Incidents
-
 260
260Florida GOP consultant admits he worked with Guccifer 2.0, analyzing hacked data
Voting models and other leaked data were “worth millions,” consultant told Guccifer 2.0. A Florida GOP campaign consultant who runs a blog...
-
 208
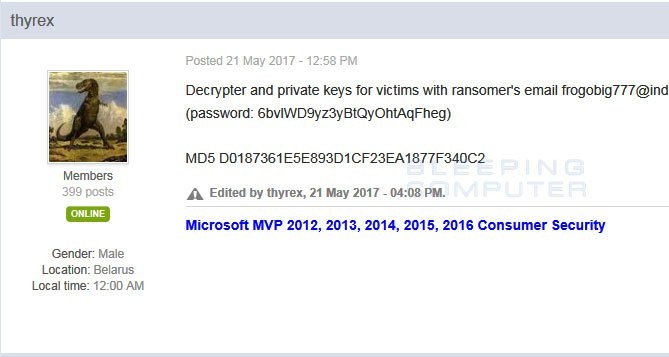
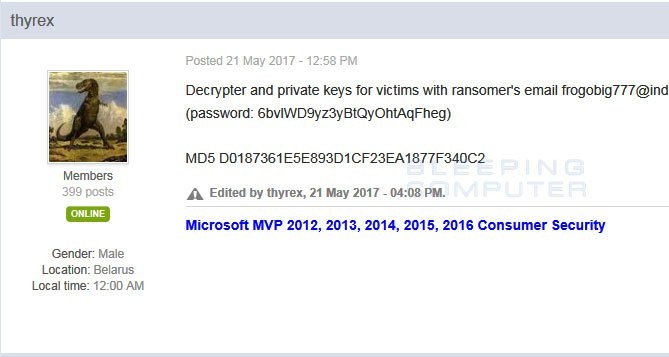
208AES-NI Ransomware Dev Releases Decryption Keys Amid Fears of Being Framed for XData Outbreak
On May 21st, a security researcher who goes by the name Thyrex, received a message on a Russian forum that contained a link...
-
 184
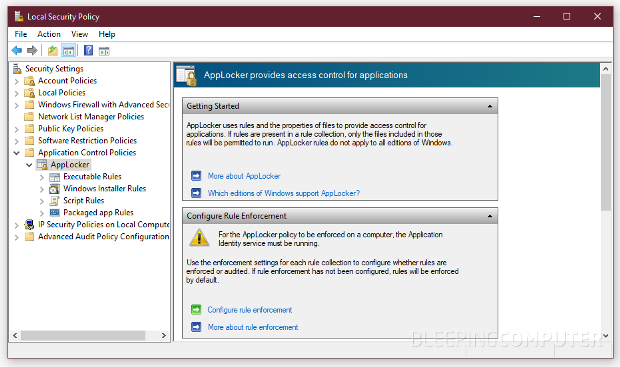
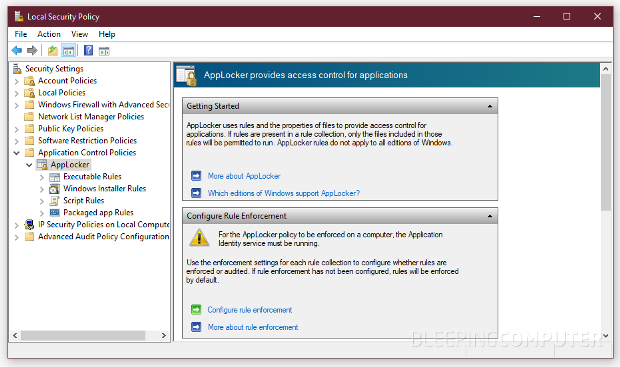
184You Can Bypass Windows AppLocker Protection via Rogue Control Panel Items
An attacker or a rogue employee can create and register custom control panel items and use these files to bypass the Windows...
-
 187
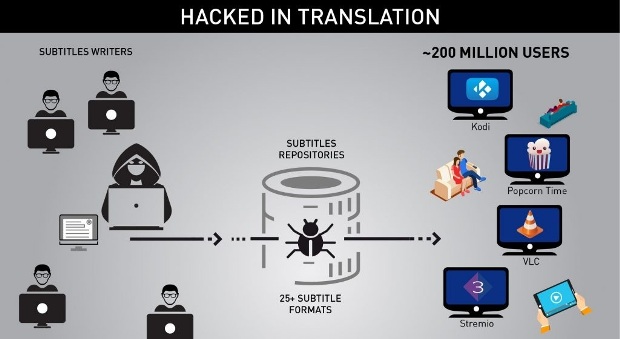
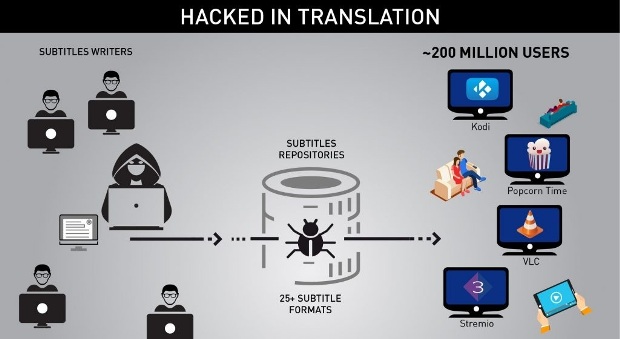
187Hacked in Translation – from Subtitles to Complete Takeover
Check Point researchers revealed a new attack vector which threatens millions of users worldwide – attack by subtitles. By crafting malicious subtitle...
-
 199
199Europol arrested 27 for jackpotting attacks on ATM across the Europe
27 people have been arrested by the Europol for jackpotting attacks on ATM across many countries in Europe. Europol has arrested 27...
-
 208
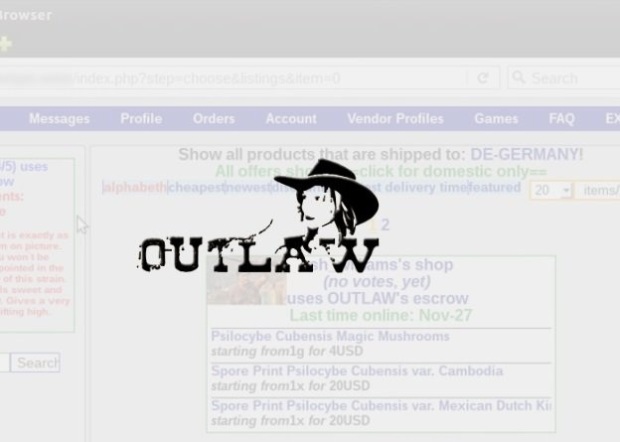
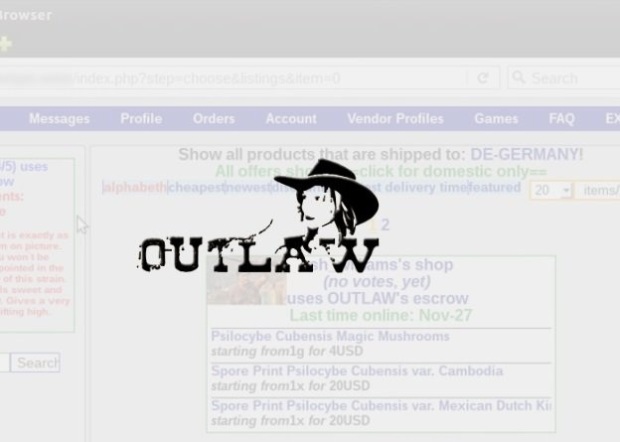
208Dark Web Market Shuts Down Claiming Hack, but Users Fear an Exit Scam
The Outlaw Dark Web market has shut down this week under mysterious circumstances, and while admins said the site closed down after...
-
 184
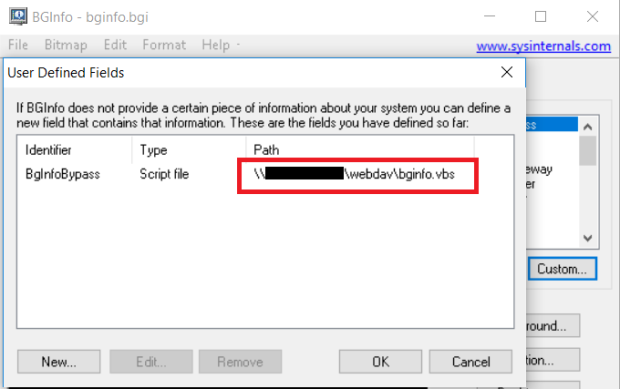
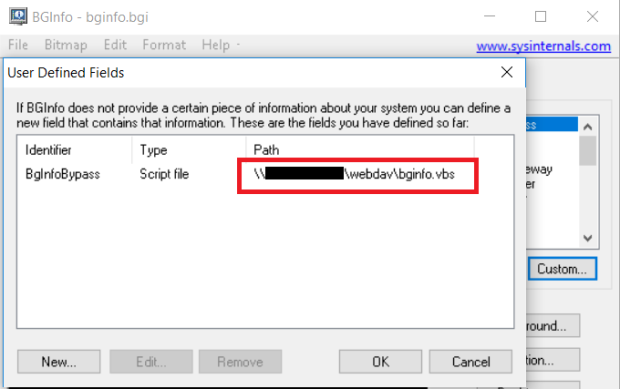
184Bypassing Application Whitelisting with BGInfo
BGinfo.exe older than version 4.22 can be used to bypass application whitelisting using vbscript inside a bgi file. This can run directly...
-

 100
100A hack has put data of 17 million Zomato users at risk: Should India be worried?
It’s sad, but someone, somewhere on the Dark Web will now be privy to all your eating habits, or at least the...
-

 189
189Fearing Shadow Brokers leak, NSA reported critical flaw to Microsoft
WaPo confirms long-held suspicions as NSA cyberweapons crisis threatens to grow worse. After learning that one of its most prized hacking tools...
-

 88
88Security Guard Hacks and Trashes Company Servers After Quitting His Job
A California judge has found Yovan Garcia, a former security guard, guilty for hacking his former employer, stealing proprietary software, and trashing...
-

 202
202Bell Canada hacked, 1.9 million customer account details stolen by hackers
The telco giant Bell Canada was the victim of a security breach that exposed roughly two million customer account details. The long...
-
 214
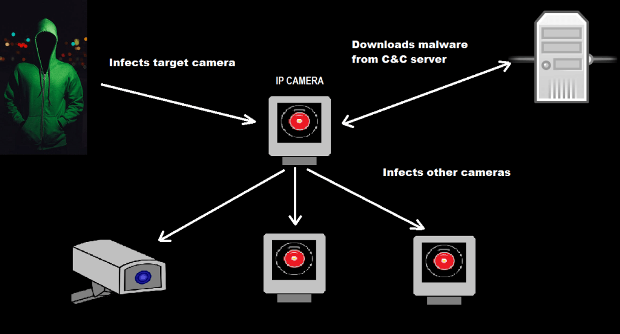
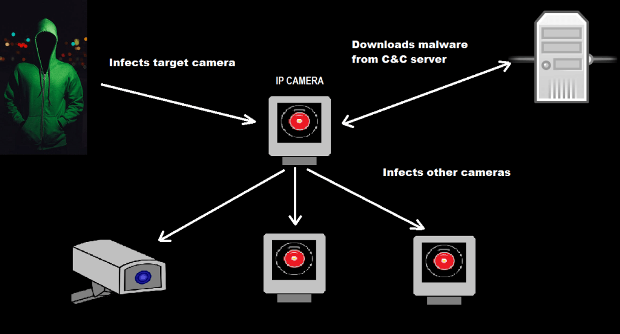
214New IOT Attack Linked To Iran – Persirai Malware Strikes at IP Cameras in Latest IOT Attack
Trend Micro has discovered a new attack on internet-based IP cameras and recorders powered by a new Internet of Things (IOT) bot...
-

 132
132Major French news sites victim of DDoS attack
Major news sites in France including Le Monde and Le Figaro went down yesterday in the fallout of a DDoS attack. Many...
-

 78
78Telefonica Tells Employees to Shut Down Computers Amid Massive Ransomware Outbreak
A ransomware outbreak is wreaking havoc all over the world, but especially in Spain, where Telefonica — one of the country’s biggest...
-

 309
309Edge Security Flaw Allows Theft of Facebook and Twitter Credentials
Argentinean security researcher Manuel Caballero has discovered another vulnerability in Microsoft’s Edge browser that can be exploited to bypass a security protection...
-
 335
335Linux and Other Open Source Technologies Protect Online Privacy: Snowden
Short Bytes: At the OpenStack Summit, the ex-NSA contractor talked about the downsides of proprietary software and their threat to people’s privacy....
-

 169
169San Bernardino iPhone Hack: U.S. Senator Reveals How Much the FBI Spent on It
Despite the information being deemed classified, the number is now out thanks to Senator Feinstein’s mistake. The FBI won’t reveal how exactly...
-
 215
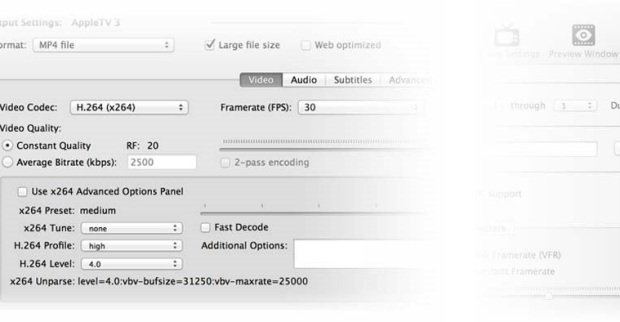
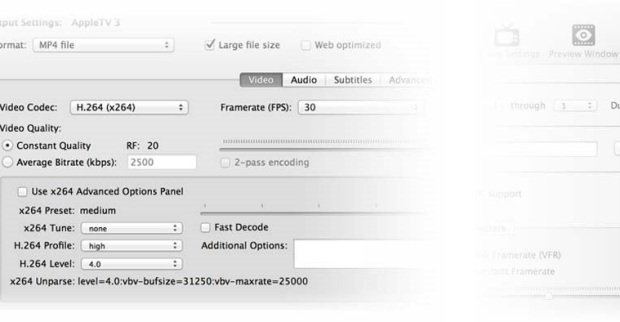
215Website of HandBrake App Hacked to Spread Proton RAT for Mac Users
The website of the HandBrake app has been compromised, and one of its download mirrors modified to host a version of the...
-

 87
87Emmanuel Macron’s party says it’s been hit by “massive” hack
Thousands of documents allegedly from Macron’s party were leaked less than two days before the final round of the French presidential election....
-

 242
242How do hackers hide their IP address?
How do hackers hide their IP address from prying eyes. Hackers are known for breaking into most impregnable web servers around the...
-
 175
175How to remote hijack computers using Intel’s insecure chips: Just use an empty login string
Exploit to pwn systems using vPro and AMT. Code dive You can remotely commandeer and control computers that use vulnerable Intel chipsets...






