Hackers Repository
-

 406
406SocialPath – Track users across Social Media Platforms
SocialPath is a django application for gathering social media intelligence on specific username. It checks for Twitter, Instagram, Facebook, Reddit and Stackoverflow....
-
 629
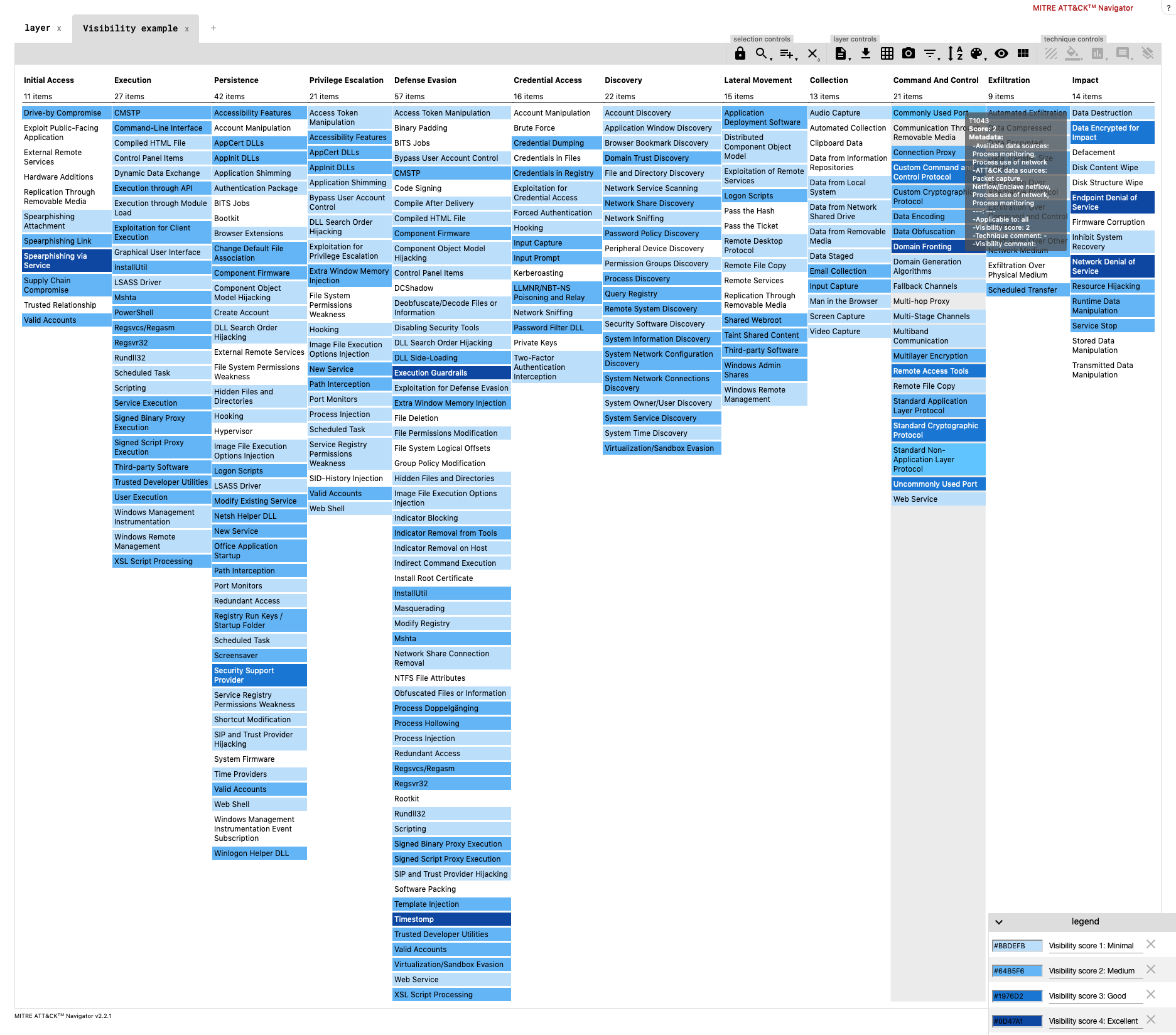
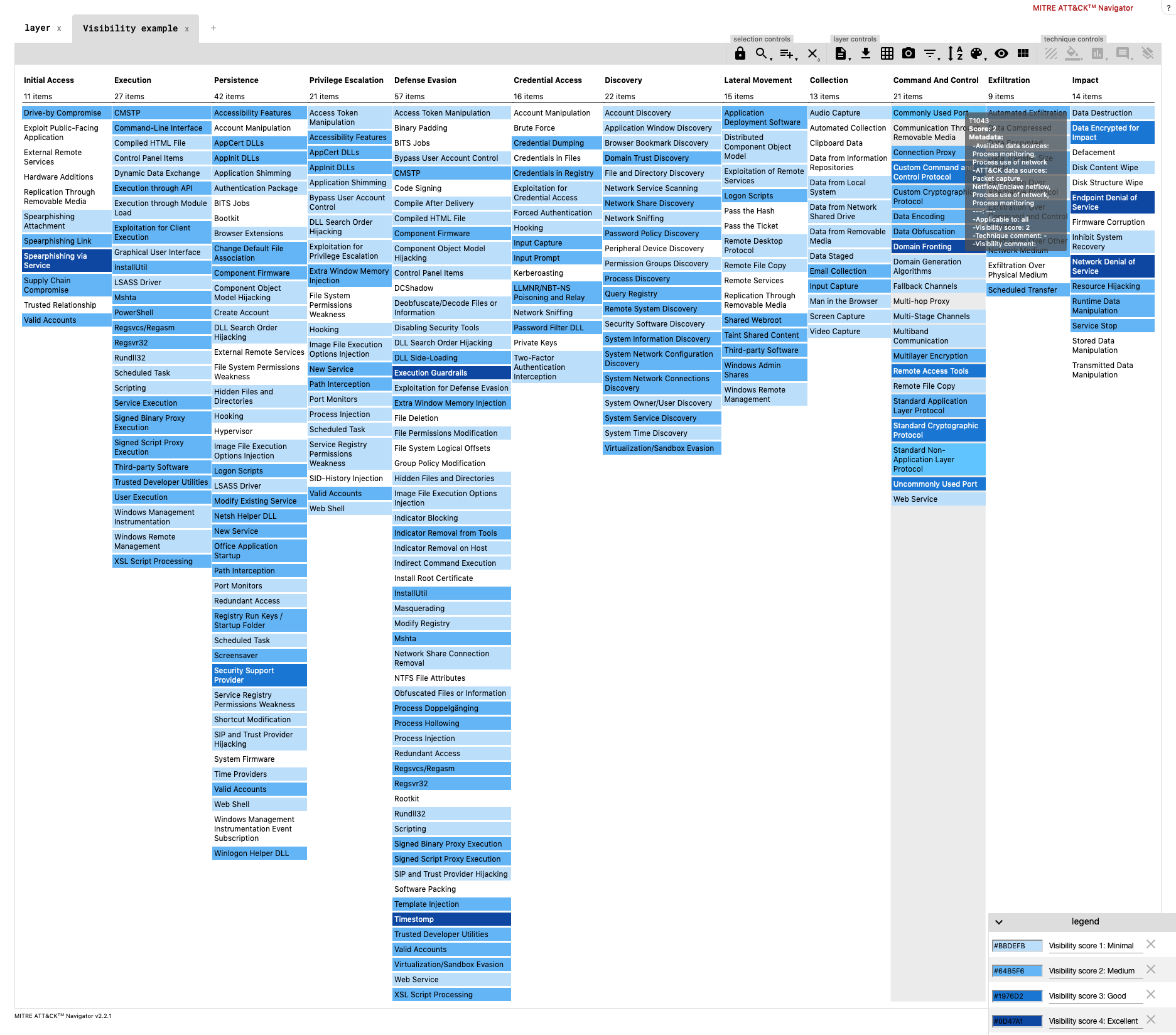
629DeTTecT – Detect Tactics, Techniques & Combat Threats
DeTT&CT aims to assist blue teams using ATT&CK to score and compare data log source quality, visibility coverage, detection coverage and threat...
-
 423
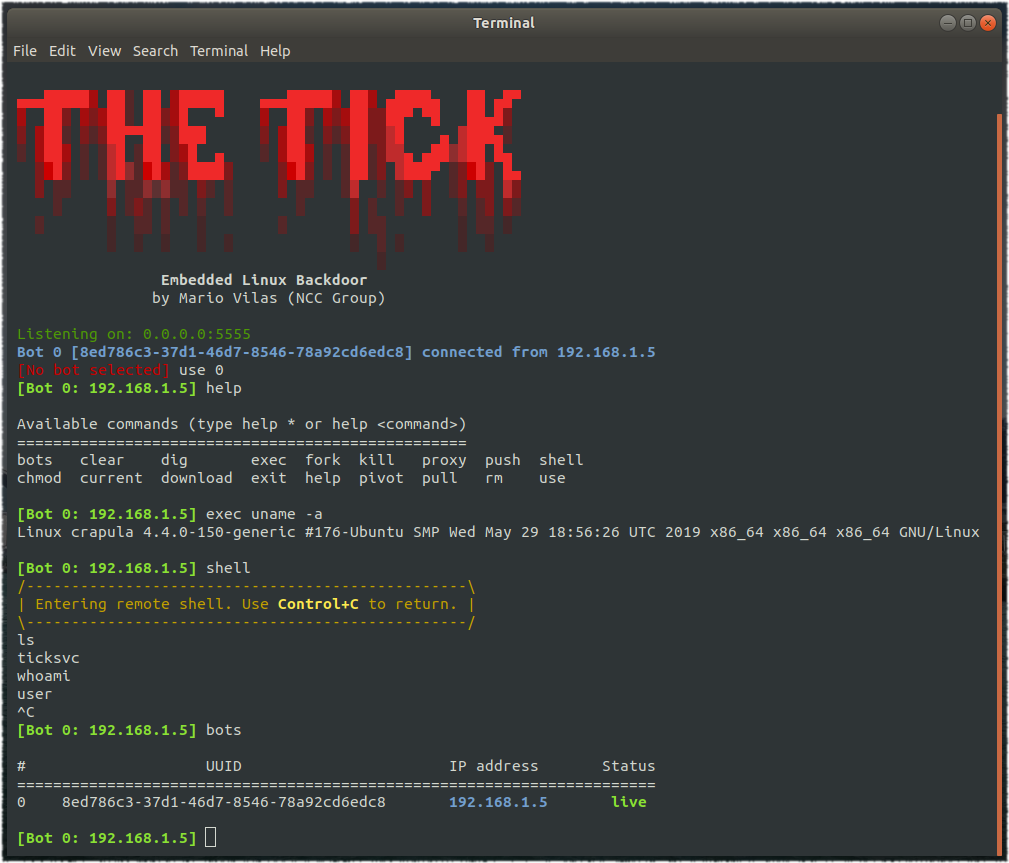
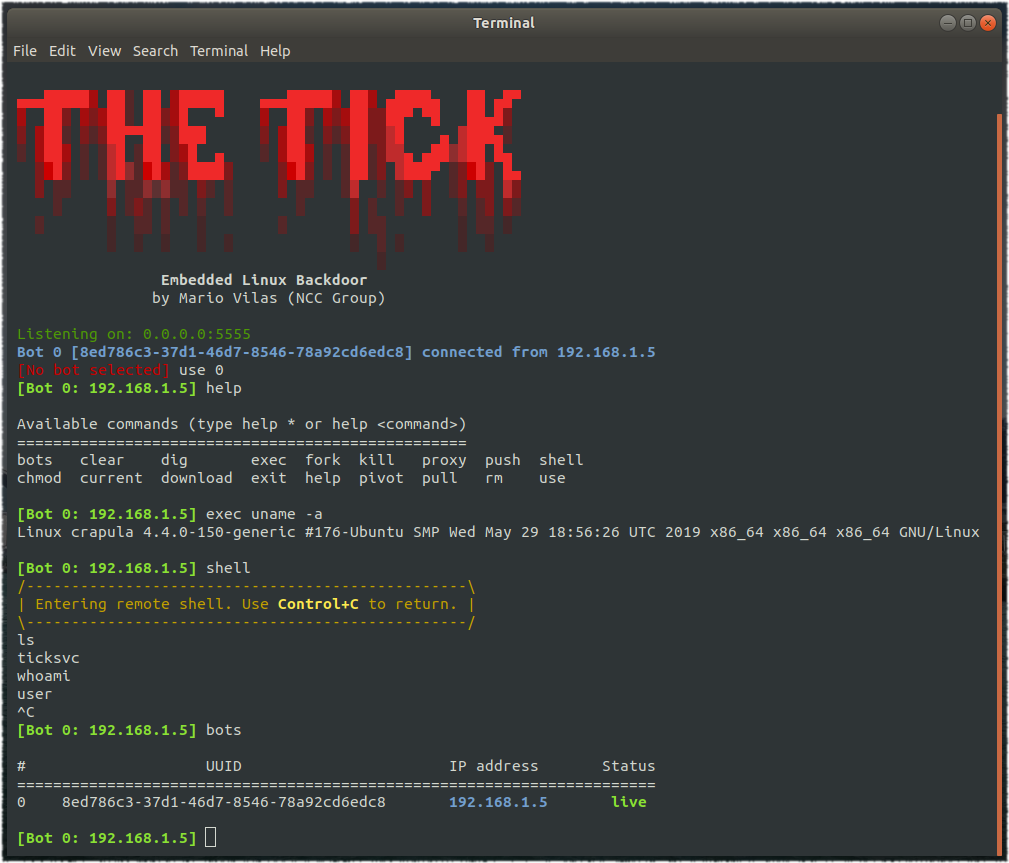
423TheTick – A simple embedded Linux backdoor
A simple embedded Linux backdoor. Compiling The Tick depends only on libcurl, so make sure you have the corresponding development package. For...
-

 558
558CATPHISH – Phishing and Corporate Espionage
CATPHISH is a tool to generate similar-looking domains for phishing attacks. The program will check expired domains and if they are categorized...
-
 890
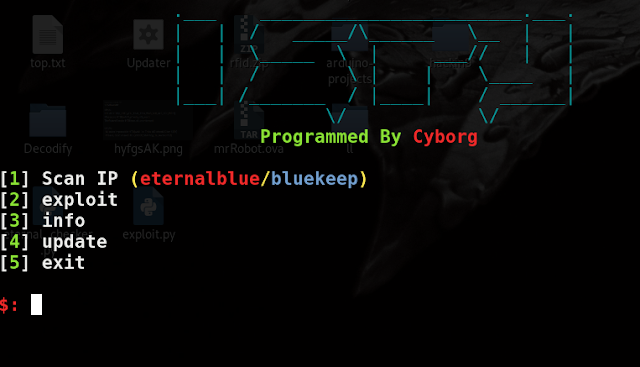
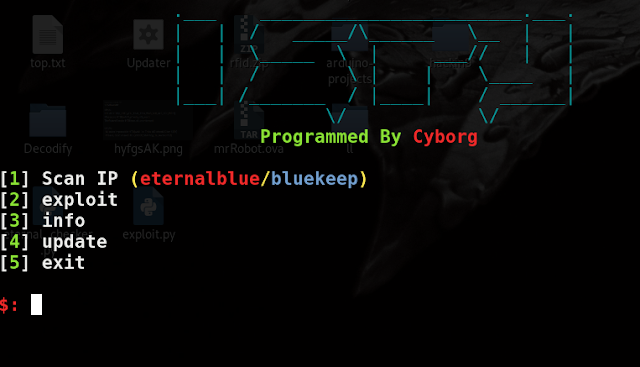
890Ispy – Eternalblue (MS17-010) / Bluekeep (CVE-2019-0708) Scanner And Exploit
ispy : Eternalblue(ms17-010)/Bluekeep(CVE-2019-0708) Scanner and exploiter ( Metasploit automation ) How to install : git clone https://github.com/Cyb0r9/ispy.git cd ispy chmod +x setup.sh...
-

 683
683ConPtyShell – Fully Interactive Reverse Shell for Windows
ConPtyShell is a Fully Interactive Reverse Shell for Windows systems. The introduction of the Pseudo Console (ConPty) in Windows has improved so...
-
 380
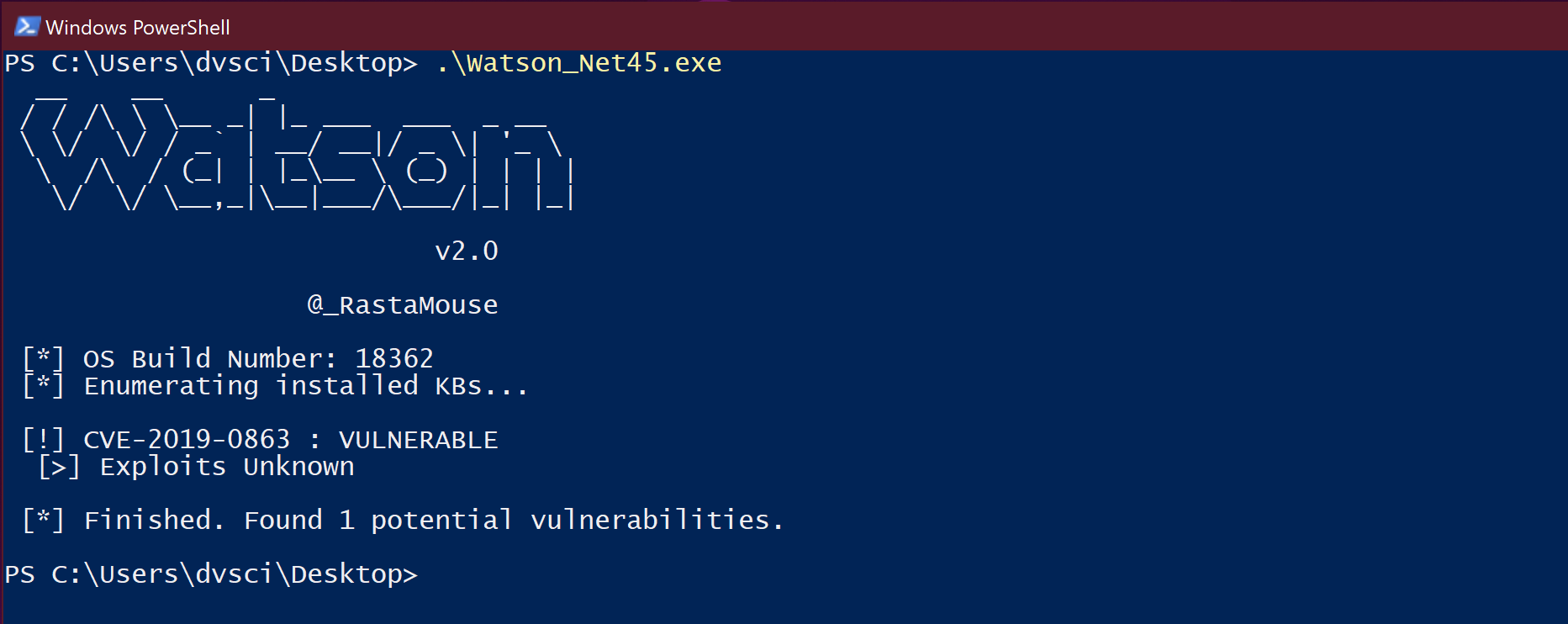
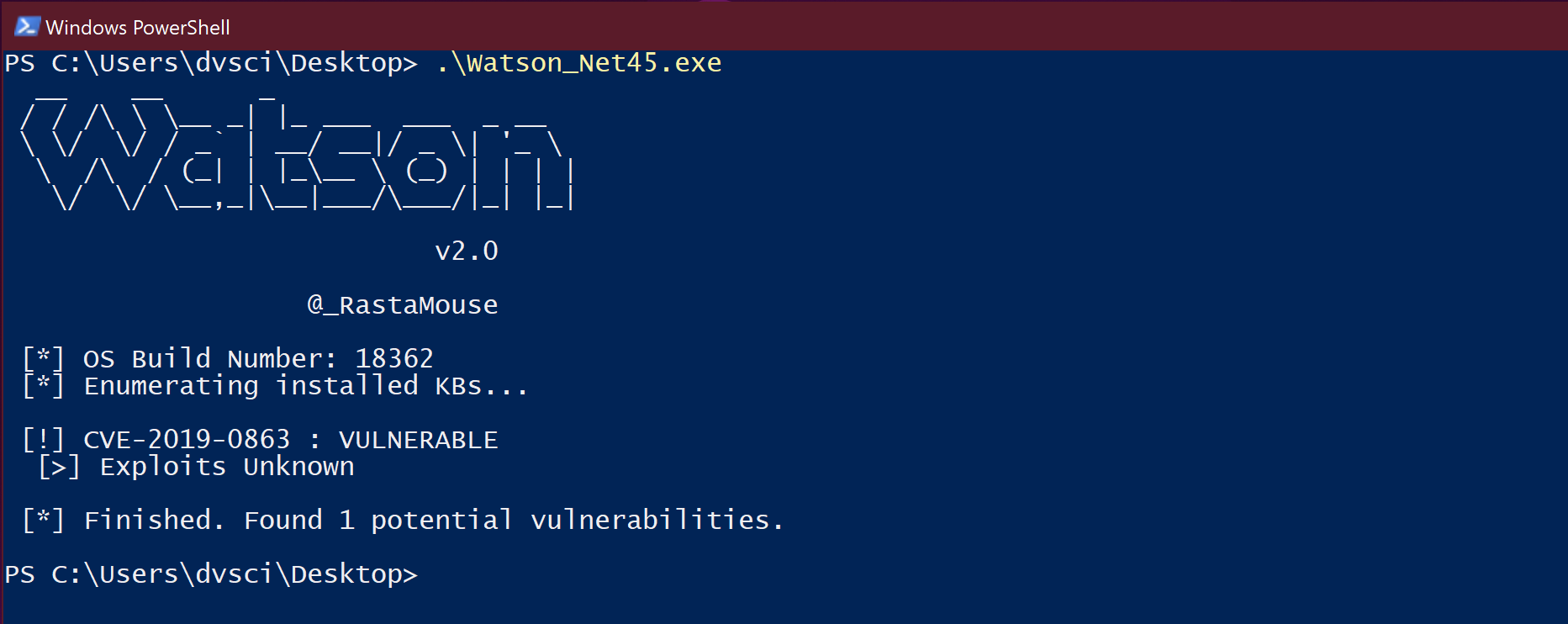
380Watson – Enumerate missing KBs and suggest exploits for useful Privilege Escalation vulnerabilities
Watson is a .NET tool designed to enumerate missing KBs and suggest exploits for useful Privilege Escalation vulnerabilities. My focus is on...
-

 583
583GeoSpy – OSINT analysis and research tool for social engineering attacks
Geolocation Spy (GeoSpy) is an OSINT analysis and research tool, which allows people to track and execute intelligent social engineering attacks in...
-
 582
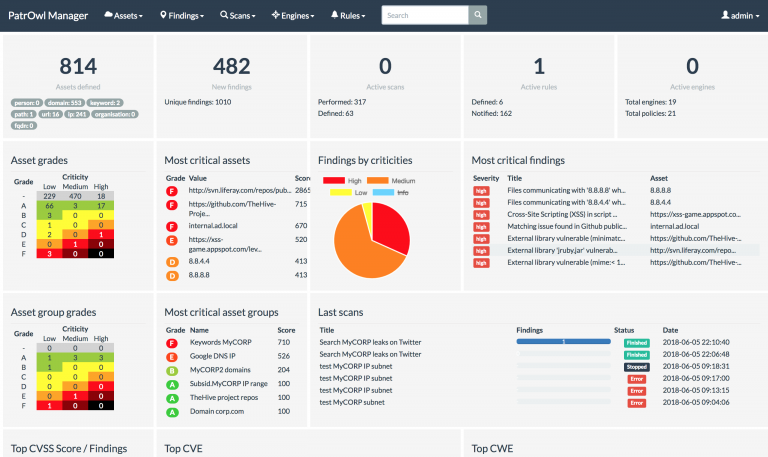
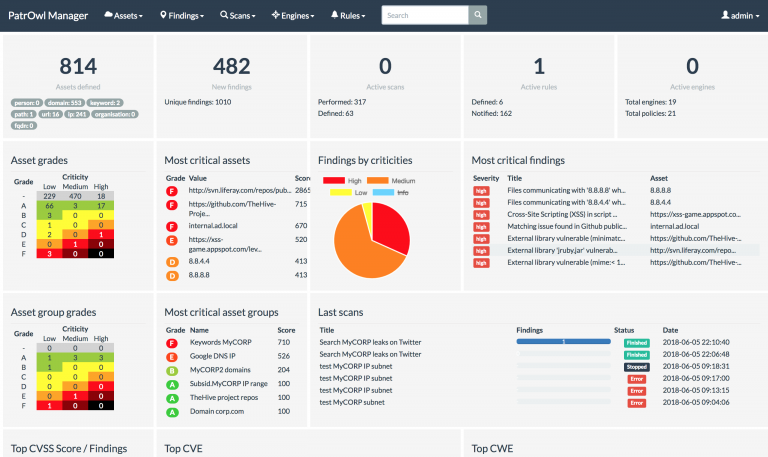
582PatrOwl – Smart and Scalable Security Operations Orchestration Platform
PatrOwl is an advanced platform for orchestrating Security Operations like Penetration testing, Vulnerability Assessment, Code review, Compliance checks, Cyber-Threat Intelligence / Hunting...
-
 382
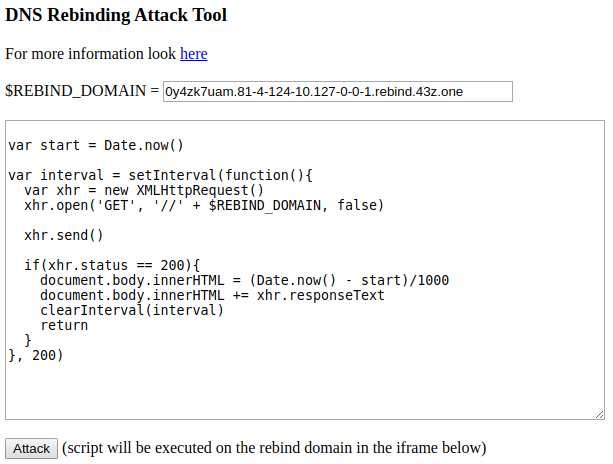
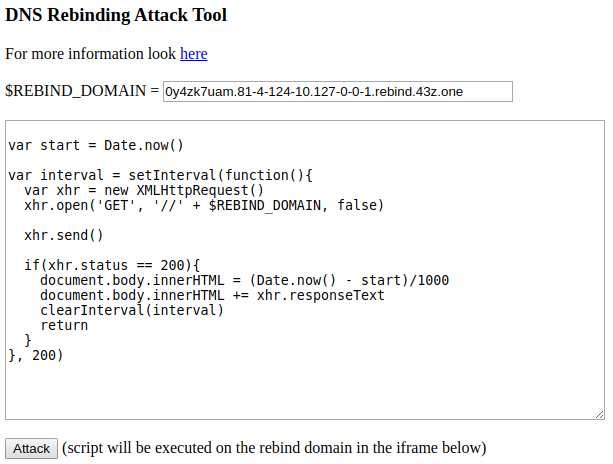
382DNS Rebinding Tool – DNS Rebind Tool With Custom Scripts
This project is meant to be an All-in-one Toolkit to test further DNS rebinding attacks and my take on understanding these kind...
-
 339
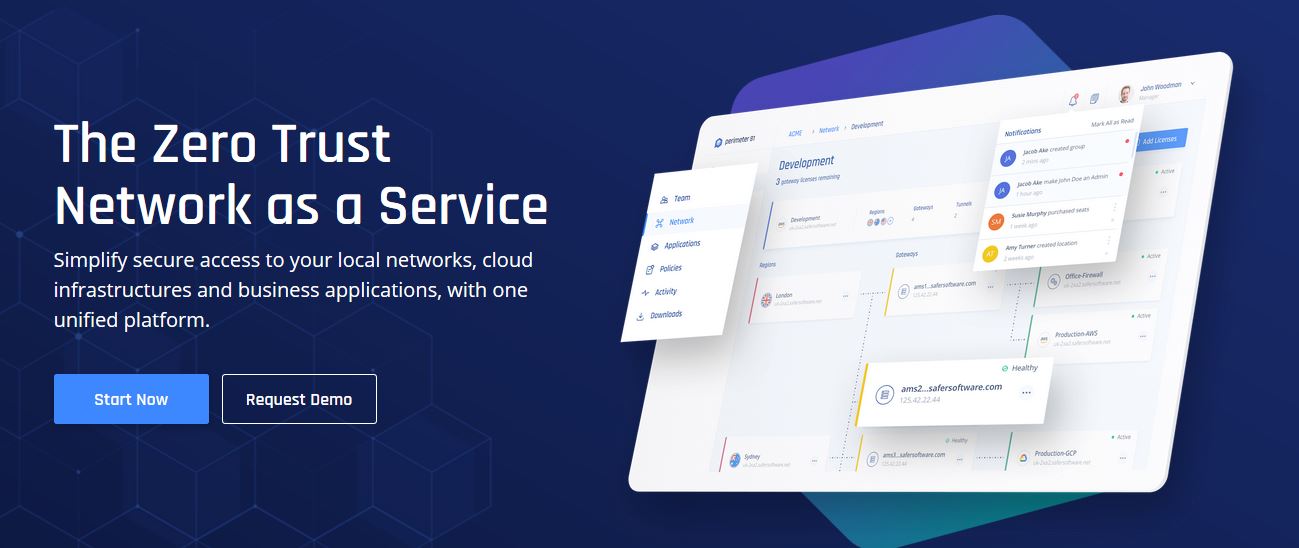
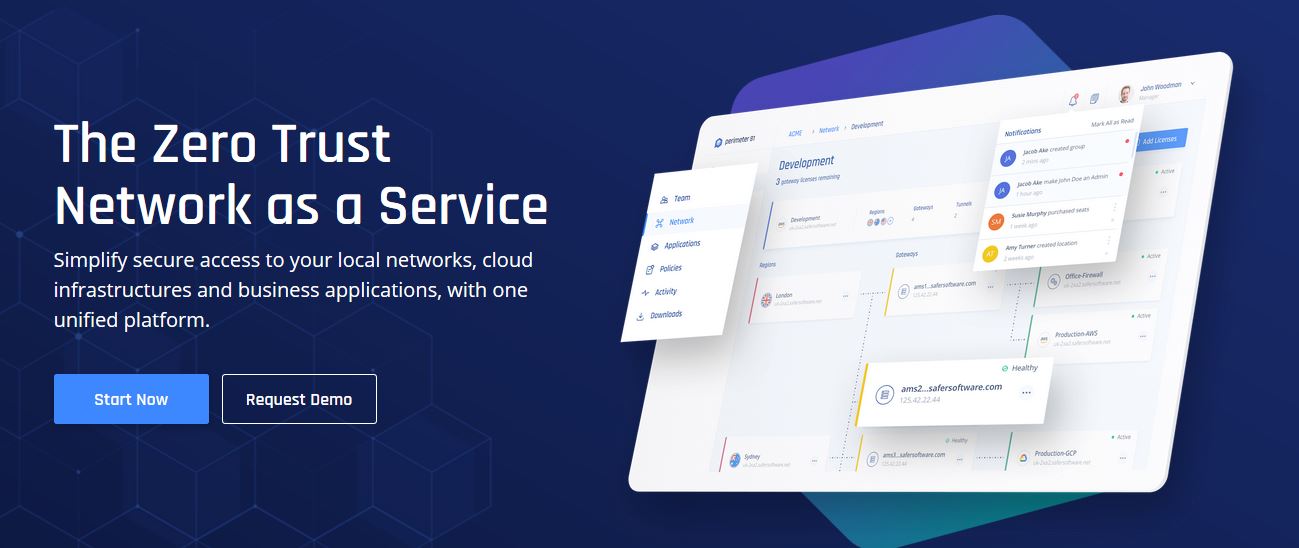
339Perimeter 81 – The Zero Trust Network as a Service
Perimeter 81 is a Zero Trust Network as a Service designed to simplify secure network, cloud and application access for the modern...
-
 366
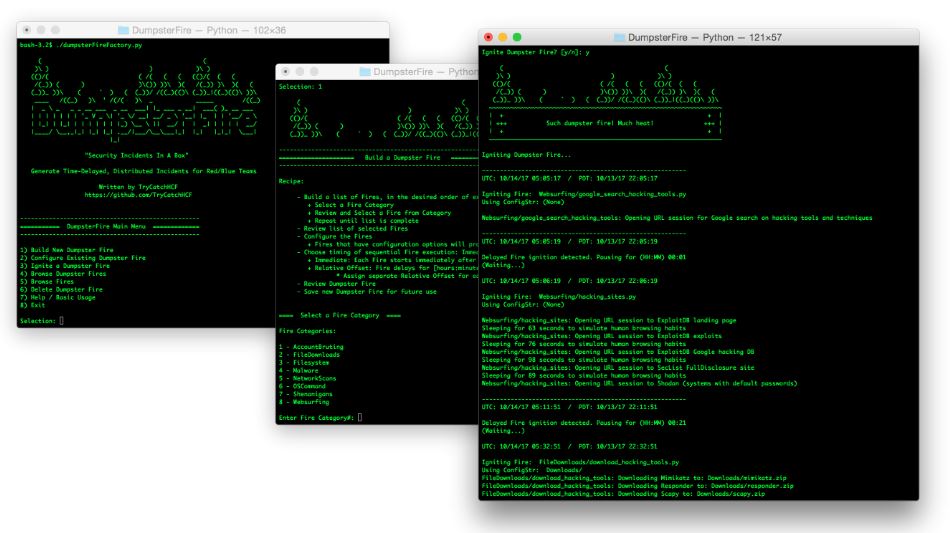
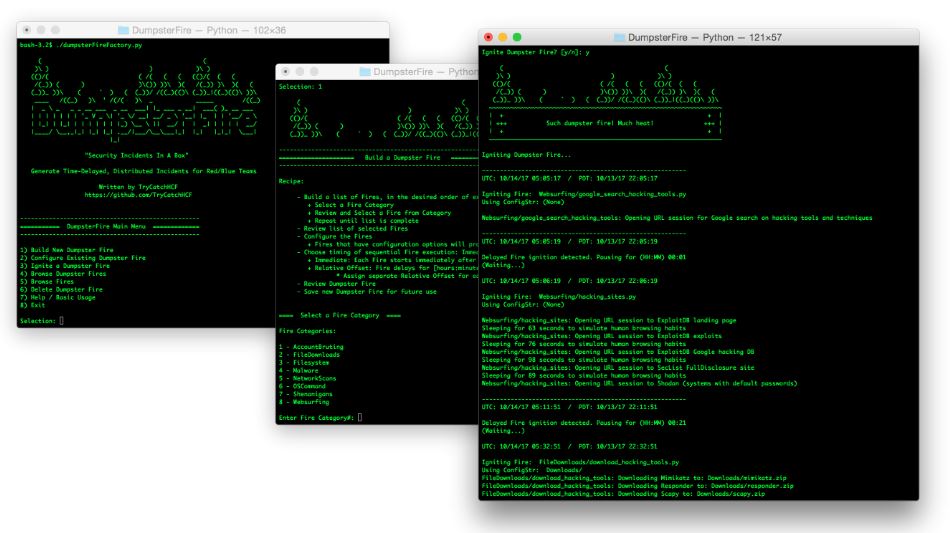
366DumpsterFire Toolset – Security Incidents In A Box!
The DumpsterFire Toolset is a modular, menu-driven, cross-platform tool for building repeatable, time-delayed, distributed security events. Easily create custom event chains for...
-
 275
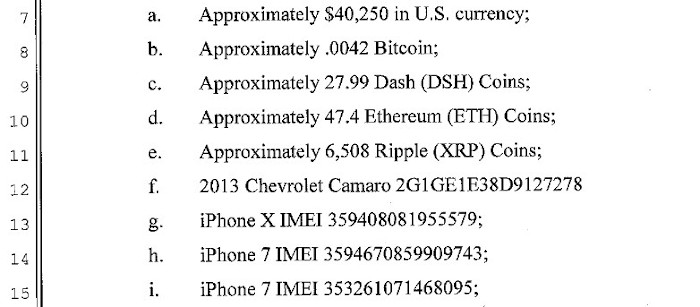
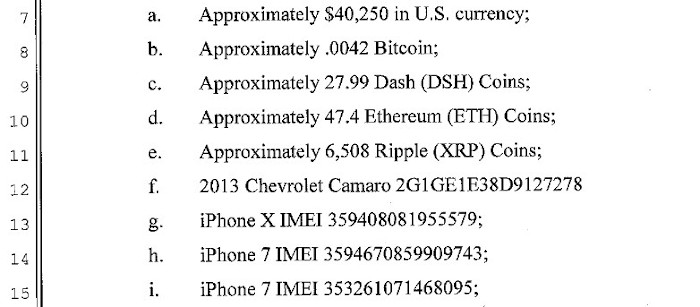
275Dark Web Vendors Plead Guilty to Cryptocurrency Money Laundering Conspiracy
Aidan Curry and Connor Brooke pleaded guilty in federal court today for conspiring to launder Dark Web proceeds through their unlicensed money...
-
 387
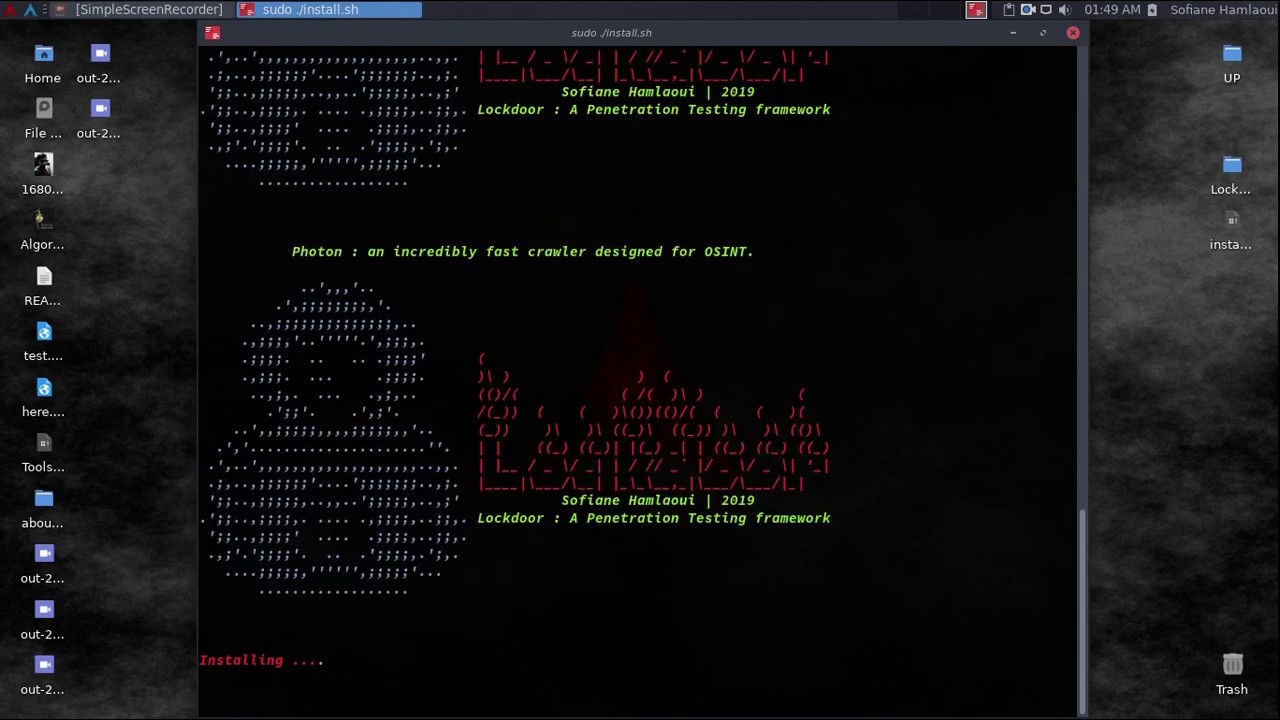
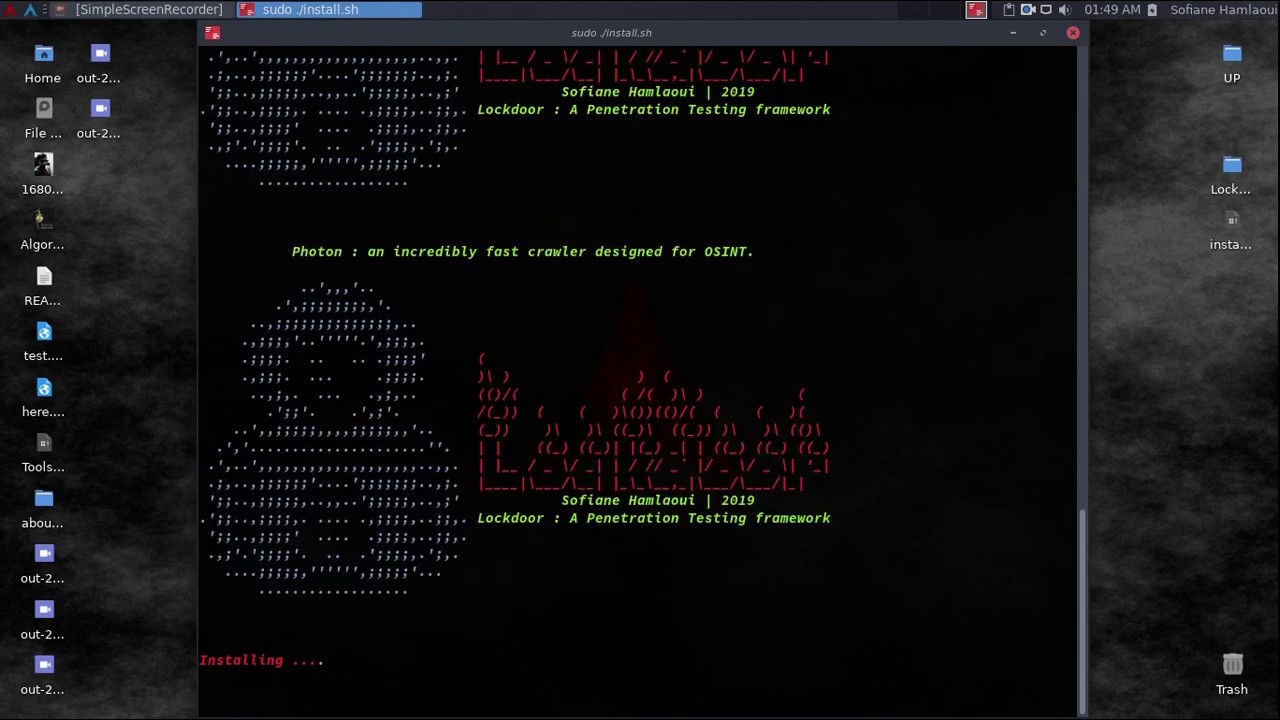
387Lockdoor – All in One Penetration Testing Framework
LockDoor is a Framework aimed at helping penetration testers, bug bounty hunters And cyber security engineers. This tool is designed for Debian/Ubuntu/ArchLinux...
-
 627
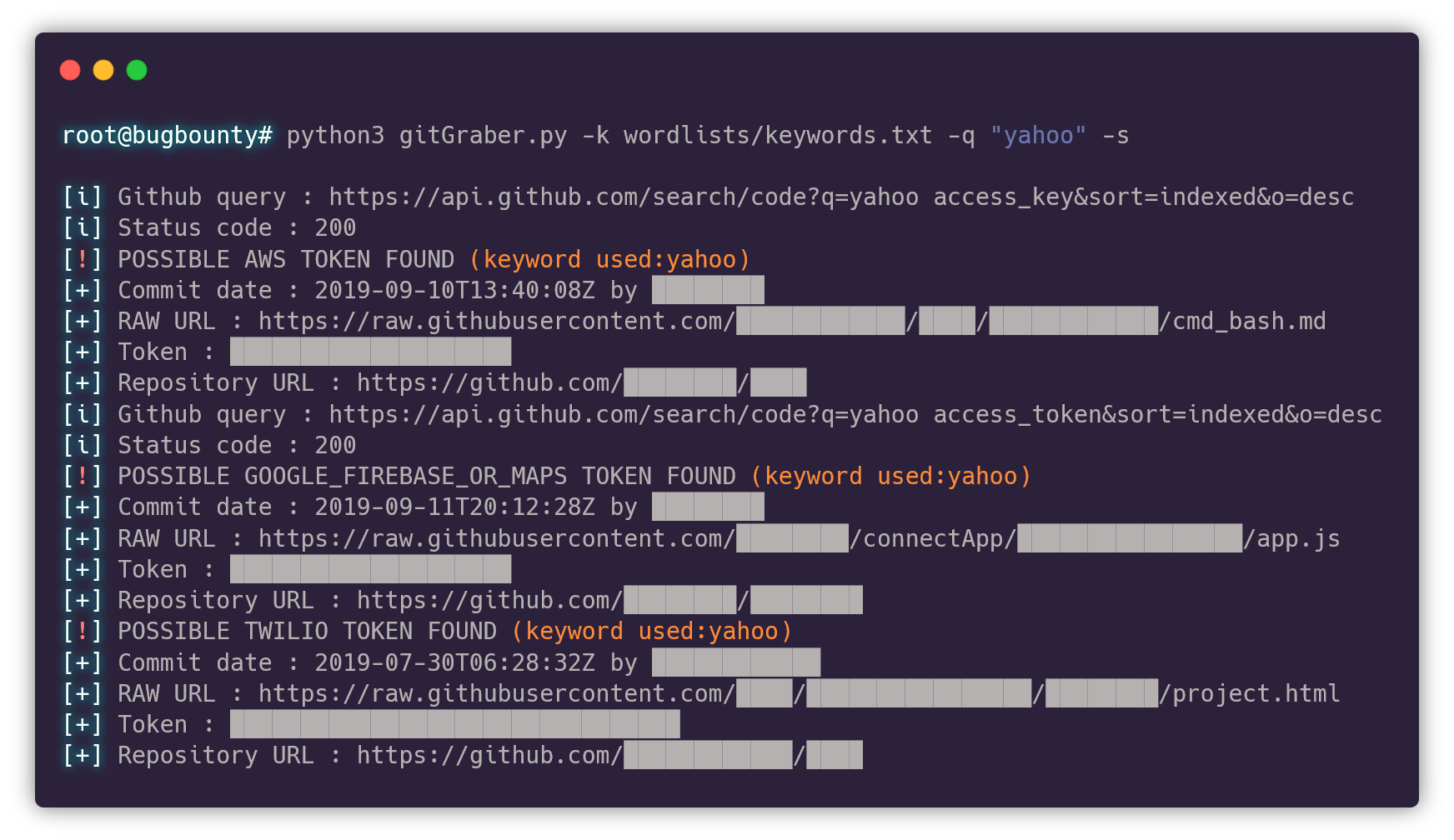
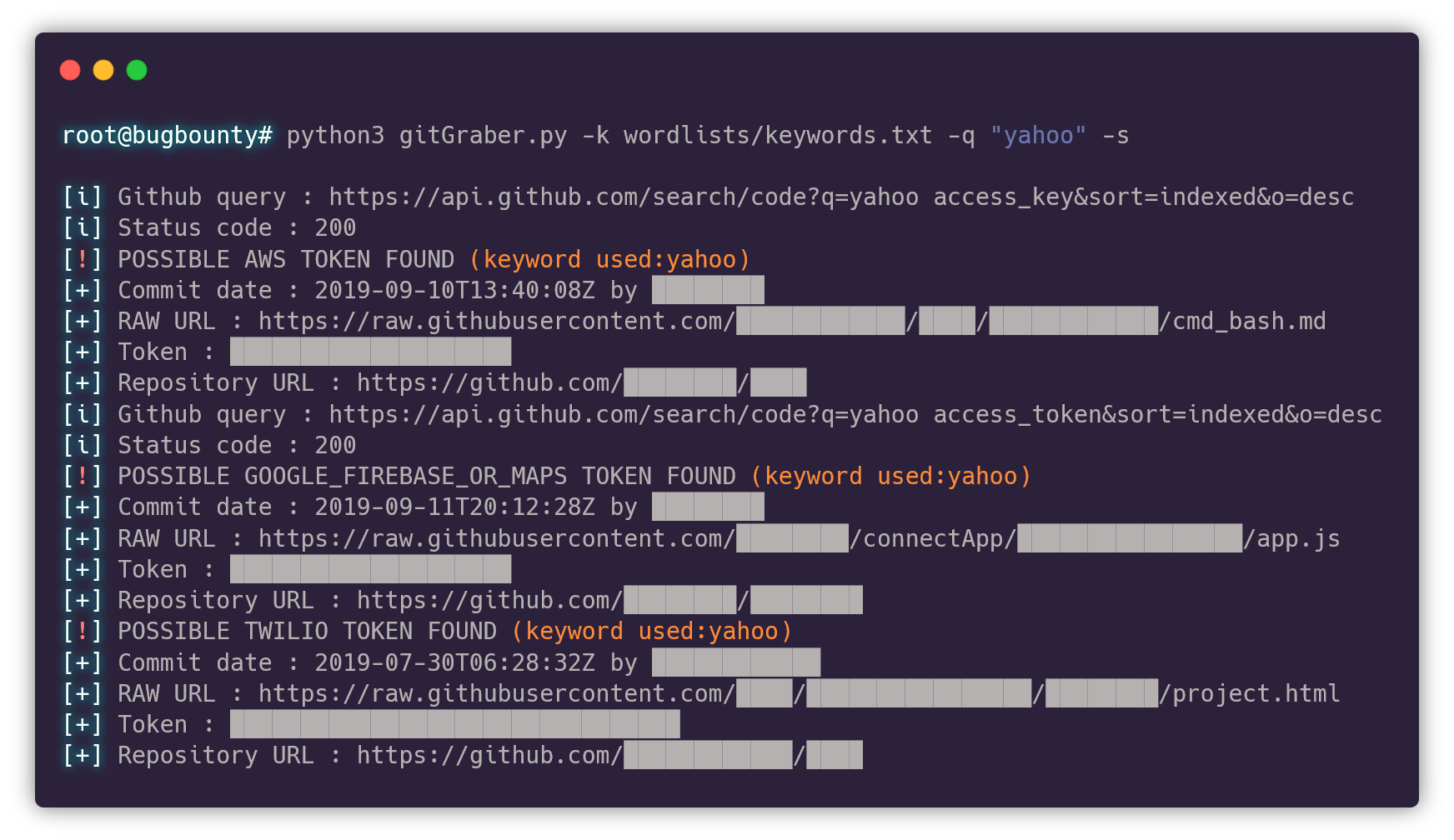
627GitGraber – Monitor GitHub to search and find sensitive data in real time
gitGraber is a tool developed in Python3 to monitor GitHub to search and find sensitive data in real time for different online...
-
 431
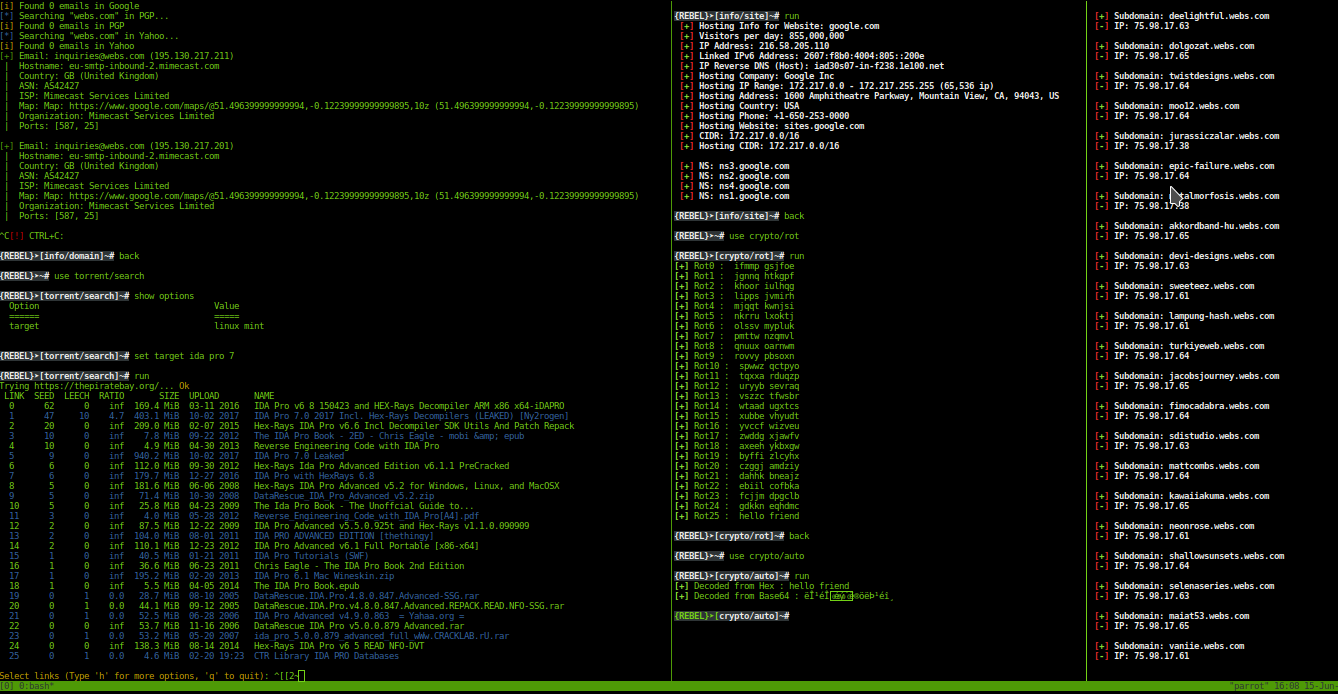
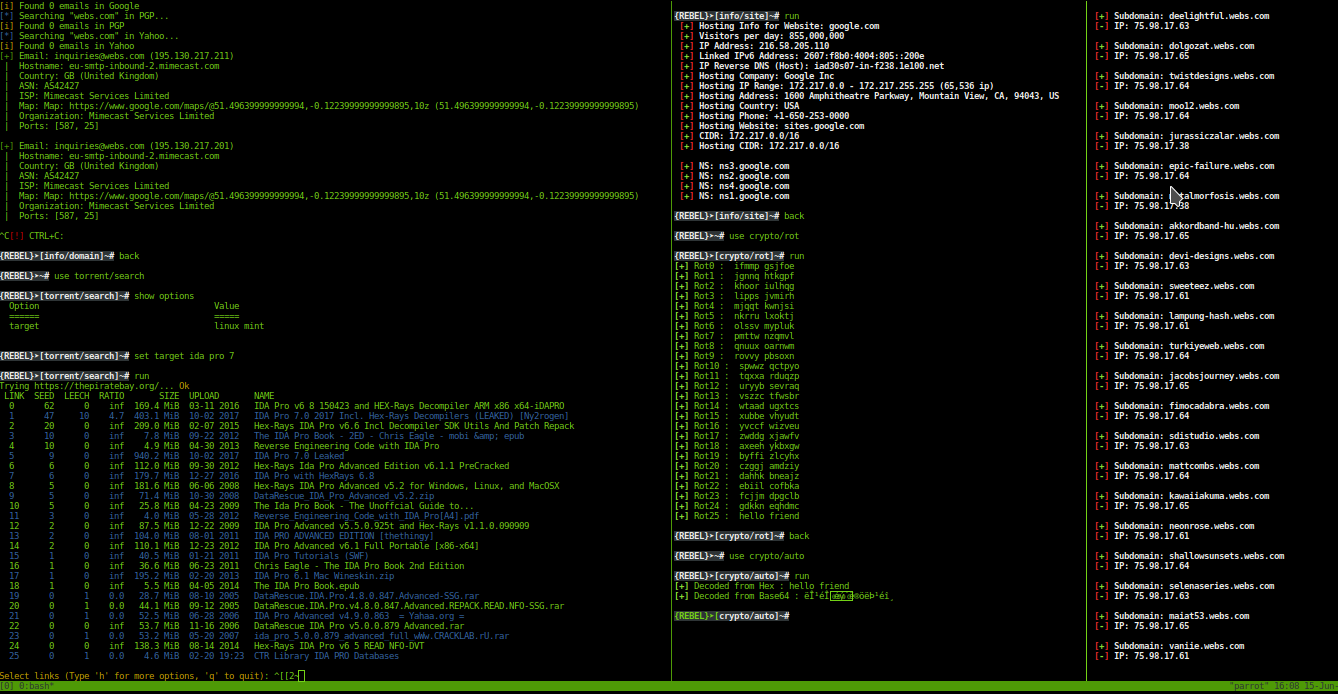
431Rebel Framework – Advanced and easy to use Penetration Testing Framework
Automate the automation with rebel framework. Install Rebel Framework git clone https://github.com/rebellionil/rebel-framework.git cd rebel-framework bash setup.sh bash rebel.sh MODULES SCREENSHOTS DEMOS SUPPORTED...
-

 366
366Router Exploit Shovel – Automated Application Generation for Stack Overflow Types on Wireless Routers
Router exploit shovel is an automated application generation tool for stack overflow types on wireless routers. The tool implements the key functions...
-
 385
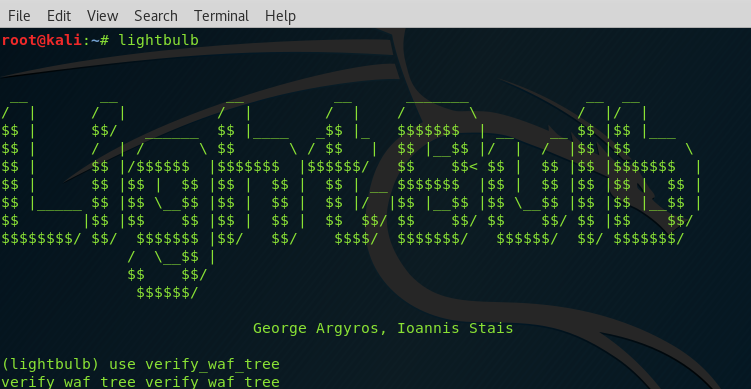
385Lightbulb – Framework for Auditing Web Applications Firewalls
LightBulb is an open source python framework for auditing web application firewalls and filters. Web Applications Firewalls (WAFs) are fundamental building blocks...
-

 408
408Top 7 Vulnerability Databases to Trace New Vulnerabilities
Vulnerability defined as the weakness that allows the attacker to enter in and harm, it may be a flaw in design or...
-
 327
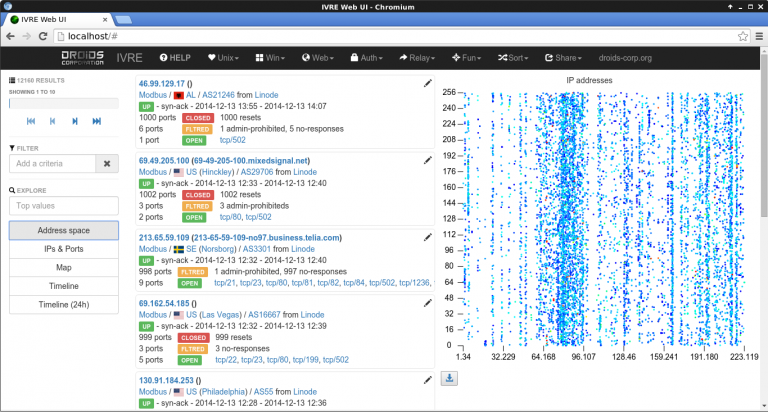
327IVRE – Network Recon Framework
IVRE (Instrument de veille sur les réseaux extérieurs) or DRUNK (Dynamic Recon of UNKnown networks) is a network recon framework, including tools...
-

 549
549Pixload – Image Payload Creating and Injecting tools
Set of tools for creating/injecting payload into images. Useful references for better understanding of pixload and its use-cases: Bypassing CSP using polyglot...






