Malware
-

 120
120InfoArmor Uncovers Malicious Torrent Distribution Network
InfoArmor has identified a special tool used by cybercriminals to distribute malware by packaging it with the most popular torrent files on...
-

 81
81Ransomware is lucrative: Attacker’s profits near $100 million
Hackers are increasingly targeting healthcare institutions with malware because of their poor cyber-security posture, reliance on legacy IT systems, third-party services and...
-

 81
81HDDCryptor Ransomware Overwrites Your MBR Using Open Source Tools
HDDCryptor, sometimes spelled HDD Cryptor and also identified as Mamba, is a new ransomware variant that rewrites a computer’s MBR (Master Boot...
-
 105
105Mozilla plans fix for same malware vulnerability with Tor [updated]
Mozilla officials say they’ll release a Firefox update on Tuesday that fixes the same cross-platform, malicious code-execution vulnerability patched Friday in the...
-
 97
97PSA: DetoxCrypto Ransomware imitating Malwarebytes
Scammers will always try and imitate legitimate tools and services in an effort to trick people into harming their accounts and devices....
-

 191
191LuaBot Author Says His Malware Is “Not Harmful”
Author says he’s not interested in launching DDoS attacks. Two weeks ago, a security researcher that goes by the name of MalwareMustDie had...
-

 103
103A backdoor on Xiaomi device allows silent and remote deliver of any app
A Dutch Computer Science student discovered the presence of a backdoor that could allow an attacker to silently install any app on...
-
 148
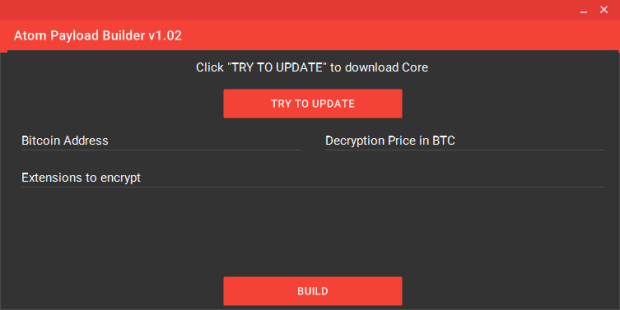
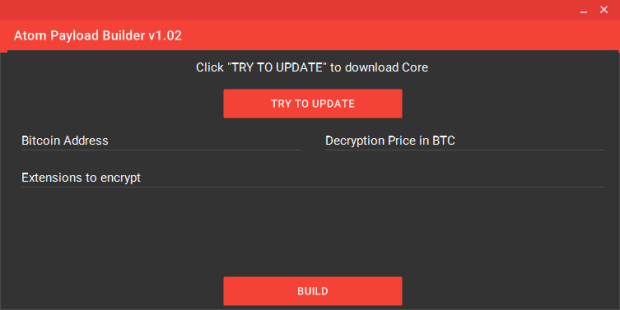
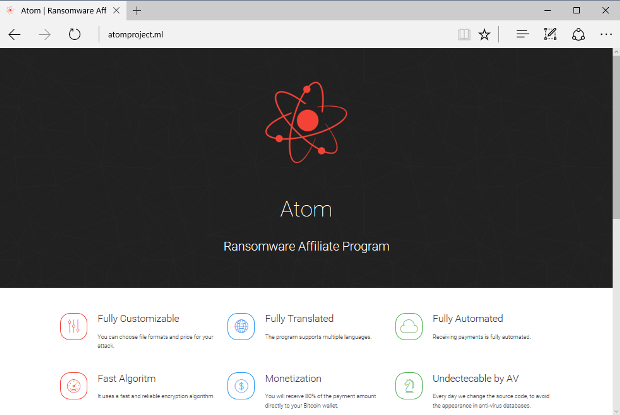
148Shark Ransomware Rebrands as Atom for a Fresh Start
The Shark Ransomware Project that appeared in July 2016 has rebranded as the Atom Ransomware Affiliate Program, offering an improved service for...
-

 116
116Recent POS malware attacks signal a need for app security for mobile payments
In the past, hackers have most often gone after specific merchants when seeking cardholder information. Recent attacks on point-of-sale (POS) vendors, however,...
-

 106
106DualToy Windows Trojan Secretly Sideloads Apps on Android and iOS Devices
Number of DualToy infections is on the rise. A trojan targeting Windows computers is secretly sideloading mobile applications to any Android or iOS...
-
 100
100Bad Press Forces Shark Ransomware Project to Rebrand
Shark Ransomware Project rebrands as Atom. The Shark Ransomware Project has recently rebranded and switched to a new domain in an attempt to...
-
 254
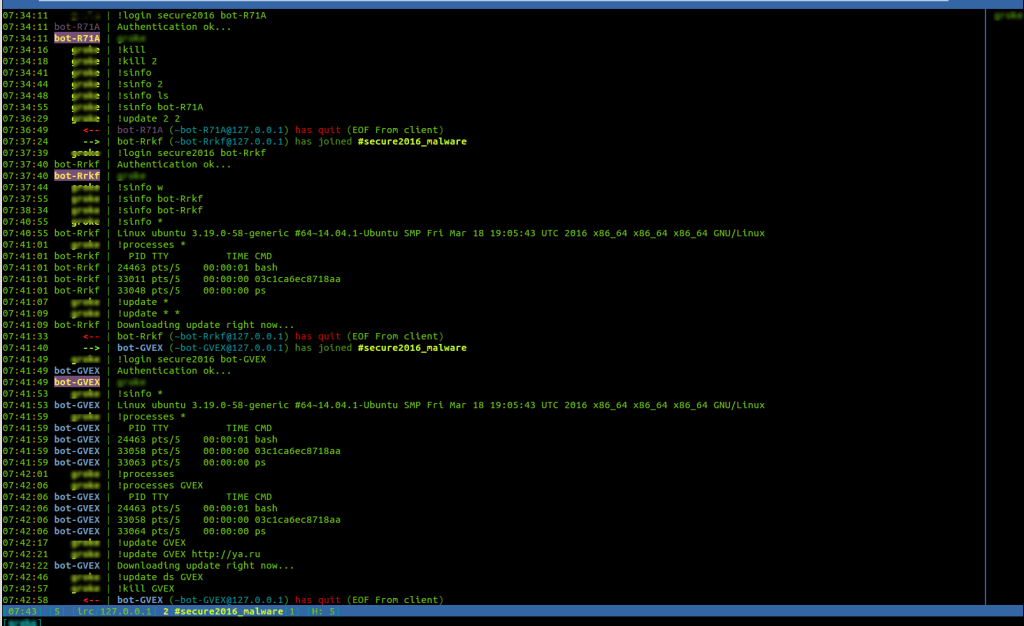
254Doctor Web discovers the first Linux Trojan that is written in Rust language
Experts from Dr Web discovered a new Linux Trojan called Linux.BackDoor.Irc.16 that is written in the Rust programming language. It is a...
-

 112
112Cryptocurrency Mining Malware Discovered Targeting Seagate NAS Hard Drives
Malware authors have made around $86,400, so far. A malware variant named Mal/Miner-C (also known as PhotoMiner) is infecting Internet-exposed Seagate Central Network...
-
 105
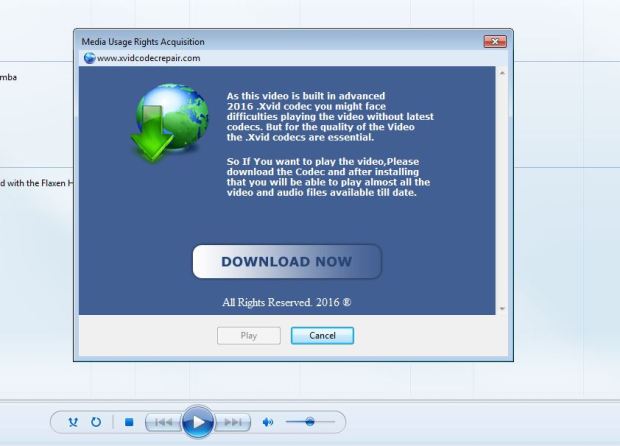
105WINDOWS MEDIA PLAYER DRM USED FOR MALWARE
Movie and TV watchers who download pirated content have long been warned of the potential for malware that might accompany their chosen...
-
 179
179Down but Not Out! Dridex Begins Targeting Crypto-Currency Wallets
The Dridex banking trojan might be involved in fewer attack campaigns, but its developers are still outfitting it with some new functionalities,...
-
 205
205Locky now using Embedded RSA Key instead of contacting Command & Control Servers
According to security researcher Timothy Davies, a new version of the Locky Ransomware, aka Zepto, has been circulating since around the September 5th 2016 that...
-

 94
94Gugi Trojan Guffaws at Android 6 Security Measures… and Then Bypasses Them
A mobile banking trojan called Trojan-Banker.AndroidOS.Gugi.c, or “Gugi” for short, found no problem bypassing a couple of the security measures introduced in...
-
 231
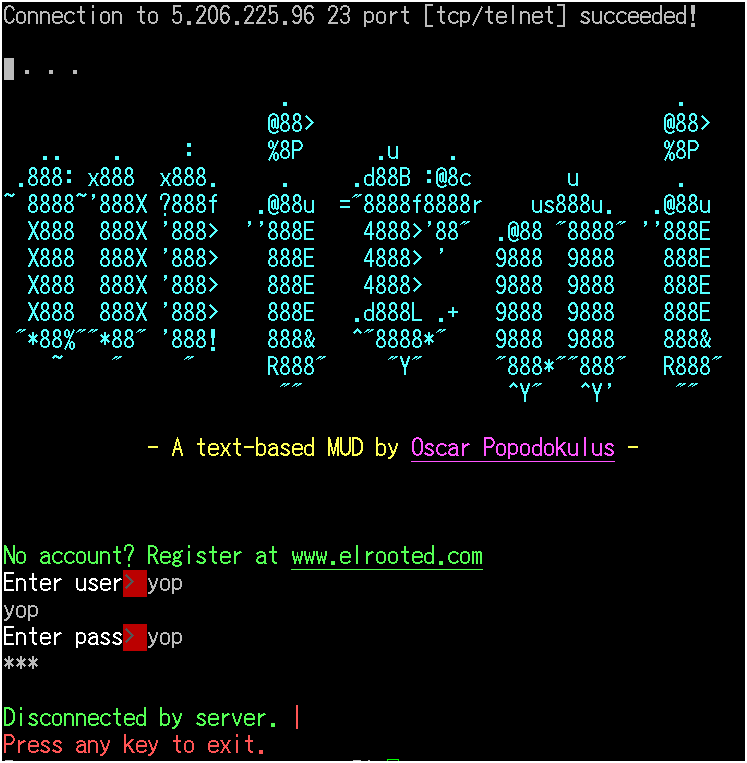
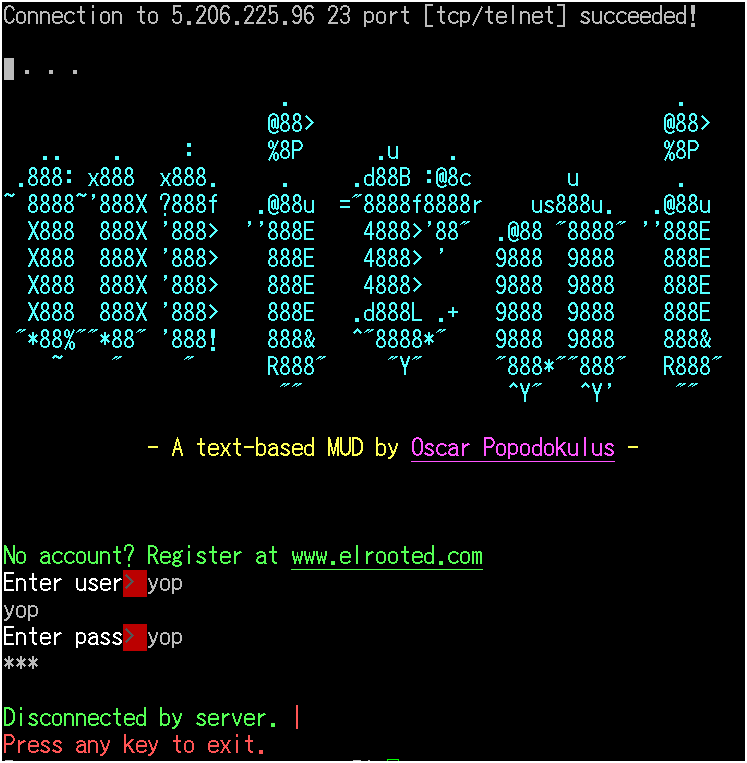
231Mirai DDoS Trojan Is the Next Big Threat for IoT Devices and Linux Servers
Mirai evolves from the source code of Gafgyt. A new trojan named Mirai has surfaced, and it’s targeting Linux servers and IoT devices,...
-

 86
86“You dirty RAT” – Spy versus Spy in the cybercrime underworld
Not all malware is ransomware, even though ransomware hogs the spotlight these days.Keyloggers are still popular in the cyberunderworld, because they help...
-
 232
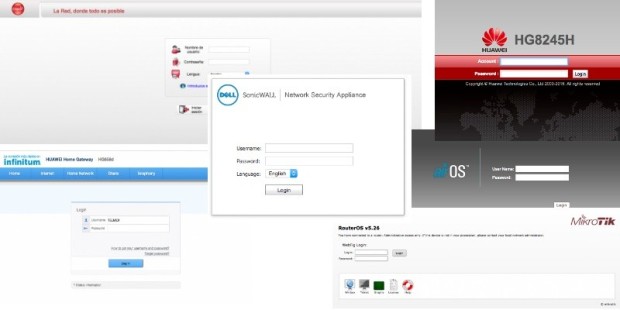
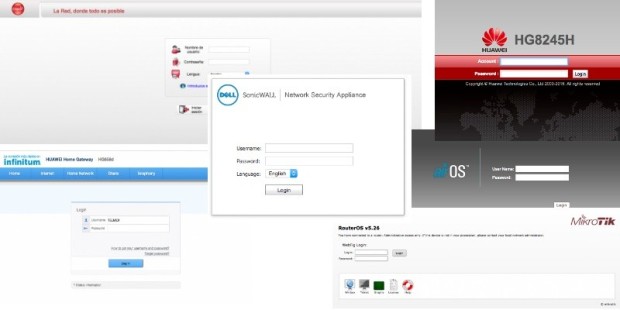
232Attackers Combine Three Botnets to Launch Massive DDoS Attack
Crooks use a botnet of CCTV cameras, one of home routers, and one made up by compromised web server. An unnamed website...
-
18 years of Googling: Malware can still be just one click away
18 years of Googling is certainly something to behold, but on this anniversary, ESET's Ondrej Kubovič is keen to highlight the cybersecurity...






