All posts tagged "Spoofing"
-
 458Mobile Security
458Mobile Security9 Android Zero-day Vulnerabilities Affects Billions of Android Devices – Hackers Perform DOS, RCE, Make, Deny & Spoof Calls
Exclusive research found 9 critical system-level Android VoIP Zero-day vulnerabilities that allow attackers to perform malicious operations, including denying voice calls, caller...
-

 234Incidents
234IncidentsHackers are spoofing police phone numbers to extort fine money from people
Authorities in the state of Delaware, US, have received multiple reports of fraudulent phone calls allegedly related to the State Police phone...
-
 256Network Tools
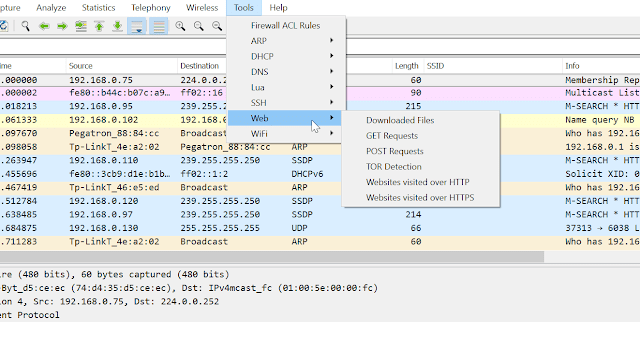
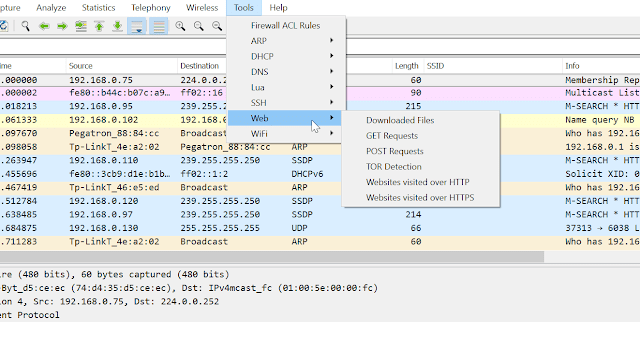
256Network ToolsPA Toolkit – A Collection Of Traffic Analysis Plugins Focused On Security
PA Toolkit is a collection of traffic analysis plugins to extend the functionality of Wireshark from a micro-analysis tool and protocol dissector...
-
 269Vulnerabilities
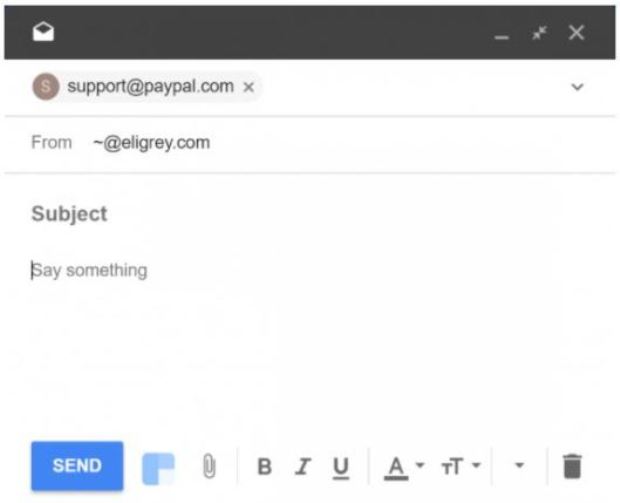
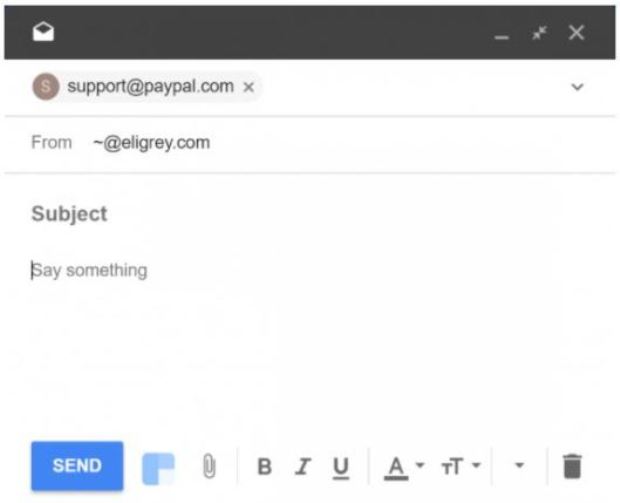
269VulnerabilitiesHack Google Inbox with a new Spoofing vulnerability
Almost a year ago, on May 4, 2017, information security researcher privately discovered and reported a spoofing vulnerability of the recipient in...
-
How To
How To Spoof MAC Address Using Macchanger in Kali Linux
MAC address spoofing is a technique for temporarily changing your Media Access Control (MAC) address on a network device. A MAC Address...






