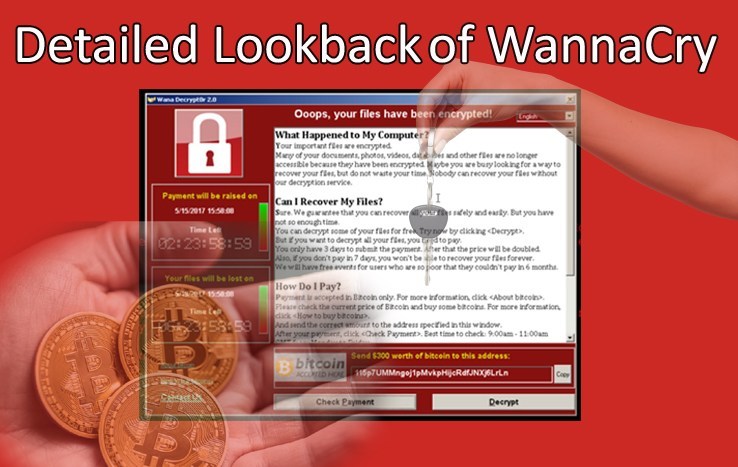
416RansomwareA complete Lookback of Historical Wannacry Ransomware Cyber Attack
Wannacry (WannaCrypt,WanaCrypt0r 2.0,Wanna Decryptor), A Computer Malware family called Ransomware that actually target the Microsoft Windows Operating systems SMB exploit leaked by...
-
How To
How to Scan for SMB vulnerabilities using Nmap
Hi there my fellow hackers, we are back with another tutorial. Today we will see how we can use a Nmap script...






