All posts tagged "SQL-injection"
-

 204Vulnerabilities
204VulnerabilitiesPHP Melody 2.7 – Multiple Vulnerabilities
What’s interesting when I come across a new piece of software is how the initial impressions change after reading the code. If...
-

 304Cyber Attack
304Cyber AttackSQL Injection Used By Hackers To Get Access Of Websites
There are numerous strategies by way of which you can hack the web sites but sq. Injection method is the one of...
-

 238How To
238How ToHere is How Hackers Perform a SQL Injection Attack
A “SQL injection” (SQLI) attack is an exploit that takes advantage of poor web development techniques and, typically combined with, faulty database...
-

 265Data Security
265Data SecurityHuman Rights Foundation Website Hacked, Thousands of Accounts Exposed
SQL injection exposes nearly 20,000 usernames and passwords. The Hungarian Human Rights Foundation website was hacked a few minutes ago by Kapustkiy...
-

 180Vulnerabilities
180VulnerabilitiesHow to Exploit Belkin WEMO gear to hack Android devices
Belkin’s WeMo home automation firmware that’s in use in several IoT devices has recently been found vulnerable to an SQL injection. Belkin’s...
-
 101Vulnerabilities
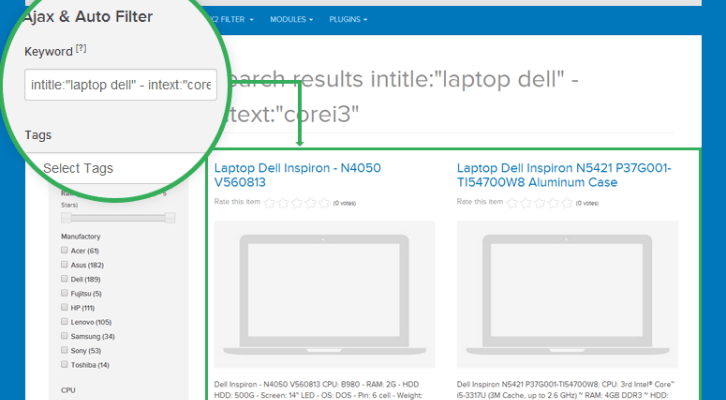
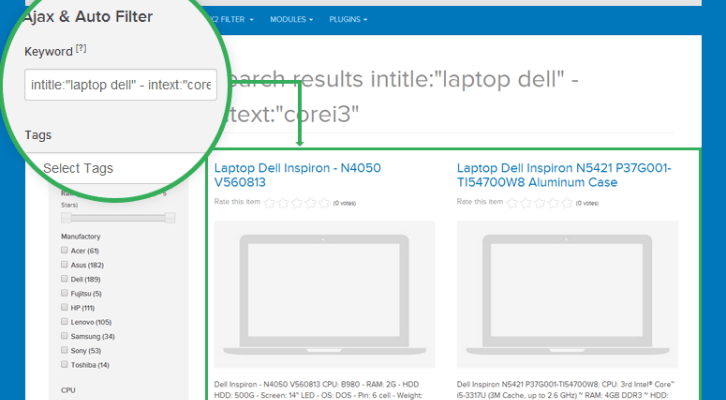
101VulnerabilitiesSQL Injection zero-day in component ja-k2-filter-and-search of Joomla
Information Security experts have discovered an SQL injection zero-day vulnerability in Joomla component ja-k2-filter-and-search. Information Security Researchers Dimitrios Roussis and Evangelos Apostoloudis...
-
 112Incidents
112IncidentsFake attacks by insiders to fool companies
Even during August’s holiday season, if you type ‘hacktivists’ in Google News – just for the last week you will get more...
-
 143Vulnerabilities
143VulnerabilitiesAfter Illinois hack, FBI warns of more attacks on state election board systems
Concern about more attacks mounting as presidential elections approach. Someone using servers in the US, England, Scotland, and the Netherlands stole voter registration...
-

 152Vulnerabilities
152VulnerabilitiesOver 25 million accounts stolen after Mail.ru forums hacked
Two hackers were able to steal email addresses and easily crackable passwords from three separate forums in this latest hack. Over 25...
-
 80Vulnerabilities
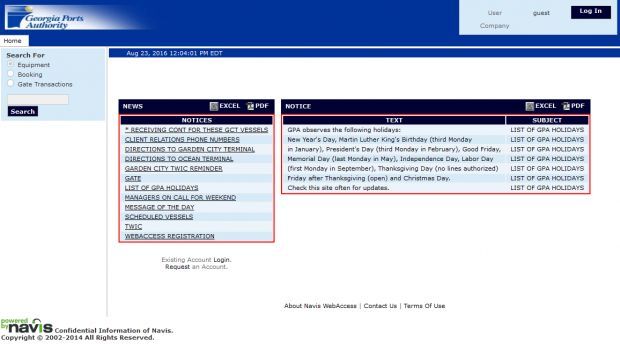
80VulnerabilitiesNavis WebAccess app used by US Ports is affected by a SQL injection flaw
The Navis WebAccess application used in the transportation sector worldwide is affected by a high severity SQL injection vulnerability. A software used...
-

 267Vulnerabilities
267VulnerabilitiesEpic’s forums hacked again, with thousands of logins stolen
More than 800,000 usernames and email addresses were taken, but most of the passwords aren’t readable or easily crackable. The company later...
-

 242Cyber Attack
242Cyber AttackLearn SQL Injection with Practical example!!
What is a SQL Injection? Full form of SQL is Structured Query Language. It is used to retrieve and manipulate data in...
-

 306Incidents
306IncidentsWorld Anti-Doping Agency Site Hacked; Thousands of Accounts Leaked
ANONYMOUS POLAND HACKED WORLD ANTI-DOPING AGENCY AND COURT OF ARBITRATION FOR SPORT’S SERVERS’ SERVER AND LEAKED PERSONAL DETAILS FOR GOD KNOWS WHAT REASON!...
-

 156Vulnerabilities
156VulnerabilitiesUbuntu Linux forums hacked!
There is a common misconception that all things Linux are bulletproof. The fact is, no software is infallible. When news of a...
-
 104Vulnerabilities
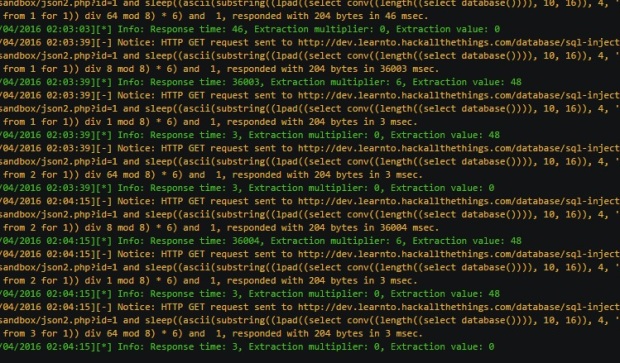
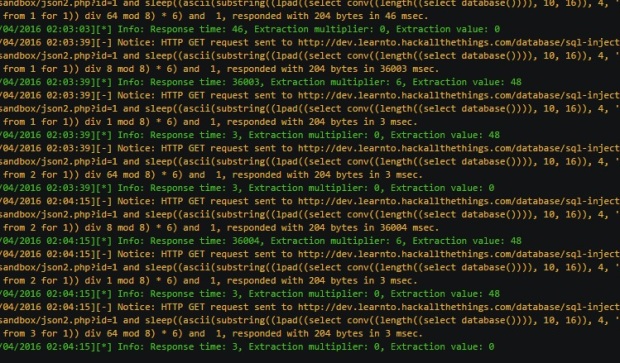
104VulnerabilitiesExtracting Multiple Bits Per Request From Full-blind SQL Injection Vulnerabilities
Blind SQL injection vectors are considered either partial-blind or full-blind in terms of feedback provided to the attacker. Often SQL injection vulnerabilities...
-

 92Vulnerabilities
92VulnerabilitiesKinky fetish forum hacked, hackers leak 100,000 user details
Hardcore fetish forum, Rosebutt Board hacked, traceable personal details leaked. The online hardcore fetish forum called Rosebutt Board was hacked by unknown hackers...
-
 98Malware
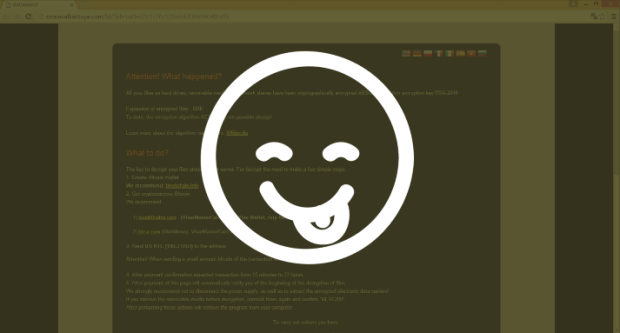
98MalwareResearchers Trick Radamant Ransomware C&C Server into Revealing Decryption Keys
Security researchers 2, Radamant coder 0.Researchers from InfoArmor, an Arizona-based cyber-security firm, have discovered an SQL injection flaw in the control panel...
-

 268Hacked
268HackedHow An SQL Injection Attack Works: Infographic
Short Bytes: Just like DDoS attacks, SQL injection attacks too are pretty infamous in the internet world. They are responsible for about...
-

 161Vulnerabilities
161VulnerabilitiesSAP Patches 12 SQL Injection, XSS Vulnerabilities in HANA
SAP patched a dozen holes in its in-memory management system, HANA, that could have led to SQL injection attacks, cross-site scripting (XSS)...
-
 122Vulnerabilities
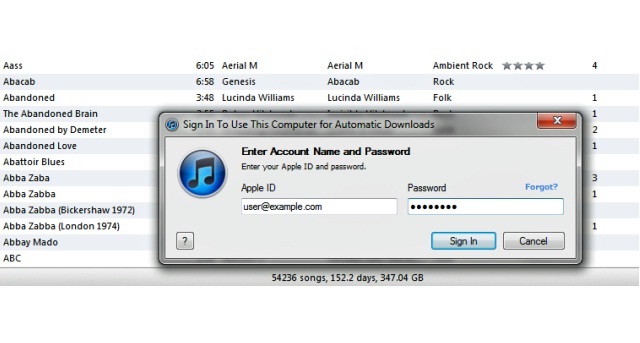
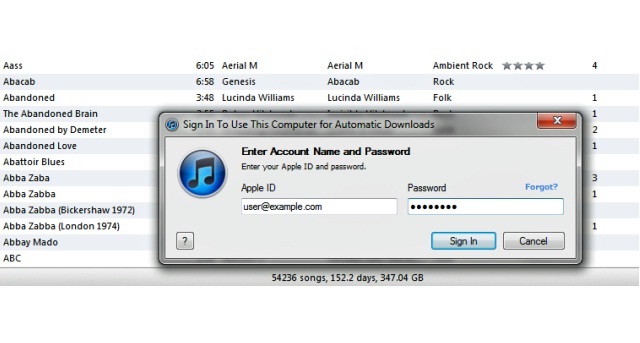
122VulnerabilitiesMalware infecting jailbroken iPhones stole 225,000 Apple account logins
A newly discovered malware family that preys on jailbroken iPhones has collected login credentials for more than 225,000 Apple accounts, making it...






