Posts By root
-
 255Vulnerabilities
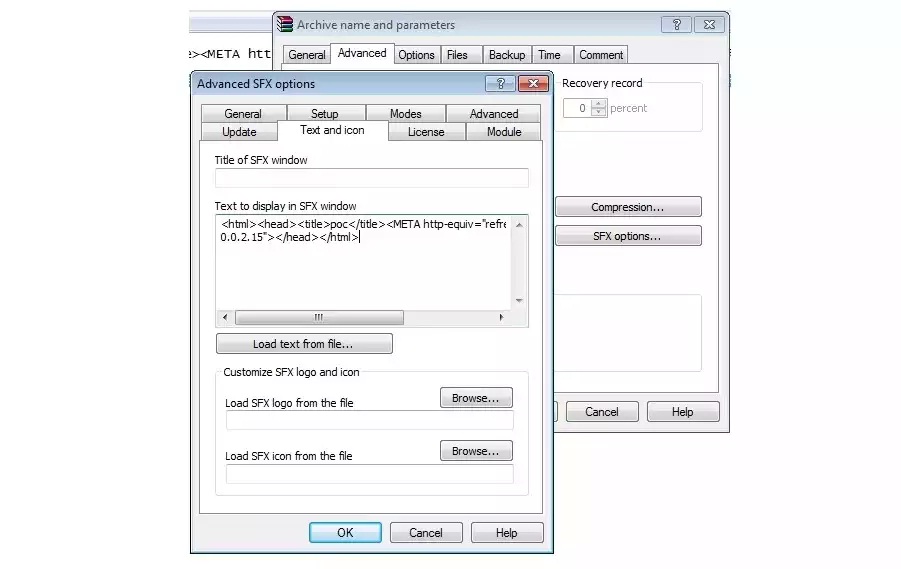
255VulnerabilitiesLatest Version of WinRAR Plagued by Dangerous Security Bug
WinRAR, the popular file compression and decompression utility, has a security vulnerability that allows attackers to remotely execute code on the user’s...
-

 293Geek
293GeekWindows Registry now Providing Shelter to Destructive Kovter Malware
Kovter Trojan can hide in Windows registry and does not need to be stored on the computer’s hard drive- claims Symantec —...
-

 98Malware
98MalwareDyreza Trojan Targeting IT Supply Chain Credentials
The Dyreza Trojan long ago ceased its exclusive focus on stealing banking credentials, and has been blamed for its part in attacks...
-

 266Data Security
266Data SecurityEdward Snowden joins Twitter and follows NSA
Fugitive US intelligence contractor Edward Snowden has opened an account on the social network website Twitter. His opening tweet was: “Can you...
-
 306Hacked
306HackedWelcome to the Darknet: The Underground for the “Underground”
Short Bytes: Do you know about the Darknet and TOR? Here’s an interesting piece of information if you are interested in the...
-

 408How To
408How ToGetting Started With Raspberry Pi – Get Everything You’ll Need (Part – 2)
Short Bytes: In the second article of Getting Started With Raspberry Pi series on fossBytes, I’ll be telling you about all the...
-

 182Data Security
182Data SecurityPirate Bay co-founder Gottfrid Svartholm Warg—aka Anakata—exits prison
Pirate Bay is online and playing a game of cat and mouse with IP regulators. Pirate Bay co-founder Gottfrid Svartholm Warg was released...
-
 308Hacked
308HackedMicrosoft Explains: “We Are Not Spying On You With Windows 10”
Short Bytes: Finally, Microsoft takes some time to address the widespread Windows 10 privacy concerns. In a blog post on Windows.com, a...
-
 164Malware
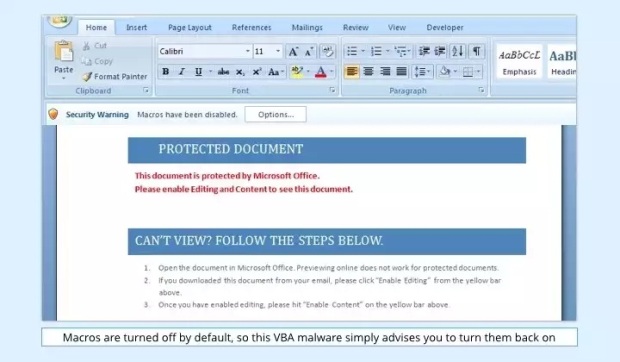
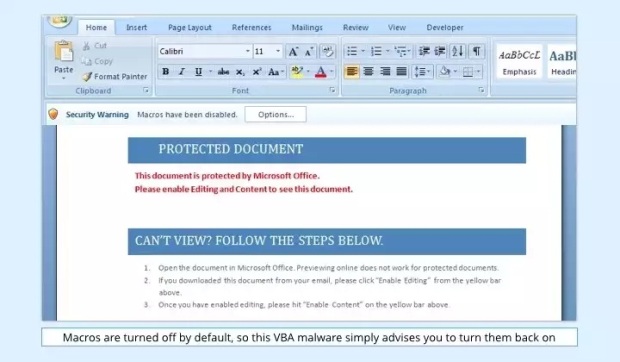
164MalwareVBA Malware Makes a Comeback Inside Booby-Trapped Word Documents
VBA stands for Visual Basic for Applications and is a programming language developed by Microsoft to help programmers create Windows applications using...
-

 163How To
163How ToTurn Off Wi-Fi Assist in iOS 9 As It Sucks All Your Data
Short Bytes: iOS 9 has a new feature Wi-Fi Assist that sucks your cellular data if the W-Fi coverage in your area...
-

 269Hacked
269HackedThe Pirate Bay Founder Finally Released From Prison After 3 Years
Short Bytes: The Pirate Bay co-founder Gottfrid Svartholm Warg is truly free again. Kristina Svartholm, his mother, announced the release on Twitter this Monday. The...
-

 128Incidents
128IncidentsHack attacks strike top porn sites
A malicious advertising campaign has targeted top adult sites like Pornhub and YouPorn. Several of the world’s most popular pornographic websites were...
-

 92Data Security
92Data SecurityStoring secret crypto keys in the Amazon cloud? New attack can steal them
Technique allows full recovery of 2048-bit RSA key stored in Amazon’s EC2 service. Piercing a key selling point of commercial cloud computing...
-

 176Malware
176MalwareTrojan Found Pre-Installed on Some Android Devices
A trojan strand targeting Android devices has been found coming pre-installed inside the firmware of some Android smartphones by Dr.Web, a Russian-based...
-

 114Data Security
114Data SecurityNew DDoS attack uses smartphone browsers to flood site with 4.5bn requests
Researchers have found that smartphone browsers can deliver a powerful flooding attack. Researchers suspect a mobile advertising network has been used to...
-
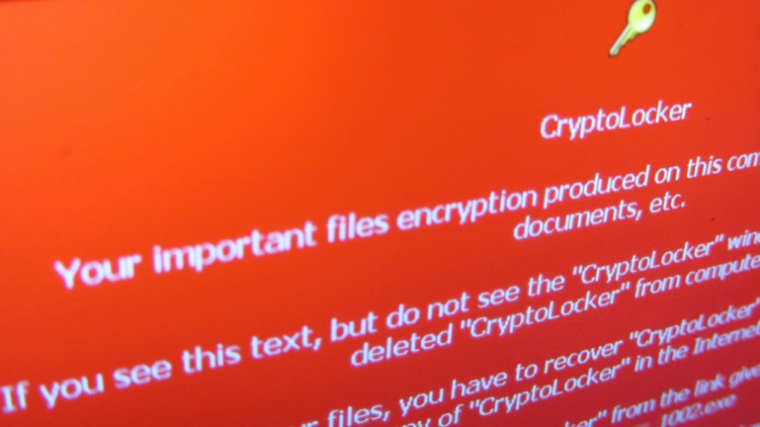
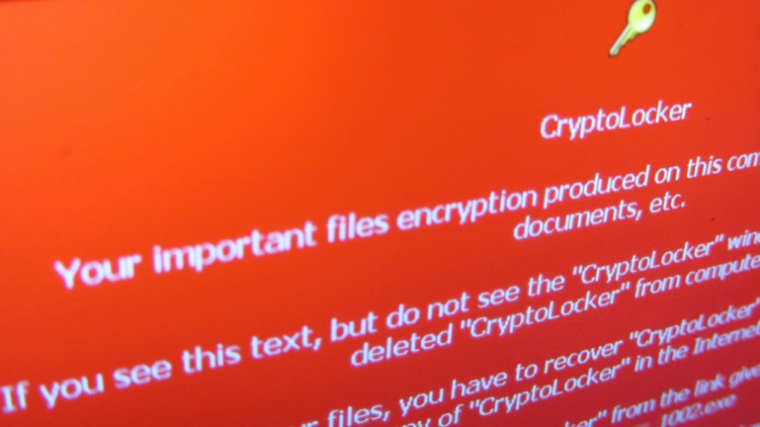 238Cyber Crime
238Cyber CrimeHackers delivering ransomware virus in package delivery e-mails
A new ransomware email campaign detected in the fake email messages sent by either PostNord or Post Denmark, identified as Cryptolocker2. Hackers...
-
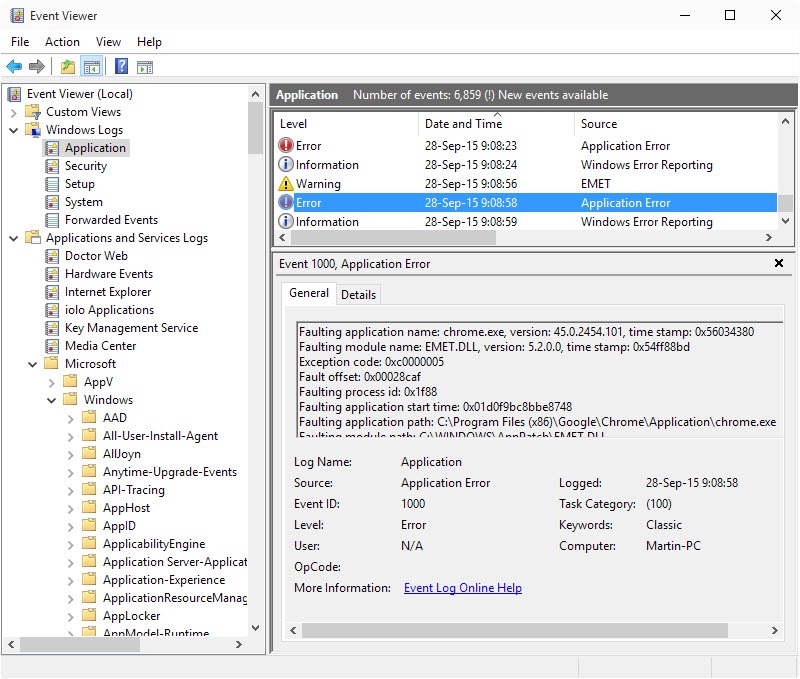
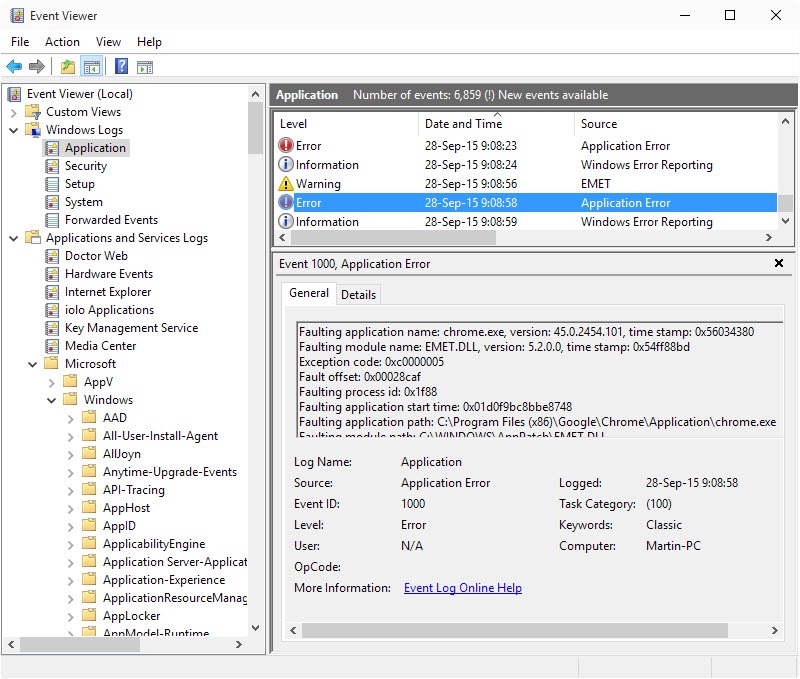 185Vulnerabilities
185VulnerabilitiesAdvanced Microsoft Enhanced Mitigation Experience Toolkit (EMET) Tips
The Microsoft Enhanced Mitigation Experience Toolkit, short EMET, is an optional download for all supported client and server versions of Microsoft’s Windows...
-

 127Vulnerabilities
127VulnerabilitiesVeraCrypt 1.15 fixes two recently reported TrueCrypt vulnerabilities
Yesterday’s update of the encryption software VeraCyrpt fixed two vulnerabilities that security researcher James Forshaw discovered in TrueCrypt’s source code. TrueCrypt, which...
-
 122Malware
122MalwareIntelligent system to check malware hidden in shortened Twitter URLs
Tool to check malware in Twitter URLs to be tested during European Football Championships next summer. An intelligent system has been created...
-
 78Data Security
78Data SecurityRephone lets you hack a cellular radio into anything
Yesterday at the Maker Faire in New York, we had a chance to check out the Rephone, a clever little project that...
-

 186Opinion
186OpinionESET Presentations at Virus Bulletin 2015
Some of the good things in store for those attending Virus Bulletin 2015.






