Incidents
-
 154
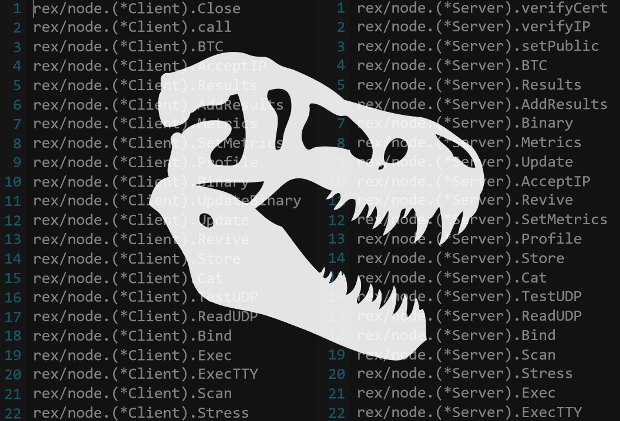
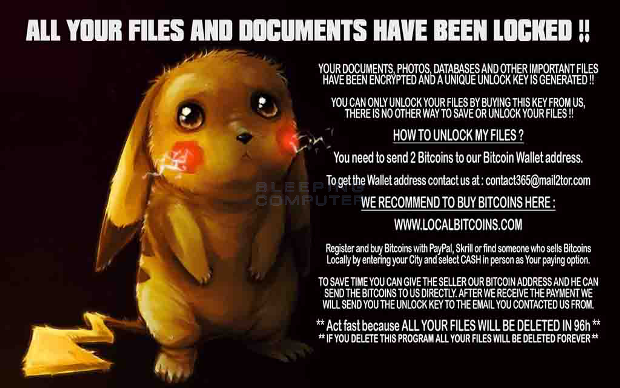
154Rex Linux Trojan Can Launch DDoS Attacks, Lock Websites, Mine for Cryptocurrency
Trojan targets CMS platforms running on Linux servers. What initially looked like a string of Drupal sites infected with ransomware (that didn’t work...
-
 219
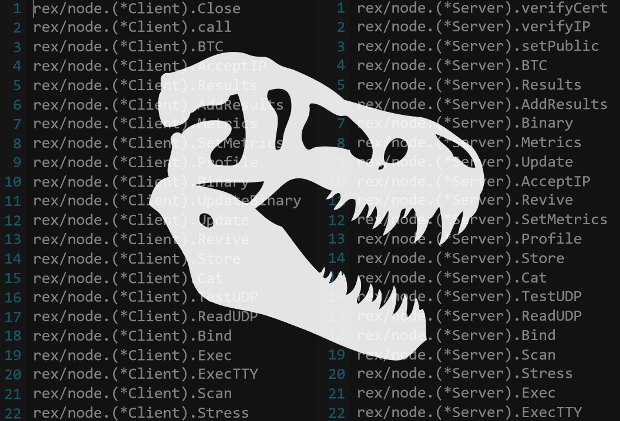
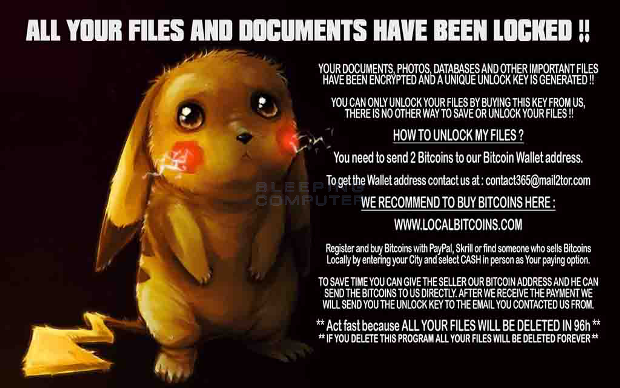
219New DetoxCrypto Ransomware pretends to be PokemonGo or uploads a Picture of your Screen
A new ransomware called DetoxCrypto has been discovered by MalwareHunterTeam that is currently being distributed under two different variants. The first variant looks...
-

 154
154Bitcoin.org suspects state-sponsored attacks on the horizon
Bitcoin traders have been warned that the upcoming Bitcoin Core software release will become a top target for well-funded hacking groups. Bitcoin.org...
-
 84
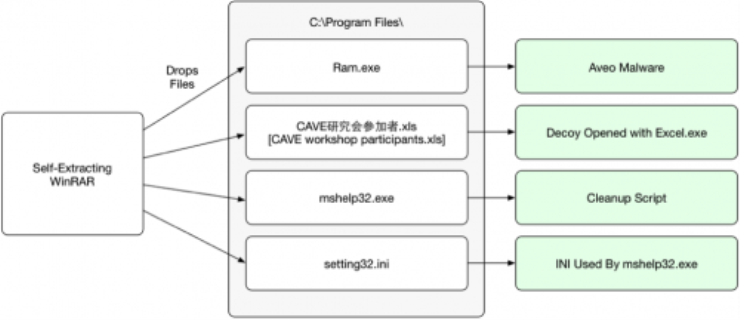
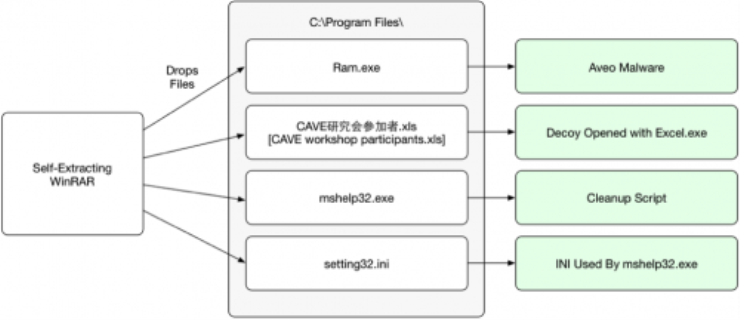
84Aveo Trojan Used in Attacks Against Japanese Users
Palo Alto Networks has identified a malware family known as ‘Aveo’ that is being used to target Japanese speaking users. The ‘Aveo’...
-

 203
203Starwood, Marriott, Hyatt, IHG hit by malware: HEI
A data breach at 20 U.S. hotels operated by HEI Hotels & Resorts for Starwood, Marriott, Hyatt and Intercontinental may have divulged...
-

 306
306World Anti-Doping Agency Site Hacked; Thousands of Accounts Leaked
ANONYMOUS POLAND HACKED WORLD ANTI-DOPING AGENCY AND COURT OF ARBITRATION FOR SPORT’S SERVERS’ SERVER AND LEAKED PERSONAL DETAILS FOR GOD KNOWS WHAT REASON!...
-

 101
101With the looming threat of Ransomware, should companies stockpile Bitcoins?
With the threat of ransomware hanging over every company’s head, does it make sense for companies to stockpile a few bitcoins in the...
-

 66
66Instagram accounts hacked, altered to promote adult dating spam
Scammers are hacking Instagram accounts and altering profiles with sexually suggestive imagery to lure users to adult dating and porn spam. Earlier...
-

 198
198Oracle-owned point-of-sale service suffers from malware attack
A Russian organized cybercrime group known for hacking into banks and retailers appears to have breached hundreds of computer systems at software giant...
-

 128
128This man hacked Tinder’s ”swipe right” feature to send invites to 200,000 women
Love Hack : Man hacks Tinder App’s ‘swipe right’ feature to send introductions to 200,000 women Hacking is mostly done to either...
-

 189
189How hackers used this Trojan malware to spy on a territorial dispute
F-Secure researchers say parties involved in the South China Sea arbitration case were infected with the data-stealing NanHaiShu Trojan. Hackers have used...
-

 96
96Bitcoin exchange Bitfinex reports $65 million has been stolen from its users
Bitcoin exchange platform Bitfinex is reporting the theft of what some users are saying is as much as 119,756btc — or about...
-

 84
84This $6 Hacker Tool Pops Cash Registers And Hotel Rooms Wide Open
It’s no secret hotel rooms can be hacked into. One security researcher has now created a cheap, discrete device the size of a card...
-
 75
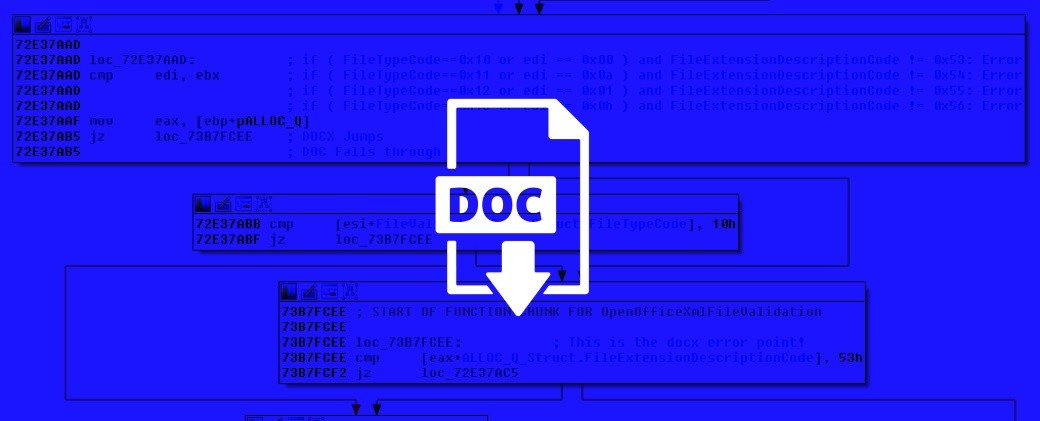
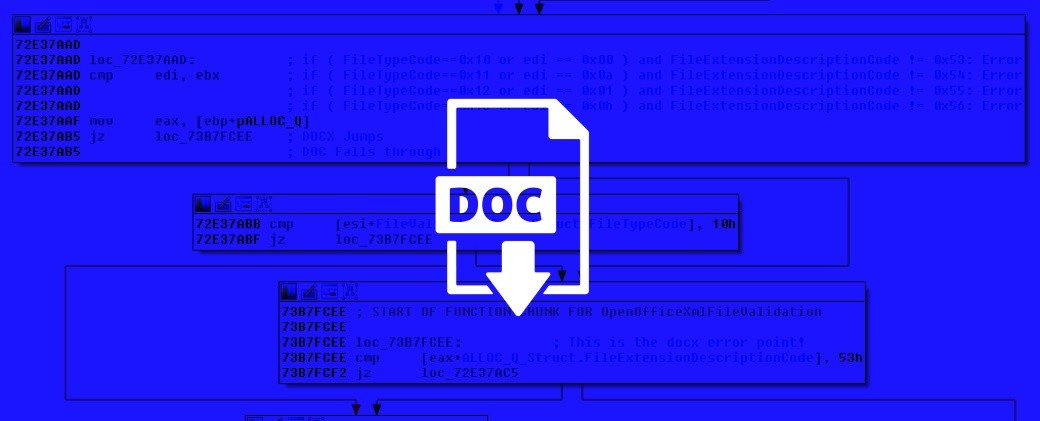
75Renaming Office Files Is Enough to Disguise Macro Malware
Macros have been used since the mid 1990s to spread malware and infect systems. Increased user awareness of the need to disable...
-
 119
119Windows Flaw Reveals Microsoft Account Passwords, VPN Credentials
Attack from the ’90s resurfaces more deadly than before. A flaw in how Windows handles old authentication procedures for shared network resources can...
-

 118
118Yahoo probing potential data breach as 200 million user accounts appear on Dark Web
A hacker using the pseudonym “Peace” has uploaded what purports to be a data dump of 200 million Yahoo accounts to an...
-
 197
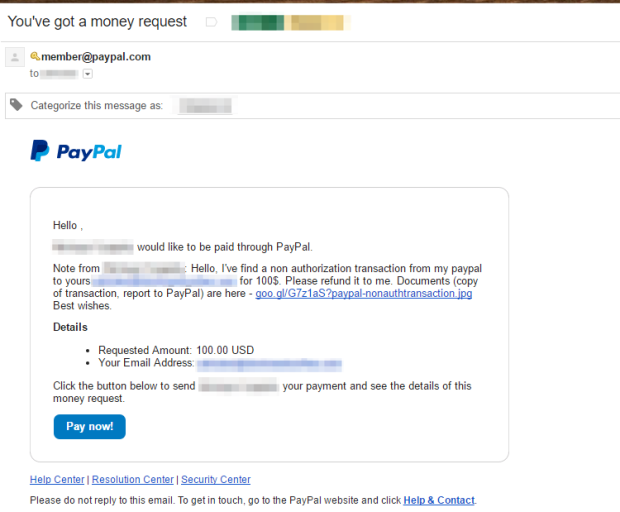
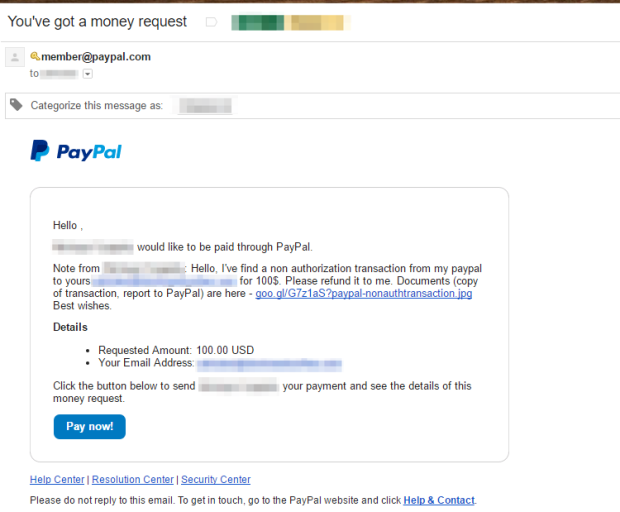
197Threat Actors Using Legitimate PayPal Accounts To Distribute Chthonic Banking Trojan
While many email providers, clients, and anti-spam engines have become adept at detecting spam, malicious messages sent via high-profile, legitimate providers are...
-

 119
119Niantic CEO John Hanke’s Twitter Account Hacked
Fueled by the lack of Pokémon GO in Brazil, a hacker group called OurMine took control of Niantic CEO John Hanke’s Twitter...
-

 76
76Proxy PAC hack allows for intercept of HTTPS URLS
Israeli experts discovered a vulnerability within the JavaScript that proxy PAC files that allows HTTPS URLs interception via Proxy Attacks. Israeli security...
-

 200
200LulzSec Member Reveals More Details About GCHQ Covert Operations
GCHQ’s JTRIG team targeted more than hacktivists. Mustafa Al-Bassam, aka tFlow, co-founder of the LulzSec hacking crew, published today more details about how...
-

 114
114Scammers exploit recent wave of attacks to trick victims with phishing attacks
Scammers exploit the recent a wave of attacks to trick victims with phishing offensive and steal sensitive data from the unaware users....






