Search results for "RCE"
-

 1.8KData Breach
1.8KData BreachRogue WordPress Plugin Exposes E-Commerce Sites to Credit Card Theft
Threat hunters have discovered a rogue WordPress plugin that’s capable of creating bogus administrator users and injecting malicious JavaScript code to steal...
-

 4.0KVulnerabilities
4.0KVulnerabilitiesBeware: Experts Reveal New Details on Zero-Click Outlook RCE Exploits
Technical details have emerged about two now-patched security flaws in Microsoft Windows that could be chained by threat actors to achieve remote...
-
 2.3KVulnerabilities
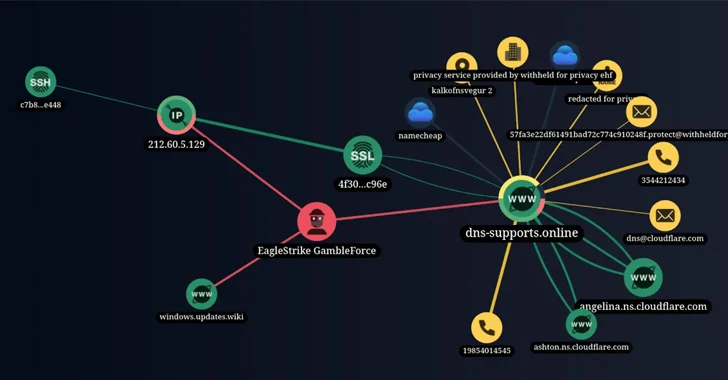
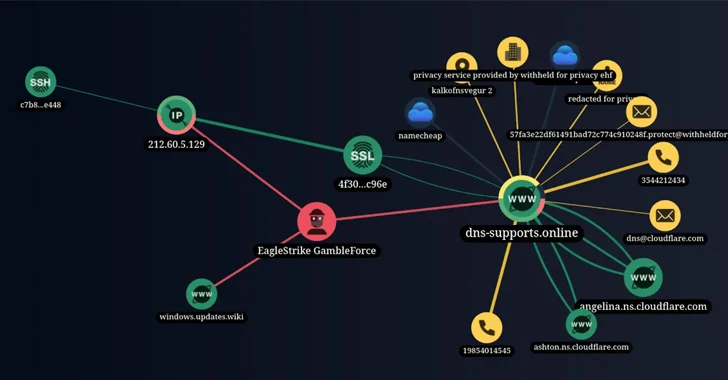
2.3KVulnerabilitiesNew Hacker Group ‘GambleForce’ Tageting APAC Firms Using SQL Injection Attacks
A previously unknown hacker outfit called GambleForce has been attributed to a series of SQL injection attacks against companies primarily in the...
-

 4.5KVulnerabilities
4.5KVulnerabilitiesNew Critical RCE Vulnerability Discovered in Apache Struts 2 – Patch Now
Apache has released a security advisory warning of a critical security flaw in the Struts 2 open-source web application framework that could...
-

 744Vulnerabilities
744VulnerabilitiesHackers Can Exploit ‘Forced Authentication’ to Steal Windows NTLM Tokens
Cybersecurity researchers have discovered a case of “forced authentication” that could be exploited to leak a Windows user’s NT LAN Manager (NTLM)...
-

 4.6KMalware
4.6KMalwareNew Ransomware Group Emerges with Hive’s Source Code and Infrastructure
The threat actors behind a new ransomware group called Hunters International have acquired the source code and infrastructure from the now-dismantled Hive...
-
 1.6KTutorials
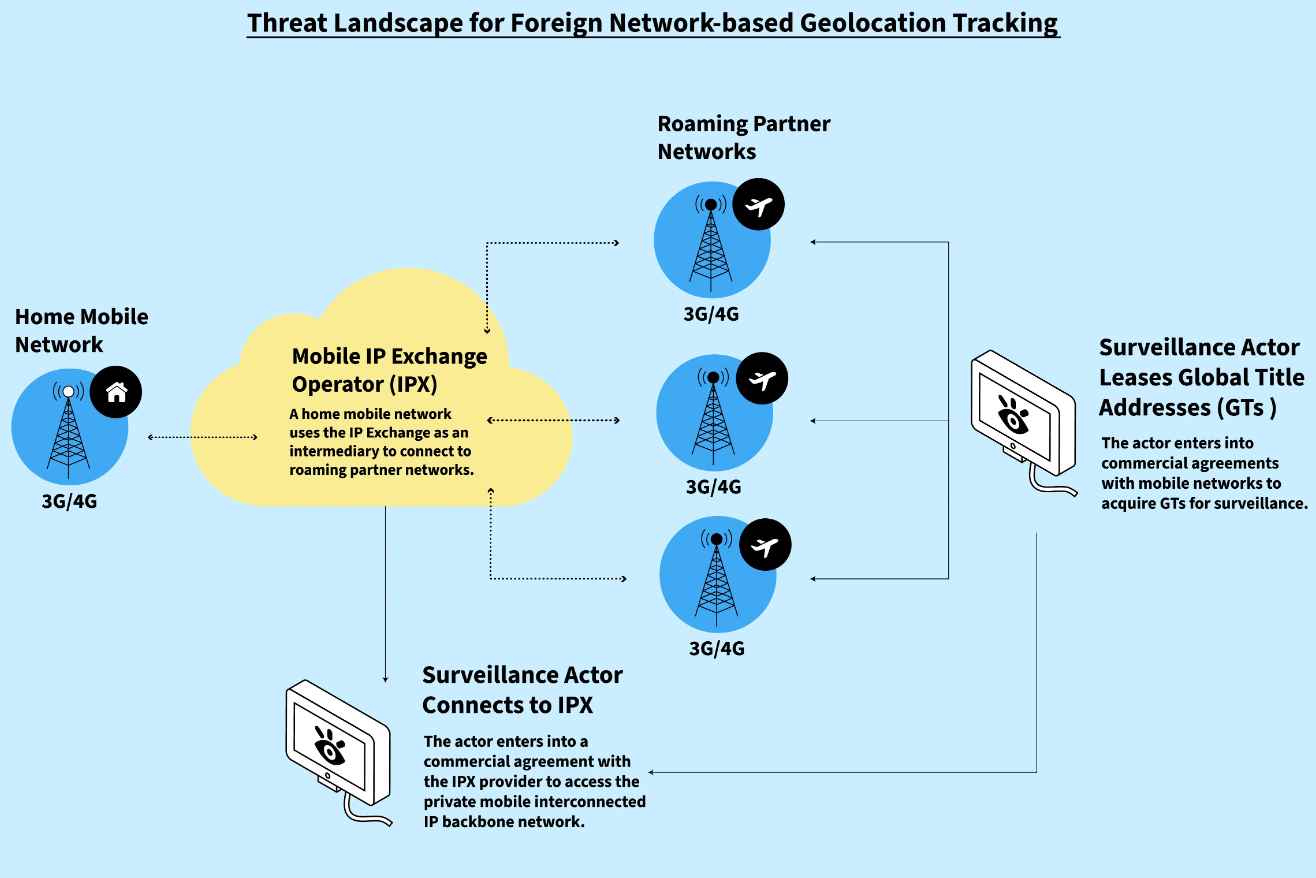
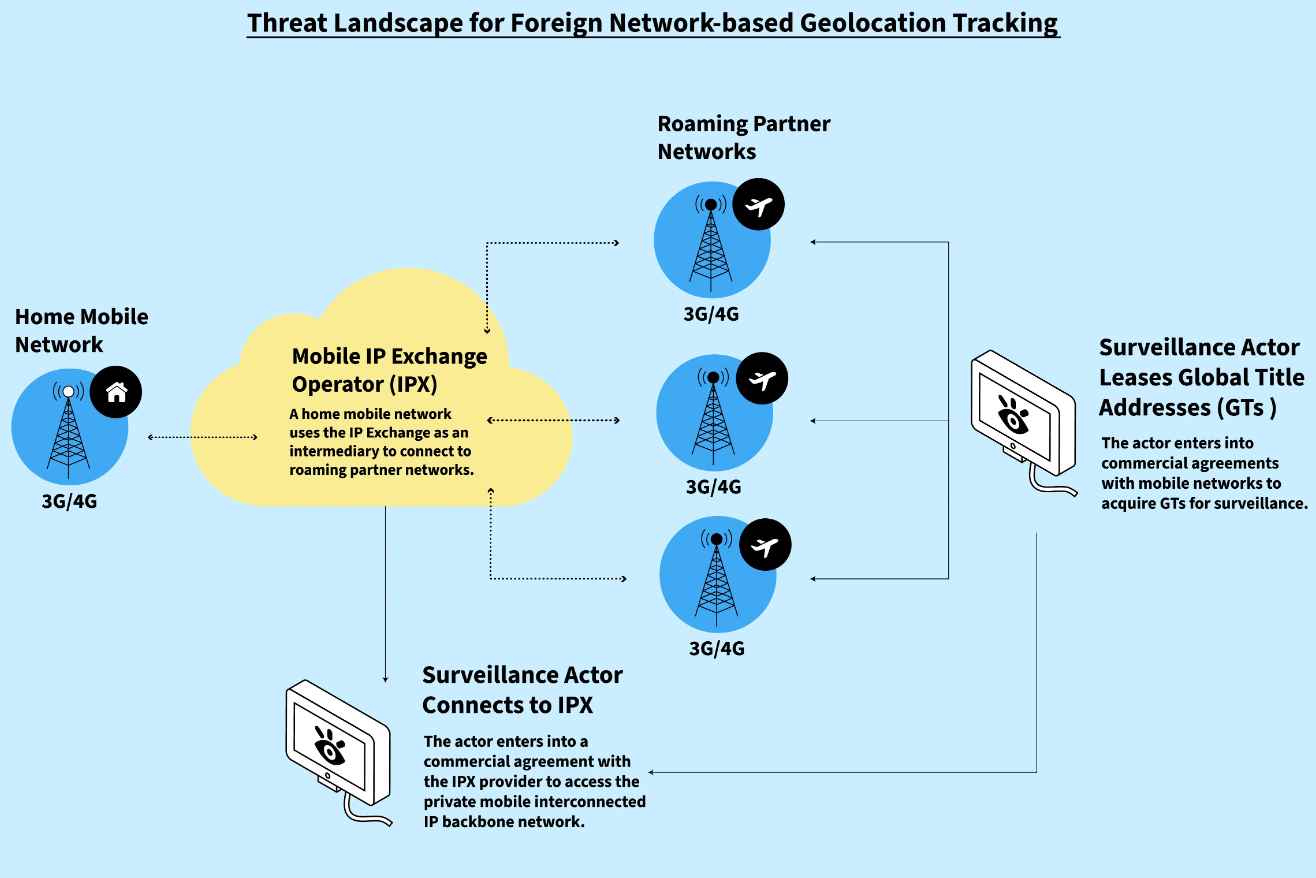
1.6KTutorialsThe Art of Interception :Active and Passive Surveillance in Mobile Signaling Networks
Mobile network data might be one of our most recent and thorough dossiers. Our mobile phones are linked to these networks and...
-

 1.3KVulnerabilities
1.3KVulnerabilitiesAct Now: VMware Releases Patch for Critical vCenter Server RCE Vulnerability
VMware has released security updates to address a critical flaw in the vCenter Server that could result in remote code execution on...
-
 4.1KVulnerabilities
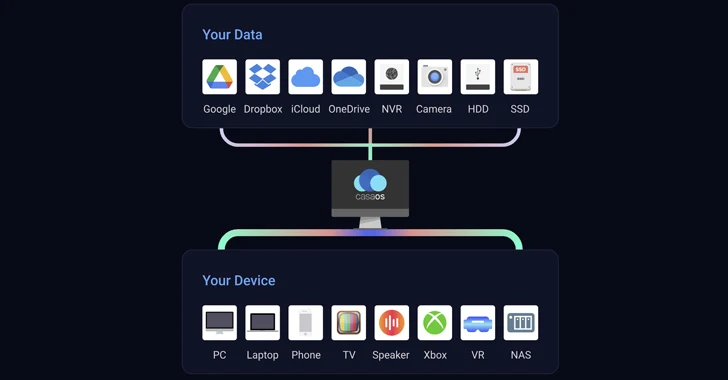
4.1KVulnerabilitiesCritical Vulnerabilities Uncovered in Open Source CasaOS Cloud Software
Two critical security flaws discovered in the open-source CasaOS personal cloud software could be successfully exploited by attackers to achieve arbitrary code...
-
 1.0KVulnerabilities
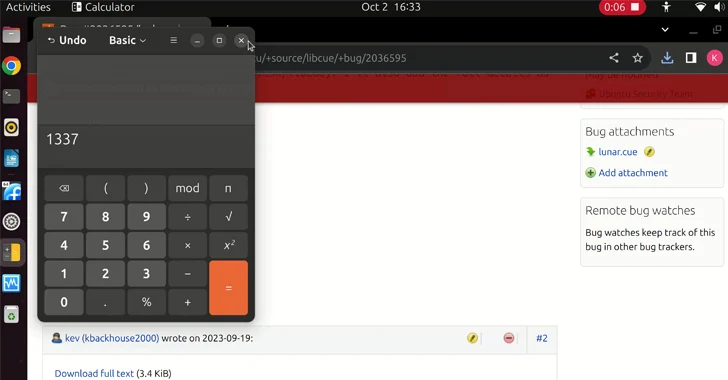
1.0KVulnerabilitieslibcue Library Flaw Opens GNOME Linux Systems Vulnerable to RCE Attacks
A new security flaw has been disclosed in the libcue library impacting GNOME Linux systems that could be exploited to achieve remote...
-
 2.1KMalware
2.1KMalwareRogue npm Package Deploys Open-Source Rootkit in New Supply Chain Attack
A new deceptive package hidden within the npm package registry has been uncovered deploying an open-source rootkit called r77, marking the first...
-
 966Vulnerabilities
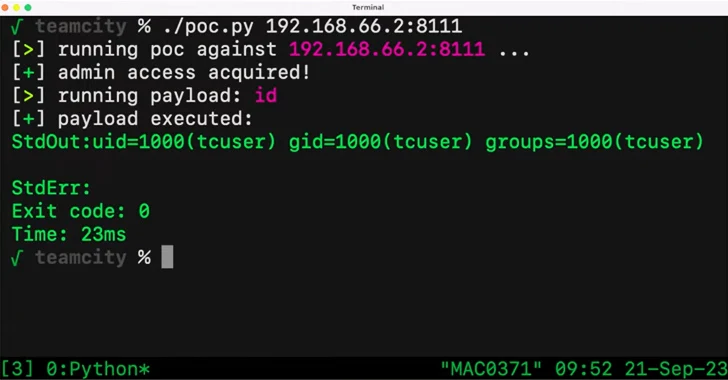
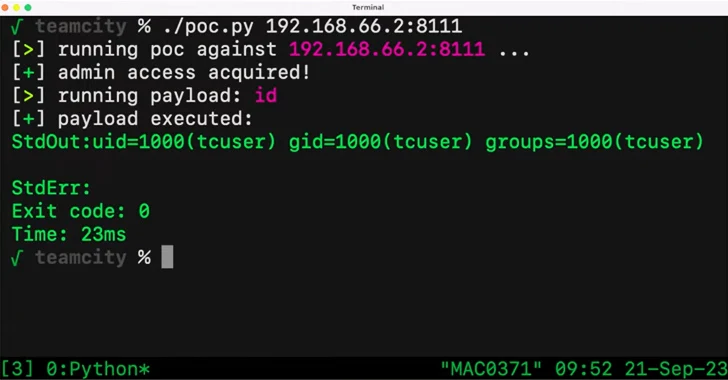
966VulnerabilitiesCritical JetBrains TeamCity Flaw Could Expose Source Code and Build Pipelines to Attackers
A critical security vulnerability in the JetBrains TeamCity continuous integration and continuous deployment (CI/CD) software could be exploited by unauthenticated attackers to...
-

 1.0KVulnerabilities
1.0KVulnerabilitiesCyberattacks Targeting E-commerce Applications
Cyber attacks on e-commerce applications are a common trend in 2023 as e-commerce businesses become more omnichannel, they build and deploy increasingly...
-
 227Tutorials
227TutorialsAzure cloud security tutorial series – Chapter 3 [Add resource to VNet]
Overview In the last chapter (Azure cloud security tutorial series – Chapter 2 [Virtual Network]) we saw on how to create VNet...
-
 1.6KVulnerabilities
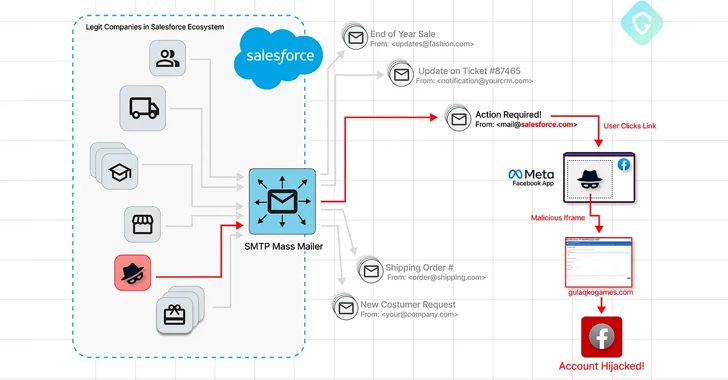
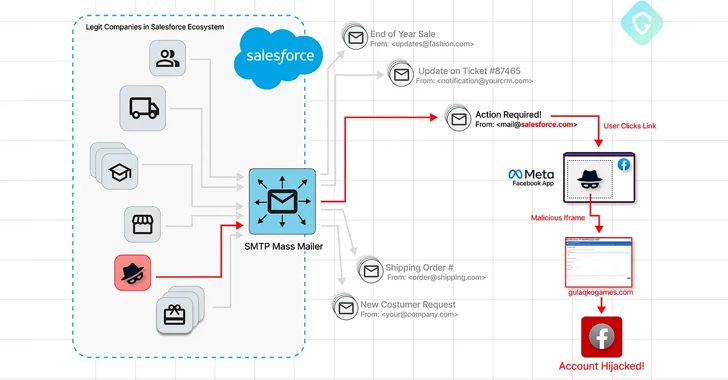
1.6KVulnerabilitiesPhishers Exploit Salesforce’s Email Services Zero-Day in Targeted Facebook Campaign
A sophisticated Facebook phishing campaign has been observed exploiting a zero-day flaw in Salesforce’s email services, allowing threat actors to craft targeted...
-
 349Vulnerabilities
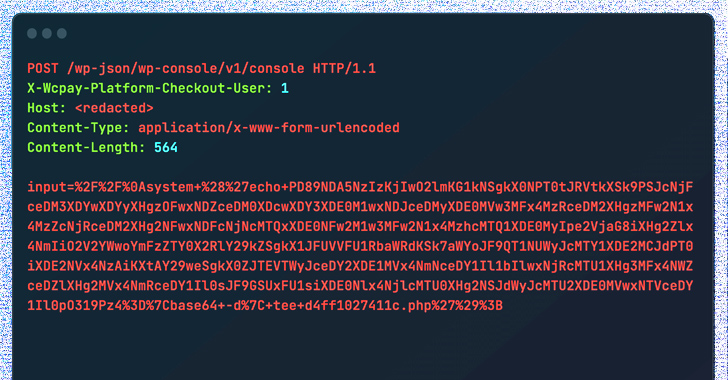
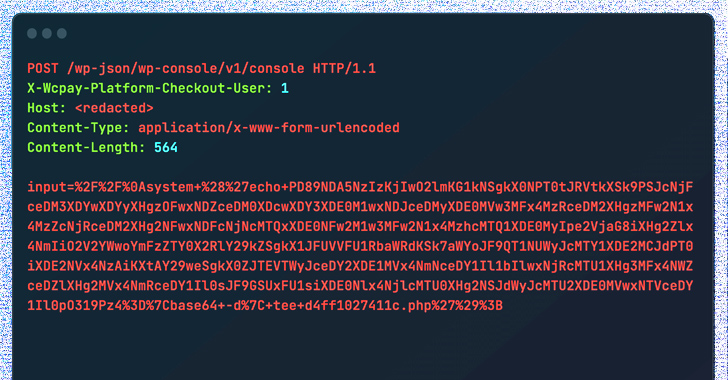
349VulnerabilitiesCybercriminals Exploiting WooCommerce Payments Plugin Flaw to Hijack Websites
Threat actors are actively exploiting a recently disclosed critical security flaw in the WooCommerce Payments WordPress plugin as part of a massive...
-

 4.4KData Security
4.4KData SecurityRazor gaming company source code, encryption keys, database and network credentials hacked
Following a buyer on a hackers’ forum offering stolen data for US$100,000 (S$134,898) in bitcoin on Saturday, it is believed that gaming...
-

 593Malware
593MalwareHackers Exploit Netwrix Auditor RCE Flaw in Truebot Malware Attack
A newly found Truebot Malware targets both US and Canada-based organizations to exfiltrate sensitive information by exploiting vulnerabilities in the Netwrix Auditor...
-

 2.8KVulnerabilities
2.8KVulnerabilitiesCritical Flaw Found in WordPress Plugin for WooCommerce Used by 30,000 Websites
A critical security flaw has been disclosed in the WordPress “Abandoned Cart Lite for WooCommerce” plugin that’s installed on more than 30,000...
-
 2.6KVulnerabilities
2.6KVulnerabilitiesCritical Security Vulnerability Discovered in WooCommerce Stripe Gateway Plugin
A security flaw has been uncovered in the WooCommerce Stripe Gateway WordPress plugin that could lead to the unauthorized disclosure of sensitive...
-

 4.2KData Security
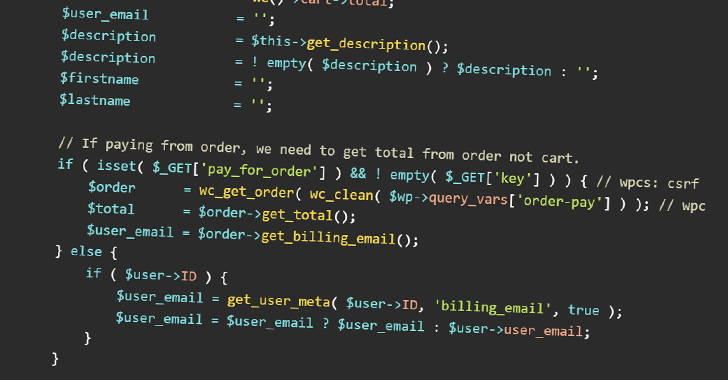
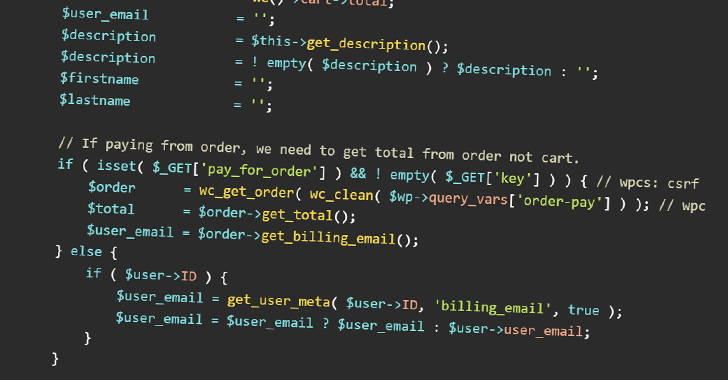
4.2KData SecurityHacking WooCommerce websites to get order details and customer personal information
The ever-changing topography of cyberspace always results in the introduction of new security flaws and vulnerabilities. A major vulnerability, which is now...






