Malware
-
 237
237SambaCry Vulnerability used in Deploying Payloads Targeting IoT devices Particularly NAS
Attackers using the SambaCry vulnerability to target older versions of Samba(3.5.0) to upload and execute the malicious payload. SambaCry Vulnerability(CVE-2017-7494) have the...
-
 217
217Record Audio and Video Silently with Obfuscated Android Backdoor – GhostCtrl
New Android malware variant GhostCtrl steals data, control devices functionalities and even hijack the devices. It is certainly a variant of commercially...
-
 205
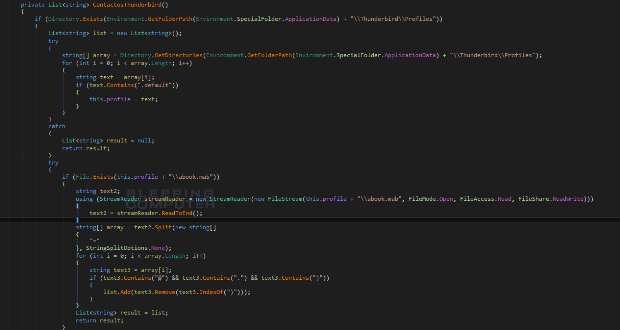
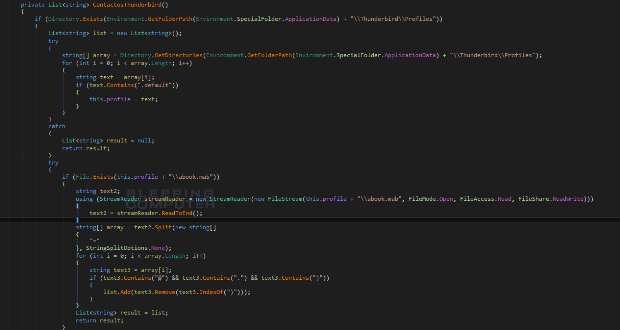
205Reyptson Ransomware Spams Your Friends by Stealing Thunderbird Contacts
Over the weekend, Emsisoft security researcher xXToffeeXx discovered a new ransomware called Reyptson that is targeting Spanish victims. Since then, we have seen increased activity in...
-

 93
93GhostCtrl Is an Android RAT That Also Doubles as Ransomware
A new Android RAT (Remote Access Trojan) detected under the name of GhostCtrl can lock mobile device by resetting their PIN and...
-
 193
193New OSX/Dok Malware Targeting macOS Users to Steal Banking Credentials by Cloning Major Bank Websites
A New MacOS Malware “OSX/Dok” Discovered to Steal Banking Credentials by cloning major Banking website which leads victims to install the Malicious...
-
 169
169New Exte CryptoMix Ransomware Variant Released
Yesterday, Malwarebytes malware researcher Marcelo Rivero discovered a new variant of the CryptoMix ransomware that is appending the .EXTE extension to encrypted file names. This article...
-

 168
168Keeping up with the Petyas: Demystifying the malware family
The origin of Petya The first Petya ransomware was released around March 2016 by a person/group calling themselves Janus Cybercrime Solutions. This...
-
 267
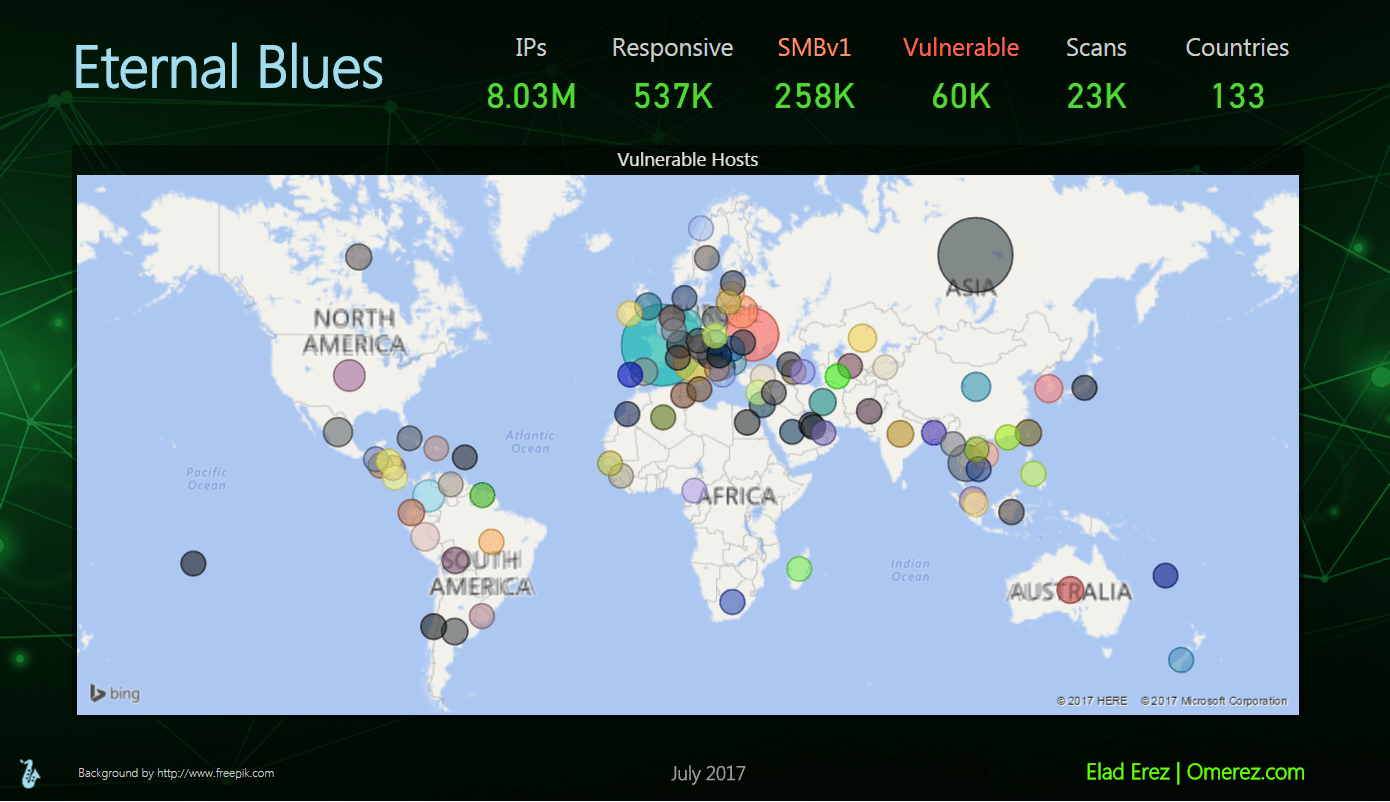
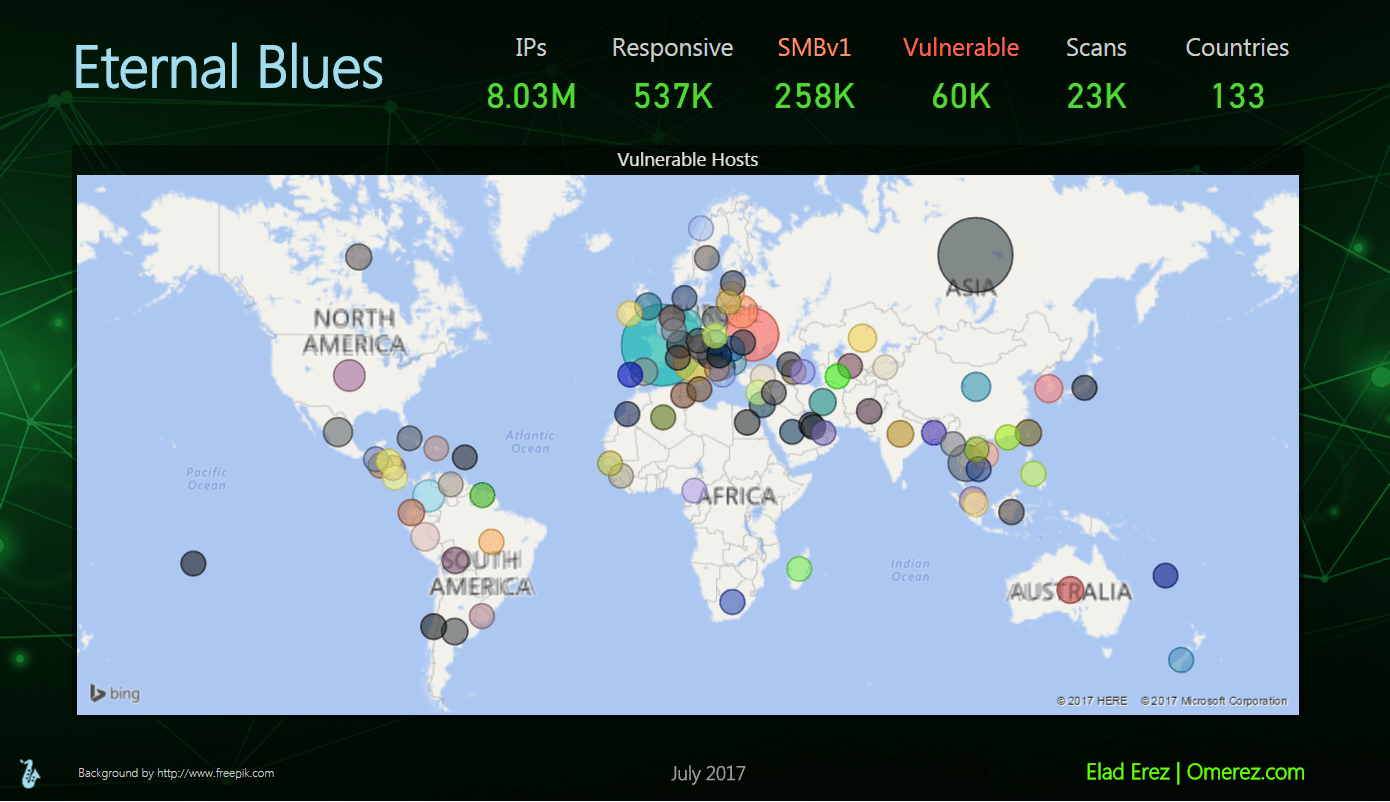
267Still More than 50,000 hosts are vulnerable to ETERNAL BLUE Exploit
Eternal Blues, a tool used in finding computers and Endpoints vulnerable to the NSA’s ETERNALBLUE exploit. All we need to do is...
-
 159
159New PoS Malware LockPoS emerges in the threat landscape
A newly discovered Point of Sale (PoS) malware dubbed LockPoS appeared in the wild and it is being delivered through the Flokibot botnet....
-
 316
316Vault 7 Leaks : CIA Android Hacking Tool “HighRise” Steals Data From Compromised Android Phones via SMS – WikiLeaks
WikiLeaks Revealed a CIA Secret Document of Android Mobile Hacking Tool called “HighRise” steal the victims Android smartphones data and send to...
-

 161
161Samba puts out new security update to address exploit that fueled WannaCry
Vuln hit “all versions of Samba from 4.0.0 onward using embedded Heimdal Kerberos.” On Wednesday, the Samba Team released new security updates to fix a vulnerability in...
-

 105
105Magala Trojan Uses Virtual Desktops to Secretly Click on Search Results Ads
A new click-fraud trojan is infecting Windows computers and using virtual desktops to click on ads in search results to earn a...
-

 100
100Adwind RAT is back, crooks are targeting Aerospace industries in many countries
Security experts at TrendMicro discovered that the notorious Adwind RAT has resurfaced targeting enterprises in the Aerospace industries worldwide. Crooks are even more opportunists,...
-

 240
240Calling Artificial Intelligence to Counter Ransomware Attacks
The progression in Artificial Intelligence have incited intense debate worldwide, some experts are calling AI to counter malware attacks In a short...
-
 179
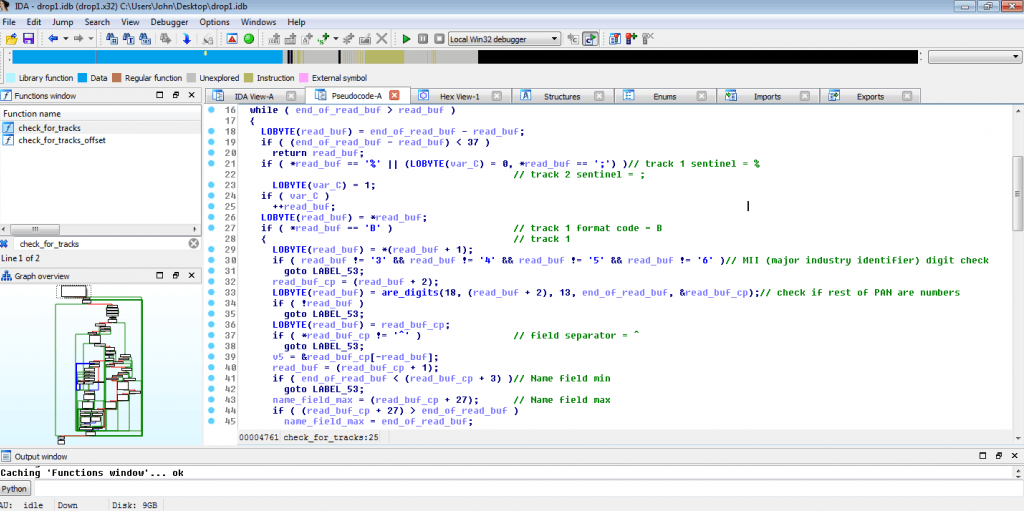
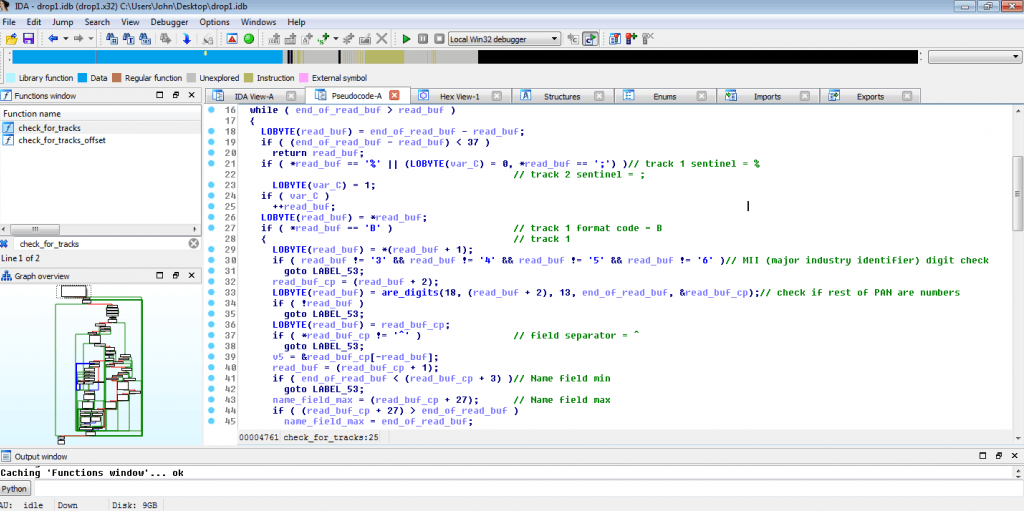
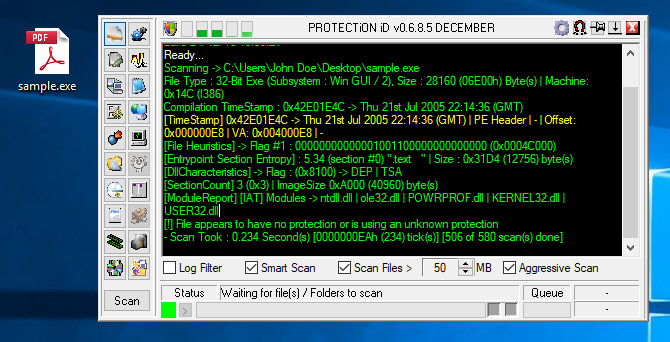
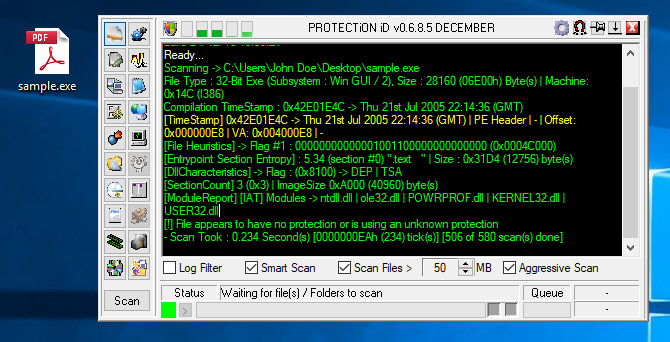
179Upatre – Trojan Downloader
You can get the sample from theZoo SHA-256: 1b893ca3b782679b1e5d1afecb75be7bcc145b5da21a30f6c18dbddc9c6de4e7 We can use behavior analysis from hybrid-analysis. Seems like there is no known protection mechanism. In...
-

 286
286Android Trojan Called “SpyDealer” Spying on More Than 40 Apps Including Facebook, WhatsApp, Skype,Telegram
A Newly Discovered Android Malware “SpyDealer” Spying on more than 40 Apps and steals Personal information including contacts list, Call History, capture...
-

 217
217DECRYPTION KEY TO ORIGINAL PETYA RANSOMWARE RELEASED
The master key to the original version of the Petya ransomware – not to be confused with the latest and massive Petya/ExPetr...
-

 89
89SLocker Mobile Ransomware Starts Mimicking WannaCry
a new variant of mobile ransomware SLocker (detected by Trend Micro as ANDROIDOS_SLOCKER.OPST) was detected, copying the GUI of the now-infamous WannaCry....
-

 162
162Highly Advanced SpyDealer Malware Can Root One in Four Android Devices
Security experts have discovered a brand new Android trojan that features a broad range of features that allow it to root Android...
-
 156
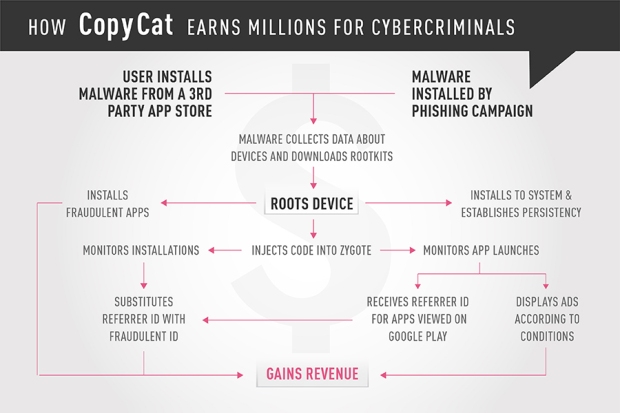
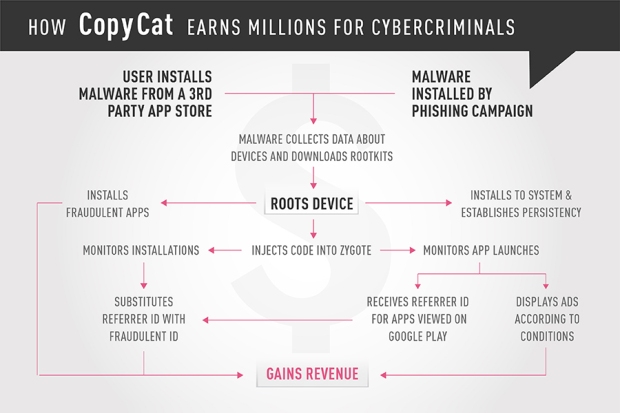
156How the CopyCat malware infected Android devices around the world
Check Point researchers identified a mobile malware that infected 14 million Android devices, rooting approximately 8 million of them, and earning the...
-
 310
310Vault 7 Leaks : CIA Hacking Tools “BothanSpy” and “Gyrfalcon” Steals SSH Credentials From Windows and Linux Computers – WikiLeaks
WikiLeaks Revealed Another CIA Cyber Weapons called “BothanSpy” and “Gyrfalcon” steals the SSH Credentials from both Windows and Linux Platform and both...






