Search results for "docker"
-

 3.3KMalware
3.3KMalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
Cybersecurity researchers have discovered multiple campaigns targeting Docker Hub by planting millions of malicious “imageless” containers over the past five years, once...
-

 1.8KMalware
1.8KMalwareHackers Exploit Misconfigured YARN, Docker, Confluence, Redis Servers for Crypto Mining
Threat actors are targeting misconfigured and vulnerable servers running Apache Hadoop YARN, Docker, Atlassian Confluence, and Redis services as part of an...
-

 2.3KMalware
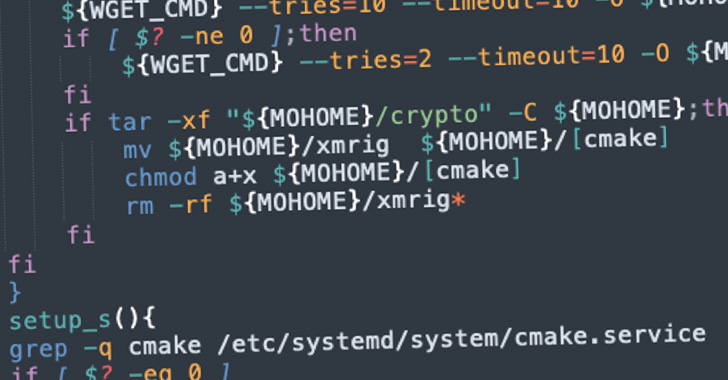
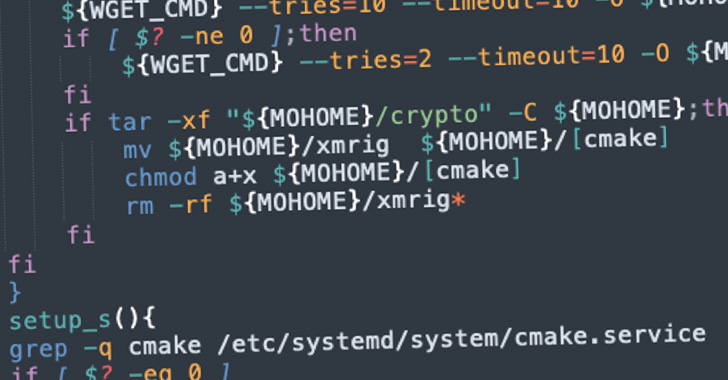
2.3KMalwareNew Docker Malware Steals CPU for Crypto & Drives Fake Website Traffic
Vulnerable Docker services are being targeted by a novel campaign in which the threat actors are deploying XMRig cryptocurrency miner as well...
-
 4.7KMalware
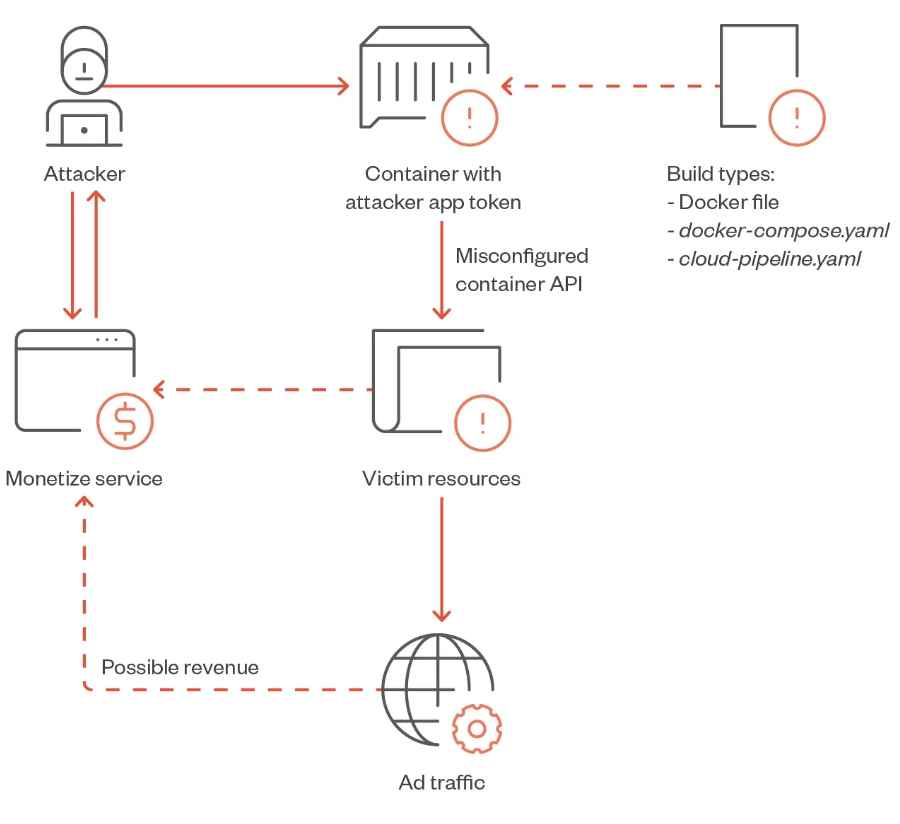
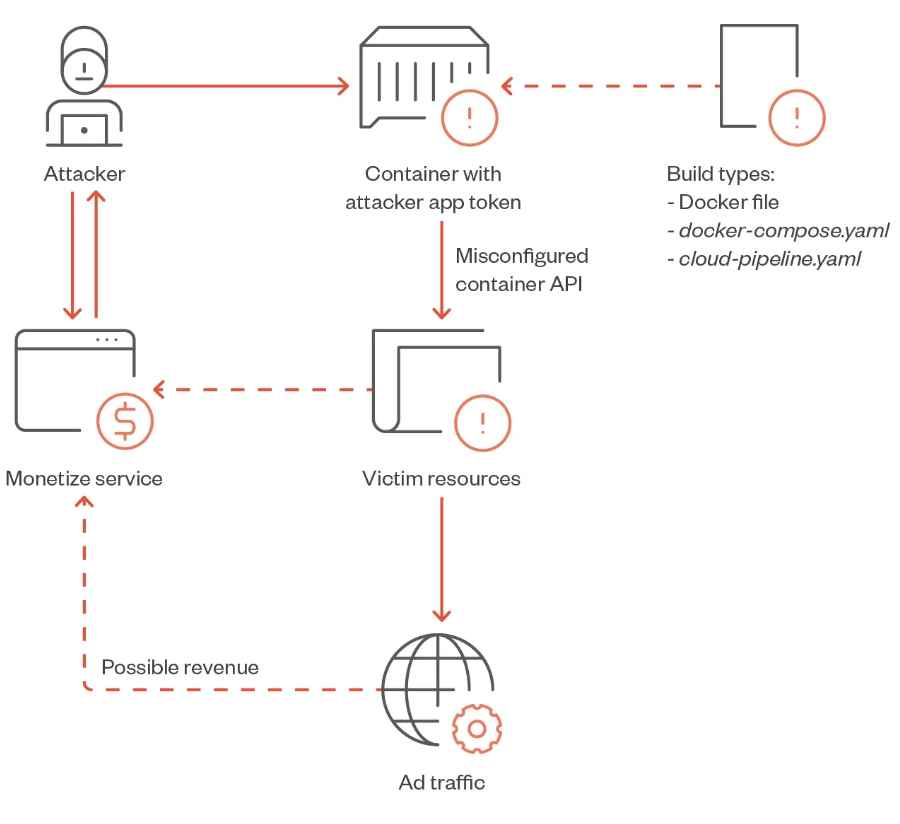
4.7KMalwareHow TrafficStealer utility allows anyone to earn money via vulnerable Docker containers
Researchers at TrendMicro have uncovered a new risk to Docker containers, a piece of malware that they have called “TrafficStealer.” The purpose...
-
 911Malware
911MalwareNew Cryptojacking Campaign Targeting Vulnerable Docker and Kubernetes Instances
A new cryptojacking campaign has been uncovered targeting vulnerable Docker and Kubernetes infrastructures as part of opportunistic attacks designed to illicitly mine...
-
 653Malware
653MalwareHackers Targeting WebLogic Servers and Docker APIs for Mining Cryptocurrencies
Malicious actors such as Kinsing are taking advantage of both recently disclosed and older security flaws in Oracle WebLogic Server to deliver...
-

 3.4KIncidents
3.4KIncidentsMore than 770 million records available through the Travis CI API: Anyone can extract tokens, secrets, and other credentials associated with services like GitHub, AWS, and Docker Hub
Software development and testing platform Travis CI confirmed the second incident of exposing its users’ data in less than a year. On...
-
 4.7KMalware
4.7KMalwareWatch Out! Cryptocurrency Miners Targeting Dockers, AWS and Alibaba Cloud
LemonDuck, a cross-platform cryptocurrency mining botnet, is targeting Docker to mine cryptocurrency on Linux systems as part of an active malware campaign....
-

 437Data Security
437Data SecurityDangerous hacking group attacks vulnerable Docker servers in cryptocurrency mining campaign
According to a report by Trend Micro, the hacking group identified as TeamTNT has been attacking Docker servers with exposed REST APIs...
-

 1.8KMalware
1.8KMalwareWormable DarkRadiation Ransomware Targets Linux and Docker Instances
Cybersecurity researchers are sounding the alarm bell over a new ransomware strain called “DarkRadiation” that’s implemented entirely in Bash and targets Linux...
-

 2.2KHack Tools
2.2KHack ToolsRE:TERNAL – Repo Containing Docker-Compose Files And Setup Scripts Without Having To Clone The Individual Reternal Components
RE:TERNAL is a centralised purple team simulation platform. Reternal uses agents installed on a simulation network to execute various known red-teaming techniques...
-
 1.0KVulnerabilities
1.0KVulnerabilitiesMost Critical Docker Vulnerability Let Hackers To Take Complete Control Over Host & All Containers Within It
Researchers discovered a critical vulnerability in Docker that allows an attacker to take complete control of the host and the containers associated...
-
 2.3KPentesting
2.3KPentestingRedCloud – Powerful Red Team Infrastructure deployment using Docker
Redcloud is a powerful and user-friendly toolbox for deploying a fully featured Red Team Infrastructure using Docker. Harness the cloud’s speed for...
-
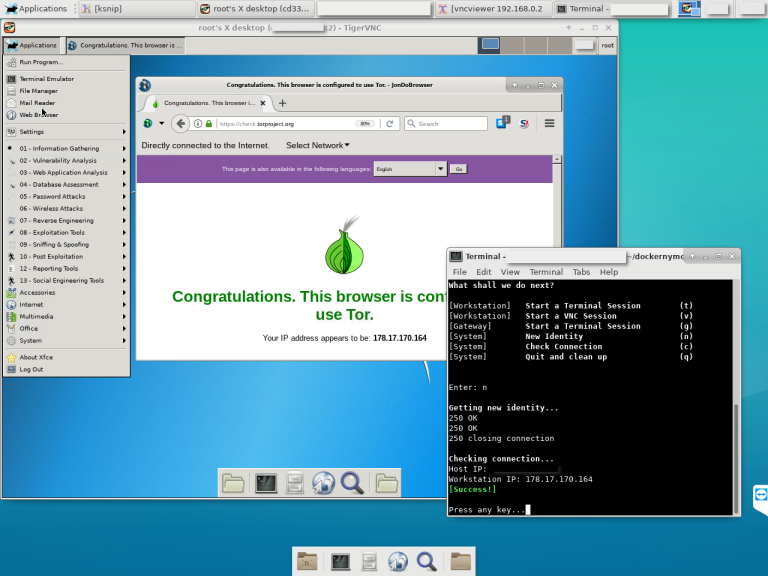
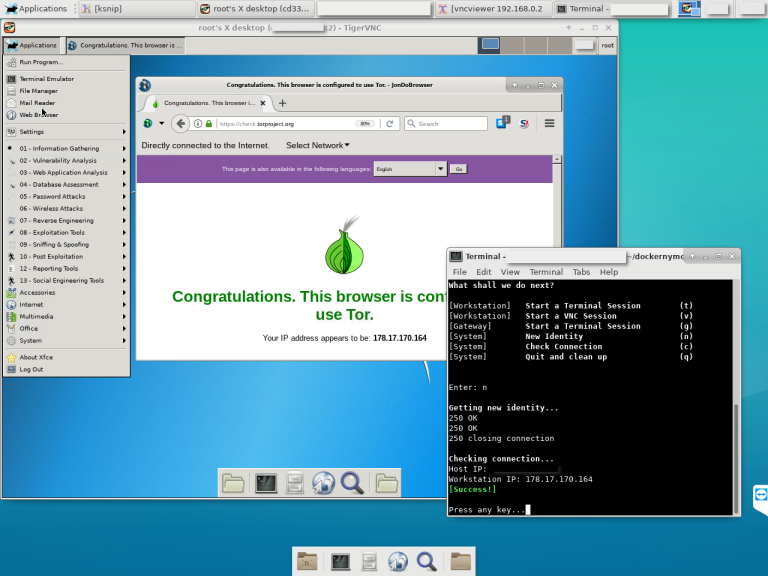 316Operating Systems
316Operating SystemsDockernymous – Create a Whonix-like gateway environment with Docker Containers
Dockernymous is a start script for Docker that runs and configures two individual Linux containers in order to act as an anonymization...
-

 3.0KCryptocurrency
3.0KCryptocurrencyCompromised Docker Hosts Use Shodan for Cryptocurrency Mining
Researchers have detected a campaign in which compromised docker hosts use Shodan for carrying out cryptocurrency mining. Hackers scan for Docker hosts...
-
 268Vulnerabilities
268VulnerabilitiesA new critical race condition vulnerability in Docker
According to IT security audits specialists all versions of the Docker software are impacted by a race condition vulnerability that, if exploited,...
-
 247Cyber Events
247Cyber EventsChange your password: Docker suffers breach; 190k users affected
Microsoft says its official Microsoft images hosted in Docker Hub have not been compromised. The company behind Docker, a computer program developed...
-
 617Incidents
617IncidentsData breach at Docker; hackers steal access keys for almost 200k accounts
In recent days, a still not identified hacker group got unauthorized access to a Docker database, a company dedicated to programmer software...
-
 312Data Breach
312Data BreachDocker Hub Hacked – Hackers Gained Access to 190,000 Users Accounts
Docker Hub Hacked, sensitive data more than 190,000 accounts may have exposed. Docker Hub discovered the unauthorized access to a single Hub...
-
 268Data Breach
268Data BreachDocker Hub Suffers a Data Breach, Asks Users to Reset Password
Docker Hub, one of the largest cloud-based library of Docker container images, has suffered a data breach after an unknown attacker gained...
-
 299Security Tools
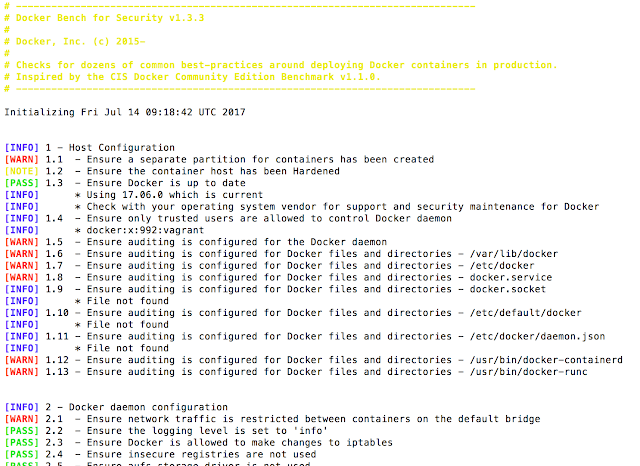
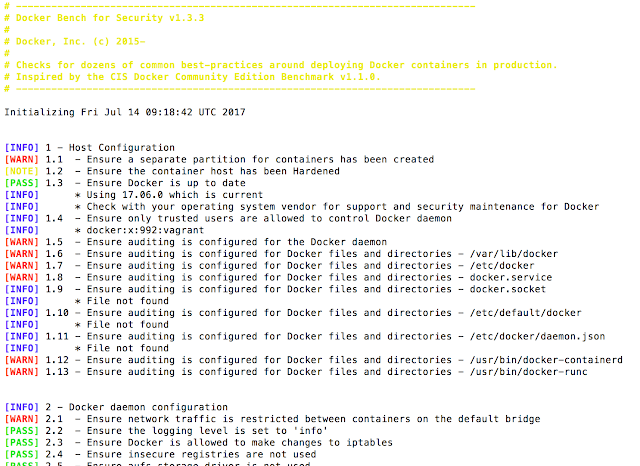
299Security ToolsThe Docker Bench For Security – A Script That Checks For Dozens Of Common Best-Practices Around Deploying Docker Containers In Production
The Docker Bench for Security is a script that checks for dozens of common best-practices around deploying Docker containers in production. The...






