All posts tagged "Tor proxy"
-

 193Malware
193MalwareDouble dipping: Diverting ransomware Bitcoin payments via .onion domains
Proofpoint researchers have been following an previously undocumented threat in which actors are stealing bitcoins via the Tor proxy onion[.]top. Operators of...
-
 429How To
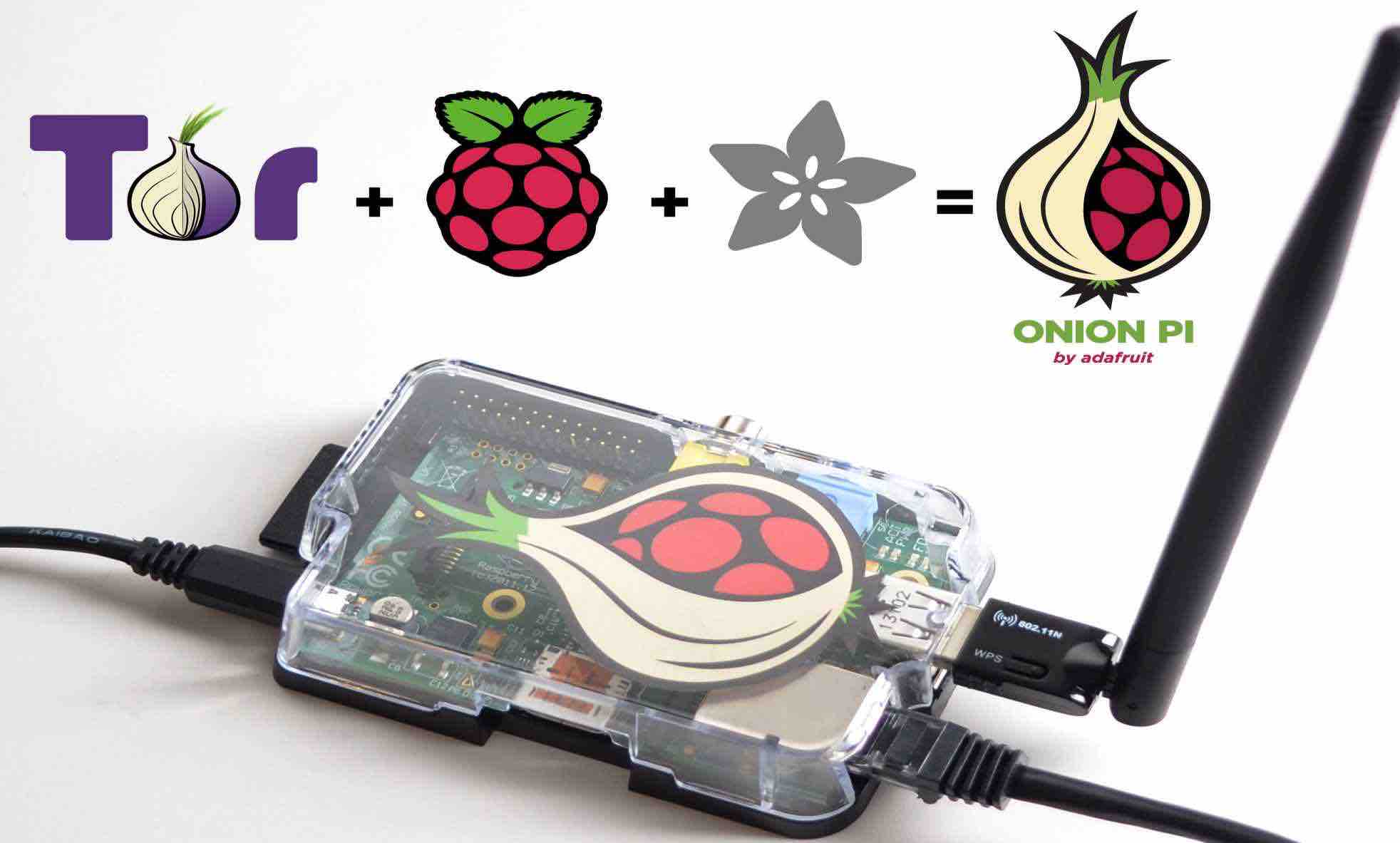
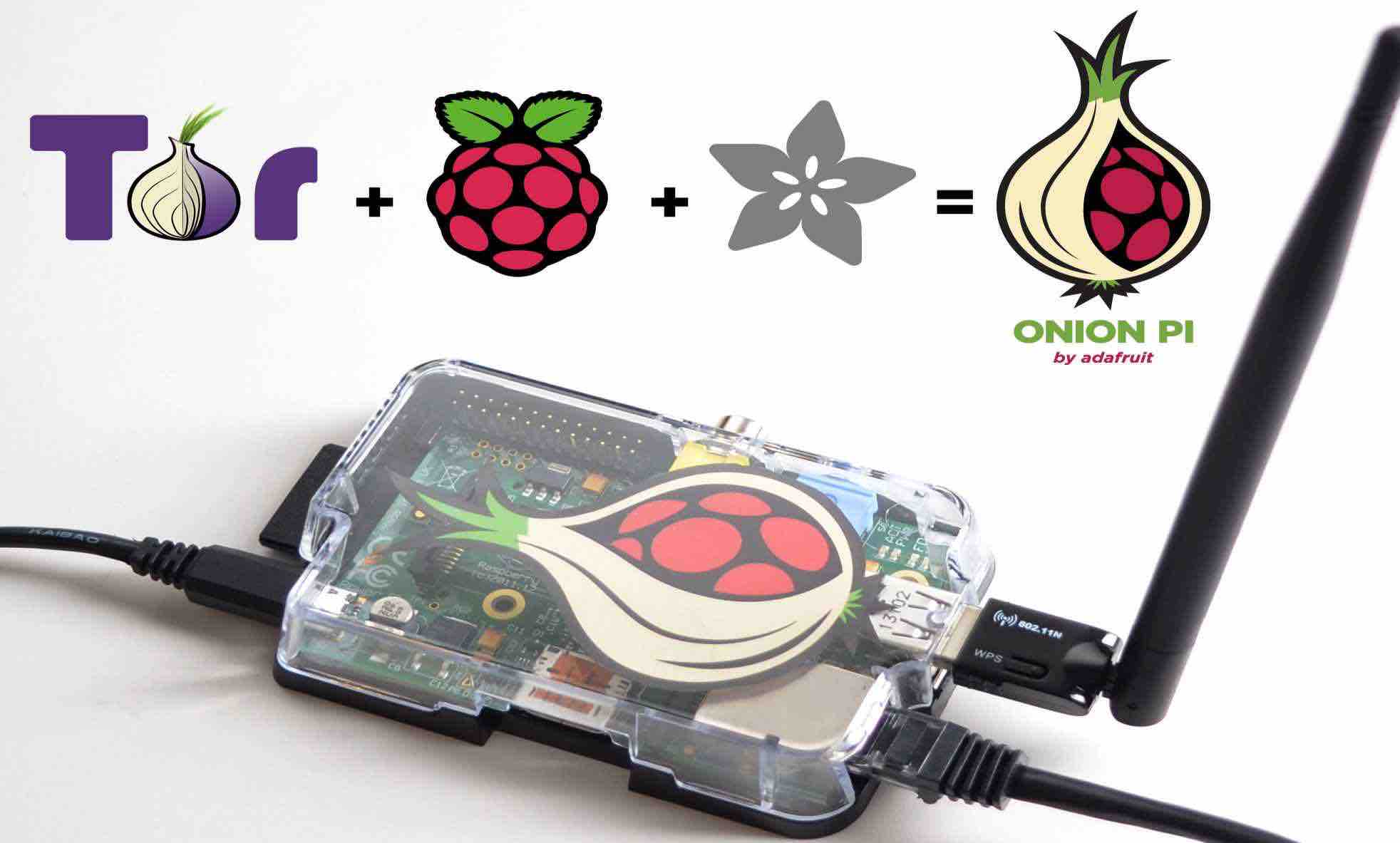
429How ToHow To Make Your Own TOR Proxy Router With A Raspberry Pi
Short Bytes: By investing some time and money, now you can make a portable Raspberry Pi TOR proxy router. Using this device, you...






