Posts By root
-
Cyber Crime
‘Anonymous’ – Now accepting bitcoin tips
Can’t find a way to support a hacktivist with your l337 sK1LLz? Turns out they take tips, bitcoin tips. We mused awhile...
-
Cyber Crime
Google your own health record?
Is that possible? Well, a researcher with Identity Finder, Aaron Titus, believes so, since he says he managed to use internet searches...
-
Social Engineering
Malware De‑Cloaked
... people have been asking me about Google's interesting paper on Trends in Circumventing Web-Malware Detection...
-
Cyber Crime
1000 days of Conficker
Nearly three years old, the Conficker worm continues to pose a threat to PCs. Aryeh Goretsky wants to know why this is,...
-
Cyber Crime
PUAs: ESET’s Most Unwanted List
Aryeh Goretsky interviewed, as his paper on Possibly Unwanted Applications is published.
-
Android
Android malware: rapidly on the rise
I have an Android in my pocket as I type, with all kinds of cool apps ranging from GPS navigation to acoustic...
-
Cyber Crime
Hack wireless industrial sensors in a few easy steps
On the heels of the recent activity with Stuxnet, the industrial process control computer worm that targeted Iranian nuclear centrifuges, a Blackhat...
-
 436Malware
436MalwareWin32/Delf.QCZ:Trust Me, I’m Your Anti‑Virus
Among the many different trojans that spread on Facebook, something popped up recently that caught our particular attention. The threat, detected...
-
Cyber Crime
Hacktivism: not a get‑out‑of‑jail card?
What we're lacking here is a clear differentiation between types of "hacktivist" or, indeed, "activist": much of the commentary that's around at...
-
Password
Where there’s smoke, there’s FireWire
Forensic software developer PassWare announced a new version of its eponymous software forensics kit on Tuesday. Already several news sources are writing...
-
Hacking
50 ways to hack a website
Well, really there are far more, but the latest study from Imperva of 10 million attacks against 30 large organizations from January...
-
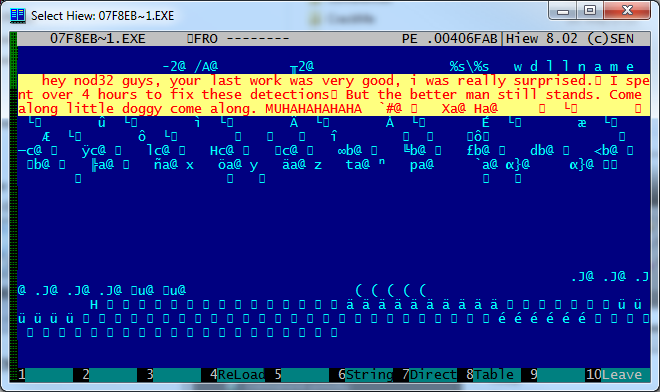
 136Malware
136MalwareCome along, little doggy, come along
The most common malware technique for avoiding detection is to create loads of “fresh” variants. Actually, the component that changes so frequently...
-
Hacking
Stuxnet: Broke Iranian nuclear centrifuges?
Or so the latest report from DEBKAfile states, claiming the Stuxnet worm broke numerous Iranian centrifuges by forcing them to overspeed, causing...
-
Android
Android apps: slow data leak?
With the proliferation of the data we hold on our mobile devices, it’s no wonder Neil Daswani, CTO of Dasient, says around...
-
Malware
Manga Management and Malware
...one Yasuhiro Kawaguchi was arrested yesterday on suspicion of "saving a virus on his computer," though the story suggests distribution of malware...
-
Hacking
‘Anonymous’ NATO data breach?
2 days ago, the FBI announced a series of raids resulting in arrests of alleged members of the hacking group ‘Anonymous’. Hoping...
-
 185Cyber Crime
185Cyber CrimeHodprot is a Hotshot
In their presentation “Cybercrime in Russia: Trends and issues” at CARO2011 -- one of the best presentations of the workshop, in my...
-
Scams
Free WiFi: Price? All your personal information
Sitting in an airport you rarely frequent, you grab your laptop and snap out a couple e-mails to send, and look, there’s...
-
Android
1 in 20 mobile devices infected next year?
The mobile devices of late have more compute power than the full desktop PC of yesteryear, and they fit it your pocket,...
-

 174Privacy
174PrivacyFacebook Video Calls powered by Skype
With Facebook's launch of video chat powered by Skype underway and enabling a new level of communication on its platform, we take...
-
Privacy
Google: your private profile – now public
Google, in an effort to get more squarely into the center of the social networking scene, is implementing a system where private...






