Posts By root
-
 146Malware
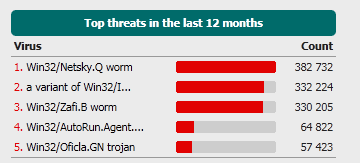
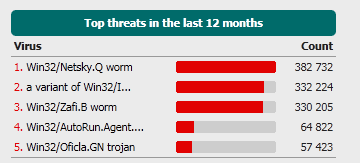
146MalwareThe more things change, the more they stay the same
It's something of a truism, that 'old viruses never die', and that certainly seems to be the case for some of the...
-
Hacking
Arizona DPS: hacked again – still – really?
On Wednesday we heard additional documents had been leaked from the Arizona Department of Public Safety (DPS). “Will this ever end?” has...
-
Cyber Crime
Facebook Facial Recognition – A picture is worth a thousand words
Facebook recently launched a facial recognition feature that allows you and others to “tag” photos with your name. As has been the...
-
Malware
Windows Rootkit Requires Reinstall?
In a ComputerWorld article Gregg Kaiser cites a Microsoft engineer as saying that the trojan that Microsoft calls “Popureb” digs so deeply...
-
Cyber Crime
SCADA still scary
"Infrastructure Attacks: The Next Generation?" now includes the speaker notes, which hopefully makes it more interesting and useful.
-
Cyber Crime
White House to double jail time for hackers?
The Obama administration seems intent on pushing for stiffer sentences for hackers caught endangering national security to 20 years prison time, doubling...
-

 423Privacy
423PrivacyLinkedIn Privacy: An Easy How‑to Guide to Protecting Yourself
Introduction LinkedIn is a social network platform whose specialty is connecting professionals together to build relationships and create business opportunity. Recently the...
-
Scams
419: UK lets the Good Times Roll
...It's a 419 (Advance Fee Fraud) message, of course. Stripped of the pseudo-governmental flim-flam, the core of the message is that they...
-
Cyber Crime
#1 Bitcoin Exchange Data Breached
Mt. Gox, the most popular Bitcoin exchange, has had a database compromised and user information stolen, sparking rapid devaluation and temporary exchange...
-
Hacking
Got Hacked? You have 48 hours to fess up
Or so the current legislation being proposed in a U.S. House of Representative subcommittee would like it. A hearing scheduled for today...
-
Hacking
I Can Neither Confirm nor Deny
As website appear to fall to hacks like the rain falls in Seattle, the question du jour doesn’t change from day to...
-
Cyber Crime
The Next Stuxnet
...the 'next Stuxnet' probably won't be any such thing, whatever we may choose to call it...
-
Cyber Crime
Why the IMF breach?
In the absence of any detailed information from the IMF itself, it's not surprising that most of the surmise around the attack...
-
 212Password
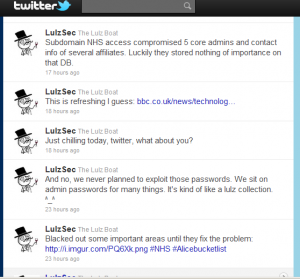
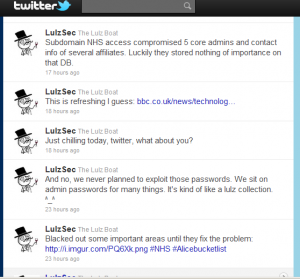
212PasswordLulzSec lulls the NHS: not such bad lads?
...on the Twitter account owned by LulzSec that they had turned their attention to the NHS. Curiously enough, they seem to have...
-
Password
A Nice Pair of Breaches
...here's a blog in stark contrast to Urban Schrott's blog about good password practice in Ireland ... Troy Hunt ran an analysis...
-
Cyber Crime
Passwords, passphrases and past caring
First: a link to another article for SC Magazine's Cybercrime Corner on password issues: Good passwords are no joke. However good your...
-
 144Cyber Crime
144Cyber CrimeBoys will be boys…
...whatever the hacker community's personal taste is in games and consoles, gamers are a tempting target...
-
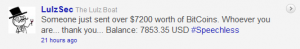
 112Cyber Crime
112Cyber CrimeBitcoin: P2P underground cyber currency?
Bitcoins, a self-generated hash-based peer-to-peer currency with no centralized regulating body, are on a stratospheric trajectory, will it replace traditional legal tender...
-
Cyber Crime
North Korea’s Overseas Cyber Warrior Training
It appears North Korea is expanding their cyber warrior savvy in a plan that includes sending the best and brightest of young...
-
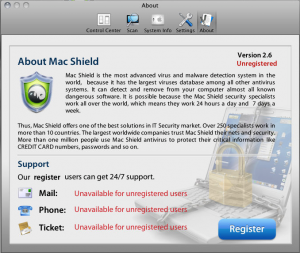
 327Mac
327MacMacDefender undergoes a name change, MacShield
The MacDefender malware has morphed again, now taking the guise of "MacShield." As in the case of its oldest sibling MacDefender,...
-
Cyber Crime
Real War – The Next Cyber Frontier
Cyber Security pundits have been keenly watching the development of nascent state targeted attacks such as the Stuxnet worm with interest for...






