Malware
-
 412
412Winnti Hacker Group Uses New Malware to Hack Microsoft SQL Servers
Winnti hacker group uses a new malware dubbed skip-2.0 to attack Microsoft SQL Servers and to gain persistence access. Winnti group believed...
-

 547
547Chinese hackers could install backdoors on Microsoft SQL 11 and 12 servers using a “magic word”
The activities of government-sponsored hacker groups can have disastrous consequences. A group of digital forensics experts from ESET has revealed the existence...
-

 743
743Winnti Group’s skip‑2.0: A Microsoft SQL Server backdoor
Notorious cyberespionage group debases MSSQL
-

 535
535Fleecing the onion: Darknet shoppers swindled out of bitcoins via trojanized Tor Browser
ESET researchers discover a trojanized Tor Browser distributed by cybercriminals to steal bitcoins from darknet market buyers
-
 582
582Free music files on the Internet could contain malware and backdoors
Digital forensics specialists report a new attack method consisting of the use of WAV audio files to hide and deliver backdoors and...
-

 446
446Operation Ghost: The Dukes aren’t back – they never left
ESET researchers describe recent activity of the infamous espionage group, the Dukes, including three new malware families
-

 549
549ATM Jackpotting – Cutlet Maker Malware Spike Around the World to Spit the Cash From ATM
Researchers discovered a new track of ATM jackpotting attack through infamous ATM malware called “Cutlet Maker” which is now rapidly growing up...
-

 661
661Winnti Hackers Group Launching New Malware via Supply-chain Attacks to Inject Backdoor in Windows
Researchers discovered a new malware campaign from the Winnti threat group that utilizes the supply-chain attacks with a new set of artifacts to...
-

 449
449Mac devices affected by this new dangerous malware variant
A team of ethical hacking specialists from security firm Confiant has revealed the discovery of a new malware variant for Mac devices....
-

 522
522New malware variant that infects NCR ATMs software
According to digital forensics specialists, the hacker group identified as FIN7 has developed a new malicious tool, capable of delivering payloads directly...
-

 574
574Connecting the dots: Exposing the arsenal and methods of the Winnti Group
New ESET white paper released describing updates to the malware arsenal and campaigns of this group known for its supply-chain attacks
-
 613
613FIN7 APT Hackers Added New Hacking Tools in Their Malware Arsenal to Evade AV Detection
Researchers discovered 2 new hacking tools called BOOSTWRITE and RDFSNIFFER that were added in FIN7 groups malware arsenal with sophisticated capabilities and...
-

 473
473ESET discovers Attor, a spy platform with curious GSM fingerprinting
ESET researchers discover a previously unreported cyberespionage platform used in targeted attacks against diplomatic missions and governmental institutions, and privacy-concerned users
-
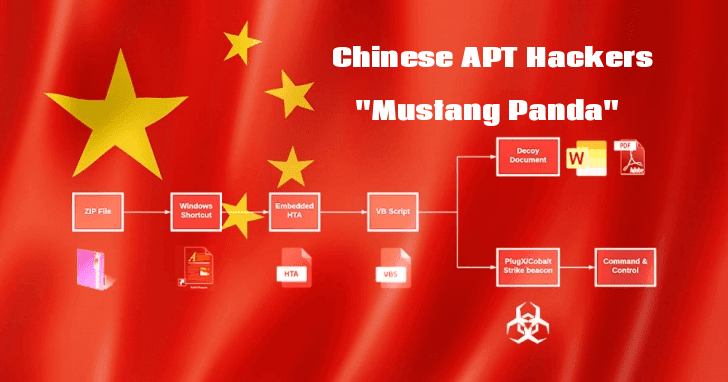
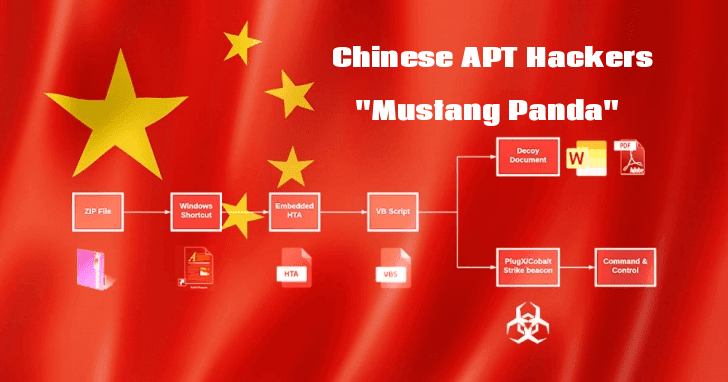 434
434Chinese APT Hackers “Mustang Panda” Attack Public & Private Sectors Using Weaponized PDF and Word Documents
Researchers discovered an ongoing malware campaign that believed to be operating by a Chinese based threat group called “Mustang Panda” that targets...
-

 519
519Paying the ransom of a cyberattack is now legal: FBI
It seems that the FBI takes an increasingly permissive stance regarding ransomware infections and ransom payments. According to digital forensics specialists, the...
-
 464
464Odix – An Enterprise-Grade File-Based Cyber Attack and Malware Protection to SMBs
Cybersecurity solutions provider odix has set its sights on bringing enterprise-grade cybersecurity to small to medium businesses (SMBs). The company specializes in...
-

 661
661Buggy Malware Attack on WordPress Websites by Exploiting Newly Discovered Theme & Plugin Vulnerabilities
Researchers discovered an ongoing buggy malware campaign that attempts to exploit the newly discovered vulnerabilities resides in the WordPress theme and plugin....
-

 474
474PKPLUG -New Research Found Same Chinese Hacking Group Involved with Multiple Cyber Attacks Across Asia
Researchers linked multiple Cyber-espionage campaigns across Asia to the threat actor group PKPLUG. The group uses its PlugX malware and the number...
-
 352
352Turla APT Hackers Using New Malware to Break The TLS Encrypted Web Traffic Communication
Turla APT threat actors distribute a new malware called Reductor, a successor of COMpfun to compromise the TLS encrypted web traffic and...
-

 400
400Ontario government had to pay hackers a $75k USD ransom
Last April information security audit specialists reported a ransomware infection in the IT systems of Stratford, a small city in Ontario region,...
-

 424
424Casbaneiro: Dangerous cooking with a secret ingredient
Número dois in our series demystifying Latin American banking trojans






