Malware
-
 279
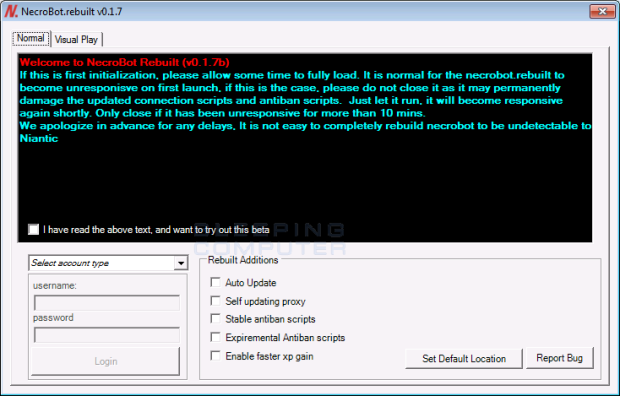
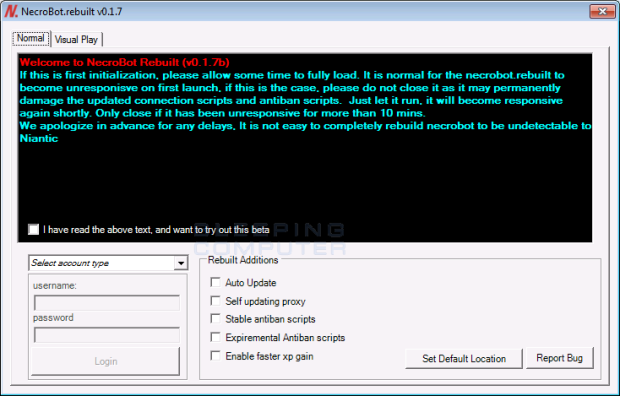
279The Nullbyte Ransomware pretends to be the NecroBot Pokemon Go Application
A new DetoxCrypto Ransomware variant called the Nullbyte Ransomware has been discovered by Emsisoft security researched xXToffeeXx that pretends to be the popular Pokemon Go bot application...
-
 78
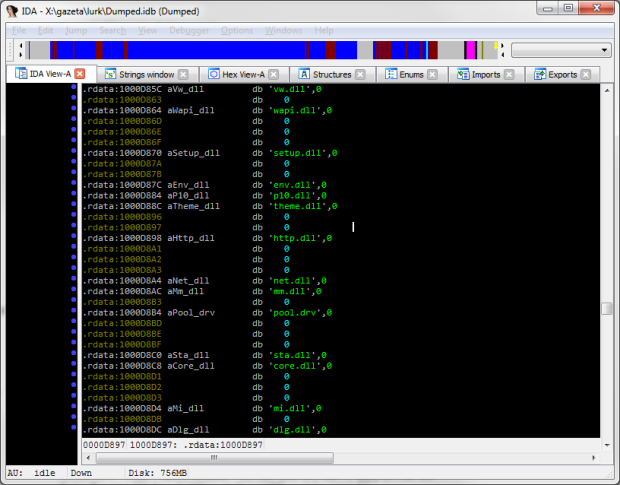
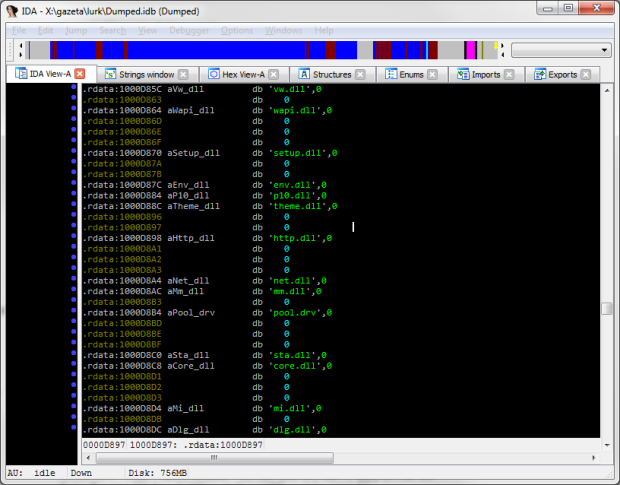
78The Hunt for Lurk
When we first encountered Lurk, in 2011, it was a nameless Trojan. It all started when we became aware of a number...
-

 171
171RIPPER ATM MALWARE AND THE 12 MILLION BAHT JACKPOT
In this blog, FireEye Labs dissects this new ATM malware that we have dubbed RIPPER (due to the project name “ATMRIPPER” identified in...
-
 75
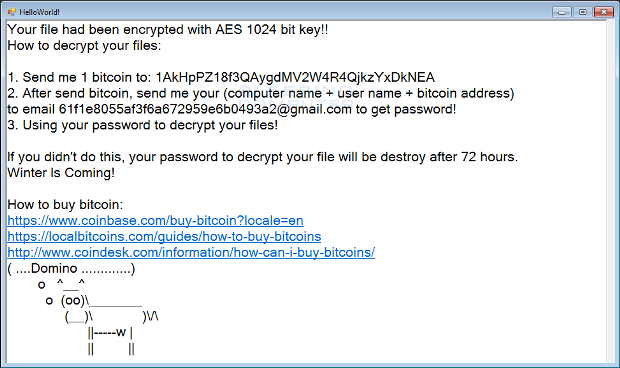
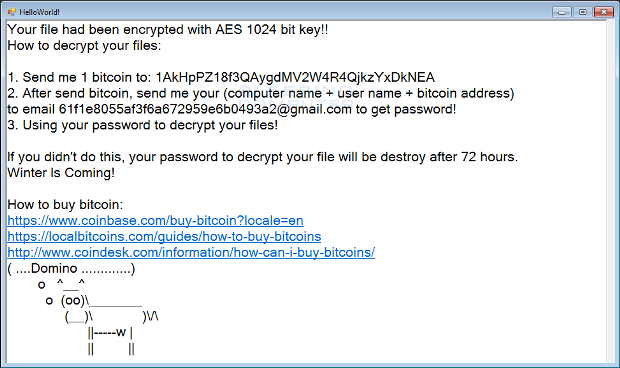
75The curious case of the Domino Ransomware, a Windows Crack, and a Cow
The Domino Ransomware is a new infection discovered by Daniel Gallagher and Michael Gillespie that is based off of the Hidden Tear open-source ransomware project. What...
-
 102
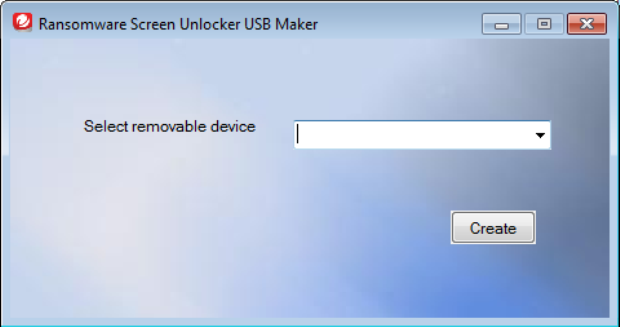
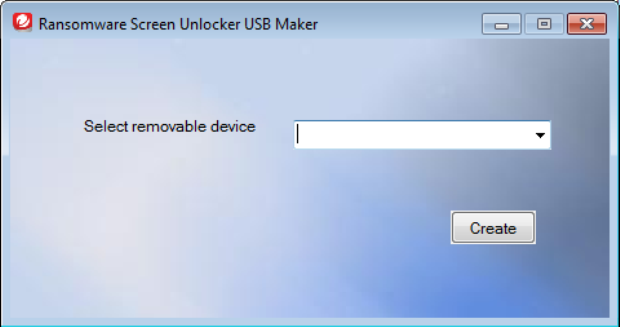
102Restore access to your PC with Trend Micro Ransomware Screen Unlocker
With so much attention focused on the file encrypting-type ransomware it’s easy to forget the simpler variety, which pops up when your...
-

 169
169Brazilian banking Trojans meet PowerShell
Crooks are always creating new ways to improve the malware they use to target bank accounts, and now Brazilian bad guys have...
-

 63
63Malware Infected All Eddie Bauer Stores in U.S., Canada
Clothing store chain Eddie Bauer said today it has detected and removed malicious software from point-of-sale systems at all of its 350+ stores...
-
 170
170New FSociety Ransomware pays homage to Mr. Robot
Crooks hijack the FSociety brand for a lame ransomware. Fans of the Mr. Robot TV show would be glad to know that real-life...
-

 344
344Nemucod serves nasty package: Ransomware and ad‑clickers
The operators of the notorious trojan downloader Nemucod seem to have stepped up their game, serving their victims with ransomware and ad-clickers.
-
 215
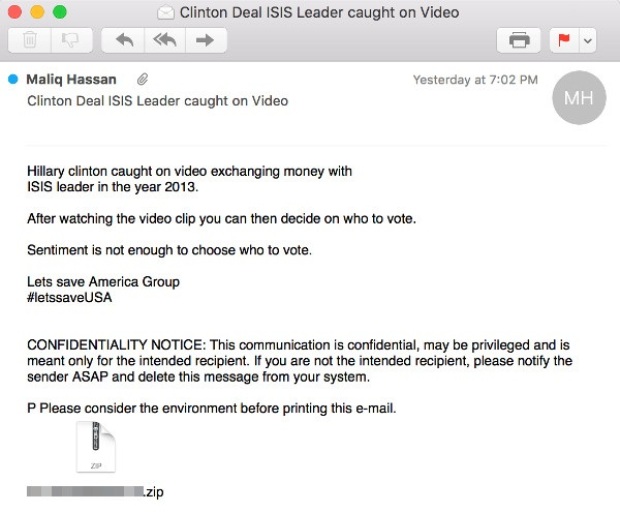
215Non-existent video involving Hillary Clinton and ISIS leader used as bait in malicious spam
Malicious attachment contains Adwind cross-platform remote access Trojan. Cybercriminals are using clickbait, promising a video showing Democratic Party presidential nominee Hillary Clinton exchanging...
-

 83
83Nemucod now spreading banking trojans in Brazil
On the morning of Friday August 12th, ESET researchers noticed a huge outbreak of a new Spy.Banker variant, detected as Spy.Banker.ADEA. It...
-
 81
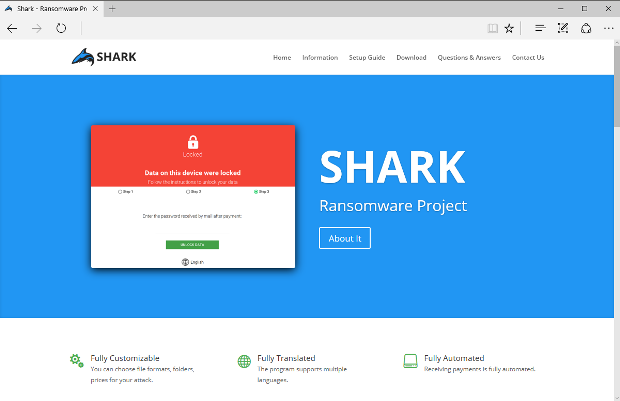
81Scammy-Looking Shark Project Delivers Fully Working Ransomware
New free ransomware project appears online. Hooray!!! Serbian security researcher GrujaRS shared with Softpedia a ransomware project called Shark, freely distributed on the...
-
 271
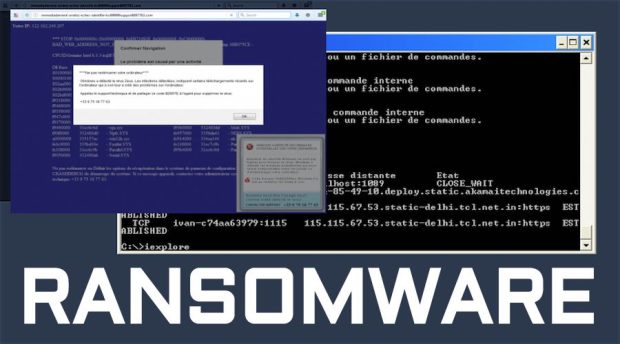
271Guy Tricks Windows Tech Support Scammers Into Installing Ransomware Code
Short Bytes: A man named Ivan Kwiatkowski managed to install Locky ransomware on the machine of a person who was pretending to...
-

 70
70QuadRooter: Unfortunately, you can’t have it patched for now
ESET researchers have spotted fake patch apps for Android – probably the first ever malicious mobile apps masquerading as a patch for...
-
 175
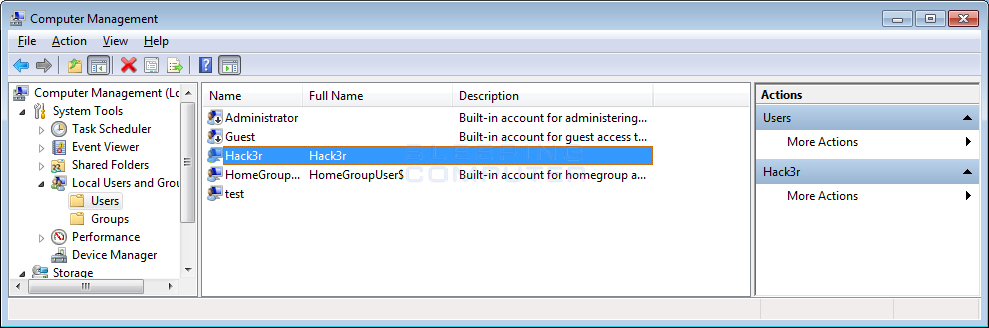
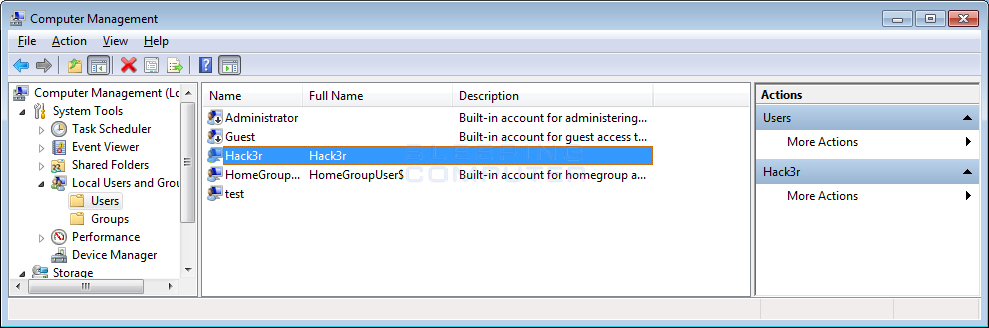
175PokemonGo Ransomware installs Backdoor Account and Spreads to other Drives
With the popularity of PokemonGo, it was inevitable that a malware developer would create a ransomware that impersonates it. This is the case...
-
 177
177CryptFile2 Ransomware Returns in High Volume URL Campaigns
Proofpoint researchers originally discovered the CryptFIle2 ransomware in March [1]. At the time, it was spreading via exploit kits (EKs); however, beginning...
-

 163
163Bungling Microsoft singlehandedly proves that golden backdoor keys are a terrible idea
Redmond races to revoke Secure Boot debug policy. Microsoft leaked the golden keys that unlock Windows-powered tablets, phones and other devices sealed by...
-

 182
182Researchers Hide Malware Inside Digitally-Signed Files Without Breaking Hashes
New technique makes malware detection almost impossible. A team of security researchers from Deep Instinct have discovered a method of injecting malware inside...
-
 82
82Nemucod is back and serving an ad-clicking backdoor instead of ransomware
The trojan downloader Nemucod is back with a new campaign. This time however, it has changed the payload served to its victims...
-
 363
363Nemucod is back and serving an ad‑clicking backdoor instead of ransomware
The trojan downloader Nemucod is back with a new campaign. However, it has changed the payload served to its victims – ransomware...
-

 87
87Development version of the Hitler-Ransomware Discovered
It looks like file deletion is becoming a standard tactic in new ransomware applications created by less skilled ransomware developers. This is...






