Malware
-
 258
258Iranian Hacker Group Launch APT Attack on Government Organizations To Steal Email Data, Files & Credentials
Newly discovered APT Cyber Espionage Campaign called “Leafminer” from Iranian Hacker Group targeting the wide range of government organizations to steal the...
-

 334
334Beware of Fake Banking Malware Apps in Google Play That Steals Credit Card Details and Internet Banking Credentials
Fake Banking Apps that posing to be from three major Indian banks made way into the official Google Play store. The malicious...
-
 309
309Hackers Distributing FELIXROOT Backdoor Malware using Microsoft Office Vulnerabilities
Newly discovered malware campaign distributing powerful FELIXROOT Backdoor using Microsoft Office Vulnerabilities to compromise the victim’s windows computers. FELIXROOT backdoor campaign initially...
-

 229
229New Variant of Dangerous Kronos Banking Malware Spreading via Malicious Word Documents
A new variant of Kronos Banking Trojan appeared in wild targeting users in Germany, Japan, and Poland. The trojan first appeared in...
-
 152
152New Clipboard Malware Monitors the Windows Clipboard for Cryptocurrency Addresses and Replace its Own Address
New Clipboard Malware variant discovered that abuse the users Copy-Paste habit and check the Cryptocurrency wallet to replaced its own wallet Address...
-
 269
269Android Device With Open ADB Ports Exploited to Spread Satori Variant of Mirai Botnet
A new exploit targeting Android devices with open ADB port 5555 to spread malware through command line troubleshooting utility called Android Debug...
-
 245
245Beware !! Hackers Deliver FlawedAmmyy RAT via Weaponized Microsoft Word and PDF Documents
Cybercriminals spreading powerful FlawedAmmyy RAT via Weaponized Microsoft Word and PDF Attachments to spy victims device and steal the sensitive information Remotely....
-
 359
359US-CERT Alerts Powerful Emotet Banking Malware Attack on Government, Private and Public Sectors
The US-Cert team issued an alert for advanced Emotet banking malware attack that targets governments, private and public sectors in the most...
-
 295
295Dangerous macOS Backdoor That Steals User Login Credentials Remained Undetected for Years
A macOS backdoor dubbed Calisto remained undetected from the radar of antivirus solutions for years. The malware initially uploaded into virustotal back...
-
 170
170Blackgear Cyberespionage Abuses Blogging and Social Media Services To Evade Detection
Blackgear Cyberespionage campaign is active at least from 2008, the threat actors behind the campaign use various malware tools such as the...
-

 267
267Prospective on the evolution of ransomware
This is a reflection exercise on the possible evolution of one of the most common information threats nowadays. Are ransomware threats the...
-
 202
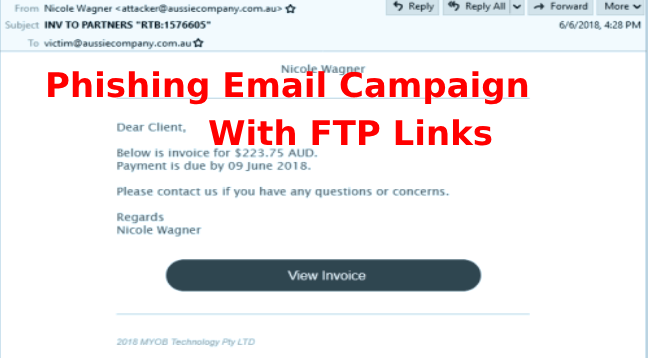
202DanaBot Banking Trojan Steal Private and Sensitive Information
A new phishing email campaign targeting Australian customers with a fake standard MYOB-like HTML invoice template that contains FTP links pointed to...
-
 317
317Russian APT28 Hacking Group Tracked Using a Variant X-Agent Delivering Via JPG File
Security researchers from Z-Lab at CSE Cybsec observed series of malware submitted to the online sandbox and a sample submitted to Virus...
-
 181
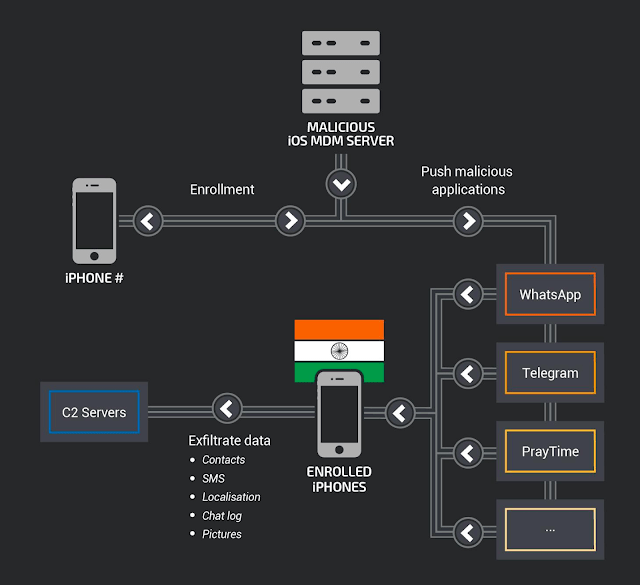
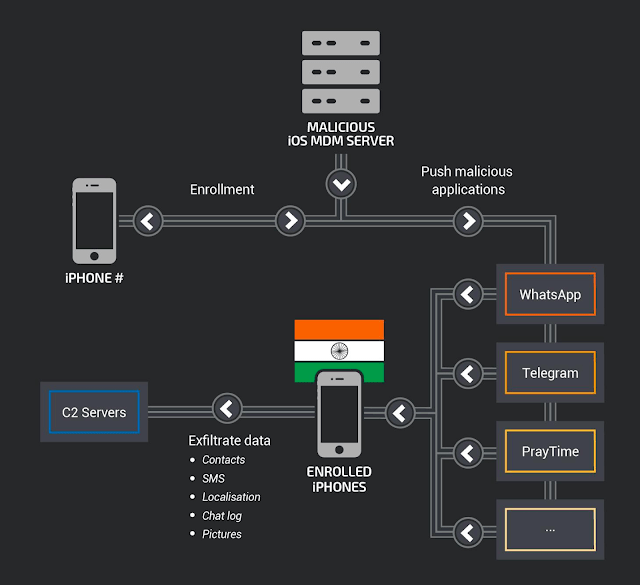
181Advanced Mobile Malware Attack Against iPhones in India using MDM System Control
Advanced mobile malware campaign targeted against 13 iPhone users in India and the attacker using an open-source mobile device management (MDM) system...
-

 372
372Hackers Distributing Anubis Malware via Google Play Store to Steal Login credentials, E-wallets, and Payment Cards Details
Anubis banking malware re-emerges again and the threat actors distributing the malware on Google Play store apps to stealing login credentials to banking...
-

 126
126B&B Hospitality Group restaurants infected with malware
Nine of the consortium establishments have been compromised The malware found at the B&B Hospitality Group (B&BHG) sale points in the New...
-

 253
253Ammyy Admin compromised with malware again; World Cup used as cover
Website altered to serve a malware-tainted version of otherwise legitimate software with the global event in Russia acting as a smokescreen
-

 172
172Sophisticated Spyware Attack on Military Mobile Devices to Record Phone Calls & Take a Picture
A few days before the Israeli security firm reported that Hamas cyber attackers installed a sophisticated spyware in Israeli soldiers Military Mobile Devices...
-
 226
226Hackers Signed Malware With Stolen Code Signing Certificate From Tech- Companies
A code signing certificate allows an application developer to sign their software before publishing to the web and the end-users can verify...
-

 447
447Certificates stolen from Taiwanese tech‑companies misused in Plead malware campaign
D-Link and Changing Information Technologies code-signing certificates stolen and abused by highly skilled cyberespionage group focused on East Asia, particularly Taiwan
-

 247
247Old Malware Gives Criminals Tricky New Choice: Ransomware or Mining
The Rakhni Trojan is now giving bad actors the ability to infect victims either with a ransomware cryptor or a miner. An...






