Malware
-

 325
325Android Gamers Beware of Fake Fortnite Game that Contains Spyware and Cryptocurrency Miner
Android malware posing as Fake Fortnite Game includes spyware, cryptocurrency miner and install unwanted apps that show ads to generate revenue for...
-

 191
1917 Malicious Apps Reappeared on the Play Store Using Google Icons
Seven malicious apps reappeared in Play store with slightly different names under a new publisher account. Those malicious apps are already reported...
-

 276
276Cryptocurrency Miner Discovered on the Ubuntu Snap Store
Researchers found a hidden malware inside the software in the Ubuntu Snap store. The information security experts found that two applications, which...
-
 389
389Dangerous PANDA Banking Malware Spreads Through Phishing Attacks Targets Banks, Cryptocurrency Sites and Social Media
The PANDA Malware first identified in the year 2016 by Fox IT, the malware primarily focused on banking sectors. With the last...
-

 146
146SynAck targeted ransomware uses the Doppelgänging technique
The Process Doppelgänging technique was first presented in December 2017 at the BlackHat conference. Since the presentation several threat actors have started using this...
-
 229
229Root Cause of Powerful Internet Explorer (IE) Zero-day Vulnerability that Allow Attackers to Perform Remote Hacking
New Internet Explorer Zero-day remote code execution vulnerability has been discovered that allows an attacker could execute arbitrary code and take the...
-

 267
267100,000 Users Infected With the Password Stealing Malicious Chrome Extension Distributed Through Facebook
A new malware campaign propagating via crafted socially-engineered links on Facebook abuses the users by installing a malicious chrome extension and performs...
-

 241
241One year later: EternalBlue exploit more popular now than during WannaCryptor outbreak
The infamous outbreak may no longer be causing mayhem worldwide but the threat that enabled it is still very much alive and...
-
 304
304Researchers Found Backdoor in Python Library That Steal SSH Credentials
Recently we saw an attempt to hide a back door in a code library, and today there is a new case. This...
-

 307
307New Cryptocurrency Mining Malware “MassMiner” Attacking Web Servers Using various Powerful Exploits
Newly discovered cryptocurrency mining malware called MasssMiner using various powerful exploits to compromise web servers to mine monero Cryptocurrency around the world....
-

 159
159Backdoor hidden in the npm JavaScript package
According to researchers, the node’s Packet Manager (npm) team just avoided a disaster when it discovered and blocked the distribution of a...
-
 327
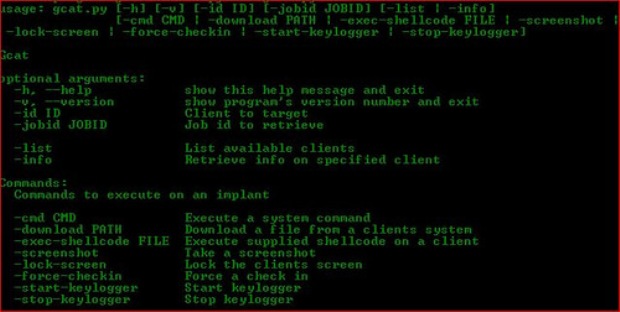
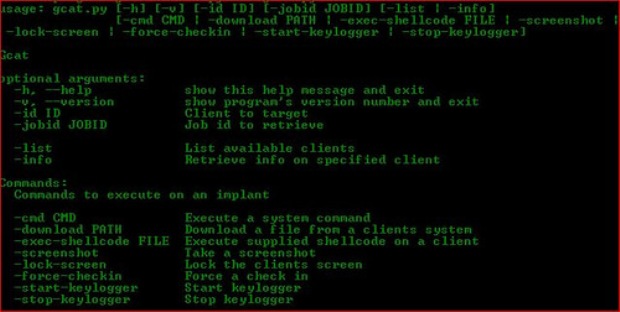
327GravityRAT – A Powerful Remote Access Trojan Conducting an APT Cyber Attack in India, US and UK
A newly uncovered APT Malware called GravityRAT deployed by a hacking group to attack various sectors in India, US, and UK. This...
-

 3.7K
3.7KIs “Malware of Mass Disruption” the WMD of the future? Insights from the stage at RSA 2018
ESET's Global Security Evangelist Tony Anscombe expands on his theory
-
 222
222APT Group Cyber Attack Against Medical Sectors to Hack X-Ray & MRI Scan Machines
New APT Cyber espionage group Orangeworm targeting healthcare sectors and other medical related industries to deploy the powerful Kwampirs backdoor to compromise the...
-

 430
430Sednit update: Analysis of Zebrocy
Zebrocy heavily used by the Sednit group over last two years
-

 128
128Firms using WebEx at risk of poisoned Flash attacks
Companies should check they are running latest version of WebEx, and beware attacks via the road less travelled.
-
 195
195Hacker Selling Powerful SquirtDanger Malware in Underground Market that Take’s Screenshot, Steal Wallets & Browser Passwords
Newly discovered botnet malware called SquirtDanger is widely Distributing, selling, and trading in the global underground market and infect the victims to...
-
 205
205APT Cyber Attack Using Unpatched Internet Explorer Zero-Day to Hack Windows Computers
Cyber Criminals behind the APT attack using an Internet Explorer Zero-Day vulnerability to compromise the windows based computers. An APT hacking group using MS...
-

 171
171Ransomware-as-a-Service platforms available on the dark web
Information security experts at CSE CybSec ZLab malware Lab have conducted an analysis of the principal Ransomware-as-a-Service platforms available on the dark...
-
 279
279Android Spyware & Banking Trojan Attack via DNS Spoofing that Poses as Legitimate Facebook or Chrome App
A new wave of network attacks that uses DNS spoofing and cache poisoning method to distribute XLoader Android Spyware and Banking Trojan. DNS...
-

 143
143XiaoBa Ransomware Retooled as Coinminer But Wreck Your Files
The authors of the XiaoBa ransomware have retooled their malware’s code into a cryptocurrency miner (coinminer). According to information security experts, despite...






