Posts By root
-

 262Data Security
262Data SecurityUSB Killer Version 2.0 is Here to Burn and Destroy Your Computer
The maker of USB Killer is here with the USB Killer version 2.0 – a more advanced version of the computer frying...
-

 186Hacked
186HackedUSB Killer Version 2.0 Burns and Destroys Your Computer
Short Bytes: The maker of USB Killer is here with the USB Killer version 2.0 – a more advanced version of the...
-

 313How To
313How ToHow to Find Your Lost or Stolen Laptop?
Having your laptop stolen is the biggest nightmare anyone can face in the era of our gadget-centric lives. Here are some ways...
-
 253Hacked
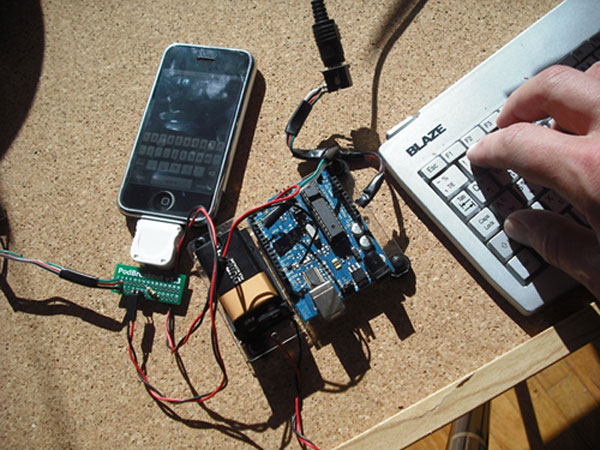
253HackedCrypto Backdoor Isn’t The Only Way To Hack Into Your iPhone
Short Bytes: Crypto backdoor entry isn’t the only way for the cops to access your data. You think your iPhone is the...
-

 88Data Security
88Data SecurityHackers can steal your BRAIN WAVES
Depressingly familiar and stupid mistakes in EEG kit, health org’s storage of recorded brains. BruCon: Behold the future: attackers can already get...
-

 96Malware
96MalwareMalware attack targets America’s Thrift Stores
America’s Thrift Stores said this week that it has been the victim of a malware-driven cyberattack by Eastern European criminals who stole...
-

 174Data Security
174Data SecurityCops Don’t Need a Crypto Backdoor to Get Into Your iPhone
The privacy community scored a victory in a year-long battle over the future of encryption: In internal discussions, the White House quietly...
-

 303News
303NewsSomeone Hacked Uniformed Services University and Leaked Their Credentials Online
A hacker going with the online handle of Kuroi SH hacked and defaced several domains of the United States based Uniformed Services...
-

 376Cyber Events
376Cyber EventsGreat Firewall of China at Work, Apple News May Have Been Blocked
Apple news (Currently in testing mode) has been taken down in China by the company itself. The reason behind this seems obvious:...
-
 313Hacked
313Hacked10 Steps To Defeat Hacking Attacks (And What To Do After You’ve Been Hacked)
Short Bytes: In the third article of the “Steps to Effective Security” series, I’ll tell you 10 steps to defeat hacking attacks and...
-

 283Data Security
283Data SecurityHackers Can Steal Corporate Passwords Through Cisco’s WebVPN Service Backdoor
Researchers identified a flaw in Cisco’s WebVPN — Hackers managed to install backdoors via two methods on the service — This weakness...
-

 84Data Security
84Data SecurityUS Ports – Cyber attacks can cause the release of dangerous chemicals
US Ports are still vulnerable to cyber attacks that release dangerous chemicals, cybersecurity in the maritime industry is crucial for Homeland security....
-

 93Data Security
93Data SecurityVariants now spawning off new Android SMS malware
AndroidOS.SmsThief does what it says on the tin – acts as a thief through SMS, on Android. Mobile network security and threat...
-
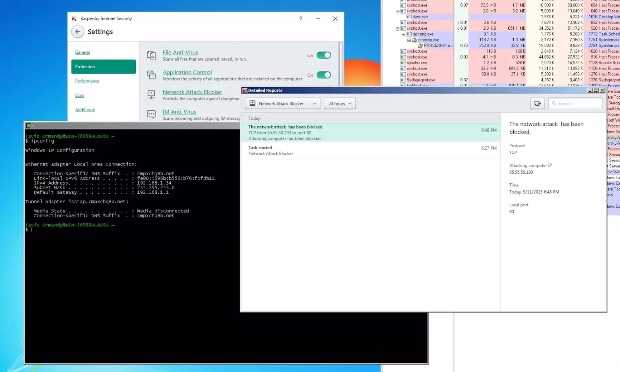
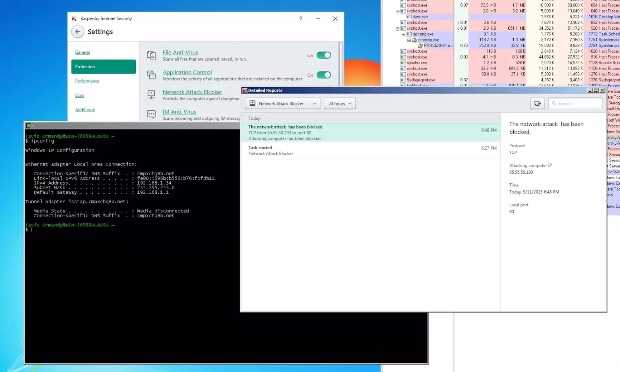 148Vulnerabilities
148VulnerabilitiesKaspersky Antivirus Fixes Bug That Allowed Attackers to Block Windows Update and Others Services
Attackers could have fooled Kaspersky antivirus in blocking Windows Update or some of its own update servers A vulnerability that allowed abuse...
-

 198Malware
198MalwareZeus Trojan and MWI Exploit Kit Used Against Israeli Public Sector
Security vendor interrupts hacking campaign targeting Israeli security firms, government agencies, and hospitals.Security experts have identified and isolated a series of attacks...
-

 109Vulnerabilities
109VulnerabilitiesBoffin’s easy remote hijack hack pops scores of router locks
Singaporean telco’s customer premises equipment is a gateway to security hell. Thousands of routers mandated for use by a major Singaporean telco...
-
 346Lists
346Lists10 Inventions That Make Nikola Tesla One Of The Greatest Scientists Of All Time
Short Bytes: Nikola Tesla, who is regarded as of the greatest scientists of all times, has gifted the world in every possible way...
-
 246Hacked
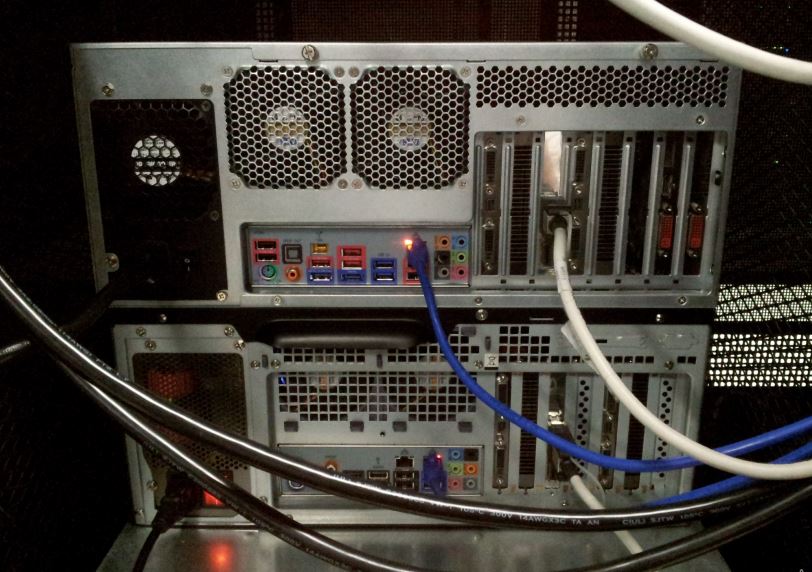
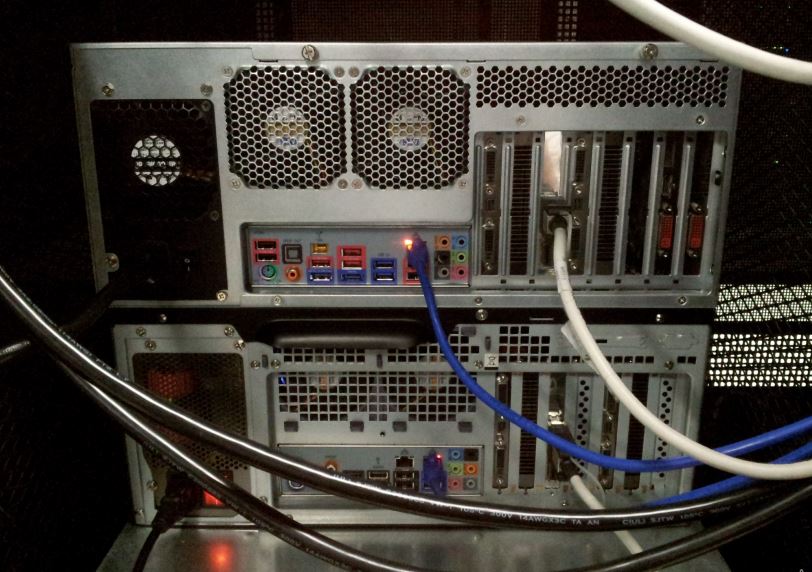
246HackedThis Computer Cluster Cracks Every Windows Password in 5.5-hours or Less
Short Bytes: A password-cracking expert has created a new computer cluster that cycles about 350 billion guesses per second and it can crack...
-

 218News
218News20 Sites to Download just about everything
Download Free Software,Movies, Music, Templates, WordPress themes, Blogger Themes and Icon pack with these websites. Theses are totally free websites for any...
-
 234Geek
234GeekLearn it Faster: The Complete Linux Kernel in a Single Map
Short Bytes: Today, we are sharing an interactive Linux Kernel map that will teach you the basics and understand the various subsystems....
-

 240Hacked
240HackedSurprise: For the First Time, USA Asked and China Arrested Hackers
Short Bytes: The Chinese government has taken an unprecedented step to comply with a U.S. request and arrest some hackers suspected of hacking...






