Malware
-
 208
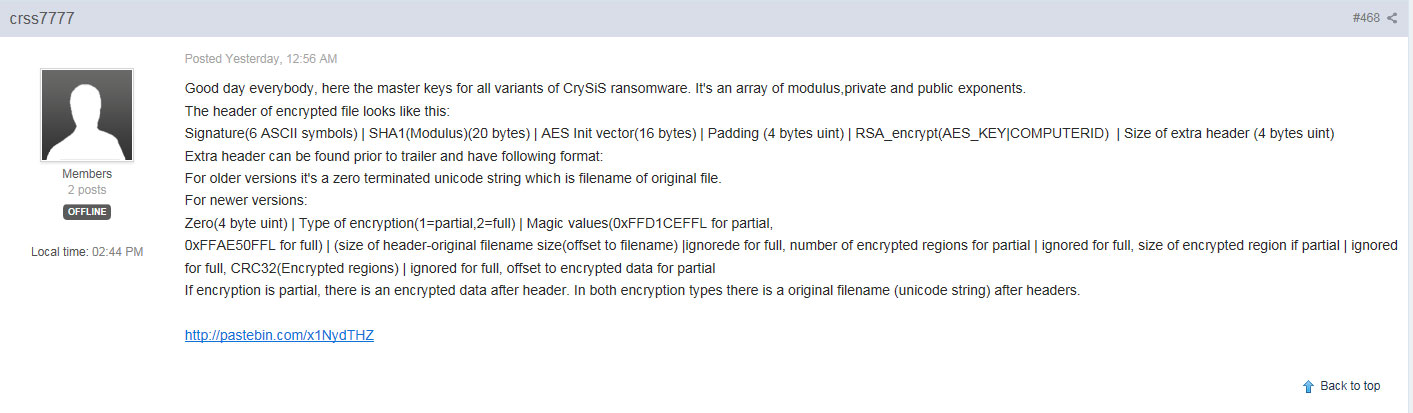
208Master Decryption Keys and Decryptor for the Crysis Ransomware Released.
In a surprise move, the master decryption keys for the CrySiS Ransomware have been released early this morning in a post on...
-

 134
134Locky ransomware campaign exploits fears of data stolen in OPM hack
Emails tell victims they need to download an attachment to view “suspicious activity” – then infects them with ransomware. In the immediate...
-

 221
221Sednit: A very digested read
This feature offers a very digested read of ESET's trilogy of research papers on Sednit, one of the most notorious groups of...
-

 114
114Tesco Bank not alone in being targeted by Retefe malware
Tesco Bank, which recently saw thousands of its customers lose funds to cybercriminals, has been found on the target list of the...
-

 313
313AVG Wants Your Home Router to Fight Internet of Things Malware
The internet of things is totally broken. Amateur hackers have managed to build huge botnets of compromised devices, and many of these...
-
 88
88How to do an APK Analysis Using AppMon
There are a great many tools available to help quickly analyze the behavior of mobile malware samples. In the case of Android,...
-

 87
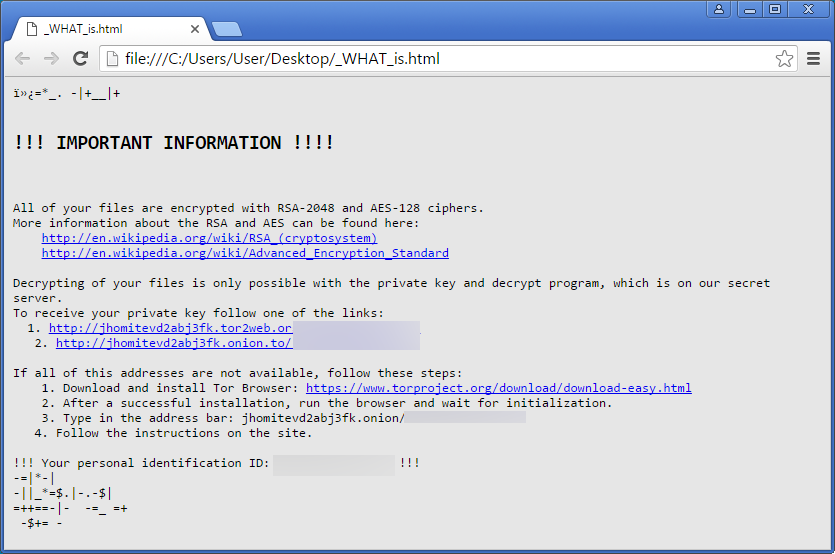
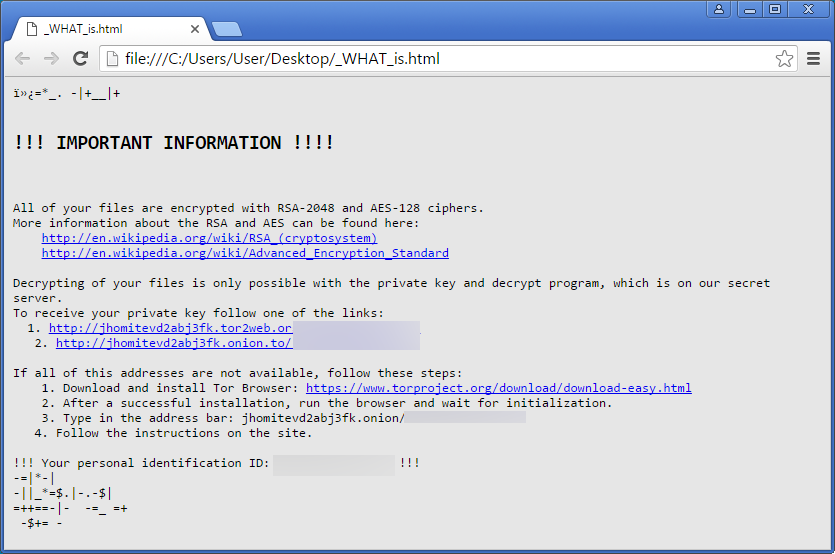
87Ransomware goes Retro with PayDOS and Serpent written as Batch Files
When it comes to ransomware, we are seeing the oddest variants being released. This is no exception with a batch file ransomware...
-
 72
72Fake Cain XPii Cleaner App Is Actually a Backdoor with Very Annoying Features
If you ask any malware analyst these days, they’ll tell you they come across countless of useless or unfinished malware variants on...
-

 235
235Flashback Tuesday: The Morris Worm
On November 2nd 1988, the Morris Worm was released, bringing the internet to an effective standstill. It was a seminal moment in...
-

 81
81Linux/Moose: Still breathing
For the past year, ESET and the security firm GoSecure combined their skills in order to research Linux/Moose further. Here's some of...
-

 190
190PHONY ANDROID FLASH PLAYER INSTALLS BANKING MALWARE
Security researchers warn that a bogus Flash Player app aimed at Android mobile devices has surfaced and is luring victims to download and install...
-

 246
246A history of mobile malware from Cabir to SMS Thief
As we continue to do more things with our smartphones, the threat posed by mobile malware increases. Here's a short history of...
-

 71
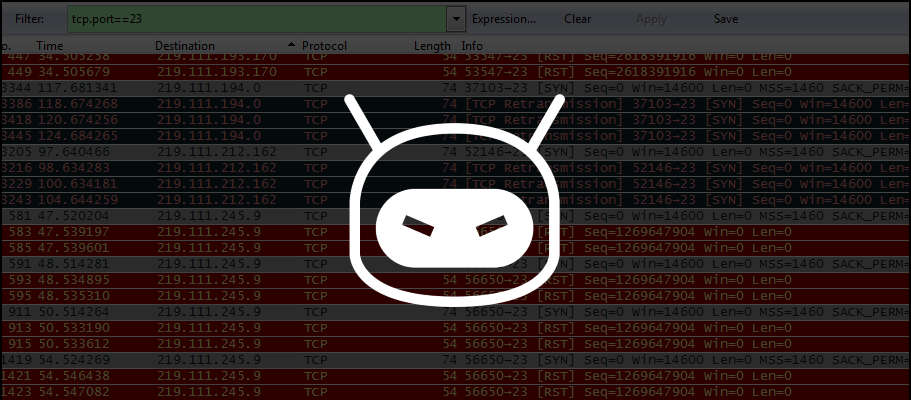
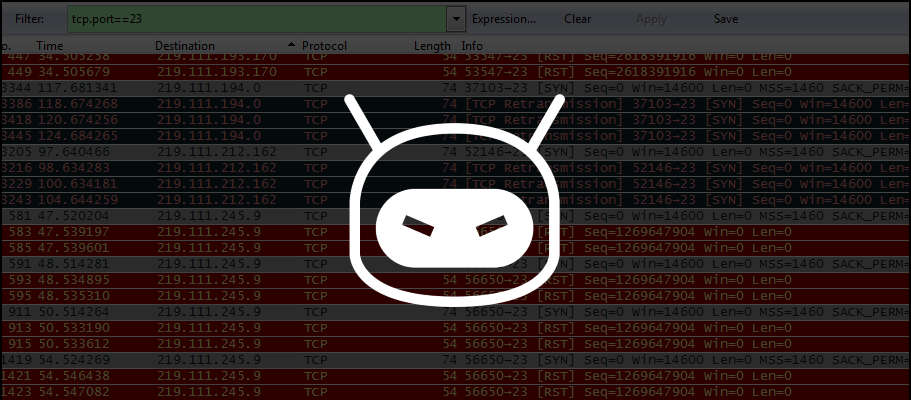
71Trick or threat? How zombie IoT devices surprised the internet
It seems the current DDoS tactics from cybercriminals is to gain control over millions of IoT devices and direct their power towards...
-
 219
219Problems Reappear for IoT Devices Owners with Discovery of New DDoS Trojan
Security researchers discovers IRCTelnet malware. A new malware family written by what appears to be an experienced coder is aiming for Linux-based...
-

 95
95The Super-Dangerous Rex Botnet Has Only Around 150 Bots
Rex incorporates some features from the Mirai malware. The Rex Linux malware is not as widespread and efficient as initially thought, and...
-

 89
89Wannabe Hackers Are Adding ‘Terrible’ and ‘Stupid’ Features to Mirai
In early October, a hacker named Anna-senpai published the source code of a malware created to automatically scour the internet for poorly...
-

 75
75Trick Bot – Dyreza’s successor
Recently, our analyst Jérôme Segura captured an interesting payload in the wild. It turned out to be a new bot, that, at...
-

 134
134Middle Eastern hackers are using this phishing technique to infect political targets with Trojan malware
‘Moonlight’ group is likely to be involved in cyberespionage, warns Vectra Networks. A hacking group is conducting cyberespionage against targets in the...
-

 232
232Lifting the lid on Sednit: A closer look at the software it uses
ESET's threat analysts have taken a closer look at the software used by Sednit to spy on its targets and steal confidential...
-
 170
170Locky Ransomware’s new .SHIT Extension shows that you can’t Polish a Turd
To further show how ransomware is such a pile of crap, a new version of Locky has been released that appends the .shit extension on encrypted files....
-

 232
232New ESET research paper puts Sednit under the microscope
Security researchers at ESET have released their latest research into the notorious and highly experienced Sednit cyberespionage group.






