Posts By root
-

 102Privacy
102PrivacyBluetooth fitness trackers ‘a threat to privacy’
Devices using Bluetooth Low Energy (BLE) to transmit their data can be intercepted by hackers, potentially exposing a trove of fitness data...
-

 387Password
387PasswordDissecting Linux/Moose: a Linux Router‑based Worm Hungry for Social Networks
A malware family that primarily targets Linux-based consumer routers but that can infect other Linux-based embedded systems in its path: Dissecting Linux/Moose.
-
 219Cyber Crime
219Cyber CrimeMoose – the router worm with an appetite for social networks
A new worm is infecting routers in order to commit social networking fraud, hijacking victims' internet connections in order to "like" posts...
-
 267Geek
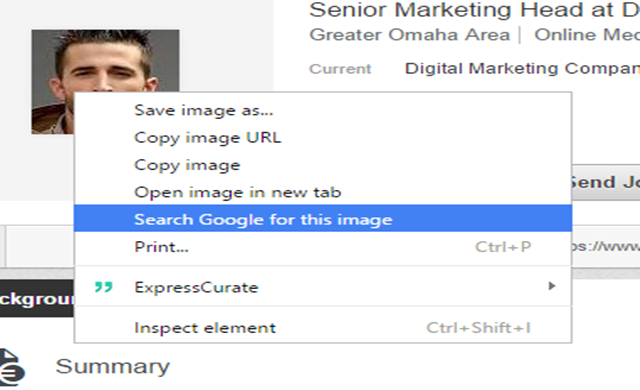
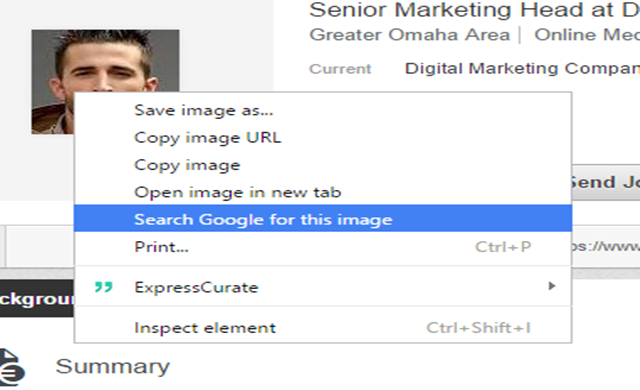
267GeekIdentifying Fake Social Media Profiles Possible with Google Image Search
Creating fake social media accounts has been the favorite trick of hackers and scammers for interacting with potential victims. However, thanks to...
-

 302Cyber Events
302Cyber EventsTeen hires attacker to DDoS his school district
A high school boy might have to face state and federal charges for allegedly hiring a third party and launching a DDoS...
-

 233Geek
233GeekDoes Wi-Fi Makes People Sick? Probably Yes!
From using PCs and cell phones to watch online movies and playing games, wireless technology has advanced greatly and made life easier...
-

 396News
396NewsHackers target Bitcoin Exchange BitFinex’ Hot Wallet
Reportedly BitFinex was hacked but due to strict security measures implementation just minimal amount was lost. BitFinex keeps more than 99.5% of...
-

 291How To
291How ToTips To Keep Your Android Device Safe and Sound
It would not be an exaggeration to say that the present age is the age of smartphones. They have invaded our lives...
-

 151Hacked
151HackedMozilla: Firefox Tracking Protection Speeds Up Web Pages by 44%
Do you know that not all web sites honor the native Do Not Track feature of your web browser? Even in the...
-

 68Cyber Crime
68Cyber Crime5 hackers who came over from the dark side
Five reformed hackers who turned their lives around to help in the fight against cybercrime, leaving their blackhat past behind.
-
 156Hacking Tutorials
156Hacking Tutorials6 Ways to Secure a Wireless Wi-Fi Network
Wireless Networking (Wi-Fi) has made it so easy for anyone to use Internet on your computer, mobile phones, tablets and other wireless...
-

 265Hacked
265HackedNSA Prepares to SHUT DOWN Mass Phone Tracking Program
As a result of a midnight session, the American Senate has voted down the USA Freedom Act- the basis of NSA’s mass...
-

 285News
285NewsAnonymous Breaches Thailand Senate Website against Human Trafficking
The online hacktivist Anonymous breached into the official website of Thailand Senate and Public Health Ministry, ending up leaking login credentials against country’s alleged...
-

 236News
236NewsWebsite of Uzbek Embassy in Kuwait hacked by anti-Assad Hacker
The anti-Bashar Al Assad hacker from Syria hacked into the official website of Uzbekistan Embassy in Kuwait and demanded governments around the world...
-
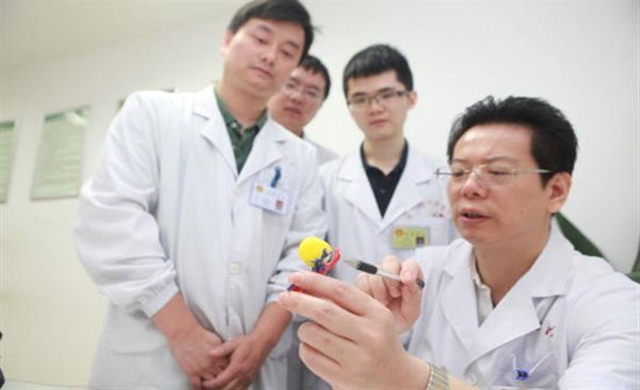
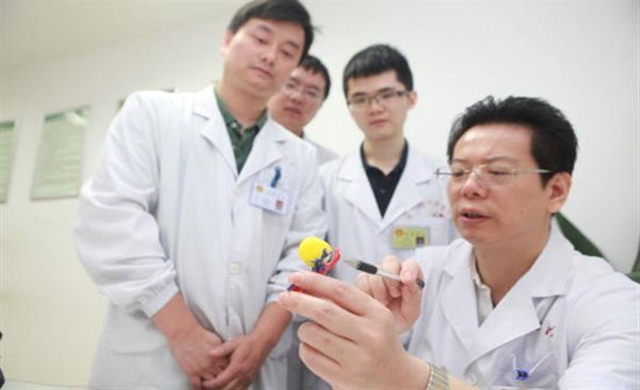 288Geek
288GeekMiracle Miracle! A woman’s kidney tumor cured by 3D printing
When it’s about performing surgeries on vital organs, today’s advanced imaging techniques such as CT scans, MRIs and ultrasound machinery have made...
-

 318Surveillance
318SurveillanceThese Iris scanners can now identify people from 40 feet away
It’s a high point for “Biometric technology” as in the latest advancement now. It is possible to record data about an individual’s...
-
 178News
178NewsAdult dating site hack reveals sexual secrets of millions, including feds and cops
An Adult Dating website AdultFriendFinder is the newest victim of a huge hack that exposed the personal information, with sexual orientation details,...
-

 302Geek
302GeekInjured Turtle Gets 1st 3D Printed Titanium Jaw Implant
A big day in the history of animal prostheses has arrived, Turkey’s medical 3D printing company provided an injured turtle with a...
-
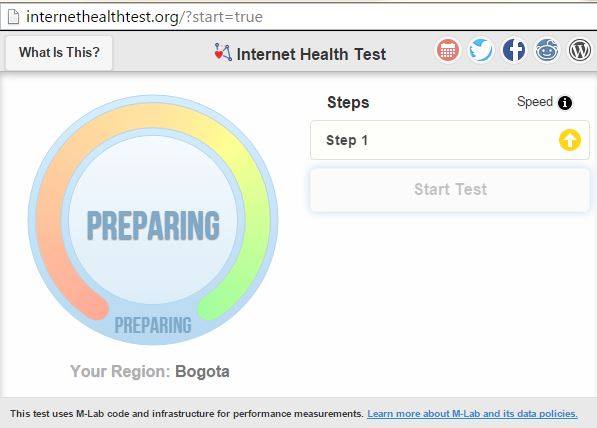
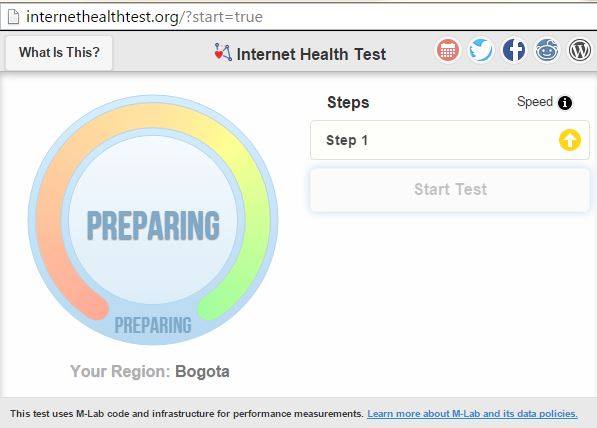 204How To
204How ToHow to Check if Your ISP is Violating Net Neutrality and Slowing You Down
The net neutrality debate continues to evolve and now the common people have a better understanding of the topic. Here at fossBytes,...
-
 330Cyber Events
330Cyber EventsHackers leak Confidential data from Saudi Ministry of Foreign Affairs! It’s Crazy
Yemen Cyber Army claims it breached into the Saudi Ministry of Foreign Affairs server and leaked plain-text login credentials of Saudi officials...
-

 89Cyber Crime
89Cyber CrimeThe wider world of security research output: webinars
Security research is published in many forms. For example, there are live and recorded webinars that cover a range of cybersecurity topics.






