All posts tagged "USB attacks"
-
 367Vulnerabilities
367VulnerabilitiesVulnerabilities expose Supermicro servers to virtual USB-Attacks
A report by network security experts states that threat actors are able to exploit some recently found vulnerabilities in remote management devices...
-

 169Incidents
169IncidentsTrump and Kim USB fan lauches information security alert
Information security experts express surprise at the fact that journalists covering the meeting between US President Donald Trump and North Korean leader...
-
 260Data Security
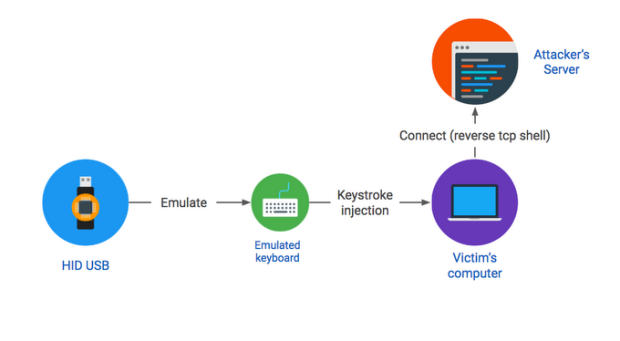
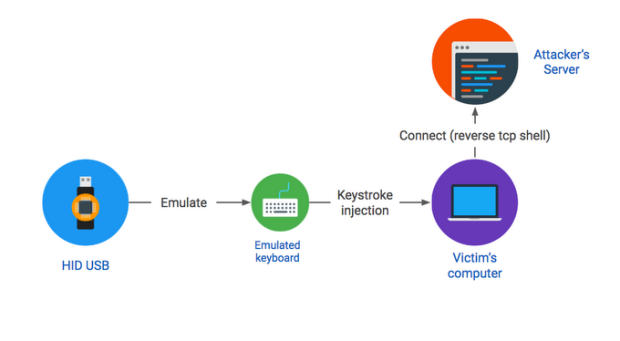
260Data Security#BHUSA2016 – Researcher explained how to hack any PC with a found USB drive
Dropping a malicious USB key in a parking lot is an effective attack vector, as demonstrated by our recent large-scale study. This...






