Malware
-

 137
137Department of Defense Warns Contractors About Iran-Linked Malware
Shamoon, a piece of malware that tries to turn infected computers into unusable bricks, is back. Earlier this month, a number of...
-

 193
193Tordow Android Trojan Roots Devices, Steals Photos, Contacts, Chrome Database
Comodo security researchers have spotted version 2.0 of a deadly Android trojan named Tordow, which first came to light in February this...
-
 206
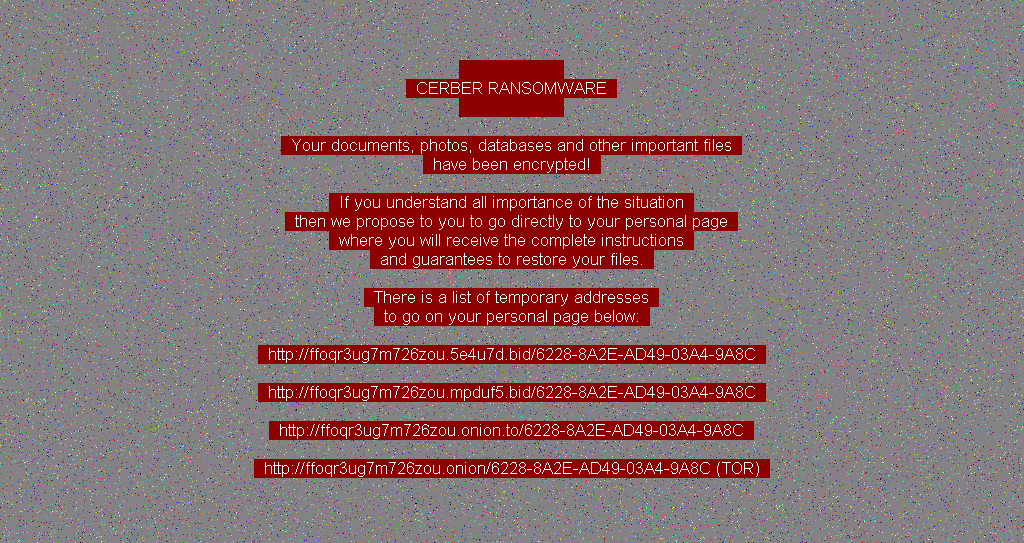
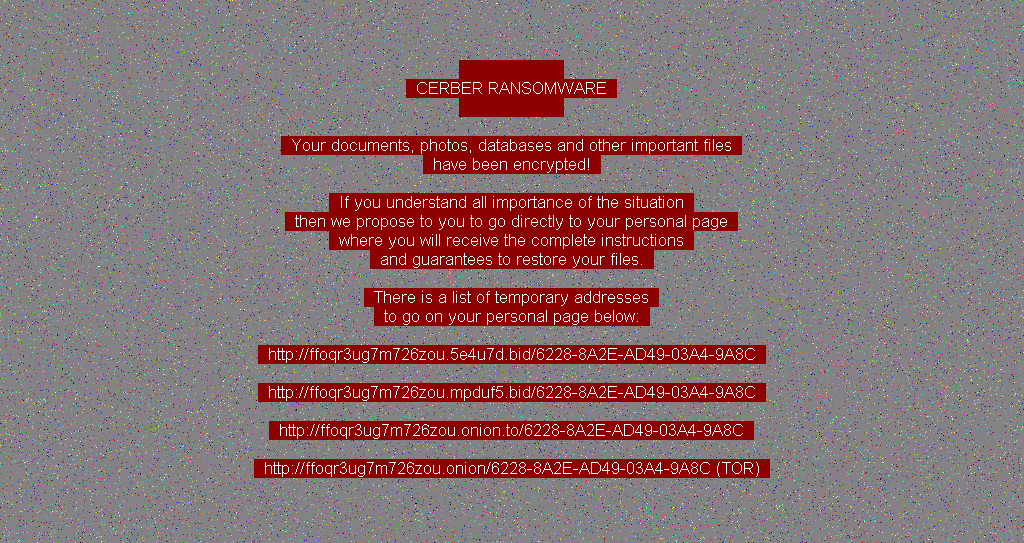
206Cerber Ransomware Spreads via Fake Credit Card Email Reports
Just in time for the Christmas holiday shopping spree, the group behind the Cerber ransomware has launched a spam campaign that uses...
-

 210
210Affordable Android Phones Coming with Malware Injected in Stock Firmware
Security firm warns of Trojans shipping with stock firmware. Russian security company Dr. Web, who also makes a PC antivirus solution bearing the...
-

 112
112Loki Trojan Infects Android Libraries and System Process to Get Root Privileges
Malware authors have released a new version of the Android Loki trojan, which can now infect native Android OS libraries after an...
-

 156
156Microsoft PowerShell Becomes a More Popular Malware-Spreading Tool
Symantec warns of growing number of malicious scripts. Microsoft PowerShell is a really powerful tool for IT professionals running Windows, and the...
-

 159
159North Korea suspected in hack of South Korea’s cyber command
North Korea appears to have hacked South Korea’s cyber command in what could be the latest cyberattack against Seoul, the military here...
-
 108
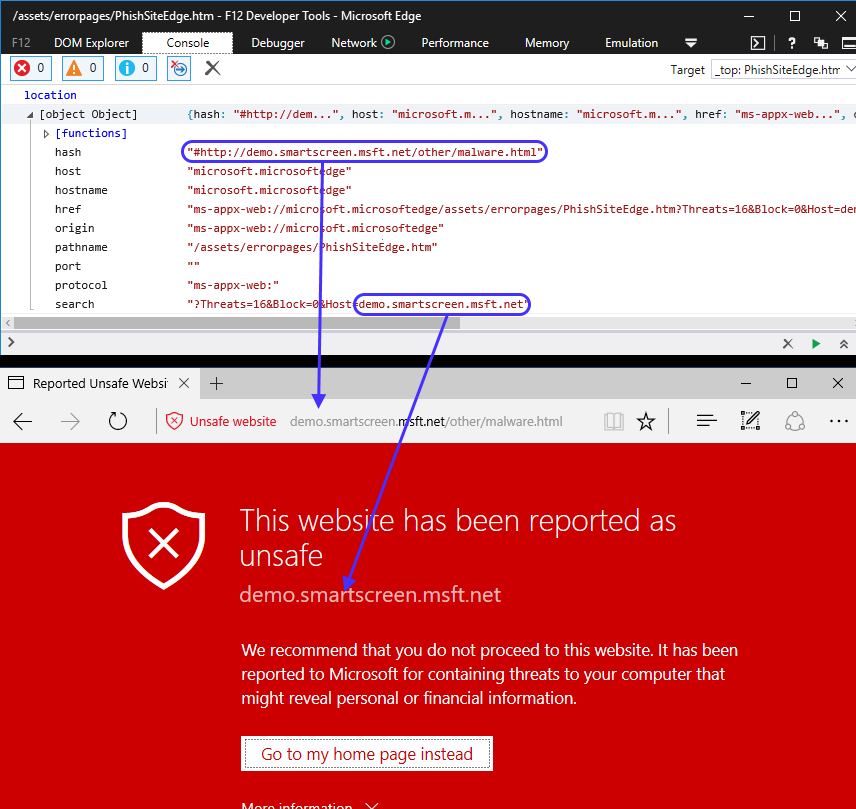
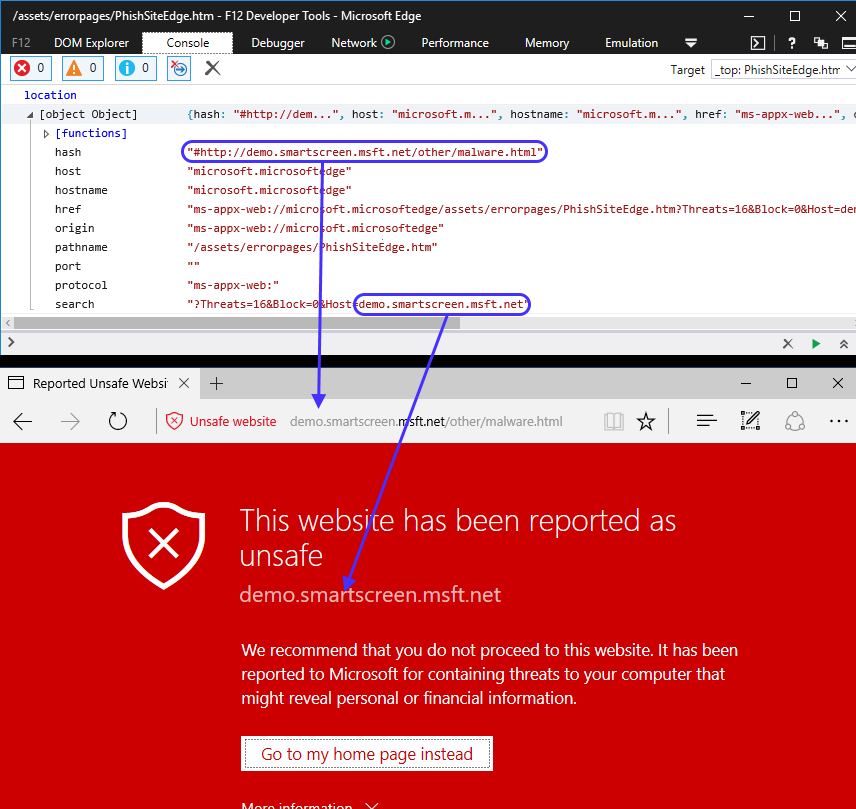
108Spoofing the Address Bar with the Malware Warning
Over the last few months, we’ve seen a proliferation of these tech-support scams where users end up “locked” in their browsers with...
-

 159
159Millions exposed to malvertising that hid attack code in banner pixels
Manipulated images are almost impossible to detect by the untrained eye. Millions of people visiting mainstream websites over the past two months...
-
 185
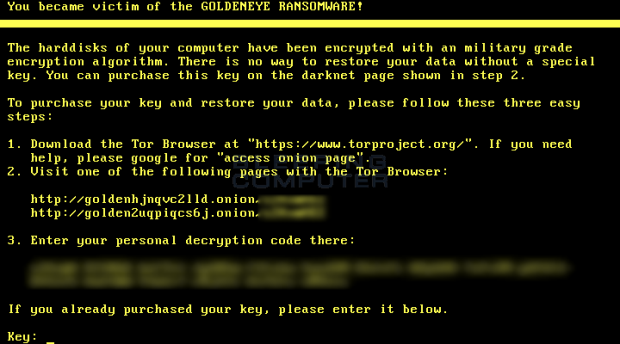
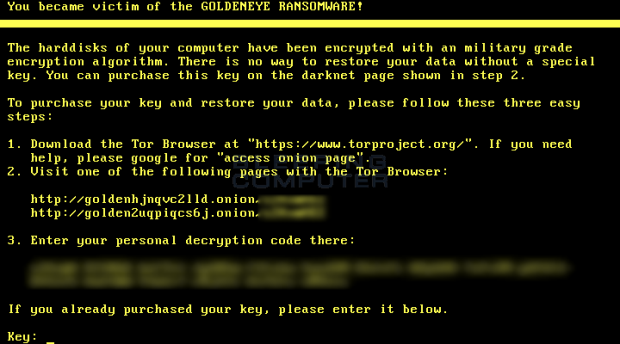
185Petya Ransomware Returns with GoldenEye Version, Continuing James Bond Theme
The author of the Petya-Mischa ransomware combo has returned with a new version that uses the name GoldenEye Ransomware, continuing the malware’s...
-

 129
129Five new malware programs are discovered every second
A new report from the respected independent testing agency AV-Test.org reveals some scary-sounding facts about the state of malware today. According to...
-

 176
176Canadian Government Is Asking Citizens If They Want Encryption Backdoors
The Canadian government is asking citizens for their feedback on several privacy and cyber-security topics, as part of a public consultation period...
-

 128
128Stegano exploit kit poisoning pixels
Visiting popular websites and getting infected without any interaction? ESET explains how the stealthy Stegano exploit kit, hiding in the pixels of...
-

 194
194Android Malware Uses TeamViewer Mobile App to Take Control of Remote Devices
Crooks are spreading Android malware disguised as a one-time password (OTP) generator app for banking apps that steals the user’s banking credentials...
-

 82
82Dorkbot: Life after disruption
A year after its disruption on 2nd December 2015, We Live Security looks at life after Dorkbot.
-

 69
69Avalanche malware network hit with law enforcement takedown
Symantec plays part in takedown of the Avalanche malware-hosting network. The Avalanche malware-hosting network has been dealt a severe blow following the...
-

 174
174Avalanche takedown: Check if you are safe
Earlier this week coordinated law enforcement action took down the Avalanche fast-flux network. ESET has been assisting in the cleanup.
-
 191
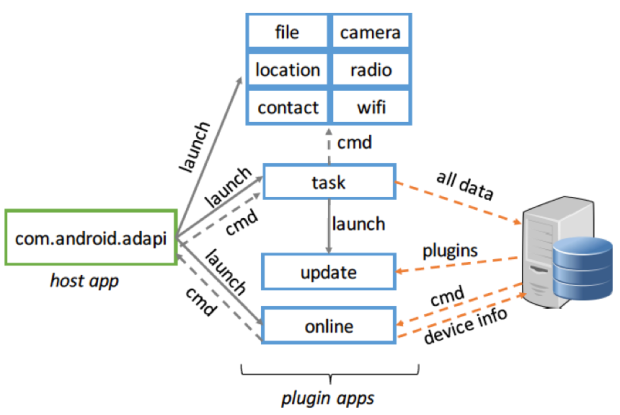
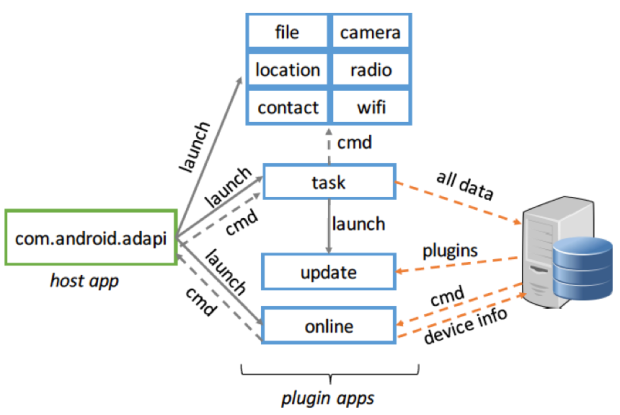
191PluginPhantom: New Android Trojan Abuses “DroidPlugin” Framework
Recently, we discovered a new Google Android Trojan named “PluginPhantom”, which steals many types of user information including: files, location data, contacts...
-

 90
90New Proteus Malware Can Mine for Crypto-Currency, Log Keystrokes, and More
A new multi-functional malware family detected as Proteus can transform the computers of infected users in proxy servers, can mine for various...
-

 66
66Hackers Are Using MailChimp to Spread Malware
You probably know MailChimp either as an email newsletter service, or the company that seems to have adverts on every single podcast...
-
 198
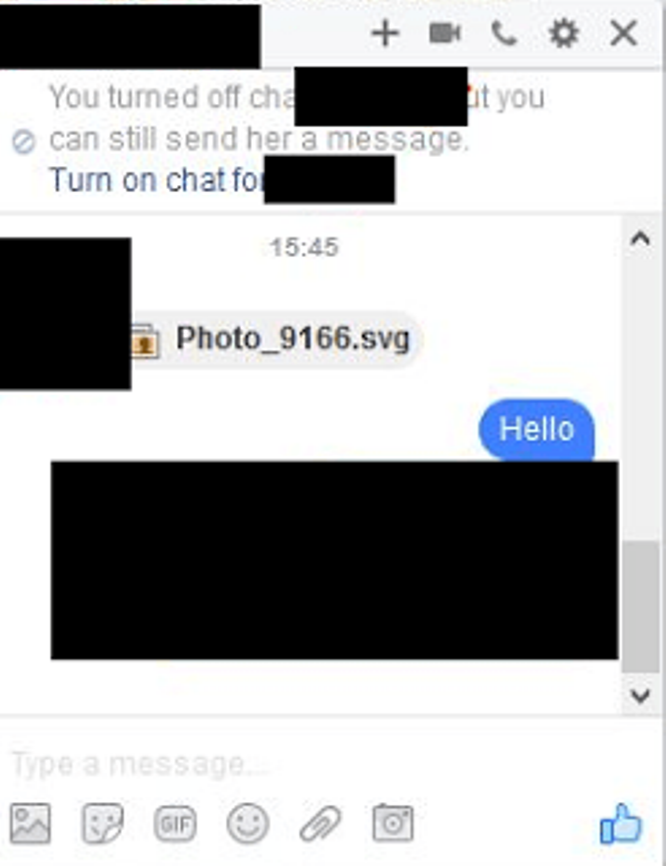
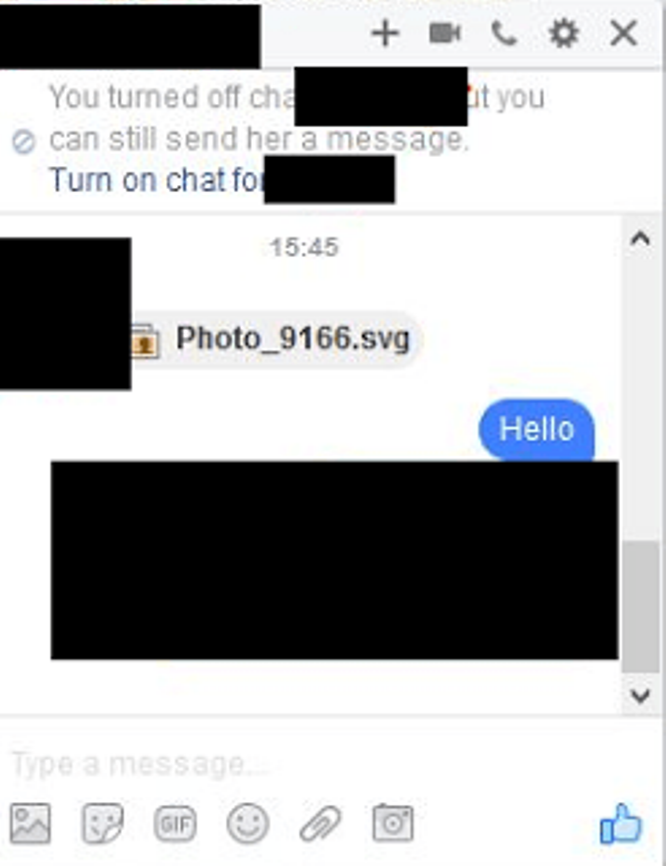
198Watch out, Locky ransomware spread via SVG images on Facebook Messenger
Researchers have discovered a new hacking campaign leveraging on Facebook Messenger to spread the Locky ransomware via SVG images. The Locky Ransomware is spread...






