Incidents
-
 246
246Database Ransom Attacks Hit CouchDB and Hadoop Servers
For the past week, unknown groups of cyber-criminals have taken control of and wiped data from CouchDB and Hadoop databases, in some...
-
 371
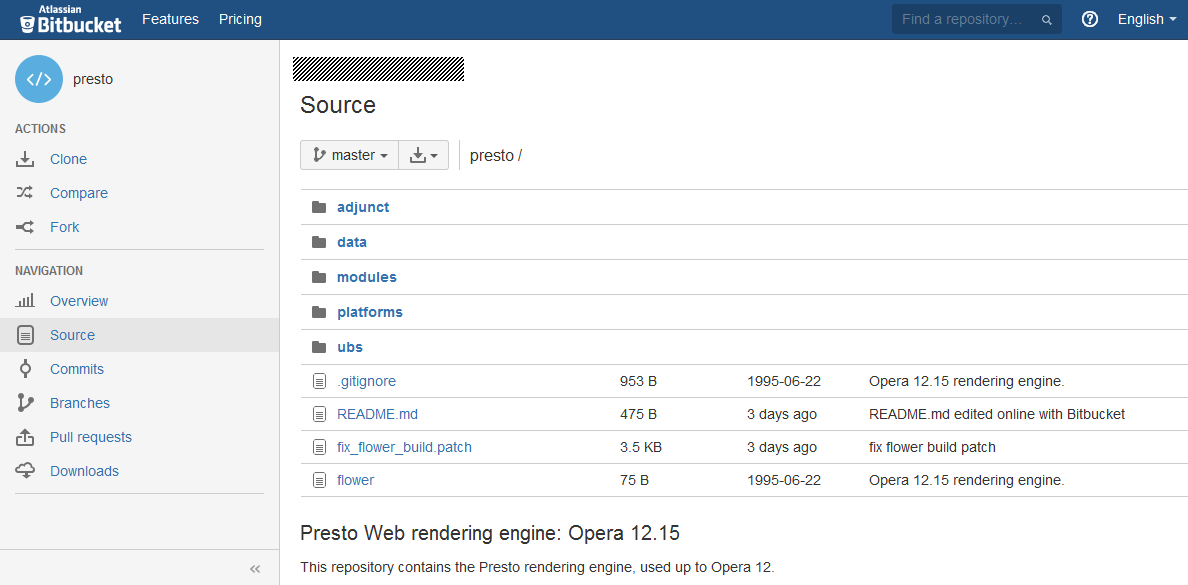
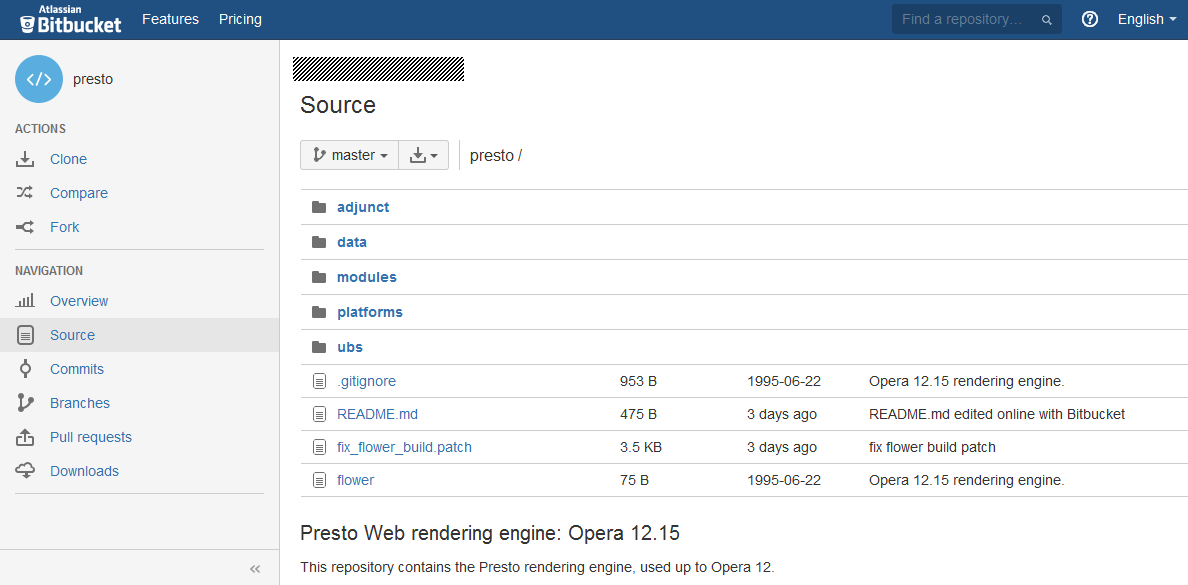
371Opera Presto Source Code Leaks Online
An unknown third-party has leaked the source code of the old Opera Presto browser engine on GitHub, and later on Bitbucket, two...
-

 156
156Hackers Steal Forum Accounts From ‘Clash of Clans’ Creator Supercell
Data traders are allegedly swapping the details of over one million user accounts belonging to Supercell, the company behind hit mobile games...
-

 138
138Author of Limitless Keylogger Faces Up to 10 Years in Prison
Zachary Shames pleaded guilty today to charges of developing and selling malware that was later used to infect thousands of victims. Before...
-

 96
96Detroit Car Makers Allegedly Hacked, Names and Social Security Numbers Stolen
General Motors already notifying employees about the breach. Detroit’s Big Three automakers are the latest big companies to become victims of hackers,...
-
 199
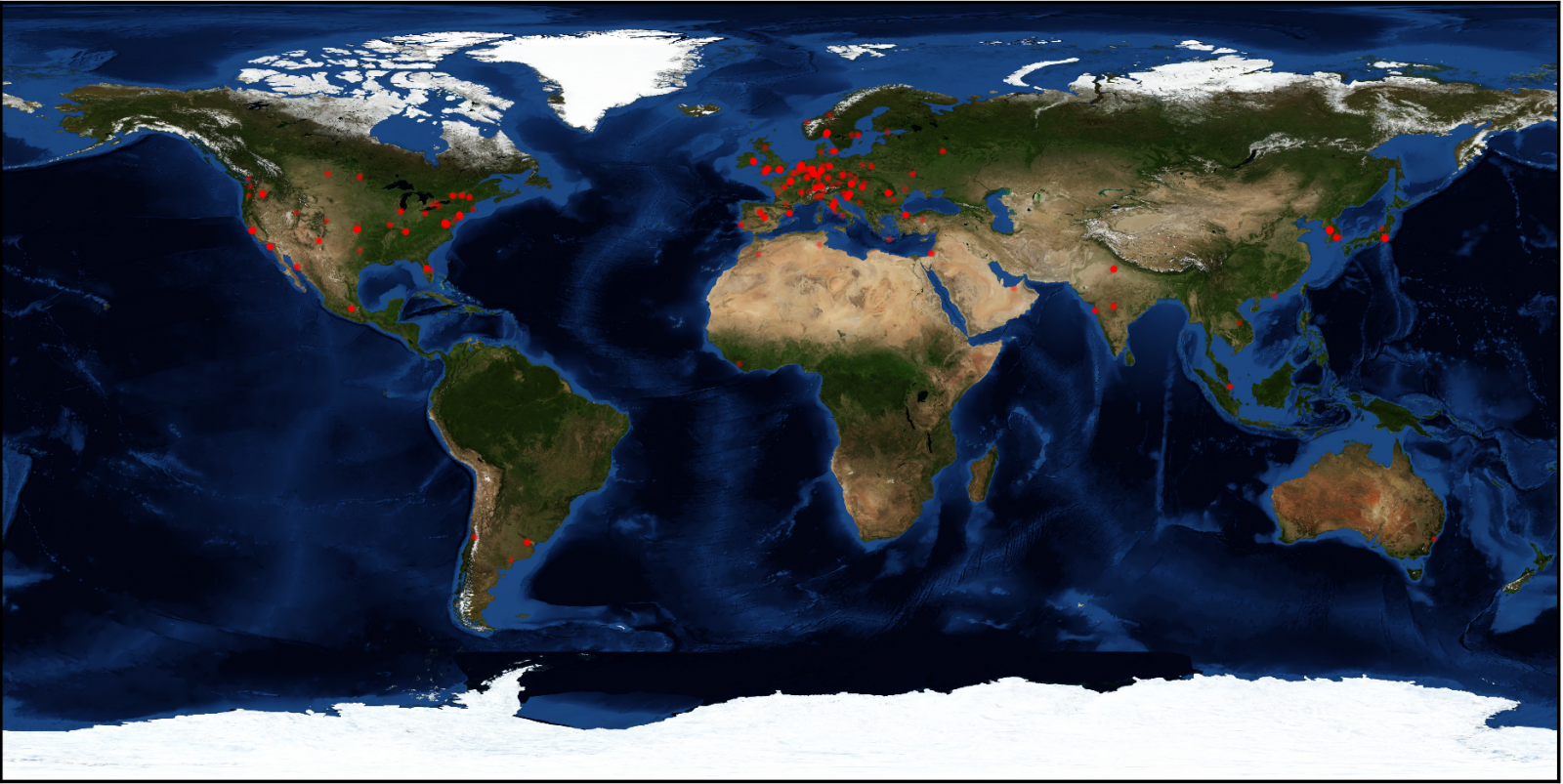
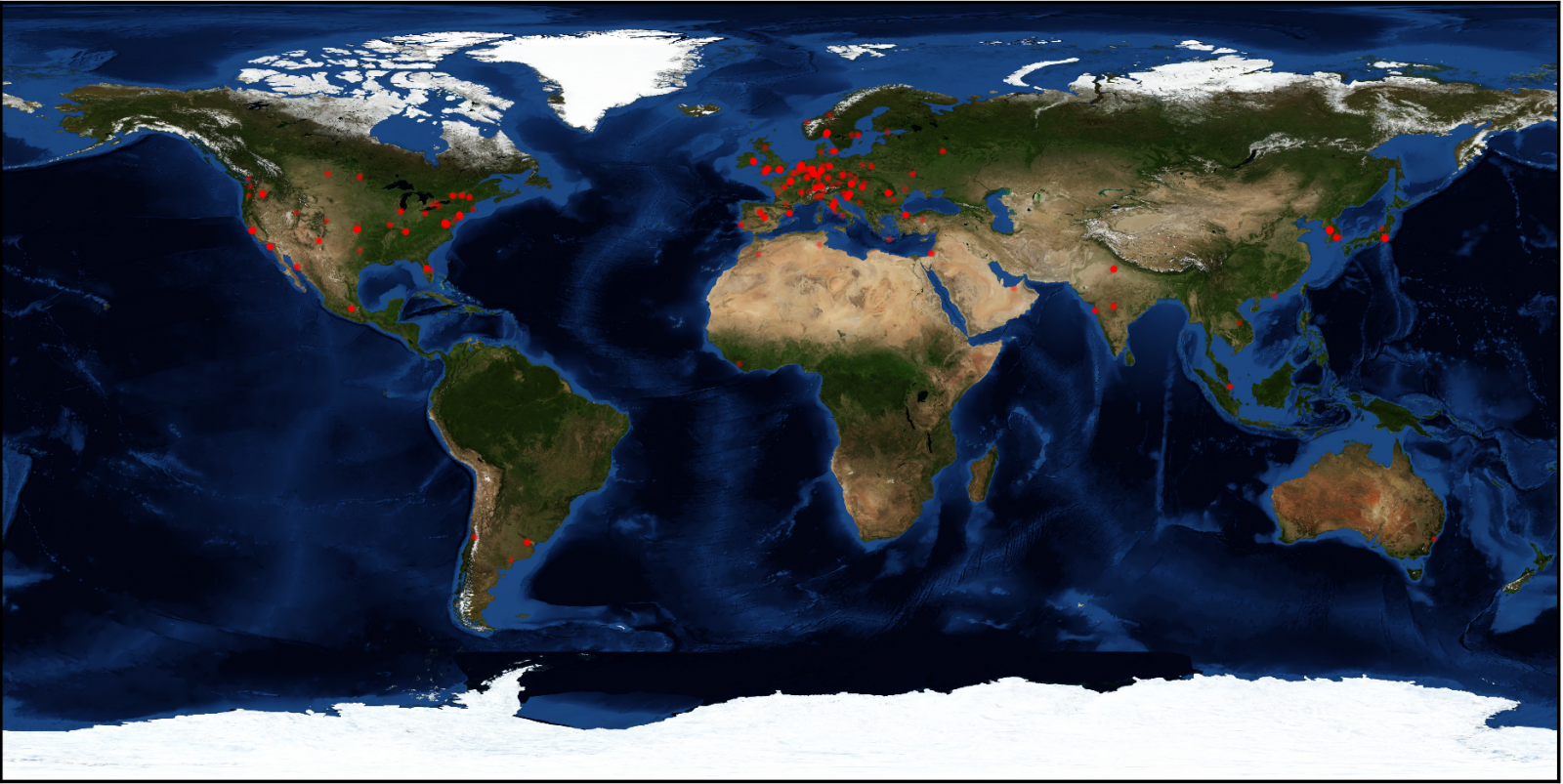
199Misconfigured Server Gives Insight Into Cerber Ransomware Operation
Security researchers have gained access to one of the servers used by the Cerber gang, from where they were able to extract...
-

 97
97Japanese researchers: your peace-sign selfies are putting you at risk
If flashing a peace sign is your go-to selfie move, you might want to think about coming up with a new signature...
-

 231
231Airport boarding gate display leaks booking codes, puts passenger data at risk
Attackers could gain full control over passenger bookings, cancel flights, and steal sensitive information with leaked booking codes. While waiting for my...
-
 197
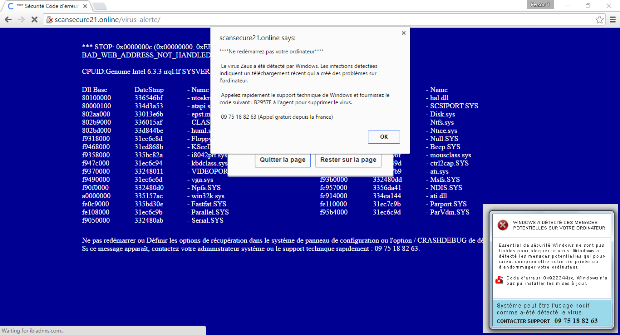
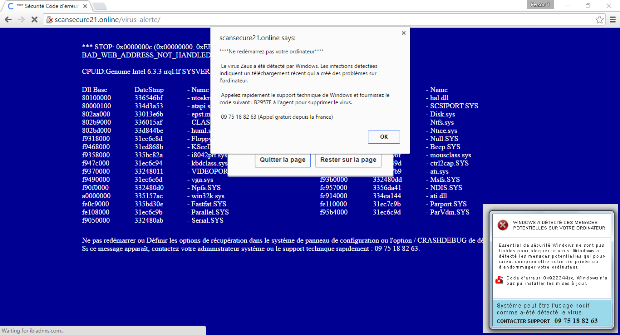
197Watch Tech Support Scam Take Over a Browser via Facebook Ads
Facebook users in France are subject to a wave of malicious ads, which if clicked, will redirect them to a website hosting...
-

 182
182ShadowBrokers offers for sale the stolen NSA Windows Hacking Tools
The ShadowBrokers is the hacker crew stolen the arsenal of the NSA-Linked Equation Group is offering for sale the stolen NSA Windows...
-
 112
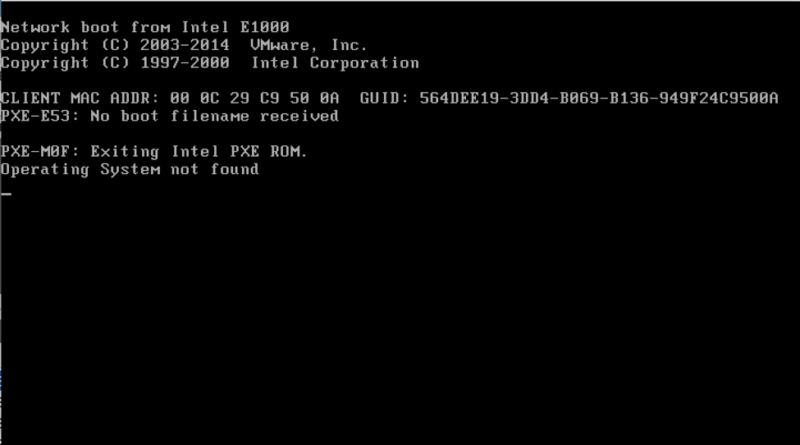
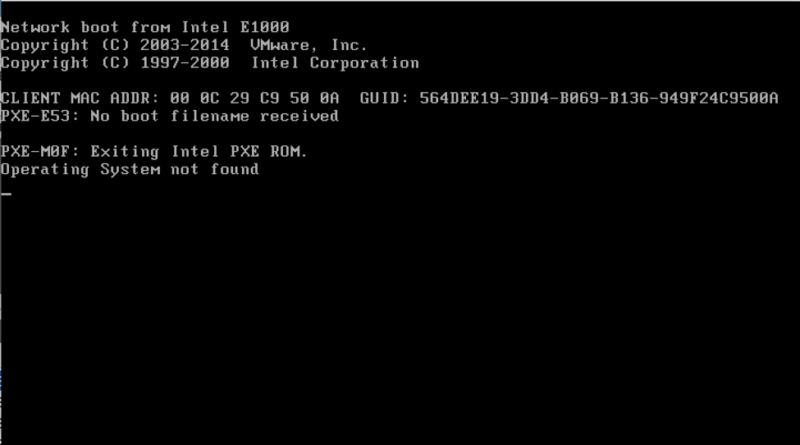
112Shamoon disk-wiping attackers can now destroy virtual desktops, too
Mystery malware begins targeting a key disk-wiping defense. There’s a new variant of the Shamoon disk-wiping malware that was originally unleashed on...
-

 109
109The Los Angeles Community College District paid a $28,000 ransom to decrypt its files
The Los Angeles Community College District has paid a US$28,000 ransomware after crooks compromised its network. Fortunately, the school retrieved data. A...
-
 145
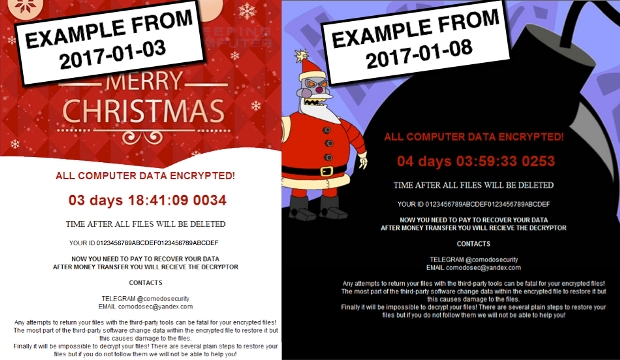
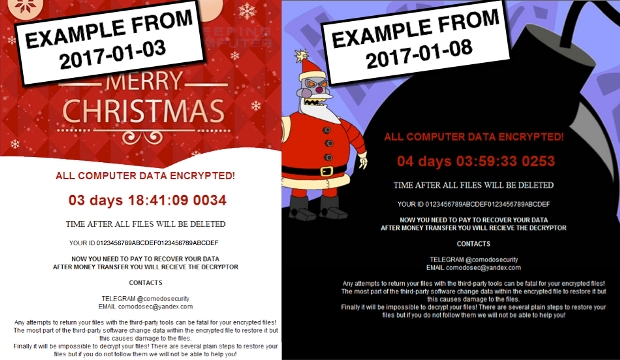
145“Merry Christmas” Ransomware Now Steals User Private Data via DiamondFox Malware
Recent variants of the “Merry Christmas” ransomware, also known as Merry X-Mas, are also dropping the DiamondFox malware on infected computers, which...
-

 248
248Connected car hacking: Who’s to blame?
I’ve just about recovered from the sensory overload that is CES to gather my thoughts from what was another fascinating event. This...
-

 261
261Verizon Again Having Second Thoughts on Yahoo Deal After 1 Billion Account Hack
Executives still looking into the deal, it seems. Verizon is once again unsure whether to complete the takeover of Yahoo or not,...
-
 183
183Browser Autofill Profiles Can Be Abused for Phishing Attacks
Browser autofill profiles are a reliable phishing vector that allow attackers to collect information from users via hidden fields, which the browser...
-
 169
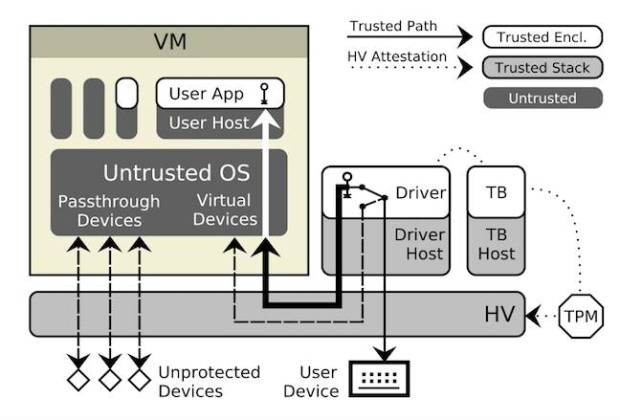
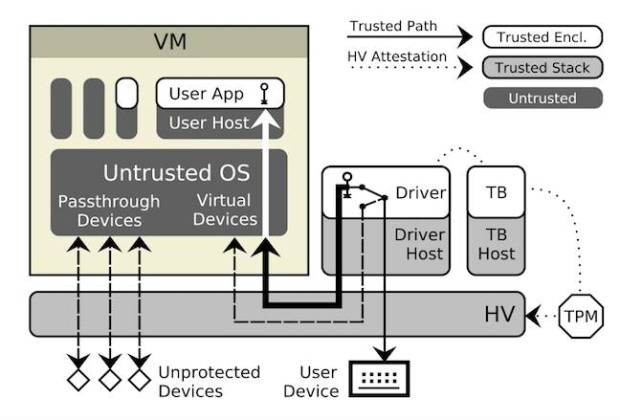
169Researchers work to save trusted computing apps from keyloggers
SGX needs I/O protection, Austrian boffins reckon. Intel’s Software Guard Extensions started rolling in Skylake processors in October 2015, but it’s got...
-

 168
168Google Brazil hacked, Google.com.br unavailable to Brazilians
A hacker going by the online handle of “Kuroi’SH” hacked and defaced the official Google Brazil domain earlier Tuesday afternoon. The hacker...
-

 229
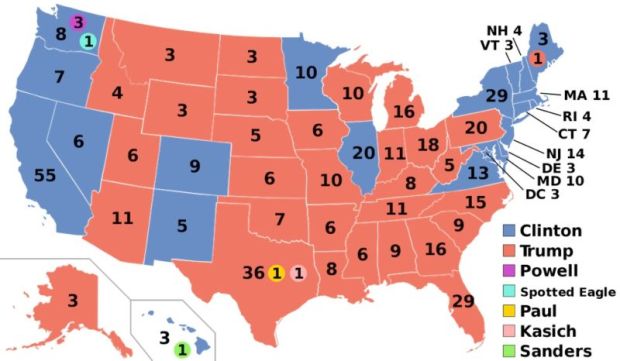
229Snowden document suggests NSA could have proof of Russian hack
Looks like the NSA has a history of positively identifying Russian hacks. The FBI, CIA and President Barack Obama all agree that...
-

 235
235MongoDB Databases Held Up for Ransom by Mysterious Attacker
An attacker going by the name of Harak1r1 is hijacking unprotected MongoDB databases, stealing their content, and asking for a Bitcoin ransom...
-
 181
181White House fails to make case that Russian hackers tampered with election
US issued JAR billed itself as an indictment that would prove Russian involvement. Talk about disappointments. The US government’s much-anticipated analysis of...






