Malware
-

 269
269Decrypt files attacked with the latest versions of GandCrab ransomware
Recover your encrypted files with this free tool A tool recently launched by experts in cybersecurity and digital forensics allows you to...
-
 182
182Unpatched Critical Bug in Microsoft Word Online Video Feature Allow Attacker to Deliver Powerful Malware
An unpatched bug that abusing Microsoft word Online Video future that allow an attacker to deliver malicious files into the victim’s system....
-
 304
304New Malware Abusing Two Legitimate Windows Files to Steal Victims Personal Data
Researchers discovered a new malware that abusing two legitimate windows files and use it against compromised victims to steal sensitive information. One...
-

 255
255West Haven pays $2k USD because of ransomware attack
According to experts, many municipalities attacked with ransomware do not have many options when facing such an incident The city of West...
-

 194
194New Android Malware Turns Your Mobile Devices into Hidden Proxies
Cyber criminals distributing new Android malware via Phishing email campaign that turns infected smartphones into hidden mobile proxies. This malicious app installing...
-
 284
284Banking Trojans continue to surface on Google Play
The malicious apps have all been removed from the official Android store but not before the apps were installed by almost 30,000...
-

 311
311DarkPulsar – A Shadow Brokers Group’s New Hacking Tool Leak To Open Backdoor & Provide Remote Control
Shadow Brokers Hacking Group’s new administrative module Tool called DarkPulsar Leaks with persistance backdoor to provide remote control to the attackers. There...
-

 211
211APT Group Uses Datper Malware To Launch Cyber Attack on Asia Countries by Executing Shell Commands
An advanced persistent threat (APT) actor group known by several different names such as Tick, Redbaldknight and Bronze Butler carried out a...
-

 409
409VestaCP compromised in a new supply‑chain attack
Customers see their admin credentials stolen and their servers infected with Linux/ChachaDDoS
-

 201
201LuminosityLink tool creator sentenced to 30 months in prison
The tool allowed access to the victims’ computers without their consent A 21-year-old man living in Kentucky, who had previously plead himself...
-

 223
223Cybercriminals Advertising Godzilla Loader Malware On Dark Web Forums
Cybercriminals Advertising Godzilla Loader Malware for $500 on Dark web forums, the malware found actively maintained and getting new updates periodically. Godzilla...
-

 303
303NotPetya linked to the Industroyer attack against energy infrastructure in Ukraine
Three of the most destructive incidents seen in modern cybersecurity are the work of the same APT The Last year occurred the...
-
 220
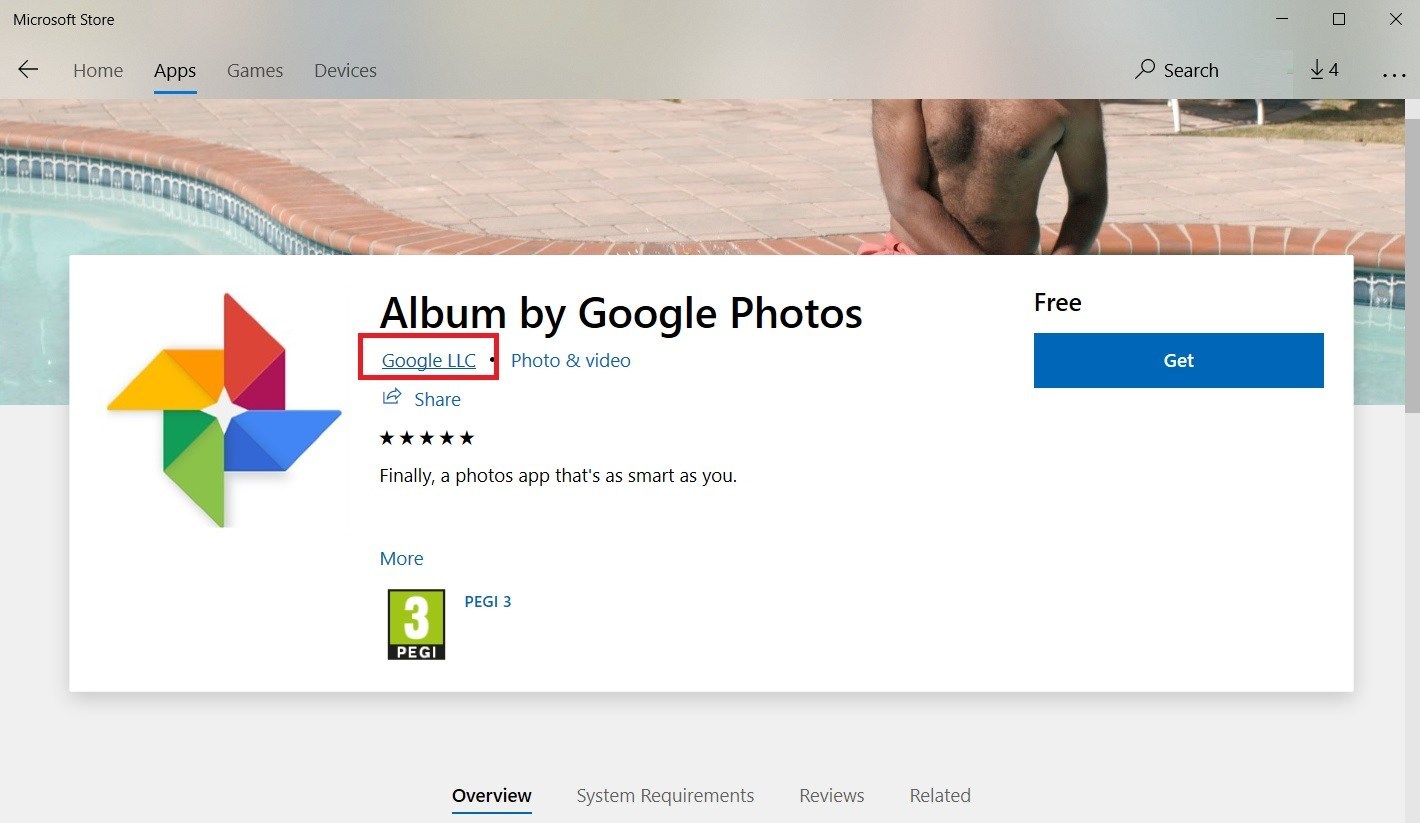
220Hackers Abuse Microsoft Store & Publish Fake Google Photos App under Google LLC Name
Third-party developers abusing Microsoft Apps store & publish fake Google Photos App under the Google LLC name but it is originally an...
-
 180
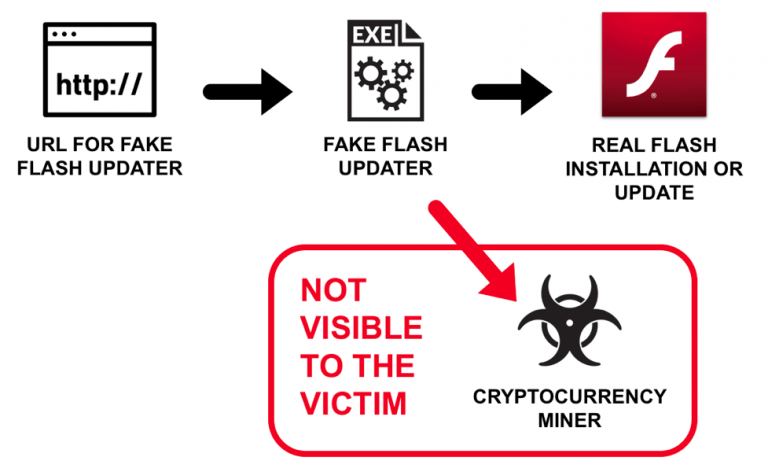
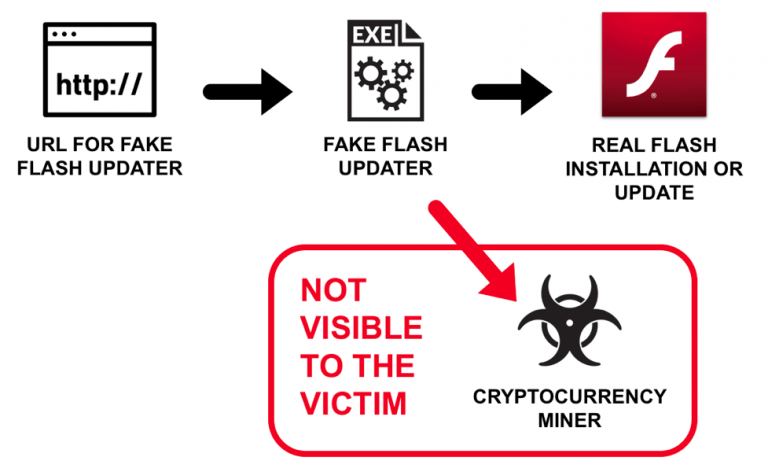
180Fake Flash Updates pushing Malware to Inject XMRig Cryptocurrency Miners
Newly discovered fake flash updates malware pushing XMRing Cryptocurrency miners along with borrowing the original Adobe installer flash updater notification. Recent campaigns are...
-
 238
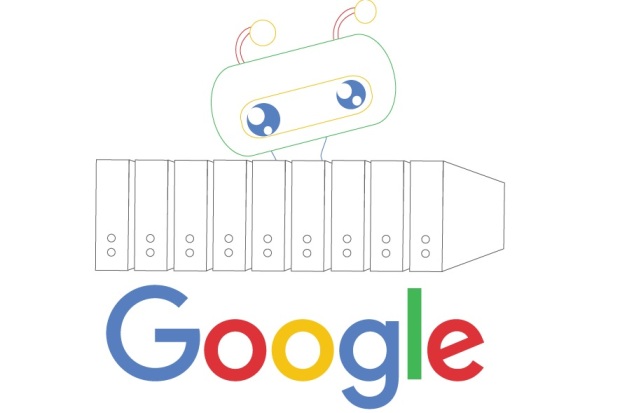
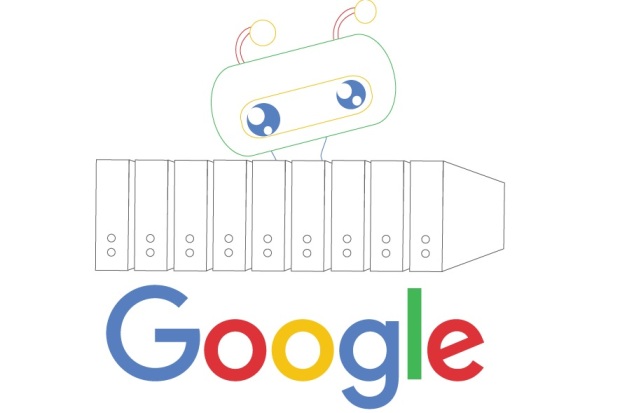
238Hackers use Googlebot in mining malware attacks
Cybercriminals abuse Googlebot servers to deliver malicious payloads in new campaign Last year, a malware campaign used Google Adwords and Google Sites...
-

 232
232The biggest CCTV manufacturer left at least 9 million devices opened to everyone’s eyes
The cloud portal of Xiongmai left opened a backdoor to its servers Another Internet of Things (IoT) device provider has been discovered...
-

 225
225Cryptomining software is hidden as Flash update
A cryptocurrency mining malware is disguised as a Flash update that appears to be legitimate, warn researchers Cryptomining popularity exploded in 2017...
-

 397
397Gallmaker Hacking Group Attack Government, Military, and Defense Sectors Using Publicly Available Hacking Tools
A new previously unknown hacking group appeared as Gallmaker attacking various public sectors such a government, military, and defense using custom malware. Attacker...
-

 278
278Hackers Abusing Legitimate Googlebot Services to Inject Cryptomining Malware
Cybercriminals now abusing the legitimate Googlebot server using fake User-Agent from another Google service to deliver Crypto-currency malware to the target victims...
-

 204
204Hackers Use Hijacked Email Address To Send Malware as a Reply to Existing Email Thread
A new more sophisticated phishing campaign uses hijacked email accounts to deliver malware as a part of the response to the existing...
-
 347
347Beware!! Hackers Now Spreading Dangerous FlawedAmmyy Malware Through PDF & IQY File
Cyber criminals now using IQY Files as a new technique for spreading dangerous FlawedAmmyy malware which is a dangerous backdoor tool that...






