All posts tagged "Venom"
-
 297Tutorials
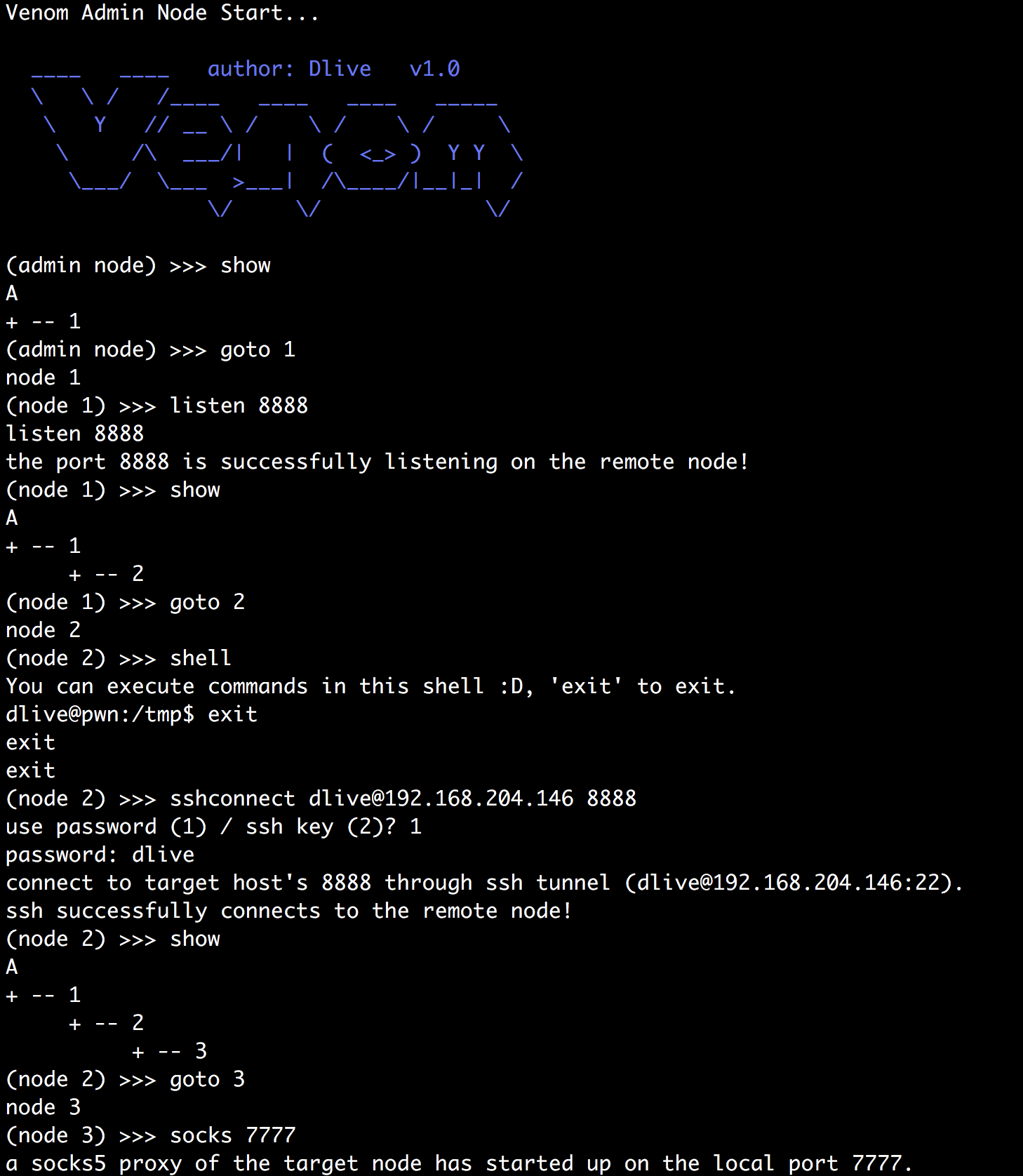
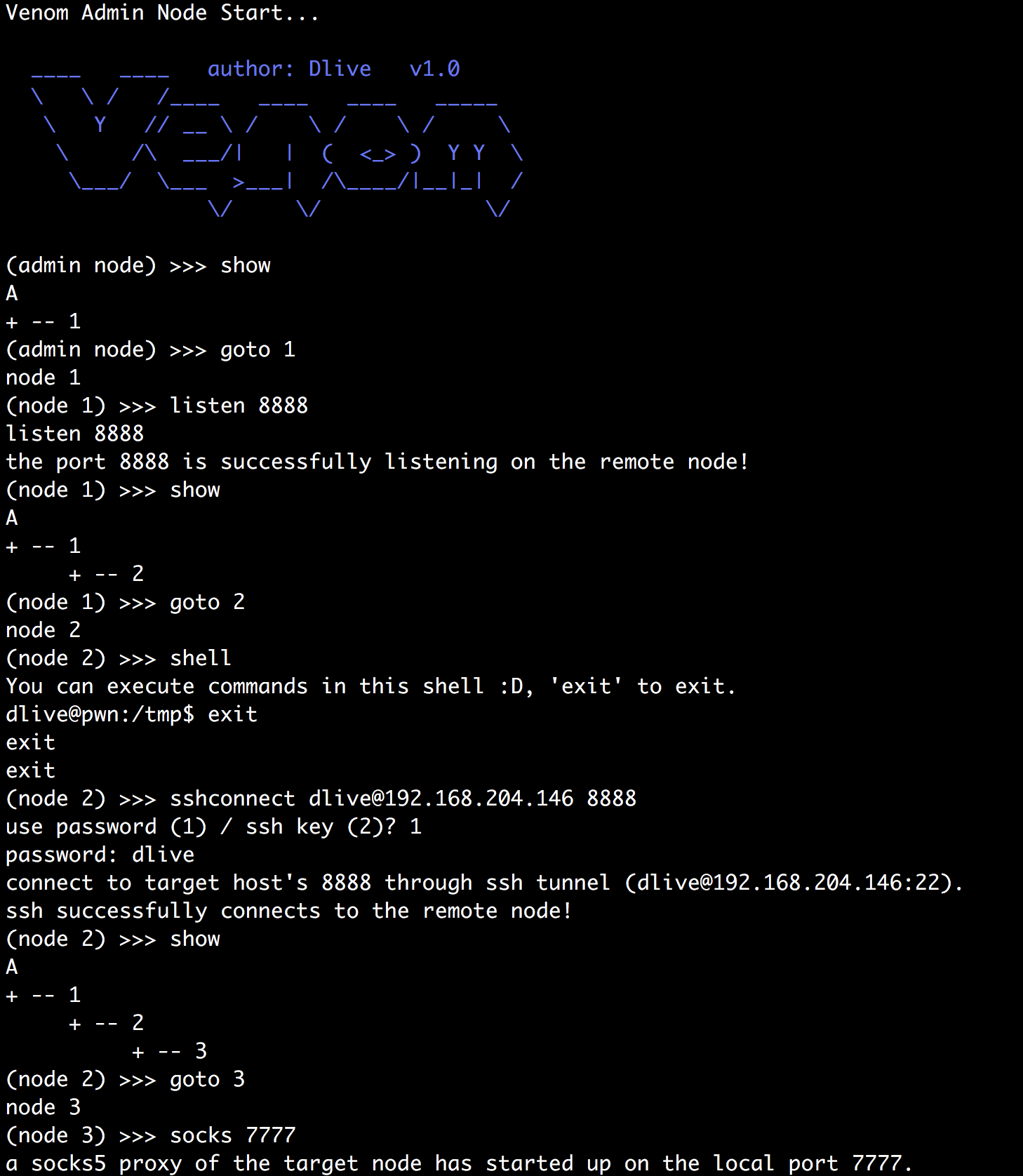
297TutorialsMulti hop Proxy for Penetration Testers (Step by Step tutorial)
As per ethical hacking experts, Internet is full of anonymous things. Lot of users surf internet using their native network operators. But...
-

 219Data Security
219Data SecurityNotion of Cloud’s Unmatched Security Shattered by ‘Venom’ vulnerability
The CrowStrike researchers discovered that any attacker can burst out of specific virtual machines and exploit whatever is running nearby — The...






