Posts By root
-
 598Malware
598MalwareChina-Linked Hackers Target Myanmar’s Top Ministries with Backdoor Blitz
The China-based threat actor known as Mustang Panda is suspected to have targeted Myanmar’s Ministry of Defence and Foreign Affairs as part...
-

 554Data Breach
554Data BreachTop Security Posture Vulnerabilities Revealed
Each New Year introduces a new set of challenges and opportunities for strengthening our cybersecurity posture. It’s the nature of the field...
-

 3.3KMalware
3.3KMalwareNew ZLoader Malware Variant Surfaces with 64-bit Windows Compatibility
Threat hunters have identified a new campaign that delivers the ZLoader malware, resurfacing nearly two years after the botnet’s infrastructure was dismantled...
-
 837Vulnerabilities
837VulnerabilitiesJuniper Networks Releases Urgent Junos OS Updates for High-Severity Flaws
Juniper Networks has released out-of-band updates to address high-severity flaws in SRX Series and EX Series that could be exploited by a...
-

 697Data Security
697Data SecurityExploit code: How the New Jenkins Vulnerability Could Compromise Your Data
Recent news about a critical vulnerability in Jenkins, identified as CVE-2024-23897, has raised significant concerns in the cybersecurity community. This vulnerability has...
-
 2.3KVulnerabilities
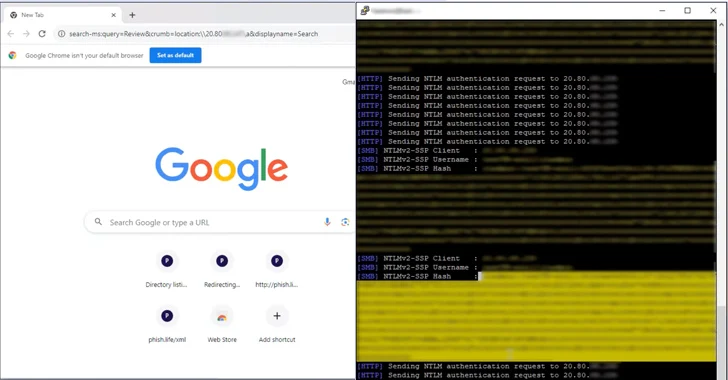
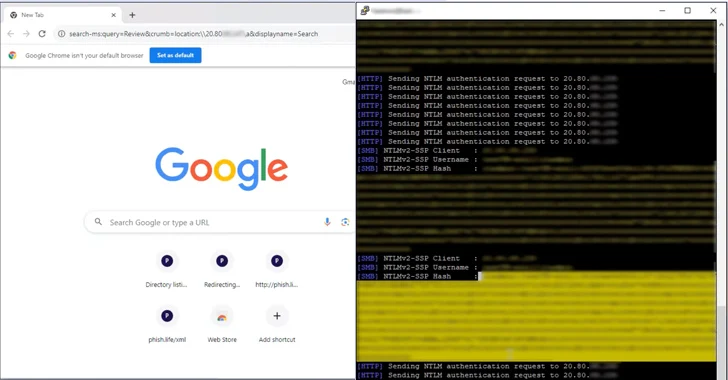
2.3KVulnerabilitiesResearchers Uncover How Outlook Vulnerability Could Leak Your NTLM Passwords
A now-patched security flaw in Microsoft Outlook could be exploited by threat actors to access NT LAN Manager (NTLM) v2 hashed passwords...
-

 2.3KMalware
2.3KMalwareRiding the AI Waves: The Rise of Artificial Intelligence to Combat Cyber Threats
In nearly every segment of our lives, AI (artificial intelligence) now makes a significant impact: It can deliver better healthcare diagnoses and...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesAlbabat, Kasseika, Kuiper: New Ransomware Gangs Rise with Rust and Golang
Cybersecurity researchers have detected in the wild yet another variant of the Phobos ransomware family known as Faust. Fortinet FortiGuard Labs, which...
-

 4.6KMalware
4.6KMalwareMalicious PyPI Packages Slip WhiteSnake InfoStealer Malware onto Windows Machines
Cybersecurity researchers have identified malicious packages on the open-source Python Package Index (PyPI) repository that deliver an information stealing malware called WhiteSnake...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesAllaKore RAT Malware Targeting Mexican Firms with Financial Fraud Tricks
Mexican financial institutions are under the radar of a new spear-phishing campaign that delivers a modified version of an open-source remote access...
-

 751Malware
751MalwareMalicious Ads on Google Target Chinese Users with Fake Messaging Apps
Chinese-speaking users have been targeted by malicious Google ads for restricted messaging apps like Telegram as part of an ongoing malvertising campaign....
-

 1.0KCyber Attack
1.0KCyber AttackMicrosoft Warns of Widening APT29 Espionage Attacks Targeting Global Orgs
Microsoft on Thursday said the Russian state-sponsored threat actors responsible for a cyber attack on its systems in late November 2023 have...
-

 2.4KMalware
2.4KMalwareRussian TrickBot Mastermind Gets 5-Year Prison Sentence for Cybercrime Spree
40-year-old Russian national Vladimir Dunaev has been sentenced to five years and four months in prison for his role in creating and...
-

 3.5KVulnerabilities
3.5KVulnerabilitiesCritical Cisco Flaw Lets Hackers Remotely Take Over Unified Comms Systems
Cisco has released patches to address a critical security flaw impacting Unified Communications and Contact Center Solutions products that could permit an...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesSystemBC Malware’s C2 Server Analysis Exposes Payload Delivery Tricks
Cybersecurity researchers have shed light on the command-and-control (C2) server workings of a known malware family called SystemBC. “SystemBC can be purchased...
-

 3.1KVulnerabilities
3.1KVulnerabilitiesCritical Jenkins Vulnerability Exposes Servers to RCE Attacks – Patch ASAP!
The maintainers of the open-source continuous integration/continuous delivery and deployment (CI/CD) automation software Jenkins have resolved nine security flaws, including a critical...
-
 799Malware
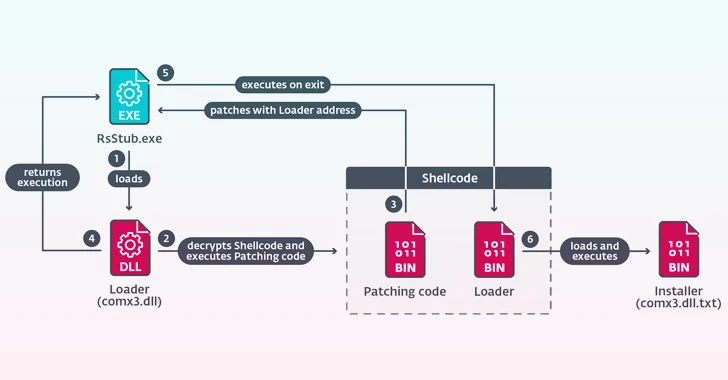
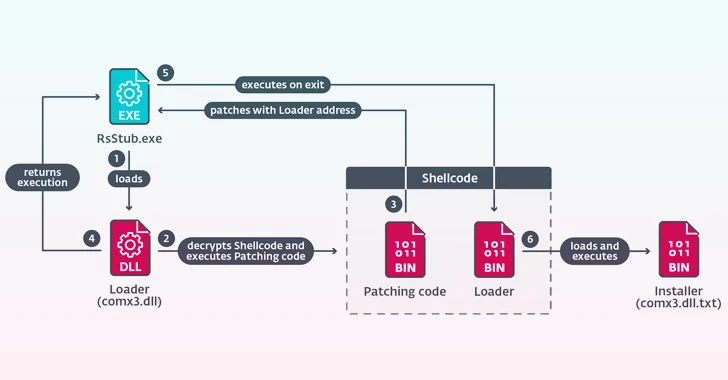
799MalwareChina-backed Hackers Hijack Software Updates to Implant “NSPX30” Spyware
A previously undocumented China-aligned threat actor has been linked to a set of adversary-in-the-middle (AitM) attacks that hijack update requests from legitimate...
-
 2.2KMalware
2.2KMalwareNew CherryLoader Malware Mimics CherryTree to Deploy PrivEsc Exploits
A new Go-based malware loader called CherryLoader has been discovered by threat hunters in the wild to deliver additional payloads onto compromised...
-

 424Data Breach
424Data BreachTech Giant HP Enterprise Hacked by Russian Hackers Linked to DNC Breach
Hackers with links to the Kremlin are suspected to have infiltrated information technology company Hewlett Packard Enterprise’s (HPE) cloud email environment to...
-
 312Vulnerabilities
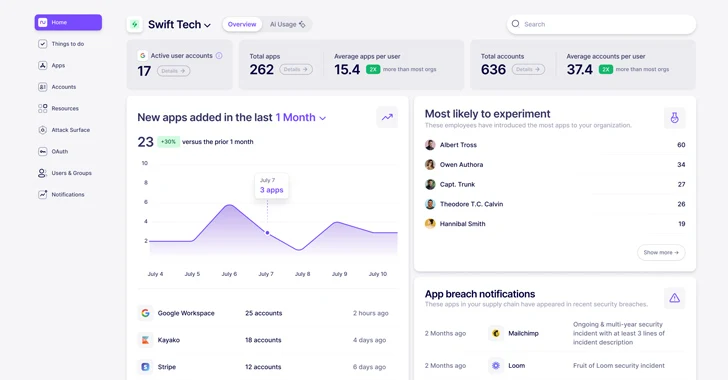
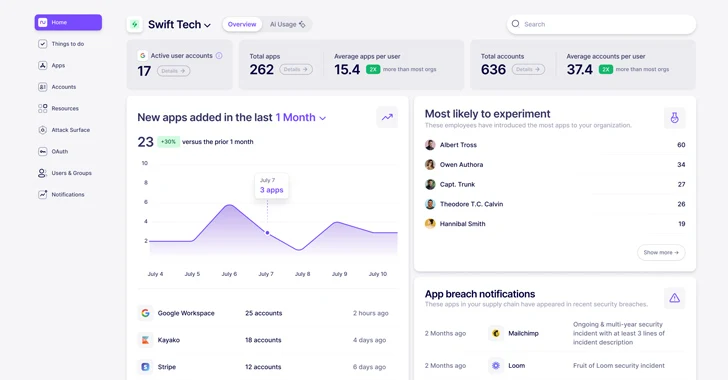
312VulnerabilitiesWhat is Nudge Security and How Does it Work?
In today’s highly distributed workplace, every employee has the ability to act as their own CIO, adopting new cloud and SaaS technologies...
-

 2.9KMalware
2.9KMalwareKasseika Ransomware Using BYOVD Trick to Disarm Security Pre-Encryption
The ransomware group known as Kasseika has become the latest to leverage the Bring Your Own Vulnerable Driver (BYOVD) attack to disarm...






