Posts By root
-
 315Data Security
315Data Security2500+ GTA V PC Accounts Rumored to be hacked but Rockstar Denies
Grand Theft Auto 5’s hub Rockstar Social Club was rumored to have been hacked. In reality, it is safe and another unnamed site...
-
 188Geek
188Geek10 Best Features in Ubuntu 15.04, Favorite Platform of Developers
This year’s first Ubuntu release – Ubuntu 15.04 – is being loved by all. Ubuntu is the favorite platform of developers and it...
-
Secure Coding
How to create a keylogger in notepad
Here is a basic keylogger script for beginners to understand the basics of how keylogging works in notepad. This script should be...
-

 69Cyber Crime
69Cyber CrimeCanada commits $36.4 million to cybersecurity measures in 2015 budget
The Conservatives' 2015-16 federal budget sees some investment in security, with $36.4 million promised over five years to address cybersecurity threats.
-
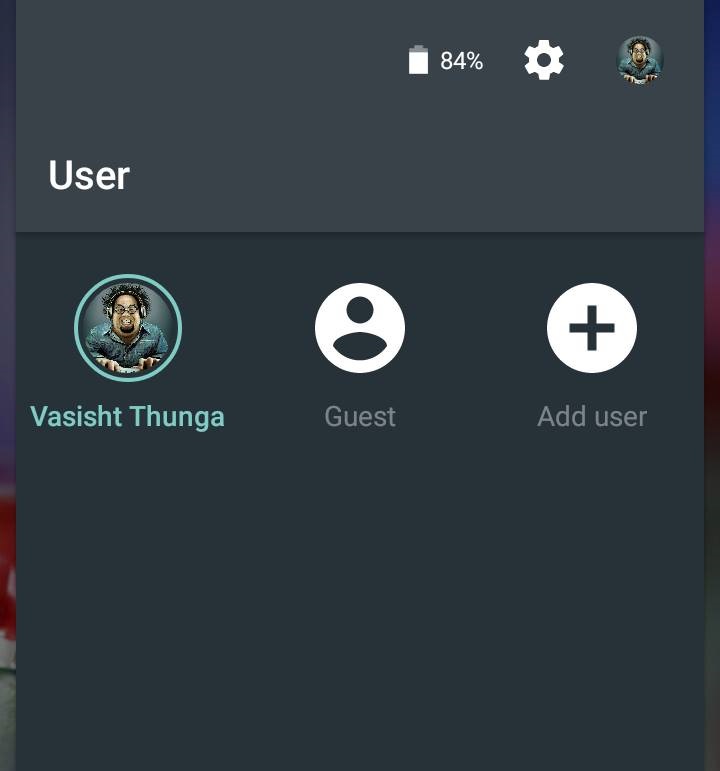
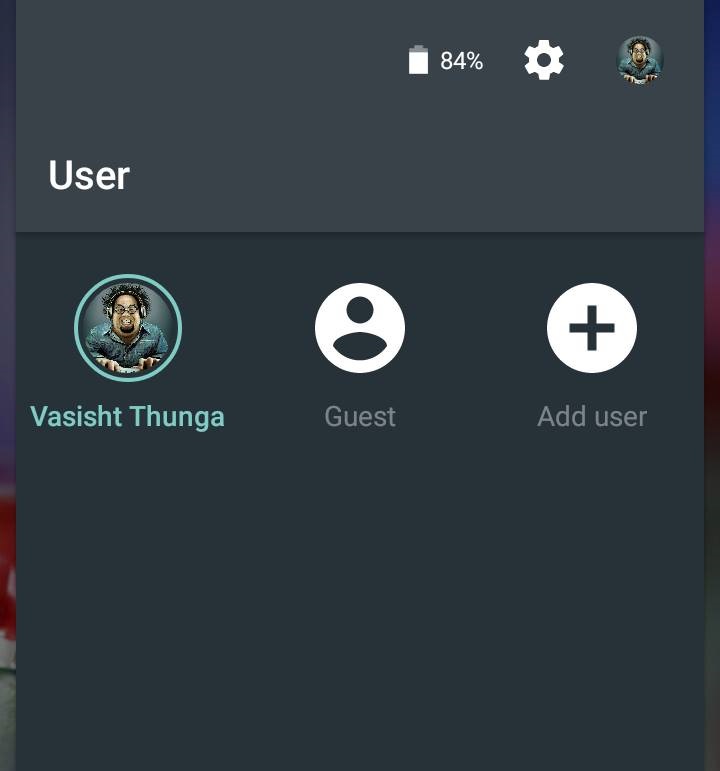 203How To
203How ToHow To Enable Guest Mode On Android
Android 5.0 Lollipop lets you quickly switch to a separate guest profile. This guest user will not contain your personal data like...
-
 123Data Security
123Data SecuritySerious Security Flaw found in 1,500 iOS apps—Checkout if your iPhone is at risk
Researchers have identified a serious vulnerability in at least 1,500 iOS apps. This security flaw has made the apps exploitable by hackers...
-
 259Cyber Events
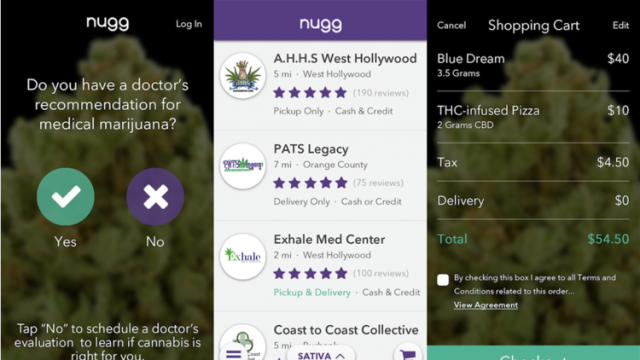
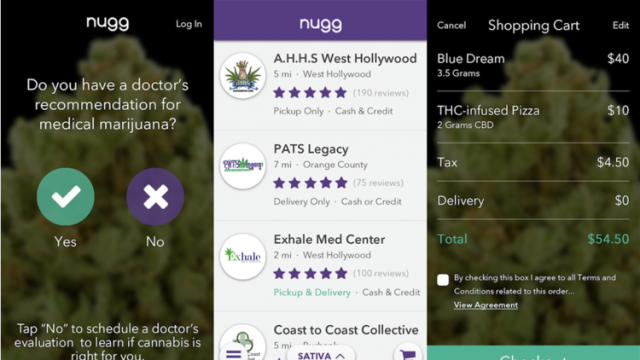
259Cyber EventsNugg App Lets You Order Medical Marijuana From Your Smartphone
Los Angeles and Orange Counties patients could order medical marijuana through Nugg, a new app. They may even schedule marijuana deliveries and...
-

 118Geek
118GeekWoman Suing Google For Losing “thousands” due to Google Play Store hack
Susan Harvey claims Google never reimbursed her even after admitting that she did not make the purchases. Madera, CA-based woman Susan Harvey...
-

 433Privacy
433PrivacyThe dirty secrets of webcam‑hacking peeping toms and sextortionists
Virtually every computer sold today comes with a dirty little secret. It can spy on you. Learn more, and how to protect...
-
 213Hacked
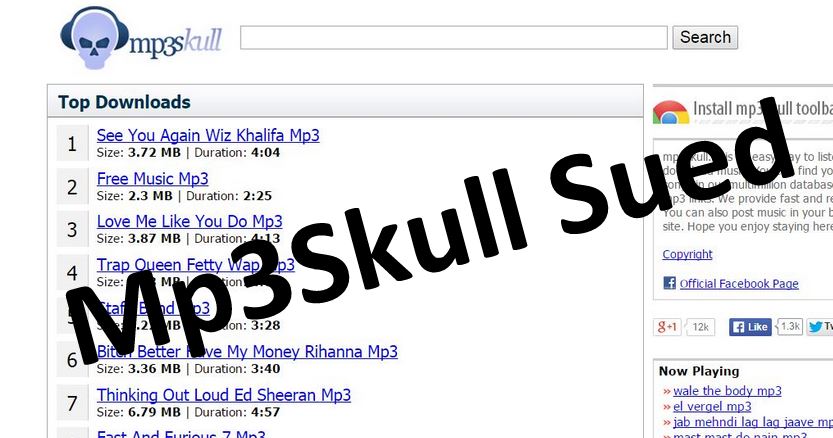
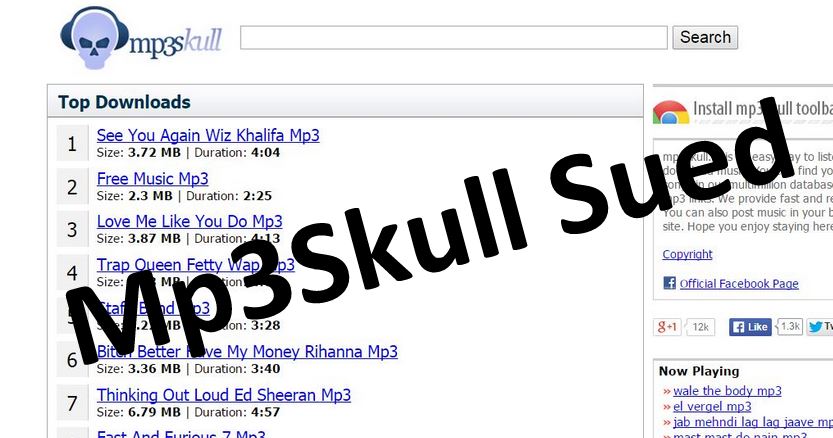
213HackedMP3 Download Website MP3Skull Being Sued Over Mass Piracy
MP3Skull is one of the most popular websites being used by people to download music illegally. TF reports that in a combined...
-

 416Malware
416MalwareNew malware ‘Punkey’ detected in new point‑of‑sale attack
A new advanced malware program targeting point-of-sale terminals is putting customer credit card details at risk, following a number of similar attacks...
-

 339Data Security
339Data SecurityXSS Vulnerability Found in Famous WordPress Plugins
Researchers have identified a relatively “common” cross-site scripting flaw (XSS) in some famous WordPress plugins — A coordinated plugin update has been released to...
-

 278Hacked
278HackedHow New Zealand and NSA Plotted Hack on China
China’s foreign ministry has expressed serious concerns over the reports of hacking attacks on China planned by New Zealand and NSA in recent...
-

 422Mobile Security
422Mobile Security1,500 iOS apps open to simple man‑in‑the‑middle attacks
Around 1,500 apps for iPhone and iPad contain an HTTPS vulnerability making it 'trivial' for hackers to perform man-in-the-middle attacks to steal...
-

 289News
289NewsAnonymous Hacks Israeli Arms Importer Site, Leaks Massive Client Login Data
Online hacktivist Anonymous has breached into the website of an Israeli arm importer and manufacture Fab-Defanse (fab-defense.com) and leaked login credentials plus personal...
-

 277Data Security
277Data SecurityFlash Player Bug Records Audio and Video without User Permission
Researchers have identified a vulnerability in some Adobe Flash Player versions that can be exploited by attackers for spying on users having...
-

 545How To
545How ToGoogle Now Lets You Download Your Entire Search History, Here is How To Do This
image: Lifehacker Google now allows you to export and download your entire search history in no time. Last year Google tested a...
-
 287Cyber Events
287Cyber EventsBrazil will sue Facebook for blocking picture of indigenous woman
Brazilian Ministry of Culture is planning to sue Facebook on blocking the picture of an Indian woman from 1909 just because her...
-
 327Geek
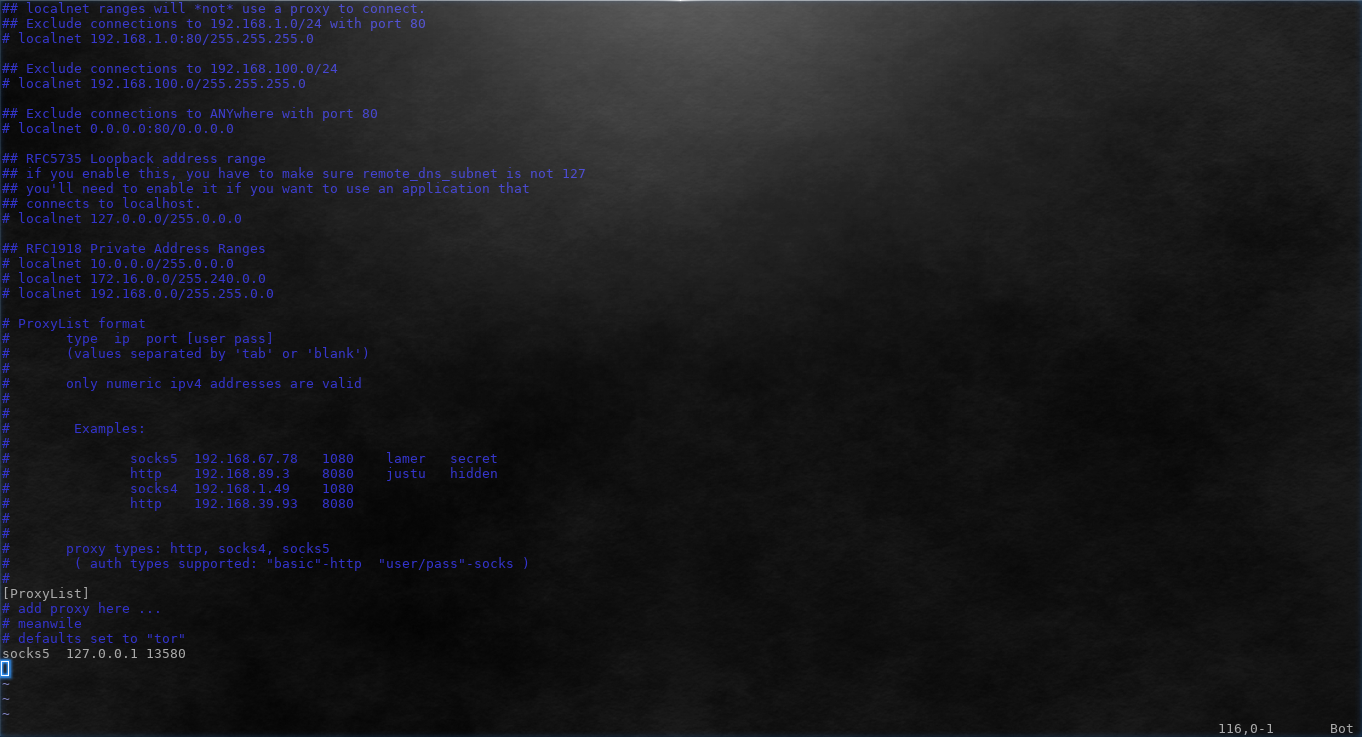
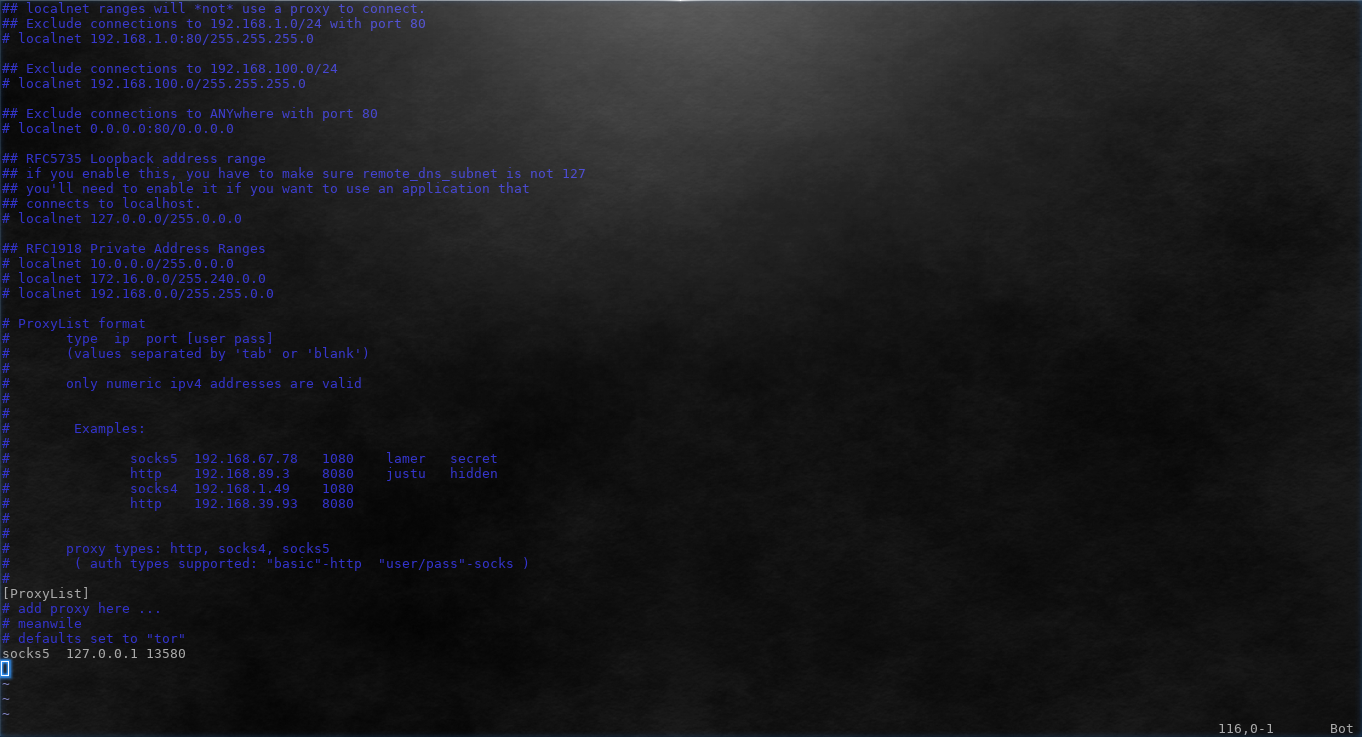
327GeekHow to Use Proxychains to Run Applications Behind Proxy
Some applications do not support proxy by default. Other applications might support HTTP proxy but fail when using SOCKS. As Tor provides...
-

 83Cyber Crime
83Cyber CrimeAustralian infosec body lobbies for mandatory security baseline
Australia's infosec industry is lobbying for a mandatory security baseline to ensure basic IT standards are met across the country, with penalties...
-

 188Cyber Crime
188Cyber CrimeTarget agrees to $19 million data breach settlement with MasterCard
Target has ended its dispute with MasterCard over the retail giant's 2013 data breach by agreeing to a $19 million reimbursement to...






