All posts tagged "vulnerability"
-

 275Data Security
275Data SecurityFacebook will pay you $40k USD for reporting bug
The social network would pay up to $40k USD for reporting errors that allow a single account takeover In the middle...
-

 171Data Security
171Data Security60 million users’ data were exposed by the US Postal Service
The vulnerability persisted on the Postal Service website for almost a year Cybersecurity and digital forensics specialists from the International Institute of...
-

 154News
154NewsFacebook’s New Dilemma, Silently Patched
Facebook has silently patched a vulnerability very recently that enabled 3rd party sites to extract user information without seeking the consent of...
-

 282News
282NewsUsed Data Storage Devices Have Security Flaws
According to Researchers at Radboud University in the Netherlands ‘data storage devices with self-encrypting drives don’t provide the expected level of data...
-

 295News
295NewsDJI Drone Vulnerability Due to DJI Forum’s Weakness, Patched by its Vendor
Just like personal computers, smartphones and tablets, new smart devices such as the highly viral remote quadcopters (AKA drones) are powered by...
-

 312News
312NewsThe Responsible Disclosure of Software Vulnerabilities in the Nutshell
Computer security vulnerabilities are a threat that has spawned a booming industry, between the heightened global focus on security, and the proliferation...
-

 254News
254NewsThe Importance of Application Security Approach in Today’s Computing
Application security testing was not a vital part of software development in the early days of computing. In those early days, the...
-

 263News
263NewsTesla Model S Stolen, Thieves Hack the Keyless Entry System
A Tesla Model S was stolen recently in Essex, England after a pair of thieves hacked the car’s high-tech keyless entry system....
-
 282News
282NewsWhat Do We Need to Know About the 2018 Global DNS Threat Report?
Just like the healthcare industry, the financial market players are also a profitable target of cybercriminal elements. The Global DNS Threat Report...
-

 205Data Security
205Data SecurityVesta control panel servers infected with DDoS malware after supply chain attack
An open-source hosting panel software provider, Vesta Control Panel (VestaCP), has admitted that the company became a victim of a supply chain...
-

 339News
339News7 Useful Android Vulnerability Scanners
There is a huge difference between an Android antivirus and an Android app that offers vulnerability scans. The former has questionable effectiveness...
-

 303News
303NewsThe Highly Competitive Web Application Firewall Market
The Internet continues to be a rich environment for vulnerability scans against weak websites and web hosting facilities. Businesses with a web...
-

 300News
300NewsAll WhatsApp Users Must Update: Zero Day Bug Found in WhatsApp
Google Project Zero’s Natalie Silvanovich has discovered a critical vulnerability in the Facebook-owned WhatsApp instant messaging app. In her twitter feed last...
-

 249Data Breach
249Data BreachGoogle Announced Google+ Shut down, Following Security Breach That Exposed 500,000 Users Accounts
Google announced Google+ shut down following the security breach that exposed 500,000 Google+ accounts. The bug allows third-party developers to access user’s...
-

 319News
319NewsTOP 10 PHP Vulnerability Scanners
In today’s world, automation is the name of the game. People expect a faster way to do the job, to meet deadlines...
-
 323Vulnerabilities
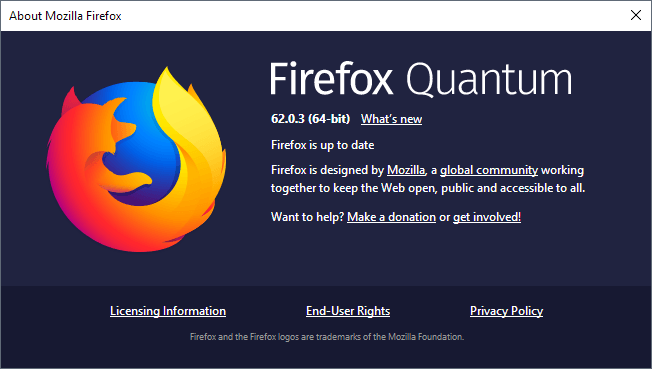
323VulnerabilitiesMozilla Firefox Releases 62.0.3 & Security Updates for 2 High Critical Vulnerabilities
Mozilla Firefox Released security updates that cover 2 critical vulnerabilities in Firefox 62.0.3 and Firefox ESR 60.2.2. One of the remote code execution...
-

 201News
201NewsNasty Linux Kernel Vulnerability Discovered, Mandatory Kernel Update Required
The Linux Kernel since version 3.16 to 4.18.8 has an unfixed vulnerability, as disclosed by Google Project Zero. The vulnerability was first...
-

 305News
305NewsNo Takers for Zero-Day Vulnerabilities on the Dark Web
According to experts vulnerability sales have been all but driven off the dark web, which now operates in the open. For years...
-

 314News
314NewsGoogle’s Vulnerability Scanning for Their Cloud Infrastructure in Beta
Google is engaging in a very competitive market in cloud storage and solutions sector. It is a growth market where the search...
-
 222Vulnerabilities
222VulnerabilitiesZDI Exposed Unpatched Microsoft RCE Zero-day Flaw in Public After it Crossed the 120 Days Deadline
A Microsoft Zero-day vulnerability that existing in Microsoft JET Database Engine has been crossed zero-day Initiative (ZDI) 120 days disclosure deadline and...
-
 276Cyber Crime
276Cyber CrimeMigrate to Tor Browser 8.0, Version 7.x Has Zero-Day Exploit
TOR, also known as the Onion router has been the go-to method for the privacy-savvy people to browse the web with confidence,...






