Malware
-

 277
277New ransomware demands users to pay 10 Bitcoin or infect another thousand mining devices
Attackers threaten to collapse users’ mining platforms Network security and ethical hacking specialists from the International Institute of Cyber Security report the...
-

 307
307ATTENTION: Torrents downloaded from The Pirate Bay contain a dangerous malware
Malicious hackers have infected some torrents on this platform with a malware functional in Windows operating systems Although in general this practice...
-

 2.0K
2.0KMac Users Targeted with Ad-Based Image Malware
Most people think that there’s little if any, Mac malware in the civilized world. Unfortunately, that impression is just wishful thinking. Well,...
-

 260
260Anatova: The new ransomware infecting hundreds of devices around the world
This new and sophisticated malicious software is able to bypass the best security measures A new ransomware family discovered at the beginning...
-
 172
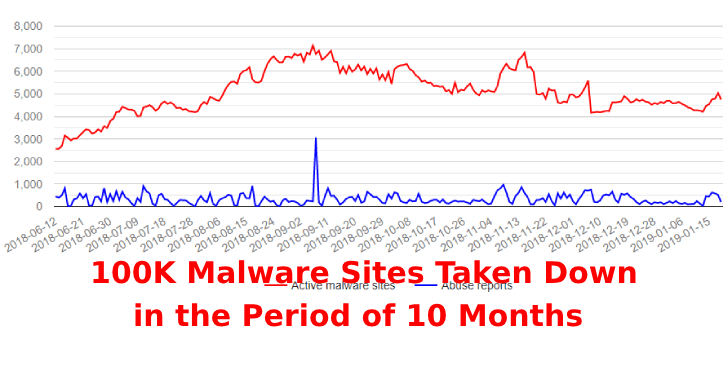
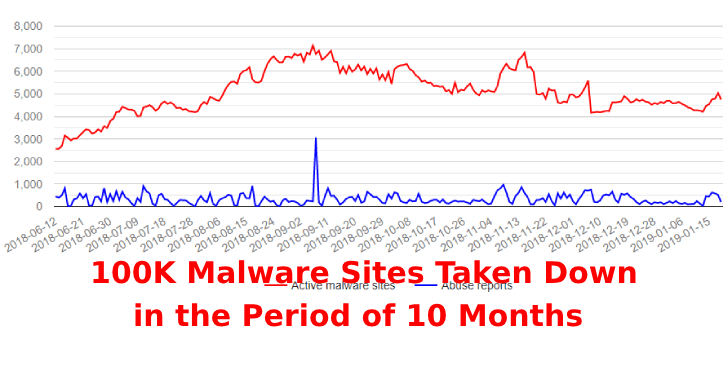
172Security Researchers Globally take down Nearly 100K Malware Sites in the Period of 10 Months
The coordinated efforts were part of the URLhaus initiative that Abuse.ch launched in March 2018, and whose primary objective is to collect...
-

 173
173Phobos, the new ransomware of Dharma Group, infects hundreds of organizations
A new ransomware called Phobos is infecting devices and networks in a massive way A group of hackers is finding remote access...
-
 247
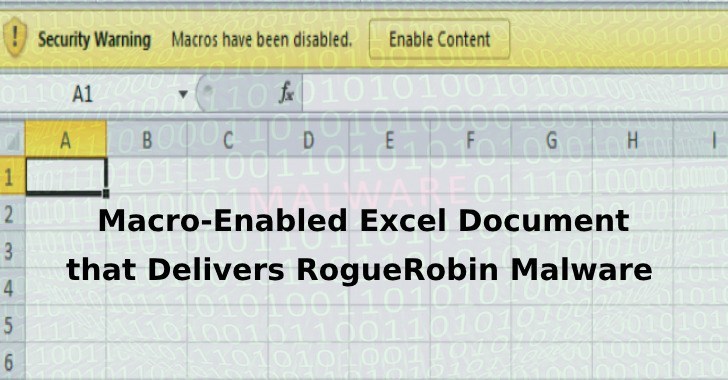
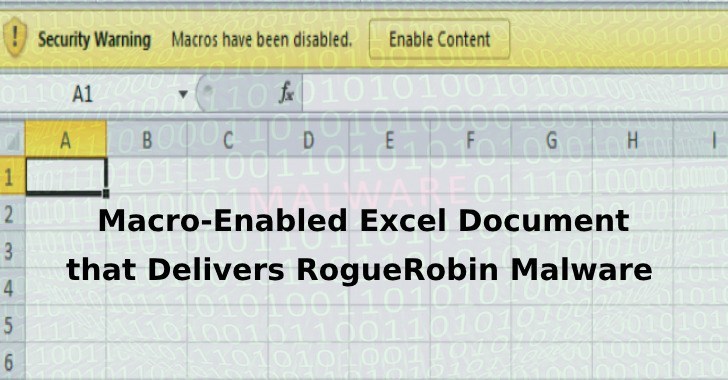
247DarkHydrus Hacking Group Uses Macro-Enabled Excel Document that Delivers RogueRobin Malware
DarkHydruns APT Group targets government entities in the middle eats with weaponized excel documents that delivers a new variant of RogueRobin trojan...
-

 393
393Pirate Bay Downloaders Beware!! – Hackers Launching Dangerous Malware via Torrent Files
Piratebay users are now being victimized by malware and phishing attack that hijacking the websites and steal the cryptocurrencies. A researcher who...
-

 221
221Hackers Launching Ransomware and CryptoMiner via Love_You MalSpam Campaign
The worst alliance of Ransomware and the CryptoMiner family in a spread spree, early January 2019. Malware Spam or MalSpam is the...
-

 270
2702 Android Apps From Google Play Store Launching Banking Malware With Sophisticated Evasion Techniques
Researchers discovered 2 Malicious Android apps from Google Play Store that drops Anubis banking malware with highly obfustication techniques. The malicious apps...
-

 464
464Chrome Extension That Steals Credit Cards Numbers Detected On Web Store
A chrome extension that still available on Chrome Web Store steals the payment card information from website forms visited by the users....
-

 302
302Pre installed malware on Alcatel smartphones makes online transactions
The application made online transactions executed in the background A team of network security experts detected a suspiciously high number of online...
-

 311
311Should insurers pay damages caused by ransomware?
The company argues that its insurance does not cover damage caused “by Acts of war” According to network security and ethical hacking...
-

 2.6K
2.6KAlcatel Smartphone Pre-Installed App Infected with Malware
An official Alcatel app, available through Google Play Store, has been found to be malware infected. It’s in a pre-installed weather app...
-

 2.1K
2.1KResearchers Found Goldluck Malware Infecting iPhone Apps
The Goldluck malware has been around for more than a year. The malware basically gave hackers privileges which allowed them to send...
-
 267
267USB-IF Launches USB Type-C Authentication Program To Protect Against From Malicious Devices
USB-IF announced USB Type-C Authentication Program to confirm the authencity of the USB device USB device, USB cable or USB charger. The...
-

 238
238Cloud service provider’s servers infected with ransomware
The cloud computing services company suffered an attack with malicious software known as Ryuk that crippled its activities During the past Christmas...
-
 193
193Beware of Pre-Installed Mobile Malware in Device System Level Before Shipping
A new landscape study states that an upcoming mobile devices may comes with per-installed mobile malware along with malicious code in it....
-

 164
164Ransomware vs. printing press? US newspapers face “foreign cyberattack”
Did malware disrupt newspaper deliveries in major US cities? Here’s what’s known about the incident so far and the leading suspect: Ryuk...
-

 242
242Shamoon Disk Wiping Malware Destructive attack via an Image of a Burning US Dollar
A disk wiping Shamoon malware performing destructive attack sample using an image of a burning US Dollar. This malware was uploaded in...
-
 144
144Linux servers infected with new ransomware variant
A new type of ransomware has been infecting servers over unsecured IPMI cards Cybersecurity and ethical hacking specialists from the International Institute...






