Malware
-

 277
277Industroyer: Biggest threat to industrial control systems since Stuxnet
ESET has analyzed a sophisticated and extremely dangerous malware, known as Industroyer, which is designed to disrupt critical industrial processes.
-

 288
288Dvmap – First Ever Android Rooting Malware with Code Injection Capabilities
Trojan Dvmap distributed through the Google Play Store, uses various exceptionally dangerous methods, including patching system libraries. It installs malicious modules with...
-

 252
252Malicious Android ads leads to Automatically Download and Install Apps that Contain Malware in Android Devices
Malicious Android Apps are growing rapidly and it used to target victims in Many ways. Spreading Malware through malvertising campaign in Popular...
-
 367
367NSA Malware “EternalBlue” Successfully Exploit and Port into Microsoft Windows 10
A Malware called “EternalBlue” Vulnerability Successfully port the exploit to Microsoft Windows 10 by the Security Researchers which has been only affected...
-

 86
86Botnets overshadowed by ransomware (in media)
Regardless of how prominent and effective ransomware appears to be, it is not the most dangerous form of malware.
-

 360
360A Banking Trojan Called “QakBot ” Attack Thousands of Windows Active Directory and users to get locksout of their Company’s Domain
An Existing Banking Trojan called “QakBot ” attack Windows Active Directory users and leads to locks out the thousands of Active Directory...
-
 183
183Beware: Chinese Malware Fireball Infects More than 250 Million Computers around the Globe
Chinese threat operation which has infected more than 250 million PCs around the world. The advanced malware, Fireball, takes control target browsers...
-
 337
337New CIA Cyberweapon Malware “Pandemic” installed in Victims Machine and Replaced Target files where remote users use SMB to Download
One of the CIA Cyberweapon Called “Pandemic” Document Leaked by Vault 7 Projects of WikiLeaks.This Malware tool Specifically interact and run as...
-
 202
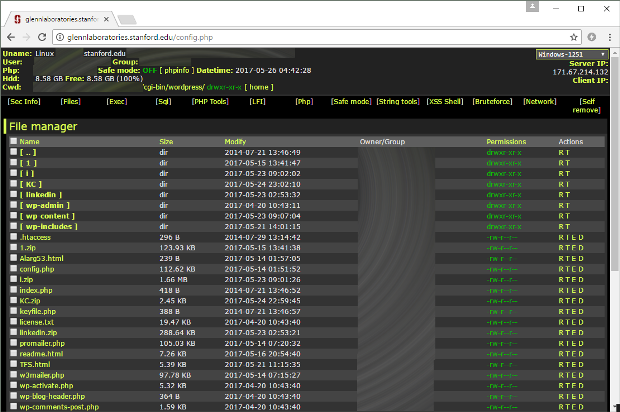
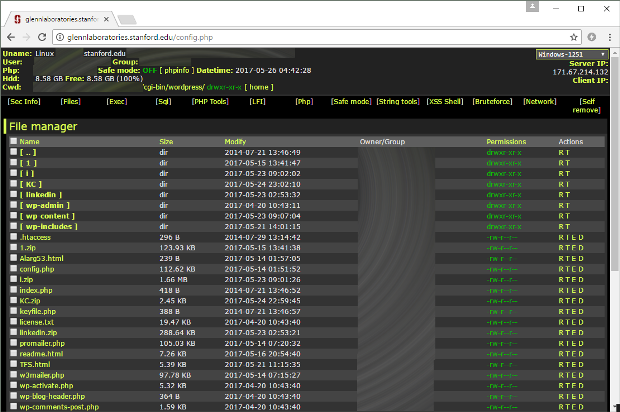
202Stanford University Site Hosted Malware for Months
For almost four months, script kiddies ran amok in one of Stanford’s subdomains, installing web shells, mailers, and other types of web...
-

 75
75Man Linked to Auto Parts Store Behind Bachosens Malware
A man linked to an auto parts store in a disputed territory of Moldova is behind the Bachosens malware, a backdoor trojan...
-

 201
201XData Ransomware Master Decryption Keys Released. Kaspersky Releases Decryptor.
In what has become a welcome trend, today another ransomware master decryption key was released on BleepingComputer.com. This time the key that...
-

 268
268Beware: Malicious Payload “Hworm” Dropped Through Embedded Youtube Video’s
A Malware called Hworm Performing multiple Attacks including steal passwords from Firefox, Opera, and Chrome browsers, ability to log keystrokes, kill running...
-

 163
163Chipotle Mexican Grill Fast-food chain notified customers a PoS malware breach
The Fast-food chain Chipotle notified users a security breach, hackers compromised its point of sale terminals to steal payment card data. The...
-

 159
159Google Boots 41 Apps Infected with “Judy” Malware off the Play Store
Google has removed 41 Android apps from the official Play Store. The apps were infected with a new type of malware named...
-

 340
340Beware: New Google Play Store Android Malware called “Judy” Infected Around 8.5 to 36.5 Million Users
A New Android Malware Called “Judy” found in google play store infected 41 Apps which all are created by a Korean company....
-

 252
252Android Users Tricked Into Installing Malware Via “App-For-Money” Scheme
An eight-month-long investigation by Roman Unuchek, a security researcher at Kaspersky Lab, has uncovered one of the most complex malware distribution...
-

 72
7264-bit malware threat may be itty-bitty now, but it’s only set to grow
The volume of 64-bit malware in the wild remains low even though computers running 64-bit operating systems became ubiquitous years ago. The...
-
 62
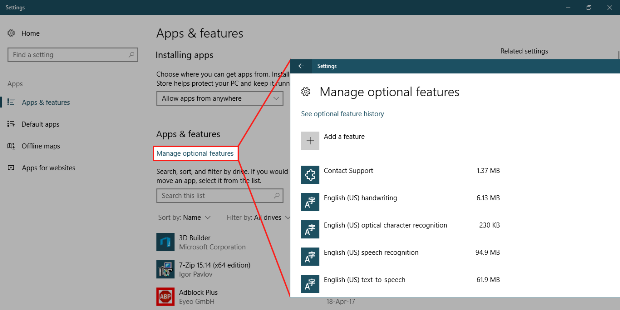
62Windows 10 UAC Bypass Uses “Apps & Features” Utility
Malware authors have a new UAC bypass technique at their disposal that they can use to install malicious apps on devices running...
-

 153
153Russian Police Apprehend “Cron” Gang Behind Tiny.z and PonyForx Malware
Russian authorities have arrested the Cron malware gang, responsible for selling the Tiny.z Android banking trojan and the PonyForx Windows infostealer. The...
-
 202
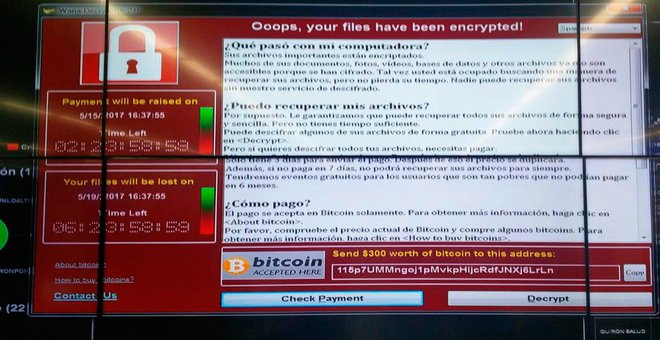
202North Korea Denies Involvement in WannaCry Ransomware Outbreak
On Friday, North Korea denied allegations that it was somehow responsible for the WannaCry ransomware outbreak that affected over 240,000 computers in...
-

 340
340New SMB Network Worm “MicroBotMassiveNet” Using 7 NSA Hacking Tools , Wannacry using only Two
[jpshare]A New Network Worm called “MicroBotMassiveNet” (Nick Name:EternalRocks) Discovered Recently which is also Performing in SMB Exploit as Wannacry .“MicroBotMassiveNet” self Replicate with...






