Malware
-

 147
147Toy Maker Maisto Unwittingly Serves Up CryptXXX Ransomware
The website of popular American brand Maisto, known for miniature and radio-controlled toy vehicles, was caught pushing the Angler exploit kit eventually leading to ransomware...
-
 177
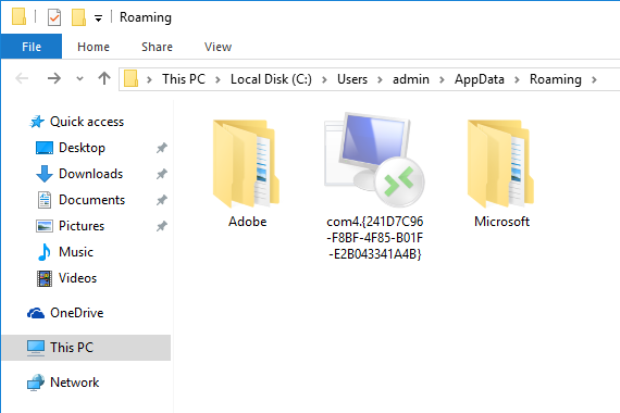
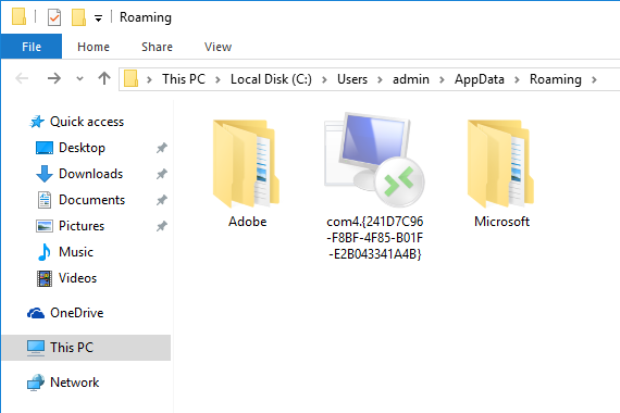
177Malware Takes Advantage of Windows ‘God Mode’
Microsoft Windows has hidden an Easter Egg since Windows Vista. It allows users to create a specially named folder that acts as...
-
 186
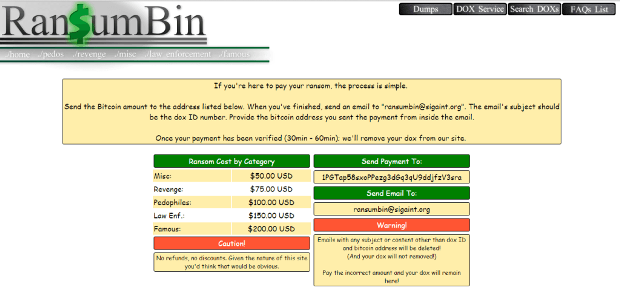
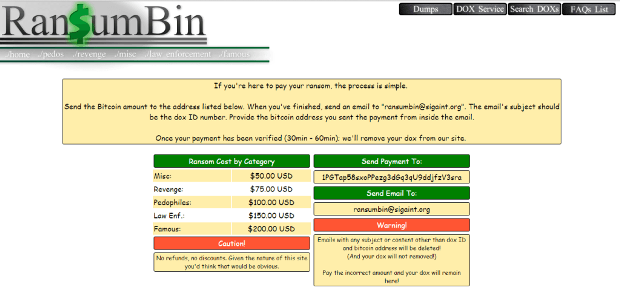
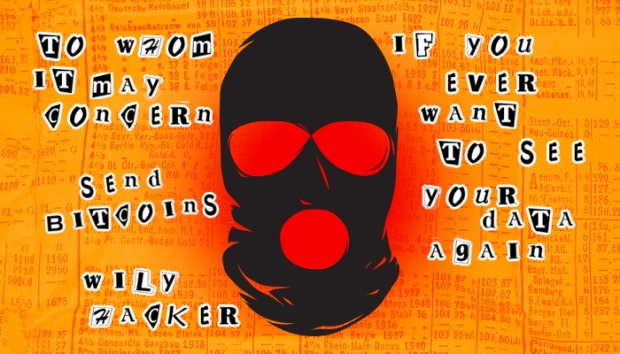
186Ran$umBin a dark web service dedicated to ransomware
A group cyber criminals created Ran$umBin, A Dark web service which operates the one-stop shop for monetizing ransomware. These days Ransomware are...
-
 298
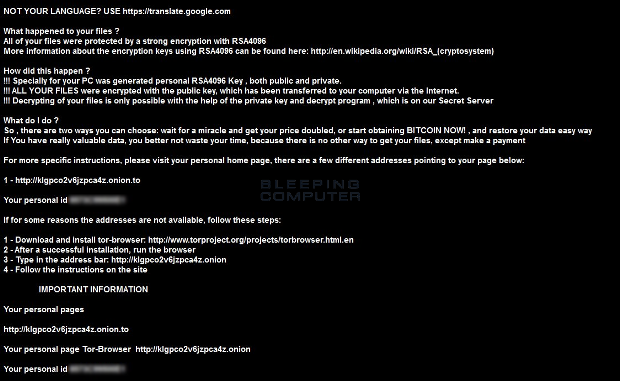
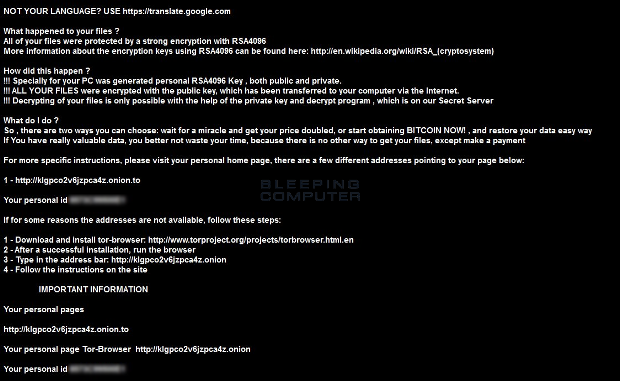
298Decrypted: Kaspersky releases free decryptor for CryptXXX Ransomware
Last week Kafeine posted an analysis of a new ransomware called CryptXXX on the Proofpoint blog. Based on their analysis they determined that...
-
 163
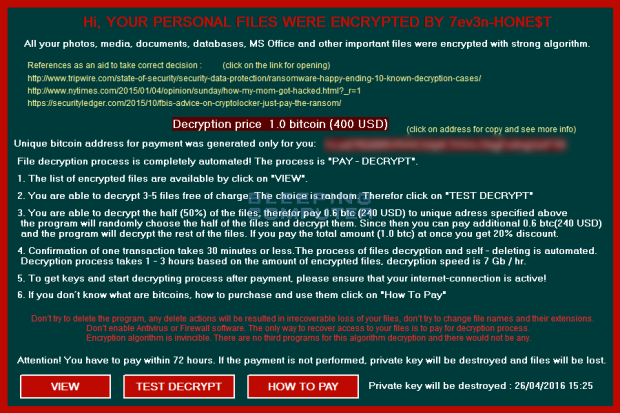
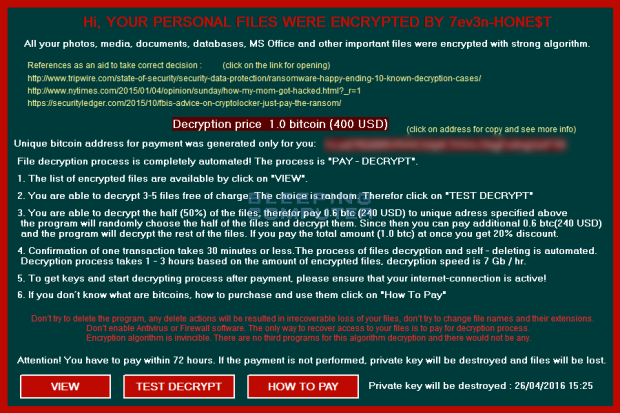
163The 7ev3n-HONE$T ransomware encrypts and renames your files to R5A
A security researcher named Mosh has discovered a new variant of the 7ev3n Ransomware, which has rebranded itself as 7ev3n-HONE$T. This ransomware will encrypt your...
-
 98
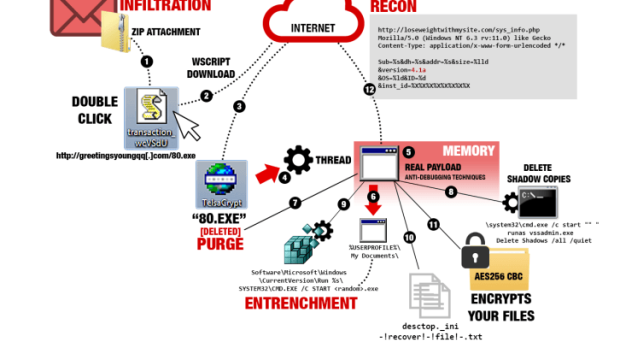
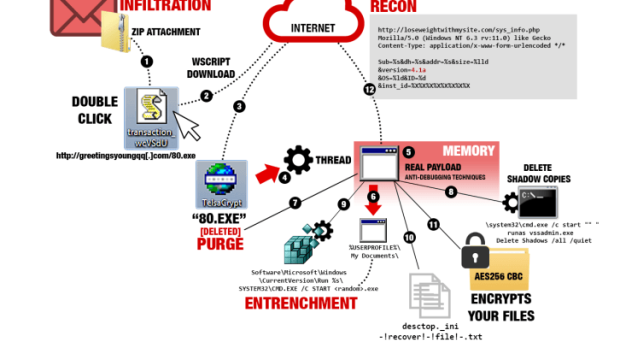
98A new strain of Teslacrypt implements sophisticated evasion
The authors of the TeslaCrypt ransomware have improved it by implementing new sophisticated evasion techniques and targeting new file types. The authors...
-

 202
202Fake Social Button Plugin Redirects to Angler EK
Compromised websites remain one of the surefire ways to redirect innocent visitors to exploit kits. During the past few days we’ve started seeing...
-
 99
99Dorkbot: 5 years since detection
In the half-decade that has lapsed since Dorkbot was first identified, millions of innocent victims, going about their everyday business, have been...
-
 117
117Google.com is dangerous website warns Google safe browsing
Google warns that surfing on Google.com is dangerous, here is why!. The world’s top website is partially dangerous for Internet users. We are...
-
 101
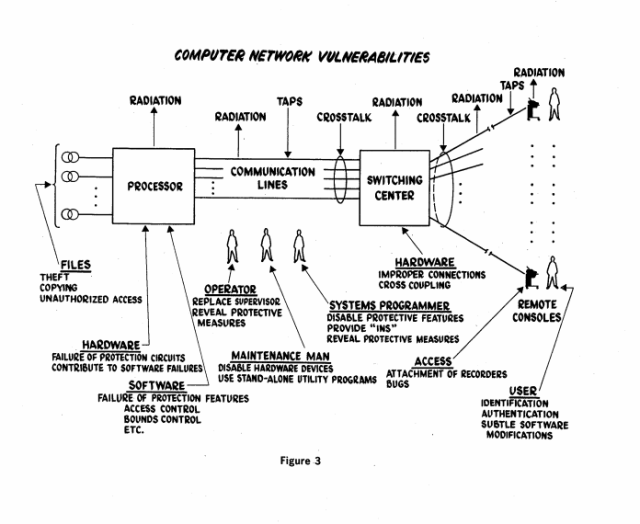
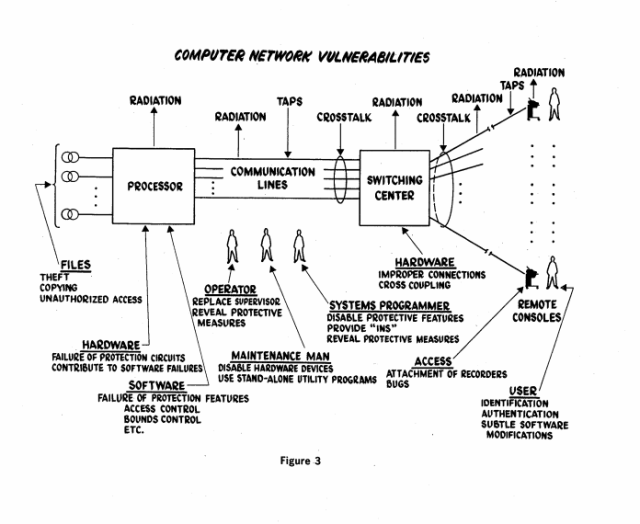
101Flashback: Declassified 1970 DOD cybersecurity document still relevant
The Ware Report’s recommendations still important as proven by ransomware and breaches. The National Security Archives at George Washington University has just added...
-
 148
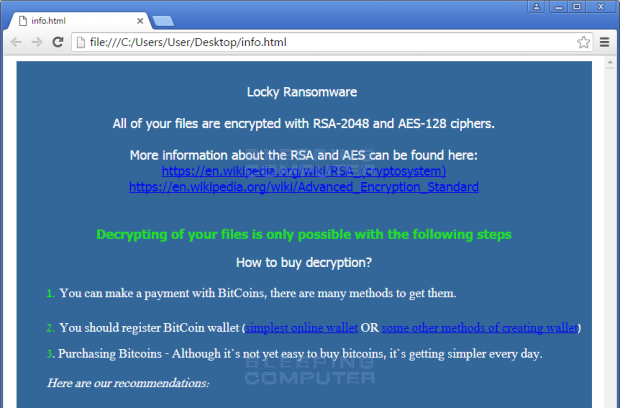
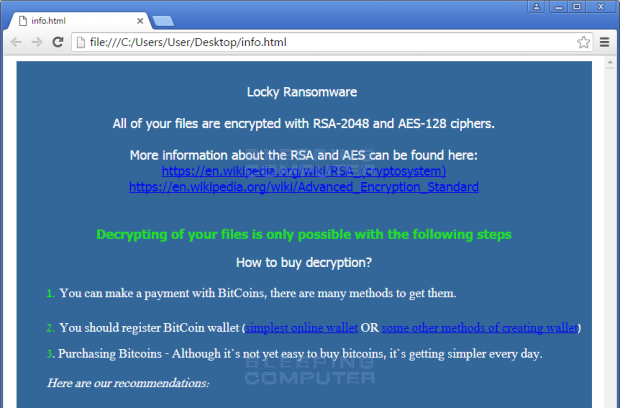
148Decrypted: The new AutoLocky Ransomware fails to impersonate Locky
A new ransomware was discovered that tries to impersonate the well known Locky ransomware. It calls itself Locky and even adds .Locky to...
-

 82
82Malware found in surveillance cameras sold through Amazon
Security researcher finds malicious code embedded within cameras offered for sale on Amazon. Last week, independent security researcher Mike Olsen discovered that CCTV...
-
 147
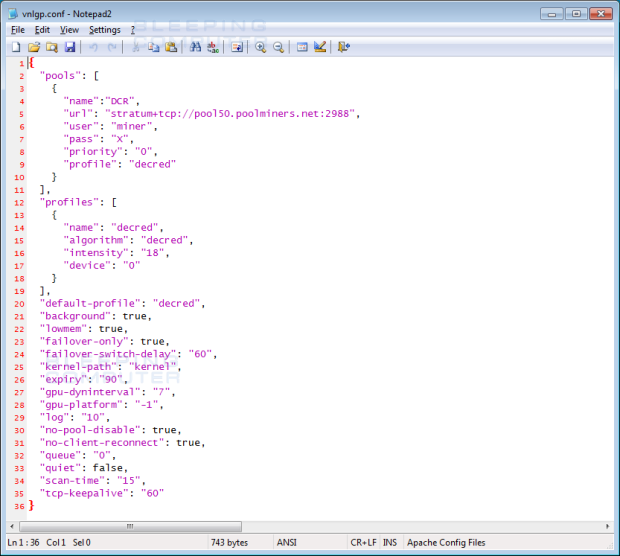
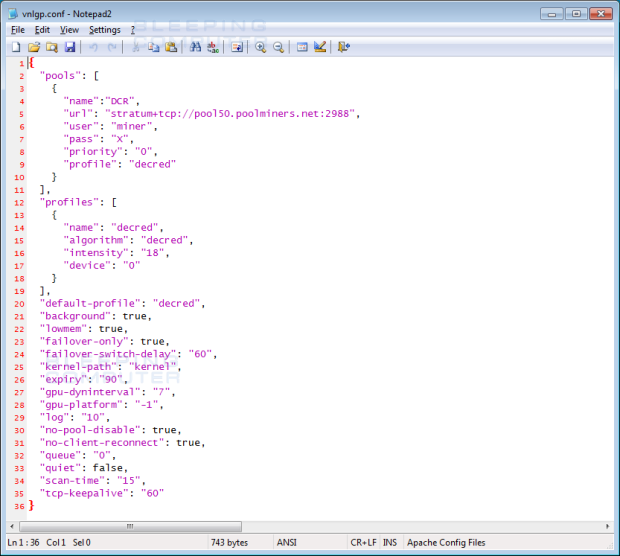
147Adware Bundlers pushing CryptoCurrency Miners on Unsuspecting Victims
Adware installers are out of control and with little or no law regulating them, the crap they push onto their victims is...
-

 152
152Rokku Ransomware shows possible link with Chimera
Rokku is yet another ransomware, discovered in recent weeks. Currently, it’s most common distribution method is spam where a malicious executable is dropped...
-
 103
103Be careful products sold on Amazon are infected with malware
Beware, even things on Amazon come with embedded malware… this is the disconcerting discovery made by the expert Mark Olsen. The security expert Mike...
-
 98
98OK, panic—newly evolved ransomware is bad news for everyone
Crypto-ransomware has turned every network intrusion into a potential payday. There’s something inherently world-changing about the latest round of crypto-ransomware that has been...
-

 185
185DDoS Attacks With BillGates Linux Malware Intensify
XOR botnet authors migrate to using BillGates malware. Over the past six months, security researchers from Akamai’s SIRT team have observed a shift...
-
 99
99TA530 group, spear phishing meets ransomware
A threat actor named TA530 group, has been targeting executives in an attempt to infect their machine with various malware, including ransomware....
-

 186
186LOCKY VARIANT CHANGES C2 COMMUNICATION, FOUND IN NUCLEAR EK
Security experts warn companies need to brace for new harder-to-detect and more determined variants of the Locky ransomware spotted recently in the...
-
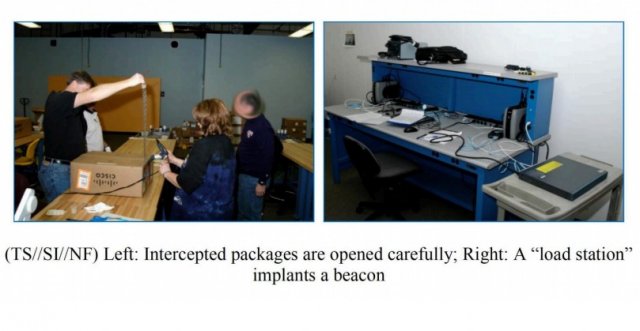
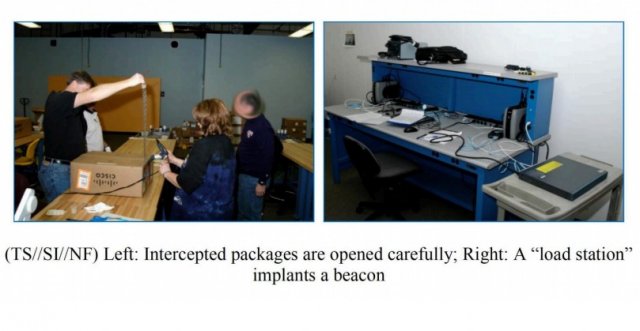 158
158Photos Show How NSA Implants Trojan In Routers For Hidden Access And Spying
ShortBytes: In a recent find out, it has been revealed how NSA implants trojan firmware in the networking devices being delivered to...
-
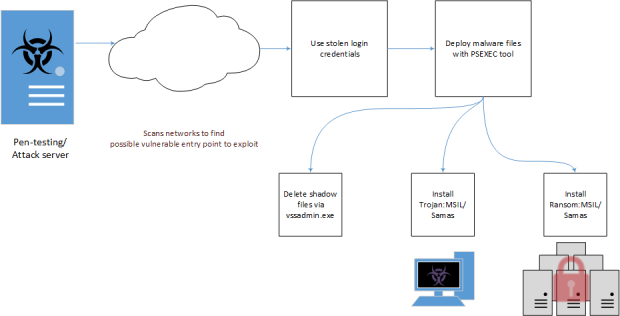
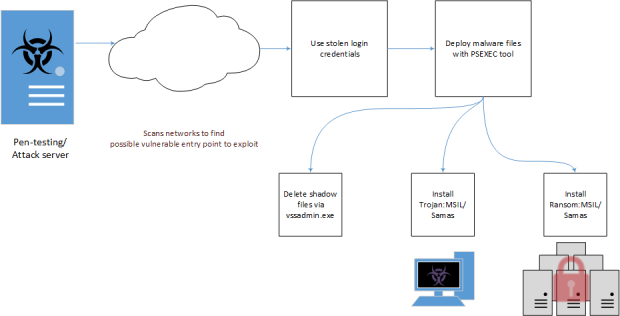 179
179Why malware like the Samsam ransomware are so dangerous for hospitals?
The FBI issued a confidential urgent “Flash” message to the businesses and organizations about the Samsam Ransomware, why it is so dangerous?...






