All posts tagged "threat intelligence"
-

 3.4KVulnerabilities
3.4KVulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
״Defenders think in lists, attackers think in graphs,” said John Lambert from Microsoft, distilling the fundamental difference in mindset between those who...
-

 3.2KCyber Attack
3.2KCyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
Threat actors are attempting to actively exploit a critical security flaw in the ValvePress Automatic plugin for WordPress that could allow site...
-

 1.8KVulnerabilities
1.8KVulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
Palo Alto Networks has shared more details of a critical security flaw impacting PAN-OS that has come under active exploitation in the...
-

 4.1KData Breach
4.1KData BreachHow to Prioritize Cybersecurity Spending: A Risk-Based Strategy for the Highest ROI
As an IT leader, staying on top of the latest cybersecurity developments is essential to keeping your organization safe. But with threats...
-

 2.3KCyber Attack
2.3KCyber AttackLearn How to Build an Incident Response Playbook Against Scattered Spider in Real-Time
In the tumultuous landscape of cybersecurity, the year 2023 left an indelible mark with the brazen exploits of the Scattered Spider threat...
-
 1.6KCyber Attack
1.6KCyber AttackCISA Issues Emergency Directive to Federal Agencies on Ivanti Zero-Day Exploits
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday issued an emergency directive urging Federal Civilian Executive Branch (FCEB) agencies to...
-

 2.5KCyber Attack
2.5KCyber AttackLUCR-3: Scattered Spider Getting SaaS-y in the Cloud
LUCR-3 overlaps with groups such as Scattered Spider, Oktapus, UNC3944, and STORM-0875 and is a financially motivated attacker that leverages the Identity...
-

 4.5KData Breach
4.5KData BreachCybersecurity Budgets Are Going Up. So Why Aren’t Breaches Going Down?
Over the past few years, cybersecurity has become a major concern for businesses around the globe. With the total cost of cybercrime...
-
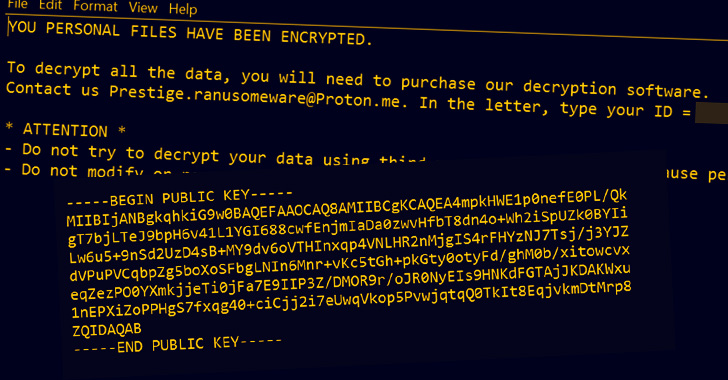
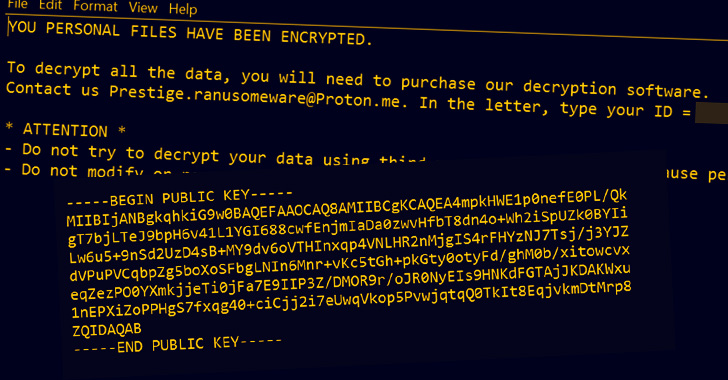 2.0KMalware
2.0KMalwareMicrosoft Blames Russian Hackers for Prestige Ransomware Attacks on Ukraine and Poland
Microsoft on Thursday attributed the recent spate of ransomware incidents targeting transportation and logistics sectors in Ukraine and Poland to a threat...
-

 2.0KLeaks
2.0KLeaksBuilding Your Incident Response Team
In order for an organization to properly respond to a breach or incident, they need to have a proper incident response team....
-
 352OSINT
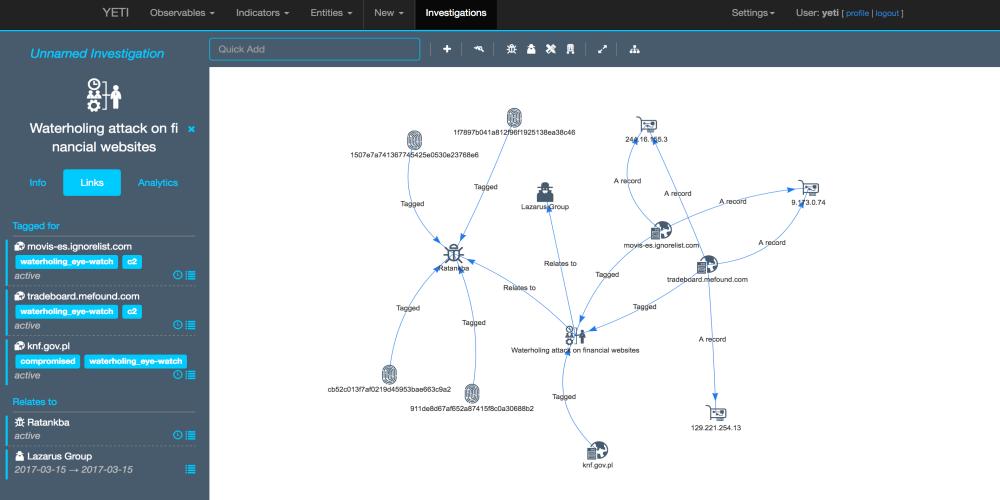
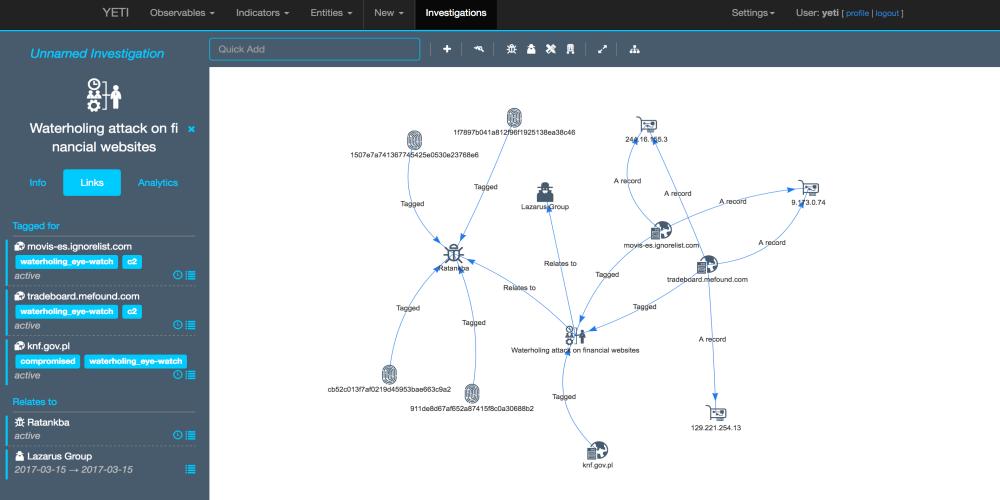
352OSINTYeti – Open Distributed Threat Intelligence
Yeti is a platform meant to organize observables, indicators of compromise, TTPs, and knowledge on threats in a single, unified repository. Yeti...






