Incidents
-

 109
109WordPress Sites Leveraged in Layer 7 DDoS Campaigns
We first disclosed that the WordPress pingback method was being misused to perform massive layer 7 Distributed Denial of Service (DDoS) attacks back in...
-

 120
120Password cracking attacks on Bitcoin wallets net $103,000
“Active attacker community” often emptied accounts minutes after they went live. Hackers have siphoned about $103,000 out of Bitcoin accounts that were protected...
-

 146
146Hackers Demand $3.6 Million From Hollywood Hospital Following Cyber-Attack
Hospital staff severely impeded in their day-to-day work. The Hollywood Presbyterian Medical Center, a 430+ beds hospital in the middle of Los Angeles,...
-
 132
132Hacker Leaks The Personal Information Of 20,000 FBI Agents
Short Bytes: An attack by a hacker has just revealed the sensitive information of about 20,000 FBI employees. Besides this personal contact...
-

 114
114Clever bank hack allowed crooks to make unlimited ATM withdrawals
Banking malware is using techniques once reserved for state-sponsored hacking gangs. To appreciate how malware targeting banks and other financial institutions is...
-

 228
228Avast SafeZone Browser Lets Attackers Access Your Filesystem
Another antivirus maker decides to mess around with Chromium default security features and gets it totally wrong. Just two days after Comodo’s...
-

 237
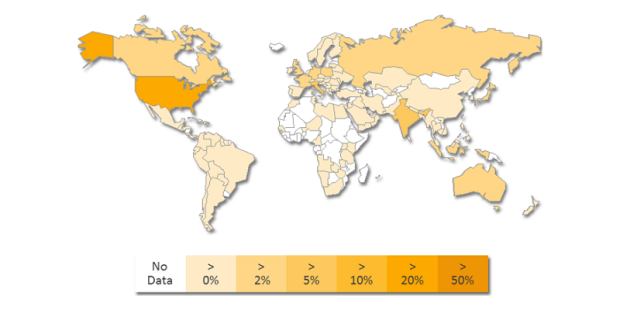
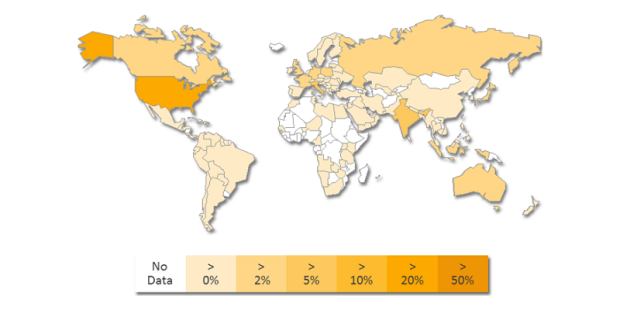
237Login duplication allows 20m Alibaba accounts to be attacked
The reuse of login details on Alibaba’s Taobao has allowed an attack on 5 percent of the accounts on Alibaba’s Chinese retail...
-
 159
159Comodo Internet Security Installs New Browser by Force, Disables All Web Security
The Comodo app also replaces links and hijacks DNS. Developers have exposed the fact that Comodo Internet Security is actually a security threat...
-
 214
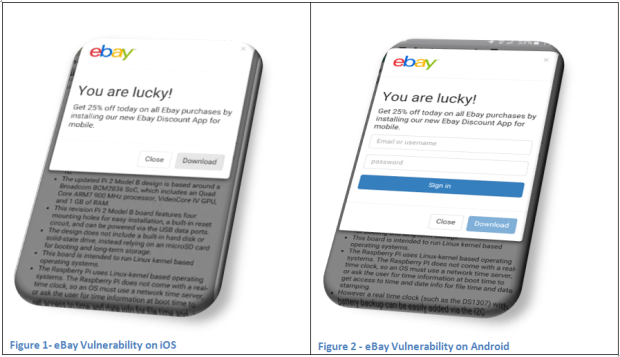
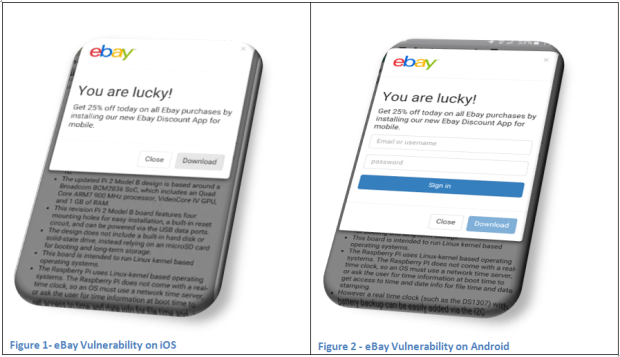
214eBay Flaw Lets Attackers Push Malware and Launch Phishing Sites
JSF**k JavaScript library abused to deliver malware. Security researchers have alerted eBay’s staff about a vulnerability in its online platform that lets...
-

 186
186NASA hacked by AnonSec that hijacked a $222m Global Hawk drone
Anonsec group hacked NASA network and released a data dump of data online. The hackers also hijacked a Global Hawk drone. Hackers belonging...
-
 111
111Default settings on Apache Web servers can reveal details about Tor traffic
Default Settings In Apache Servers Can Leak Details about Tor traffic. This has happened the second time in this week. Leaving default setting...
-

 103
103ISIS – The first man charged of cyber terrorism has been extradited to the US
Malaysia extradited a hacker charged by DoJ with stealing the personal data of US members and passing it to the ISIS. A...
-

 194
194HSBC online banking services offline due to a DDoS attack
The British branch of the HSBC bank has suffered for the second time in a month a cyber attack that brought its...
-

 101
101NSA’s top hacking boss explains how to protect your network from his attack squads
Rare public appearance from Tailored Access Operations leader. USENIX ENIGMA The United States National Security Agency (NSA) is a notoriously secretive organization, but...
-

 180
180Nuclear Threat Initiative says nations not prepared to repel cyber attacks on nuclear facilities
According a report from the Nuclear Threat Initiative, numerous nations are not prepared’ to handle the cyber attacks focusing on their nuclear facilities. Numerous...
-

 141
141Israeli Public Utility Authority hit by a severe cyber attack
The Israeli Public Utility Authority is suffering one of the largest cyber attack that the country has experienced, Minister of Infrastructure, Energy...
-

 327
327OpKillingBay – Anonymous shut down Japanese airport site to protest against slaughter of Dolphin
OpKillingBay – A group of hackers linked to the Anonymous collective shut down the Japanese Airport Website to protest against the slaughter of Dolphin....
-
 104
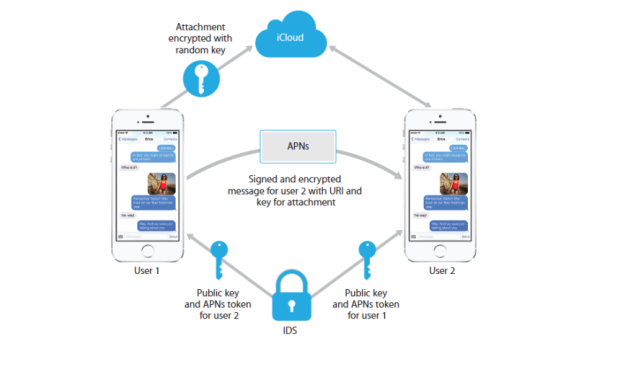
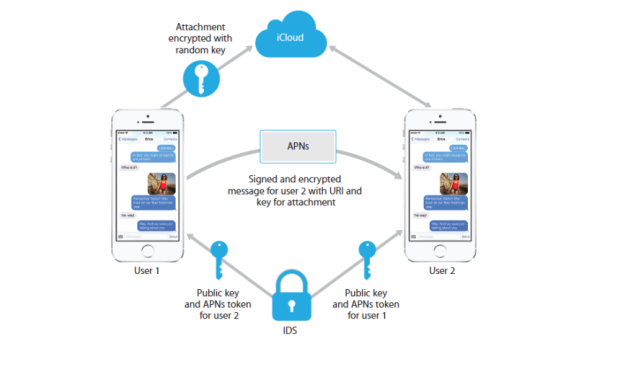
104Apple Can Still See Your iMessages If You Enable iCloud
Apple has taken a strong stance on privacy ever since the FBI began loudly demanding encryption backdoors into its products. The company’s...
-

 225
225EDA2 Open-Source Ransomware Code Used in Real-Life Attacks
Another educational open-source ransomware project goes bad. Cyber-crooks have used the open-source code of the EDA2 ransomware to create the Magic ransomware...
-
 96
96Web Reconnaissance Attack Infects 3,500 Websites, Possibly WordPress
Attackers are adding unauthorized code at the top of infected websites, over 3,500 8sites already infected. Alarms are ringing in Symantec’s offices,...
-

 198
198Chinese Group Trying to Exploit Old Fortinet SSH Backdoor
Scans for Fortinet devices have intensified. An unknown group has been scanning the Internet for old Fortinet equipment that includes a secret SSH...






