Hackers Repository
-

 4.3K
4.3KFrom Code to Color – Understanding User Interface
Developing the next great app or a fully functional website is something every developer strives for. Crafting lines of code that roll...
-

 3.8K
3.8K5G new vulnerabilities can be used for location tracking attacks
Although 5G is faster and more secure than 4G, new research indicates that it still has some vulnerabilities, which poses a certain...
-
 4.6K
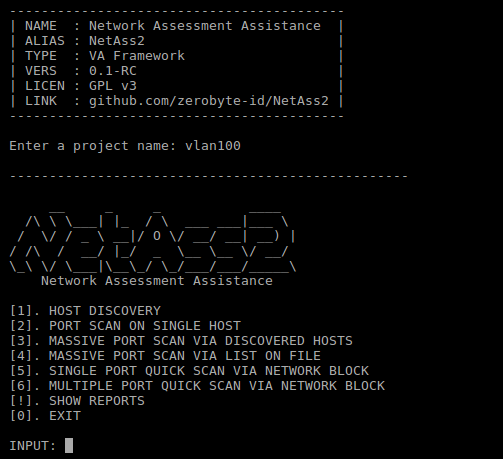
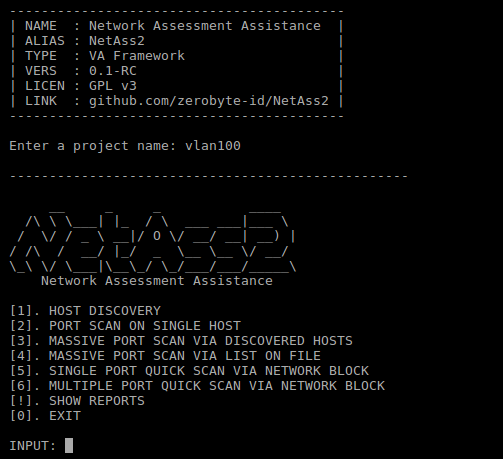
4.6KNetAss2 – Network Assessment Assistance Framework
Easier network scanning with NetAss2 (Network Assessment Assistance Framework). Make it easy for Pentester to do penetration testing on network. Dependencies nmap...
-

 3.5K
3.5KScripting Engine/Hyper-V/Exchange Remote Code Execution Vulnerability Alert
On November 12, 2019, Microsoft routinely released a security update for November. The security update covers the Windows operating system, IE/Edge browser,...
-
 4.9K
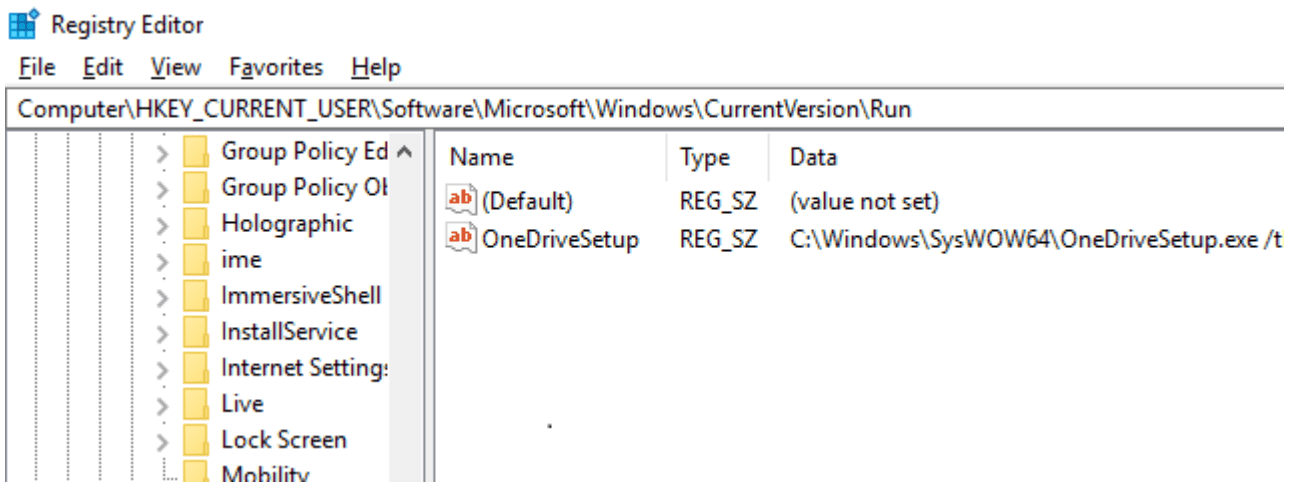
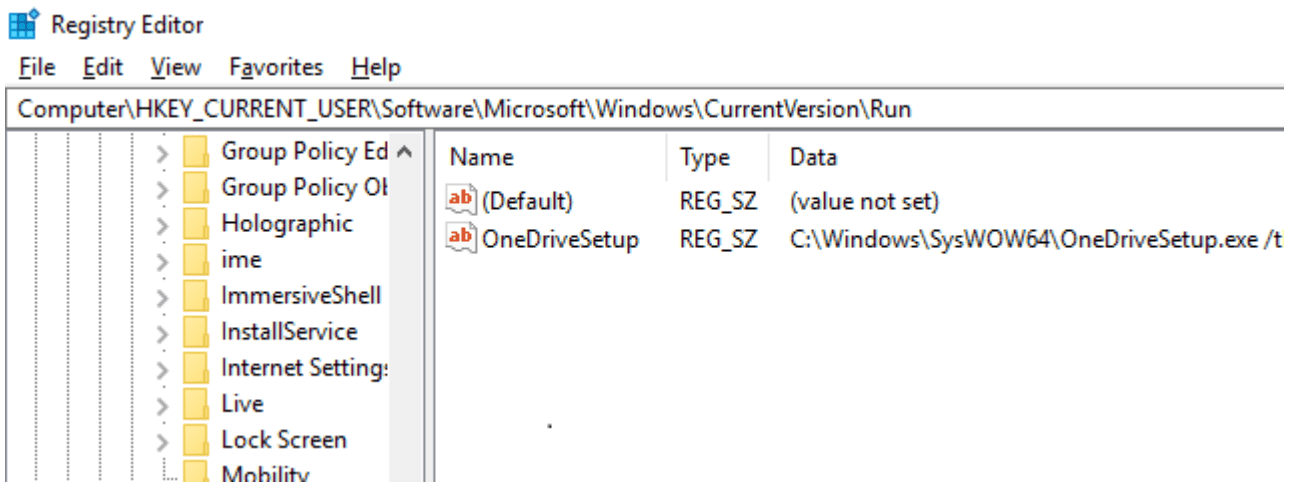
4.9KSharpHide: Tool to create hidden registry keys
SharpHide Just a nice persistence trick to confuse DFIR investigation. Uses NtSetValueKey native API to create a hidden (null-terminated) registry key. This...
-

 3.2K
3.2KRsdl – Subdomain Scan With Ping Method
Subdomain Scan With Ping Method. Flags Value Description –hostname example.com Domain for scan. –output Records the output with the domain name. –list...
-
 4.4K
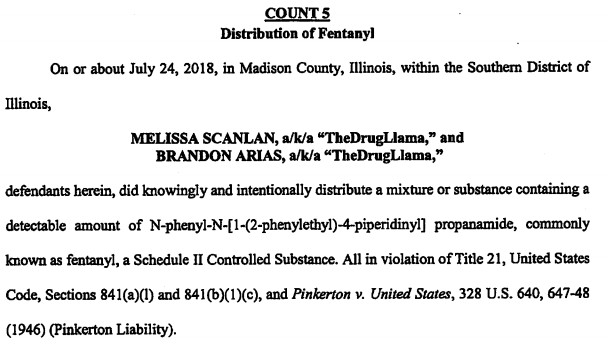
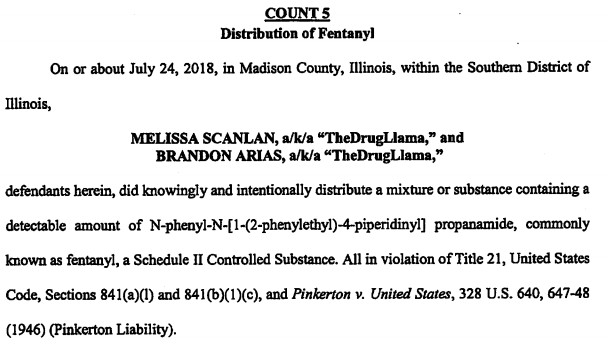
4.4KSan Diego Man Gets Nine Years for Selling Fentanyl on the Darkweb
One of the two defendants behind the Dream Market vendor account “The Drug Llama” was sentenced in a United States District Court...
-
 4.0K
4.0Kapk-mitm v0.5.3 releases: A CLI application that prepares Android APK files for HTTPS inspection
apk-mitm A CLI application that automatically prepares Android APK files for HTTPS inspection Inspecting a mobile app’s HTTPS traffic using a proxy...
-
 1.5K
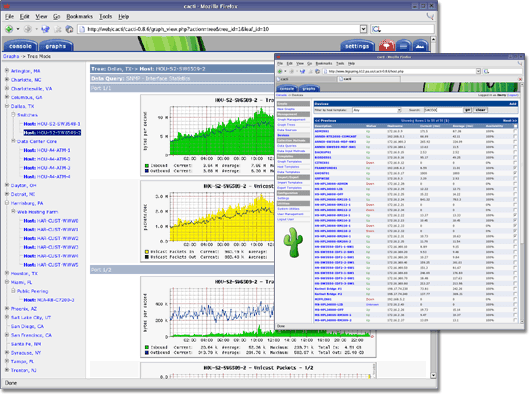
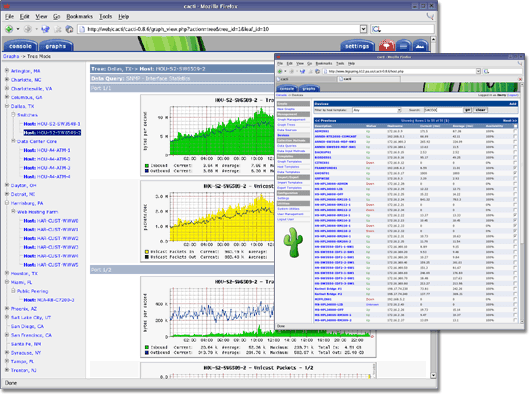
1.5KCacti – Complete Network Graphing Solution
IMPORTANTWhen using source or by downloading the code directly from the repository, it is important to run the database upgrade script if...
-
 4.0K
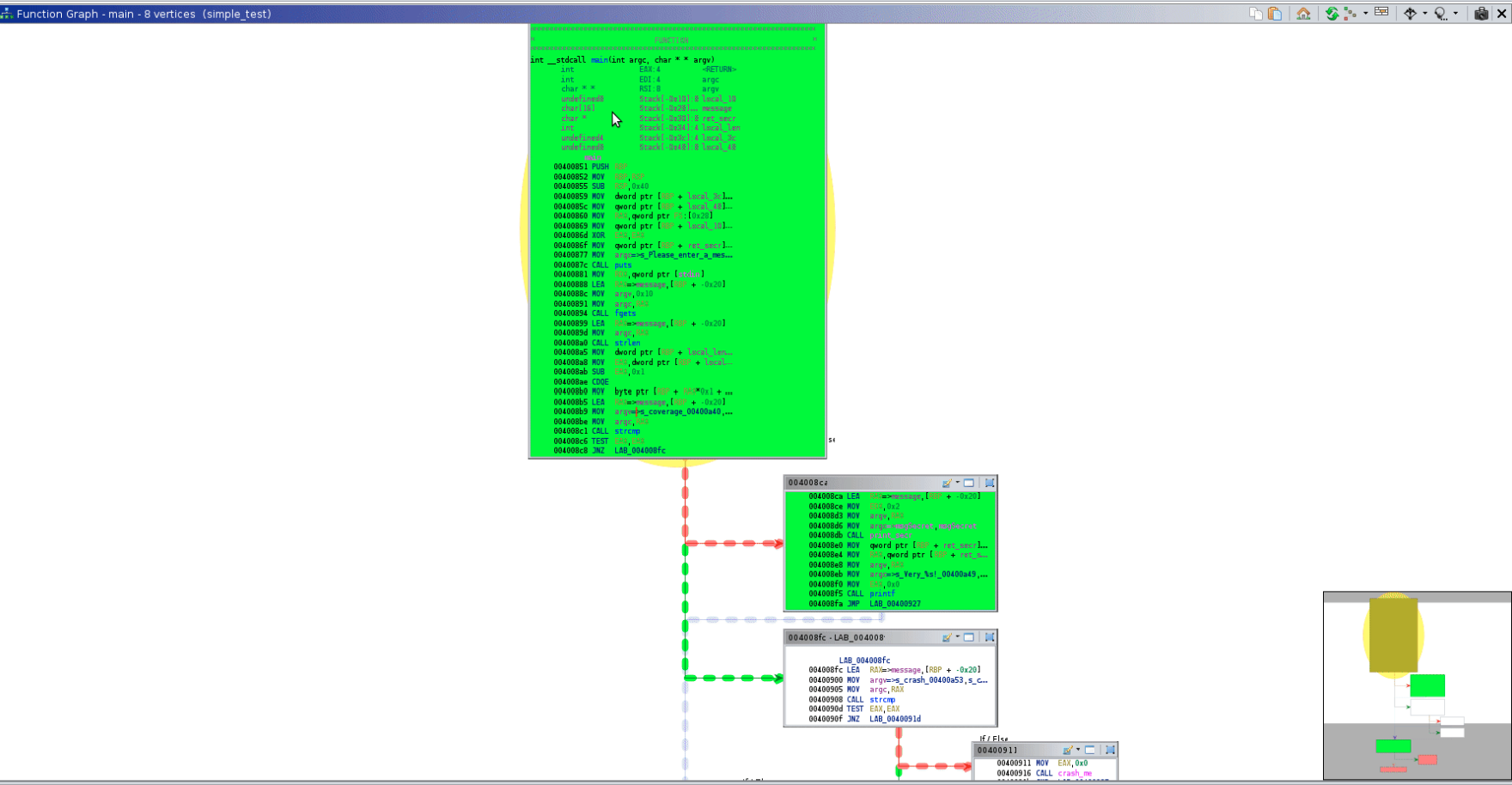
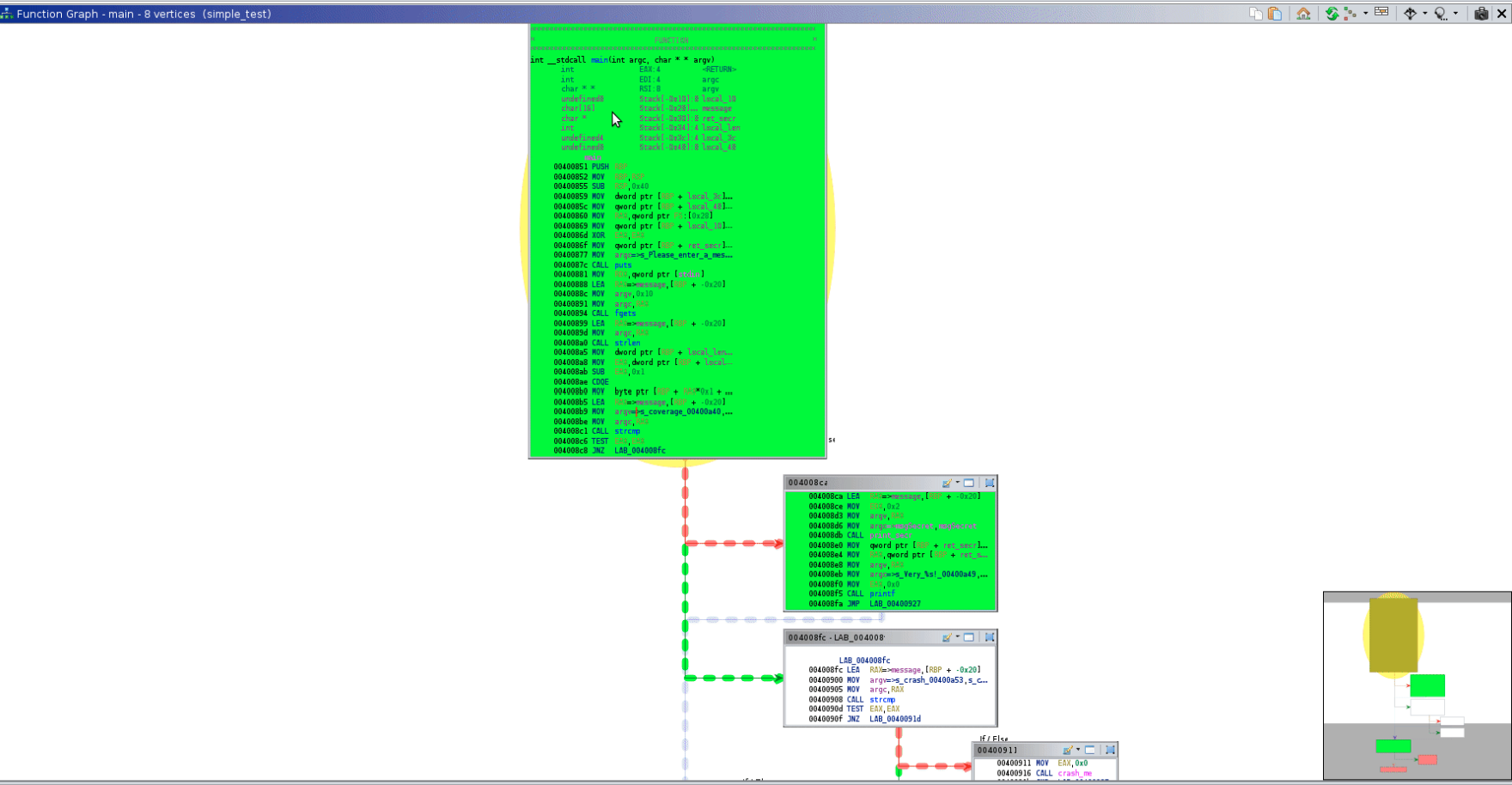
4.0Kfunction tracer: analyze a binary file with dynamic instrumentation
functrace – A function tracer functrace is a tool that helps to analyze a binary file with dynamic instrumentation using DynamoRIO (http://dynamorio.org/). These are some...
-
 2.7K
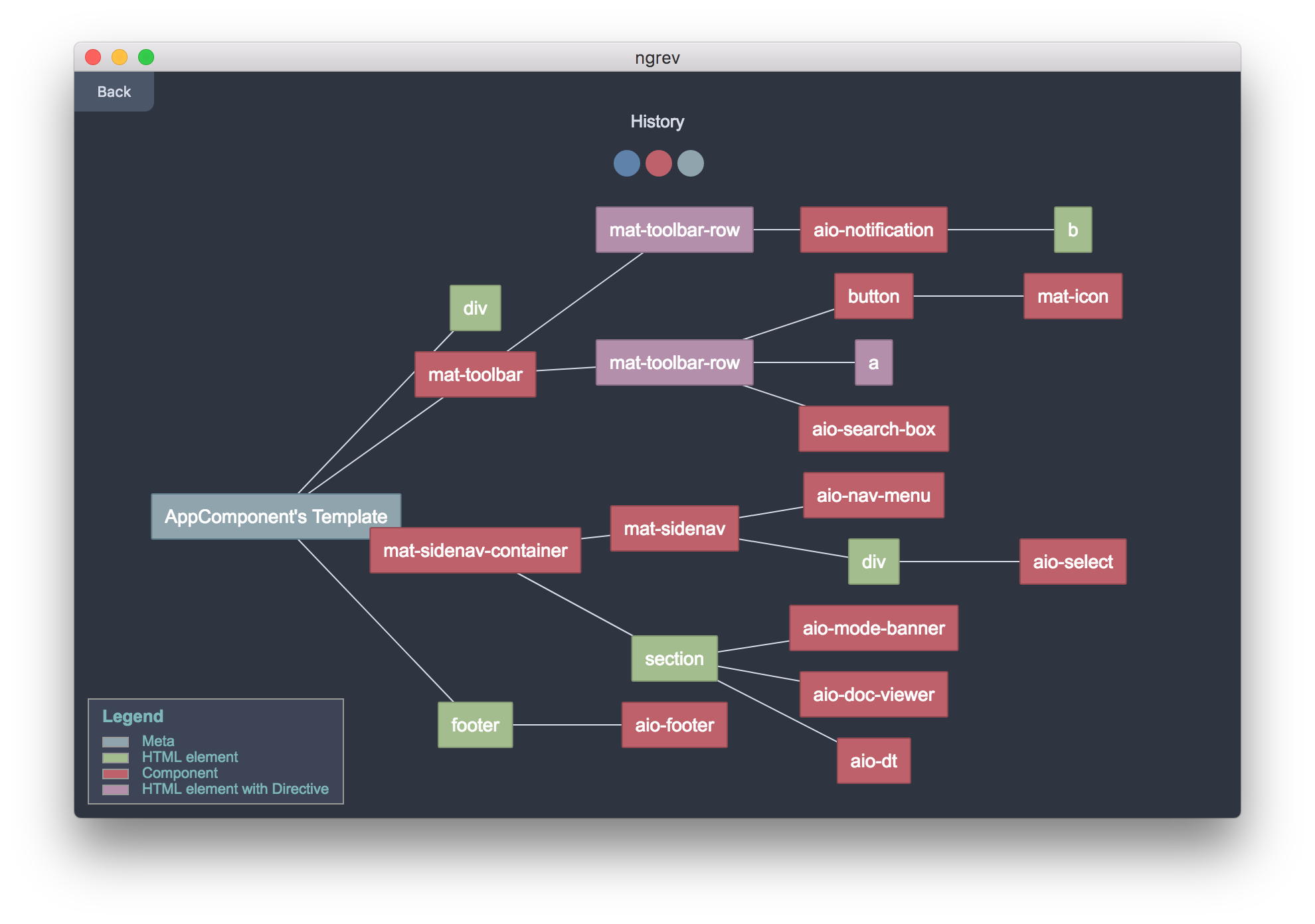
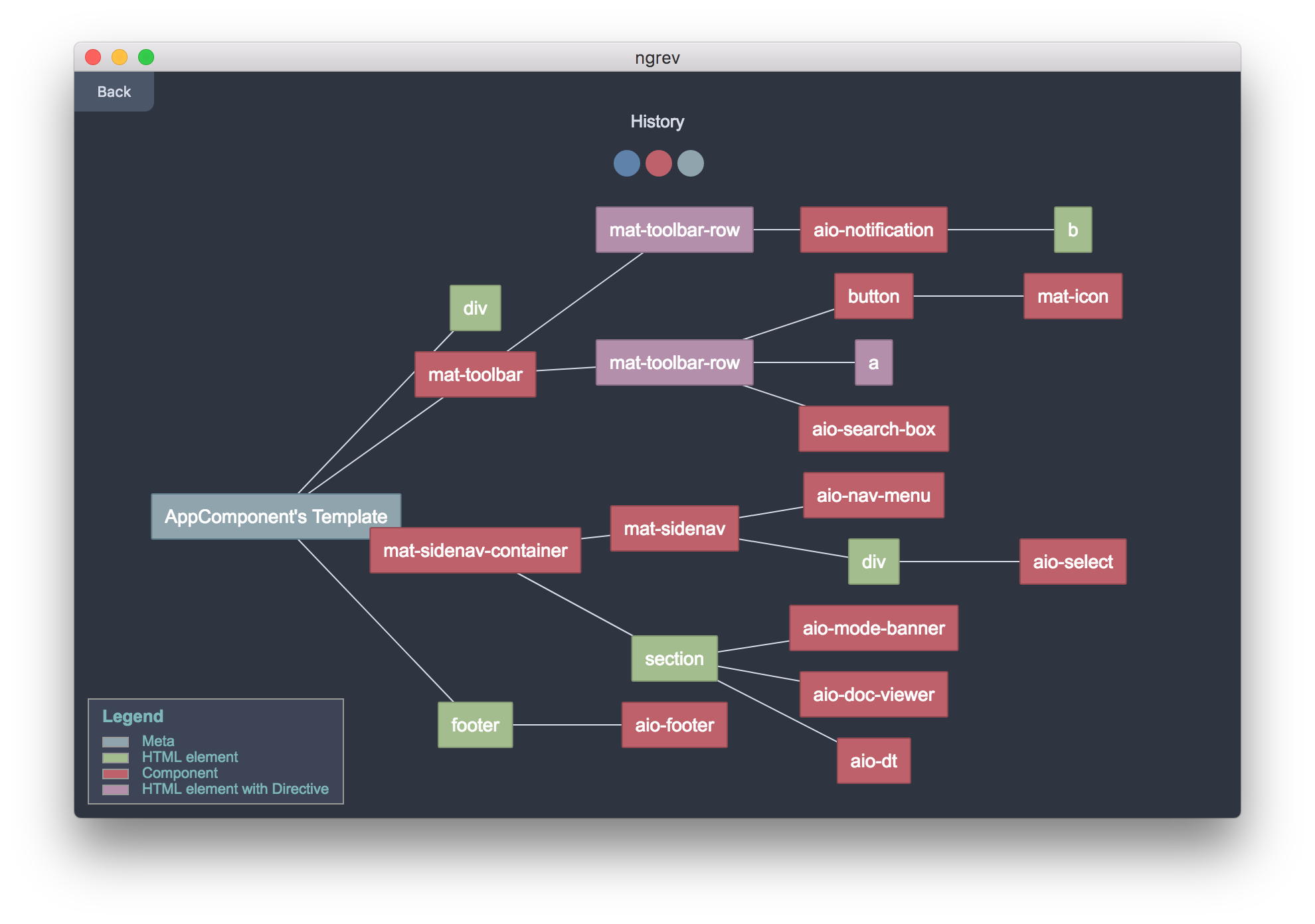
2.7Kngrev: Tool for reverse engineering of Angular applications
ngrev A graphical tool for reverse engineering of Angular projects. It allows you to navigate in the structure of your application and...
-

 936
936GCPBucketBrute – A Script To Enumerate Google Storage Buckets, Determine What Access You Have To Them, And Determine If They Can Be Privilege Escalated
A script to enumerate Google Storage buckets, determine what access you have to them, and determine if they can be privilege escalated....
-

 4.0K
4.0KNVIDIA fixes several vulnerabilities on Nvidia graphic drivers
In the recent GeForce 441.12 release, NVIDIA fixed several undisclosed high-risk vulnerabilities, and these vulnerabilities also existed in Quadro, NVS, and Tesla’s...
-
 4.4K
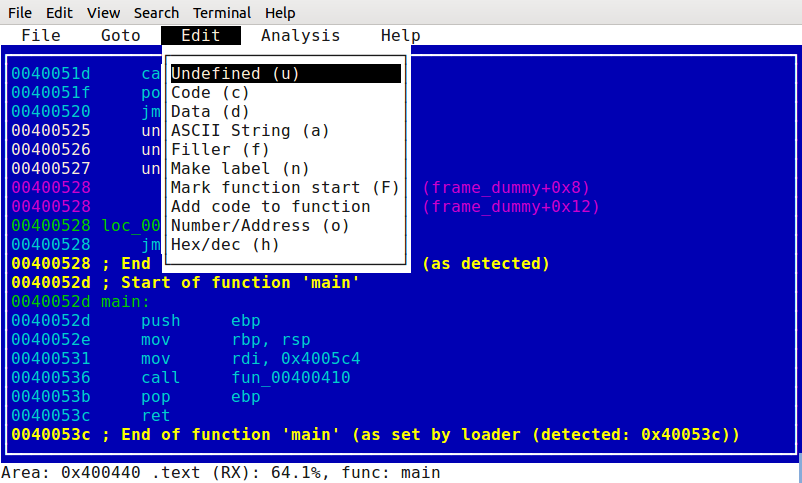
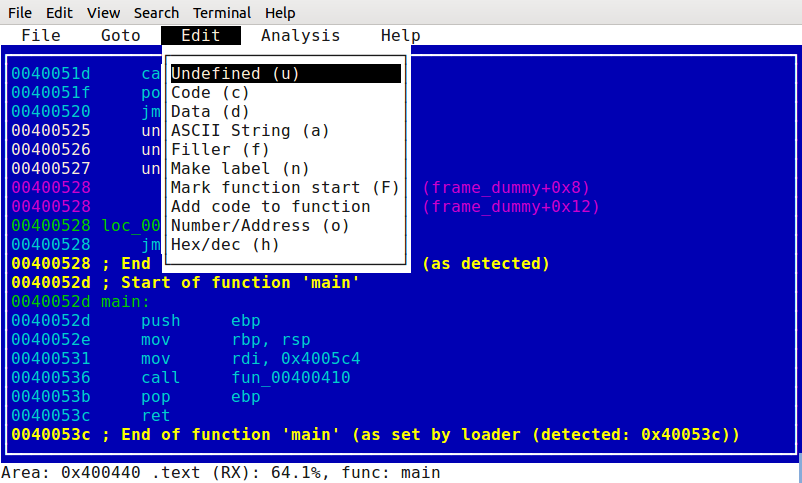
4.4KScratchABit: Easily retargetable and hackable interactive disassembler
ScratchABit ScratchABit is an interactive incremental disassembler with data/control flow analysis capabilities. ScratchABit is dedicated to the efforts of the OpenSource reverse...
-
 3.1K
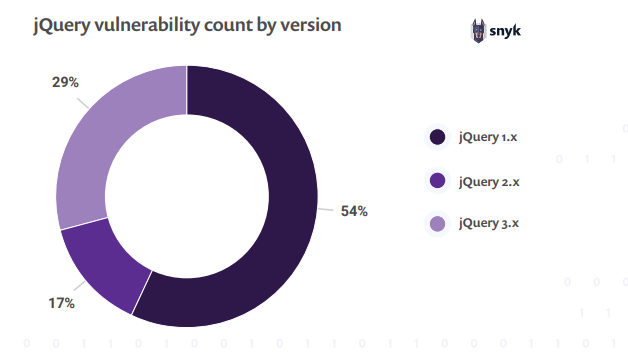
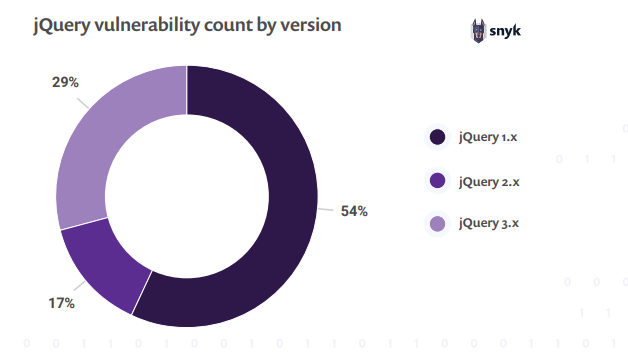
3.1KThe state of JavaScript frameworks security report 2019: at least six in ten websites are impacted by jQuery XSS vulnerabilities
Although the JavaScript library jQuery is still being used, it is no longer as popular as it used to be. According to...
-
 5.1K
5.1Kracepwn: test a race condition attack
RacePWN (Race Condition framework) RacePWN is a librace library and a racepwn utility that are designed to test a race condition attack...
-
 3.0K
3.0Kthreat_note – DPS’ Lightweight Investigation Notebook
threat_note is a web application built by Defense Point Security to allow security researchers the ability to add and retrieve indicators related...
-
 2.3K
2.3KDeepDotWeb Admin Talks About His Case from Behind Bars
From behind bars in a French prison, one of the accused administrators of DeepDotWeb provided his side of the story. Throughout the...
-

 4.3K
4.3KPoseidon v0.7.8 releases: Software Defined Network Situational Awareness
Poseidon Poseidon began as a joint effort between two of the IQT Labs: Cyber Reboot and Lab41. The project’s goal is to explore approaches to...
-

 5.0K
5.0KAdaudit – Powershell Script To Do Domain Auditing Automation
PowerShell Script to perform a quick AD audit _____ ____ _____ _ _ _| _ | | _ |_ _ _| |_|...
-
 4.5K
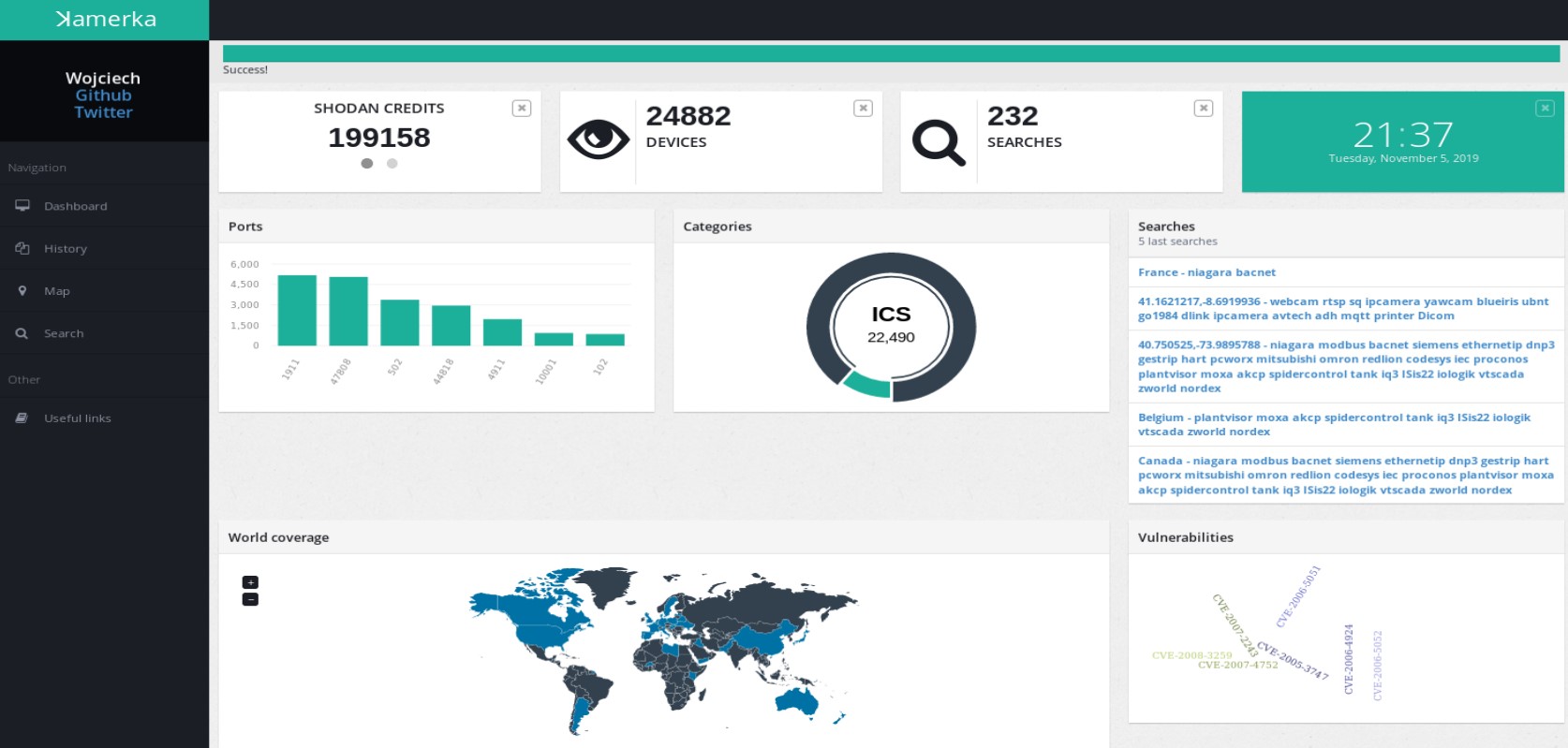
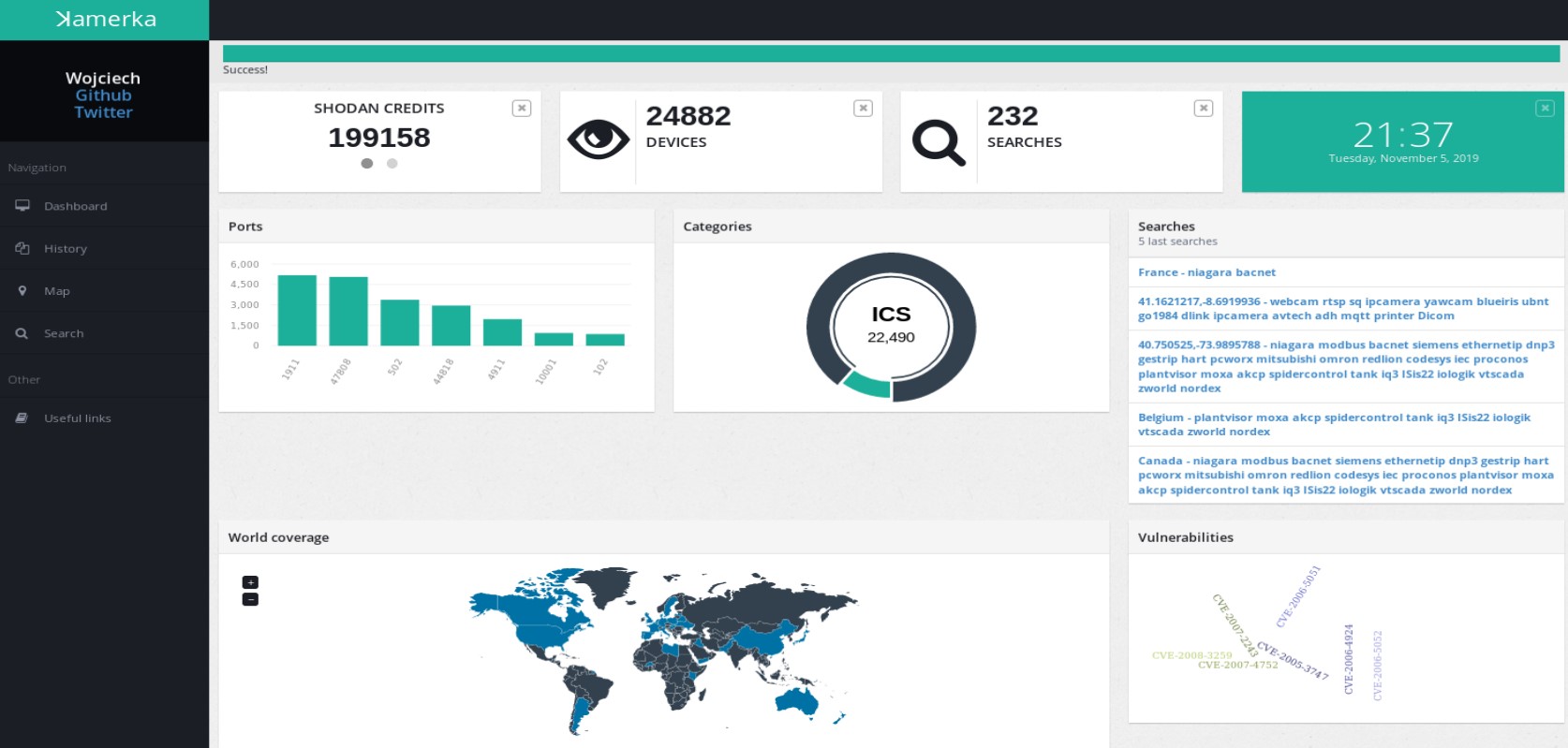
4.5KKamerka-GUI: Ultimate IoT/Industrial Control Systems reconnaissance tool
Kamerka-GUI Ultimate Internet of Things/Industrial Control Systems reconnaissance tool The main purpose of the ICS module of ꓘamerka is to map attack...






