All posts tagged "Tor"
-

 94Data Security
94Data SecurityMouse movements are enough to track down Tor users
TOR’s Anonymity Promise Slashed- Users can be Tracked with their Mouse Movements! TOR is used by probably millions of Internet users simply...
-

 204Data Security
204Data SecurityHow JavaScript Functions And Mouse Movements Can Reveal TOR Users’ True Identity
Short Bytes: While TOR software suite promises enhanced privacy and security, researchers have found new ways like TOR user fingerprinting to unmask...
-

 243Data Security
243Data SecurityTracking users on the Tor Network through mouse movements
A security researcher has devised a new technique to track users by analyzing the mouse movements, even when surfing on the Tor...
-
 104Data Security
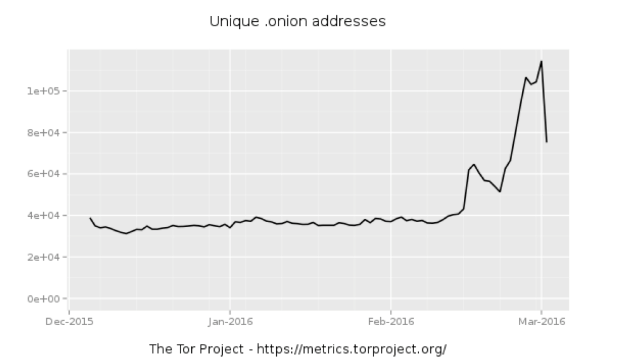
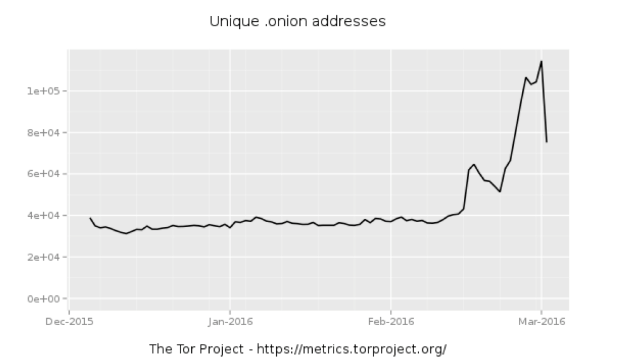
104Data SecurityWhole lotta onions: Number of Tor hidden sites spikes—along with paranoia
What’s driving the surge in hidden services—is it government tampering? In recent weeks, the number of “hidden services”—usually Web servers and other Internet...
-
 92Data Security
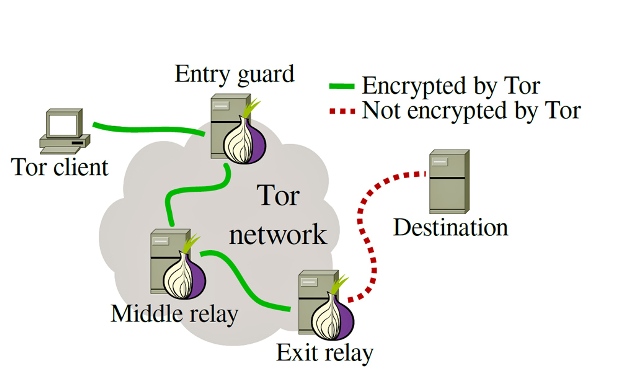
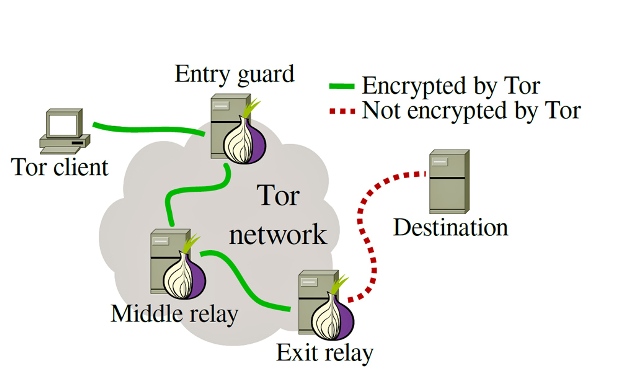
92Data SecurityTor takes aim against malicious nodes on the network
‘Sybil’ nodes could be used to de-anonymise traffic. The Tor Project is working with Princeton University boffins to try and identify possibly malicious...
-

 94Data Security
94Data SecurityThe DoD funded the Carnegie Mellon University’s research on Tor Hacking
A judge has confirmed that US Departement of Defense funded the Carnegie Mellon University to conduct research on the Tor hacking. In...
-
 203Data Security
203Data SecurityRicochet peer-to-peer messenger uses power of the dark web to escape metadata
Ricochet is the most secure encrypted anonymous messenger that sends no metadata. The security experts have approved a new internet messaging tool...
-

 88Incidents
88IncidentsHTTP GZIP Leaks Data on the General Location of Tor Websites
Some Tor servers may leak timezone info via gzipped files. Jose Carlos Norte, developer for the eyeOS virtual desktop project, has discovered an...
-
 130Vulnerabilities
130VulnerabilitiesTor Project patches critical XSS bug in its blog after researcher publicly discloses it
Tor Project patches critical bug but refuses to acknowledge the bug discovery by a security researcher. Tor Project’s website had a critical cross-site...
-
 109Incidents
109IncidentsDefault settings on Apache Web servers can reveal details about Tor traffic
Default Settings In Apache Servers Can Leak Details about Tor traffic. This has happened the second time in this week. Leaving default setting...
-
 115Data Security
115Data SecurityTor Announces Official Release of Tor Browser 5.5 With New Features
Short Bytes: Tor Browser 5.5 is the first stable release in the 5.5 series of Tor. It is released for all the...
-
 205Hacked
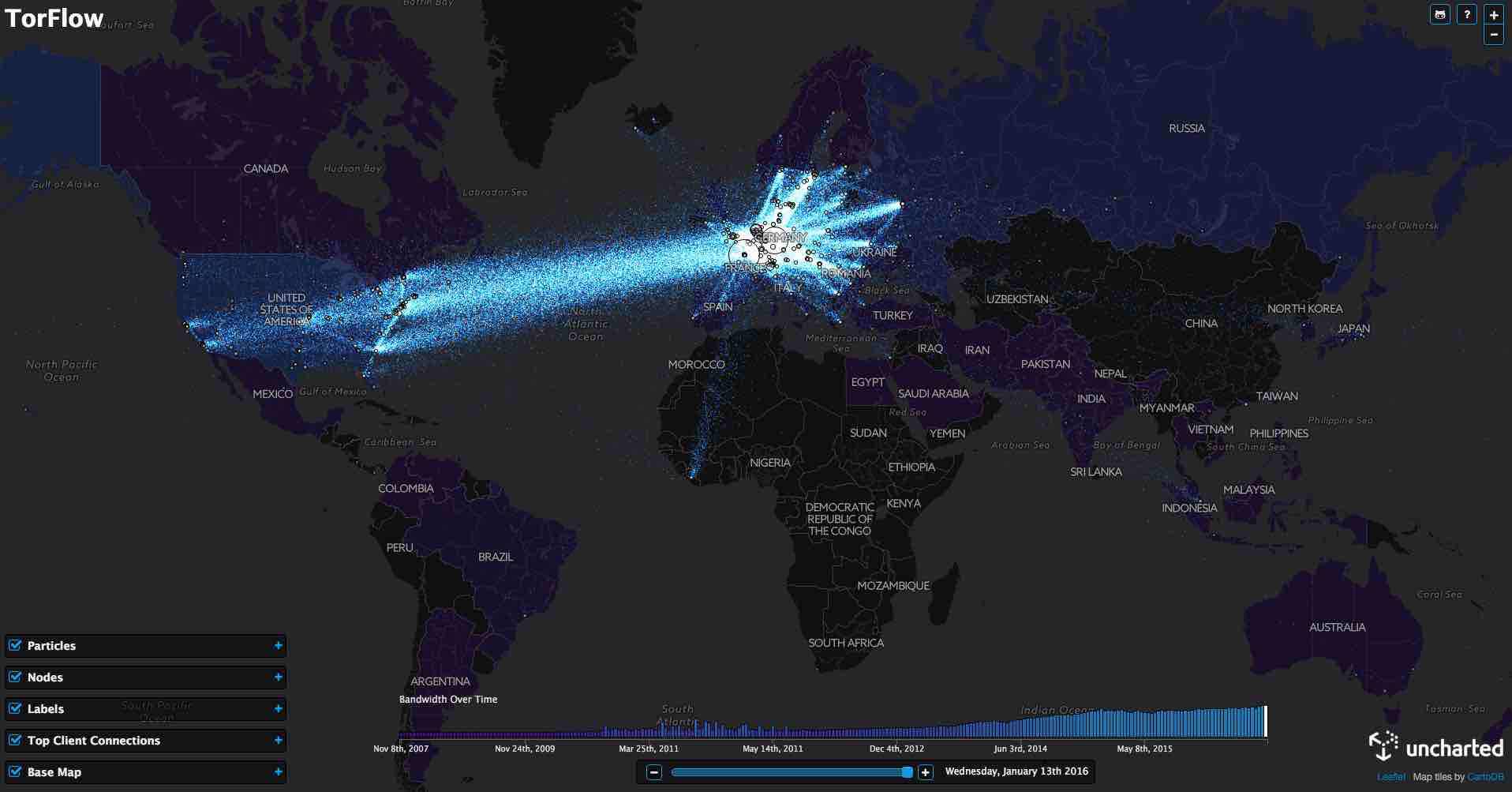
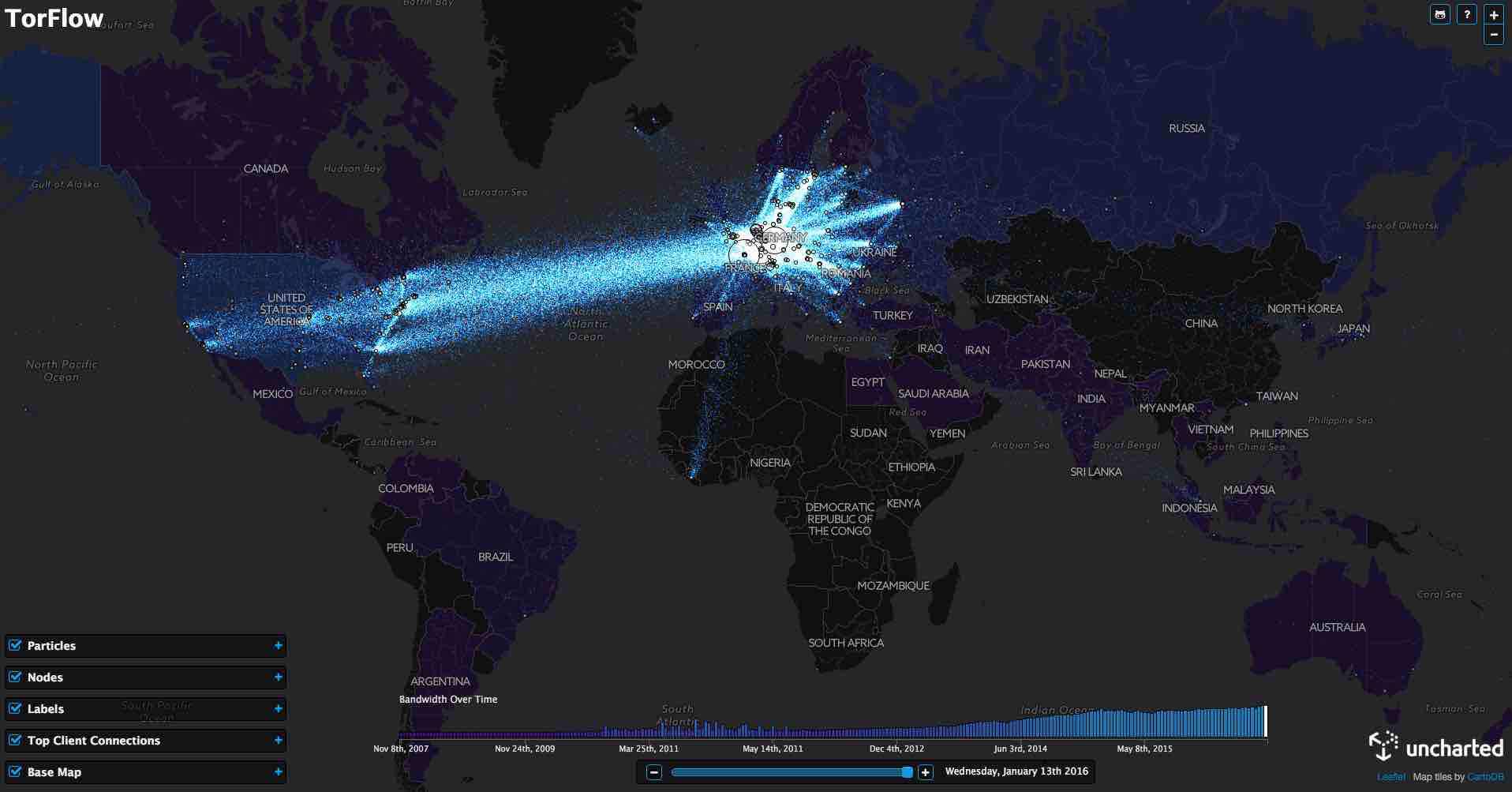
205HackedThis TorFlow Map Shows How TOR’s Data Looks As It Flows All Around The World
Short Bytes: Using the publicly available data, data visualization software firm Uncharted has prepared TorFlow — a map for visualizing how TOR’s...
-

 266Data Security
266Data SecurityFBI May Have Hacked Innocent TorMail Users
Back in 2013, the FBI seized TorMail, one of the most popular dark web email services, and shortly after started to rifle...
-
 98Data Security
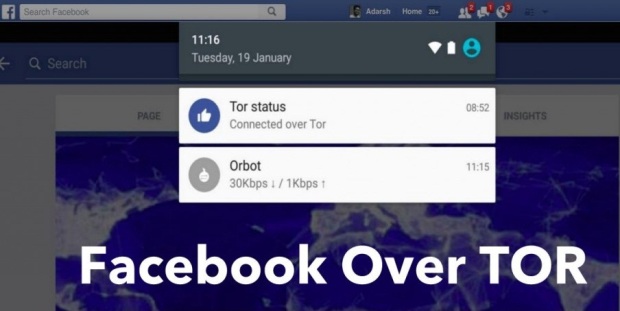
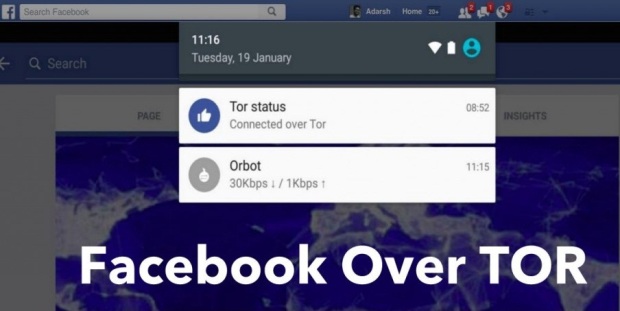
98Data SecurityFacebook Android App Gets Built-in TOR Support But Still Needs Your Real Name
Short Bytes: If you are interested in increasing the security and privacy of your network traffic, here’s a great news for you....
-

 95Data Security
95Data SecurityProPublica Launches the Dark Web’s First Major News Site
THE SO-CALLED DARK web, for all its notoriety as a haven for criminals and drug dealers, is slowly starting to look more...
-
 319Incidents
319IncidentsFBI Hacked 1000+ Dark Web Computers To Shut Down Largest Child-pornography Site
Short Bytes: Last year, the FBI engaged in the largest ever law enforcement hacking campaign to shut down “the largest remaining known...
-
 432Data Security
432Data SecurityTOR Anonymity: Things Not To Do While Using TOR
Short Bytes: Being Anonymous online is the need of the hour, and TOR browser does that job quite efficiently and honestly. But...
-

 82Data Security
82Data SecurityThe Father of Online Anonymity Has a Plan to End the Crypto War
IT’S BEEN MORE than 30 years since David Chaum launched the ideas that would serve as much of the groundwork for anonymity...
-
 176Data Security
176Data SecurityThe Tor Project Is launching the Tor Bug Bounty Program
The Tor officially announced to launch the Tor Bug Bounty Program in the next year, a great news for the Tor community....
-

 308Hacked
308HackedTails 1.8 Just Released: New Version Of Edward Snowden’s Favorite Linux OS
Image: fossBytes Short Bytes: A Tails live-USB is like a security-focused computer in a tiny box. Edward Snowden used the same OS...
-
 271Data Security
271Data SecurityMIT Creates Untraceable Anonymous Messaging System Called Vuvuzela
Researchers are still looking for a Tor alternative.Scientists at the MIT Computer Science and Artificial Intelligence Laboratory (CSAIL) have created an anonymous...






