All posts tagged "USB"
-
 3.4KData Security
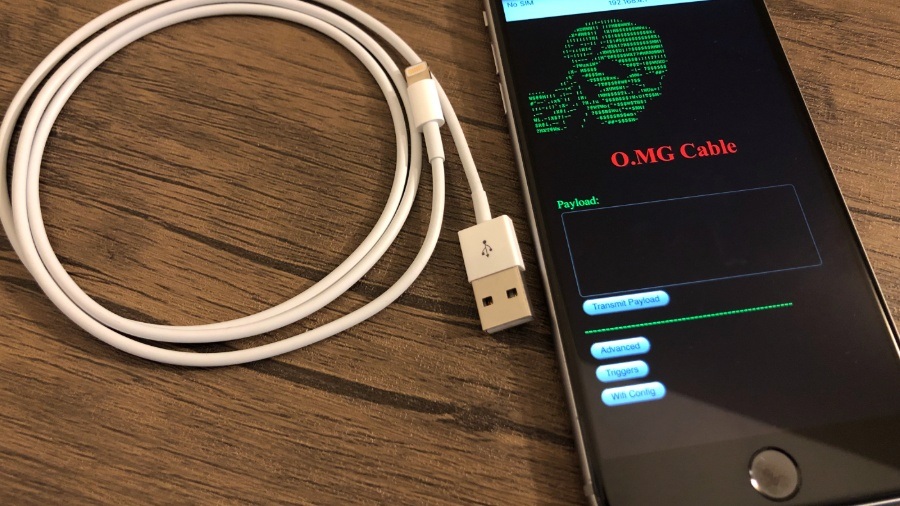
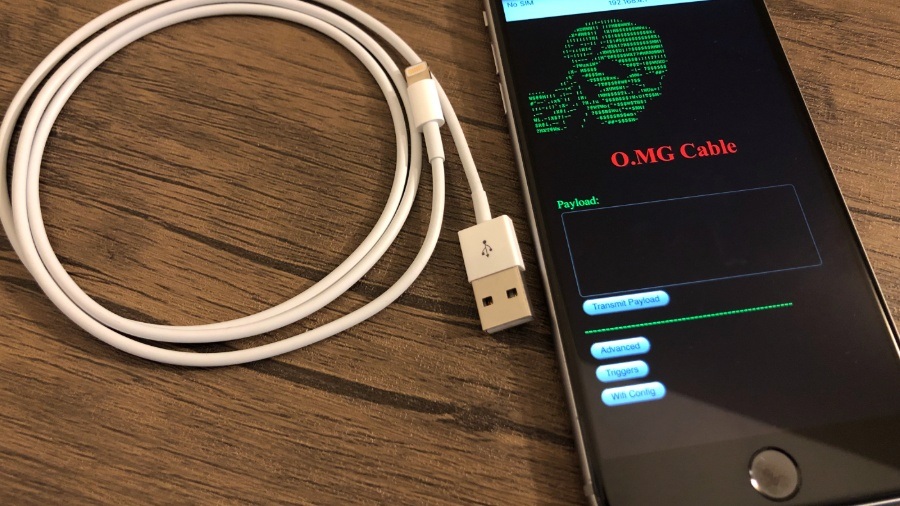
3.4KData Security$120 charging cable O.MG remotely steals data from Apple devices
Originally, O.MG Cable was introduced in 2019. In 2019, at DEFCON, an IT security researcher going by the online handle of MG...
-

 1.0KMalware
1.0KMalwareNever charge your Android or iOS smartphone in public places; new malware “juice-jacking”
A new threat has caught the attention of the cybersecurity community in Los Angeles, California. According to the district attorney office, some...
-

 302News
302NewsSony Claims Its USB-C Hub Is The World’s Fastest SD Card Reader
Sony has unveiled a new USB-C saying it is the “world’s fastest smart multifunction USB hub.” Dubbed the MRW-S3, this SD card...
-
 475Tutorials
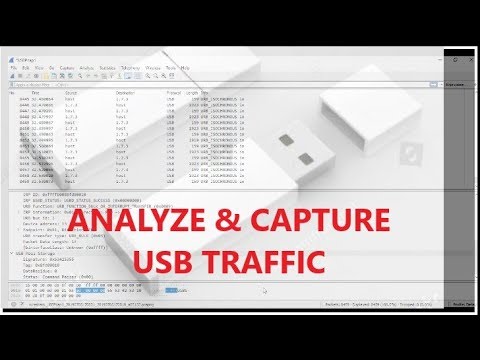
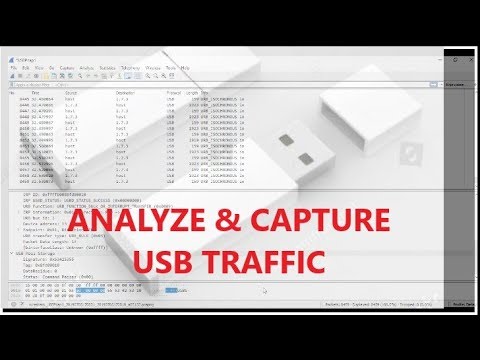
475TutorialsHow to analyze USB Traffic
Everyone would have well known with capturing network packets using analyzer tools. But very few have known with capturing with USB packets....
-

 357Geek
357GeekNew Windows 10 bug causes PCs to take longer to shut down
Windows 10 bug: If you have a device connected via cable to the USB Type-C input, you may have to wait another...
-

 325News
325NewsWant To “Block” Windows 10 May 2019 Update? Simply Plug In A USB Drive
Every Windows 10 update comes with its own share of weird issues that are often hard to explain and funny at the...
-

 229News
229NewsStudent Uses “USB Killer” To Fry $58,000 Worth of Computers
Vishwanath Akuthota, a former student at The College of Saint Rose in Albany, New York, has pled guilty to causing heavy damage to...
-

 220News
220NewsUSB 4 Will Give You 40 Gbps Transfer Speeds On Your PC, But…
There was a time when the USB 2.0 port on our PCs was fast enough to transfer countless songs and video clips....
-
 262News
262NewsUSB 3.2 Is Here To Make Things More Confusing For Everyone
Bid goodbye to slow data transfer speed as the ultra-fast USB 3.2 is here and will be available later this year. The...
-

 271News
271NewsWi-Fi ‘Hiding’ Inside USB Cable: A New Security Threat On The Rise?
Today, the world has become heavily reliant on computers owing to the various advantages they offer. It has thus become imperative that...
-
 233News
233NewsNot So Innocent USB Cable Uses WiFi To Hack Your Device
USB cables utilized for injecting malware seems an emerging threat that people would have to deal with. Last year, a researcher showcased the capability...
-
 259Malware
259MalwareUSB-IF Launches USB Type-C Authentication Program To Protect Against From Malicious Devices
USB-IF announced USB Type-C Authentication Program to confirm the authencity of the USB device USB device, USB cable or USB charger. The...
-
 214News
214NewsUSB Type-C Authentication Program Launched To Protect Devices Against Hardware Attacks
Today, the USB Implementers Forum officially launched the USB Type-C Authentication Program to set a standard for type-C USB device for improved security. Presently,...
-

 268Data Security
268Data SecurityEmployee infects US govt network with malware after visiting 9,000 porn sites
Due to the carelessness of an employee, who apparently was a porn fan, the network of the satellite imaging facility, the U.S....
-
 295Data Security
295Data SecuritySchneider Electric Shipped USB Drives Loaded with Malware
Schneider Electric has released a warning and advisory notice according to which the USB drives shipped with some of the company’s products...
-

 224Data Security
224Data SecurityThe state of USB data protection
Data protection, whether related to personal customer or patient information, is critical across virtually all industries. A survey made by information security trainingresearchers...
-

 234Hacked
234HackedLinux Security Alert: Tons Of Linux Kernel USB Flaws Found By Google Hacker
The general perception of the public is that Linux and macOS operating systems are far more secure as compared to Windows. While...
-

 224Hacked
224HackedYour “Innocent” USB Port Could Be Leaking Personal Data To Hackers
Short Bytes: The USB ports on your laptop or desktop computer can be used to steal your sensitive information. According to a...
-

 223Incidents
223IncidentsAttackers can exploit electronic cigarettes to hack computers
Hackers can exploit electronic cigarettes and any other electronic device to deliver a malware in a poorly protected network. In November 2014,...
-

 304News
304NewsMazda cars hacked with just a USB
It seems that Mazda car owners have discovered a hack that allows them to tweak the Mazda’s MZD Connect infotainment system by...
-

 199Hacked
199HackedUSB Canary: This Open Source Tool Sends SMS If A Hacker Connects A USB Device
Short Bytes: USB Canary is an open source tool that monitors for any suspicious activity on a computer. Written in Python language,...






