Malware
-

 96
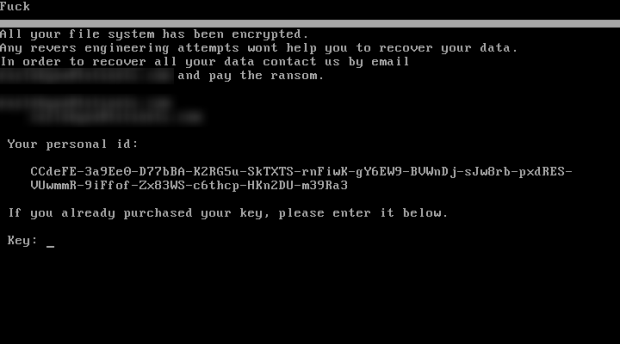
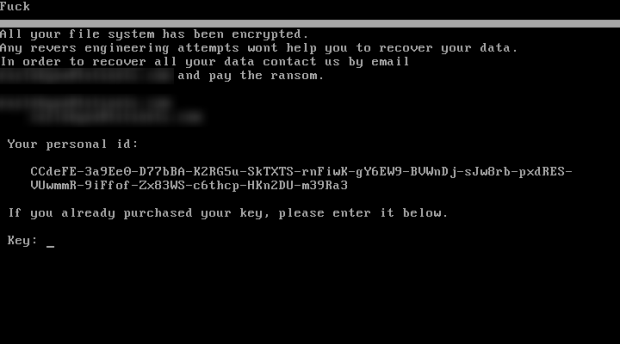
96PyCL Ransomware Delivered via RIG EK in Distribution Test
This past Saturday security researchers Kafeine, MalwareHunterteam, BroadAnalysis, and David Martínez discovered a new ransomware being distributed through EITest into the RIG exploit kit. As this ransomware was...
-
 215
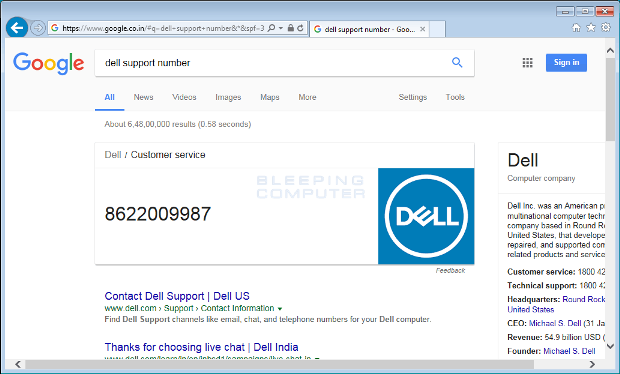
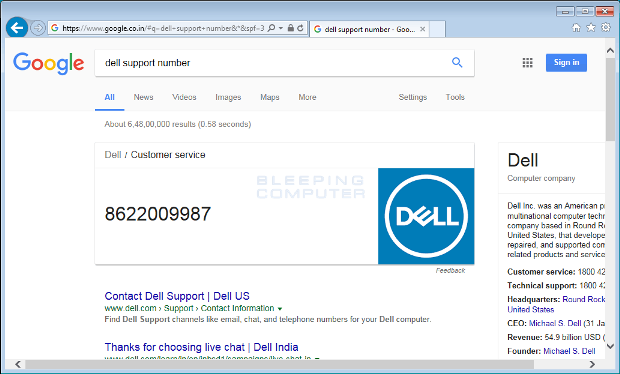
215Adware Replaces Phone Numbers for Security Firms Returned in Search Results
A new adware family named Crusader will rewrite tech support phone numbers returned in Google search results, display ads, and show popups...
-
 292
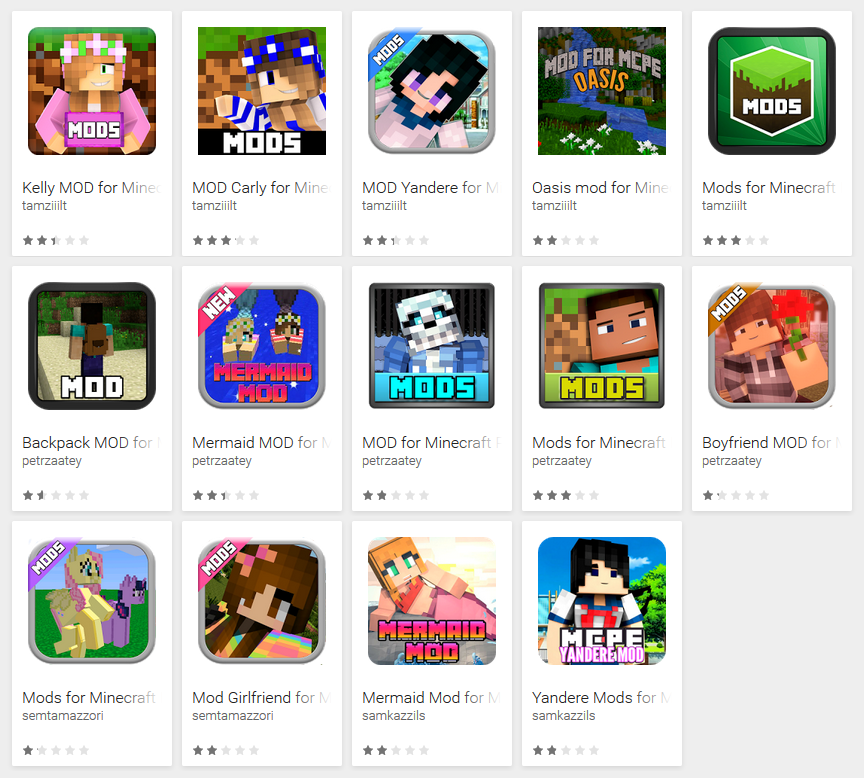
29287 fake Minecraft mods reached up to 990,000 Android users spotted on Google Play Store
Malicious Apps hosted in Google play store is a never ending process, researchers from Zsclarer and ESET reported dozens of the app...
-
 198
198Spear phishing campaign targeted Saudi Arabia Government organizations
Security researchers at MalwareBytes have uncovered a spearphishing campaign that targeted Saudi Arabia Government organizations. Security experts at MalwareBytes have spotted a...
-

 141
14116 years of Mac OS X: Secure but not invincible to malware
Mac OS X is still secure 16 years after its creation, but increasingly being targeted by cybercriminals. No operating system is 100%...
-

 164
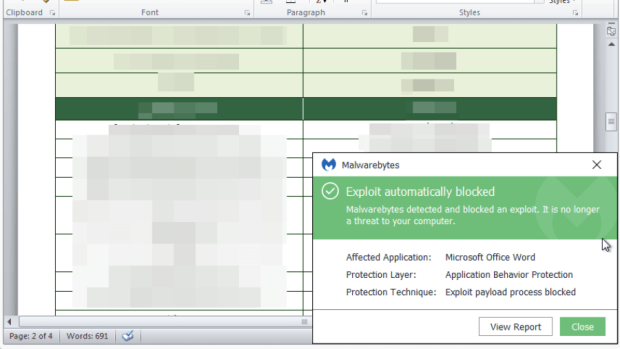
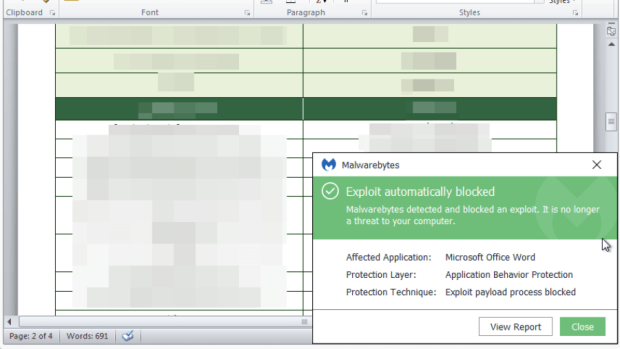
164Word Document Spreads Macro Malware Targeting Both Windows and macOS
After last month security researchers discovered the first-ever Word document spreading macro malware on macOS, last week, researchers from Fortinet spotted a...
-
 154
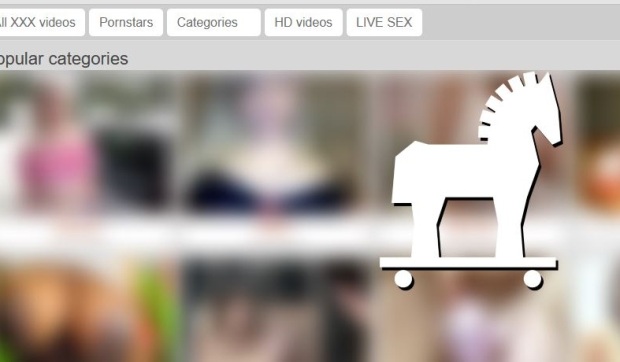
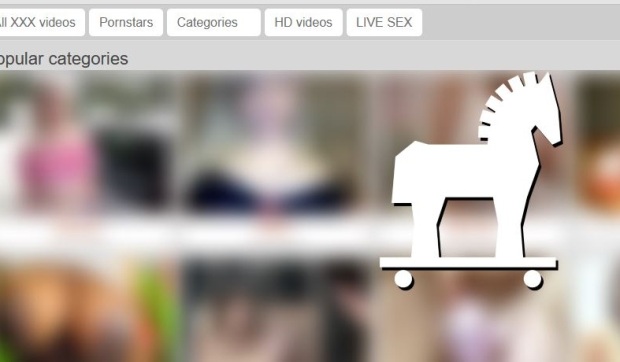
154Malvertising Campaign on Adult Sites Spreads Ramnit Trojan
Security researchers from Malwarebytes have discovered a new malvertising campaign targeting visitors of several adult websites, spreading the Ramnit trojan and focusing...
-

 96
96Most Industrial Control Systems Get Infected with Malware by Accident
The vast majority of malware incidents that take place at industrial facilities around the world are just accidental infections, albeit a very...
-

 142
142Chinese Crooks Use Fake Cellular Telephony Towers to Spread Android Malware
Malware authors in China are using fake base transceiver stations (BTSs), which is equipment usually installed on cellular telephone towers, to send...
-
 191
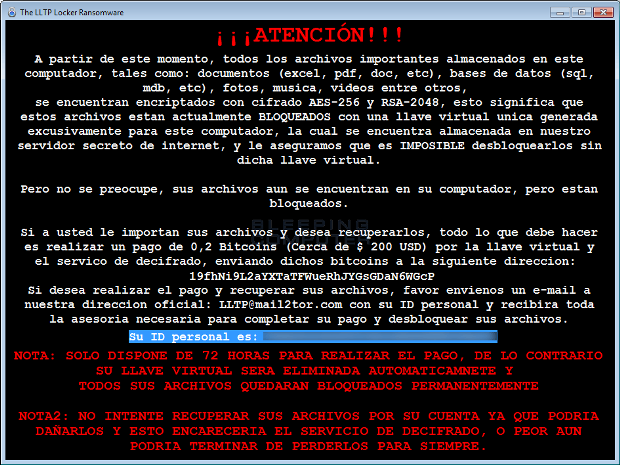
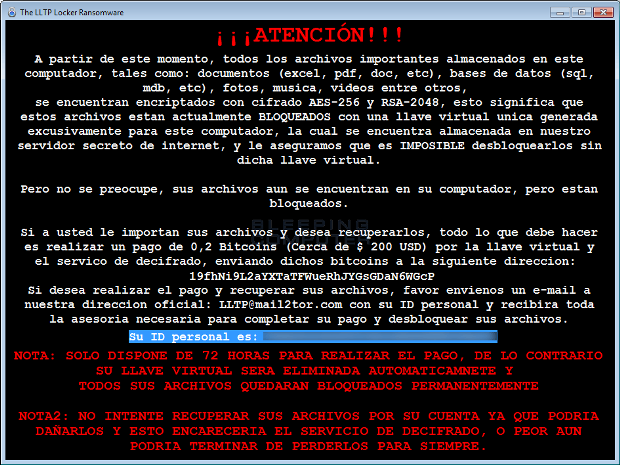
191New LLTP Ransomware Appears to be a Rewritten Venus Locker
A new ransomware was discovered today by MalwareHunterTeam called LLTP Ransomware or LLTP Locker that is targeting Spanish speaking victims. On a closer look, this...
-
 80
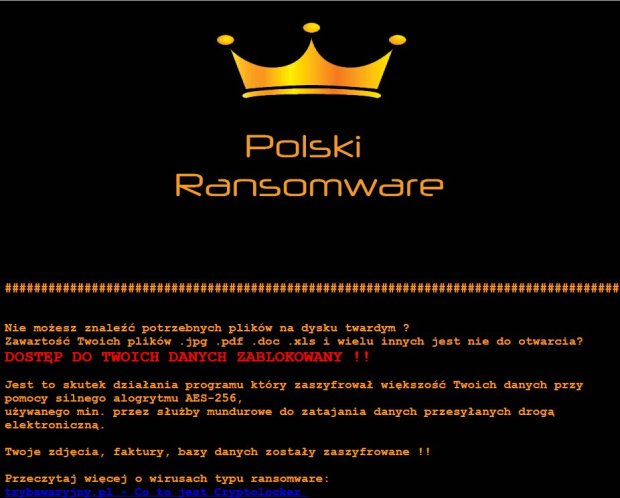
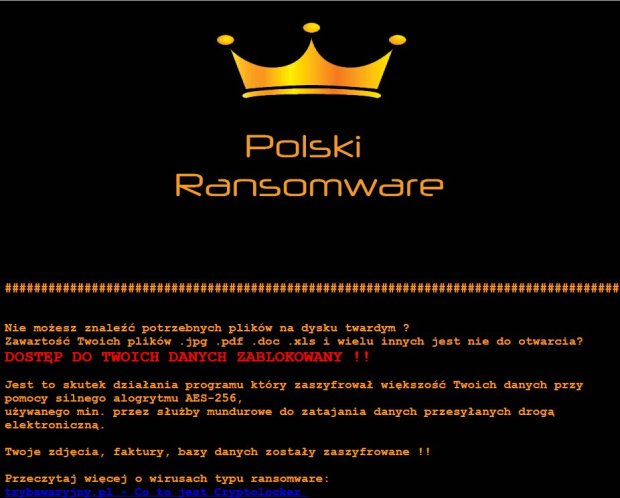
80The Polski-Vortex-Flotera Ransomware Connection
A malware author that loves Polish hip hop music appears to be behind the Polski, Vortex, and Flotera (spelled Ŧl๏tєгค) ransomware families...
-
 201
201Chinese PUPs distributing Backdoored Drivers which affect Windows operating system
PUP(potentially unwanted program) packages that install’s along with Chinese software’s consist of backdoors targeting English speakers. The backdoor was uncovered by Malware...
-

 92
92Big Surprise: Chinese PUPs Deliver Backdoored Drivers
A driver secretly installed via PUPs packages for Chinese software contain backdoors enabling a third-party to load unsigned drivers or to execute...
-

 80
80Flashback Friday: Operation Windigo
In 2014, ESET delivered a comprehensive and detailed report on Operation Windigo. We take a look back at what was documented and...
-

 129
129Ransomware operators are hiding malware deeper in installer packages
We are seeing a wave of new NSIS installers used in ransomware campaigns. These new installers pack significant updates, indicating a collective...
-

 276
276MajikPOS Dual malware targeting businesses across North America and Canada
A new group of POS malware family made its presence targeting business systems around North America and Canada.The objective of PoS malware...
-
 192
192New MajikPOS Malware targets users in across North America and Canada
Trend Micro has discovered a new PoS malware, tracked as MajikPOS, that is targeting business in North America and Canada. Security experts...
-

 186
186Revenge Ransomware, a CryptoMix Variant, Being Distributed by RIG Exploit Kit
A new CryptoMix, or CryptFile2, variant called Revenge has been discovered by Broad Analysis that is being distributed via the RIG exploit kit. This...
-
 73
73PetrWrap: the new Petya-based ransomware used in targeted attacks
Previously unknown ransomware technique. This year we found a new family of ransomware used in targeted attacks against organizations. After penetrating an...
-
 259
259“Super Malware” Steals Encryption Keys From Intel SGX Isolated Memory Fields
A scientist’s Team from Graz University of Technology revealed the method that leaking the encryption data from Intel SGX (Software Guard Extensions...
-

 254
254Hancitor Makes First Appearance in Top Five Most wanted malware – February 2017
Hancitor has grown into the main five of the ‘most wanted’ malware families worldwide for the first time, reported by Checkpoint Threat Intelligence...






