Pentest
-
 283
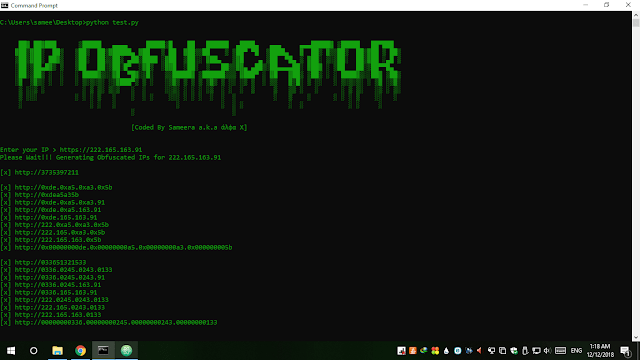
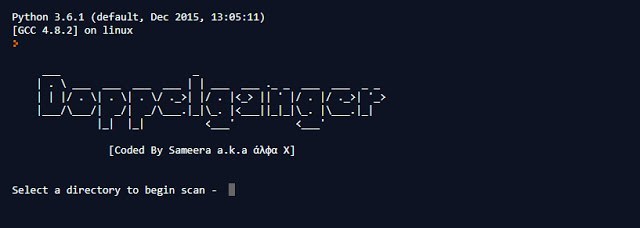
283IP Obfuscator – Simple Tool To Convert An IP Into Integer, Hexadecimal Or Octal Form
IP Obfuscator is a simple tool written in python to convert an IP into different obfuscated forms. This tool will help you...
-
 196
196Doppelganger – Python Script To Scan Duplicate Copies In A Given Directory
Doppelganger is a python script to scan duplicate copies in a given directory. This tool compare not only file names, but also...
-

 526
526W3Brute – Automatic Web Application Brute Force Attack Tool
w3brute is an open source penetration testing tool that automates attacks directly to the website’s login page. w3brute is also supported for...
-
 168
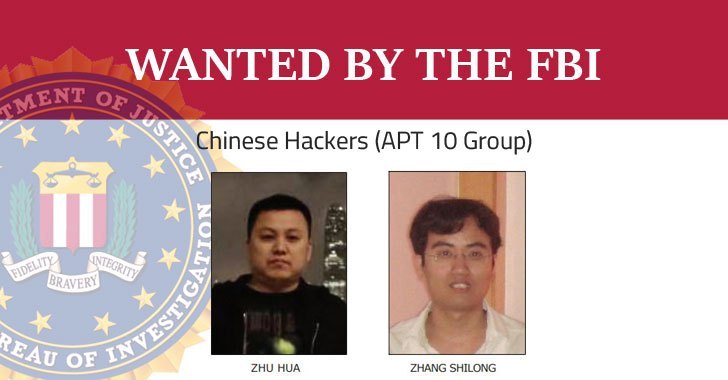
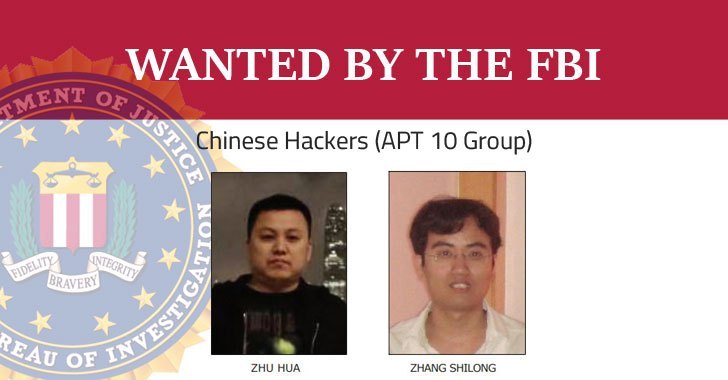
168US Indicts Two Chinese Government Hackers Over Global Hacking Campaign
The US Department of Justice on Thursday charged two Chinese hackers associated with the Chinese government for hacking numerous companies and government...
-

 196
196FBI Seizes 15 DDoS-For-Hire Websites, 3 Operators Charged
The FBI just saved the Christmas. The U.S. Justice Department announced earlier today that the FBI has seized domains of 15 “DDoS-for-hire”...
-
 166
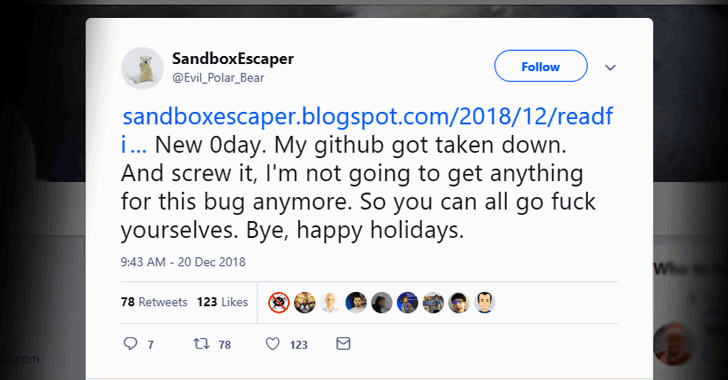
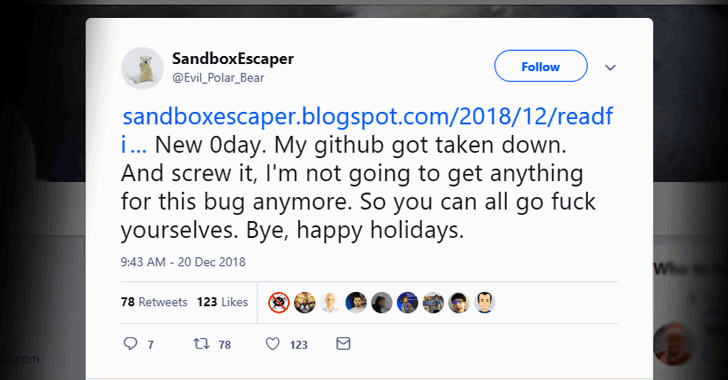
166Hacker Discloses New Unpatched Windows Zero-Day Exploit On Twitter
A security researcher with Twitter alias SandboxEscaper today released proof-of-concept (PoC) exploit for a new zero-day vulnerability affecting Microsoft’s Windows operating system....
-

 153
153Microsoft Issues Emergency Patch For Under-Attack IE Zero Day
Microsoft today issued an out-of-band security update to patch a critical zero-day vulnerability in Internet Explorer (IE) Web browser that attackers are...
-

 154
154Mayday! NASA Warns Employees of Personal Information Breach
Another day, another data breach. This time it’s the United States National Aeronautics and Space Administration (NASA) NASA today confirmed a data...
-

 191
191New Malware Takes Commands From Memes Posted On Twitter
Security researchers have discovered yet another example of how cybercriminals disguise their malware activities as regular traffic by using legitimate cloud-based services....
-

 173
173Twitter Discloses Suspected State-Sponsored Attack After Minor Data Breach
Twitter has been hit with a minor data breach incident that the social networking site believes linked to a suspected state-sponsored attack....
-
 263
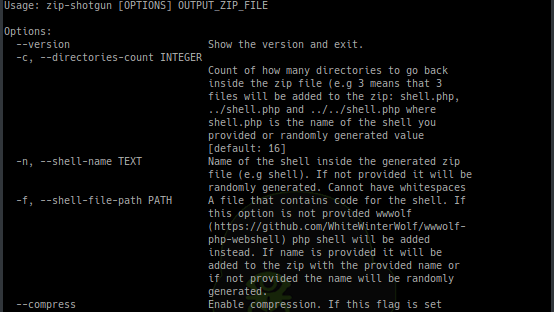
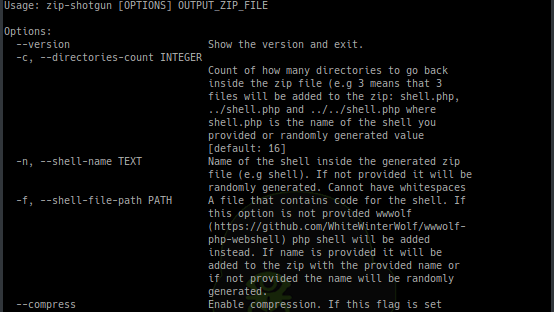
263ZIP Shotgun – Utility Script To Test Zip File Upload Functionality For Vulnerabilities
Utility script to test zip file upload functionality (and possible extraction of zip files) for vulnerabilities. Idea for this script comes from...
-
 273
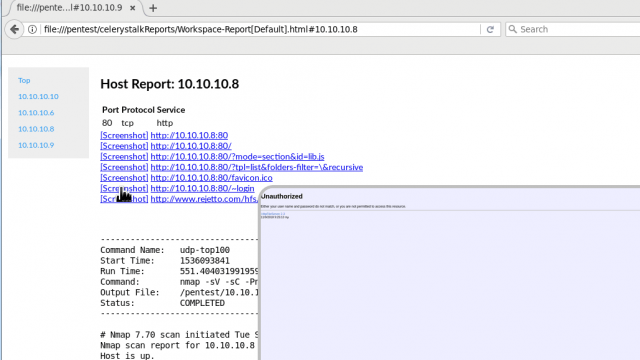
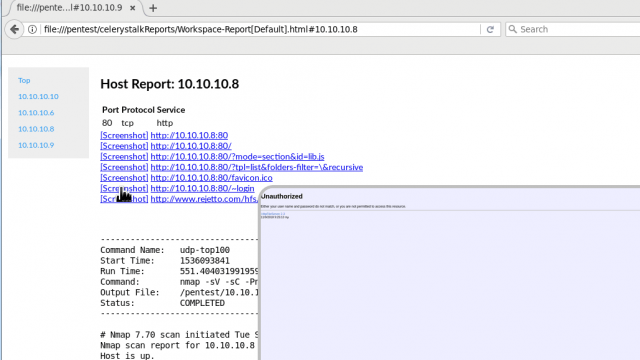
273Celerystalk – An Asynchronous Enumeration and Vulnerability Scanner
celerystalk helps you automate your network scanning/enumeration process with asynchronous jobs (aka tasks) while retaining full control of which tools you want...
-

 156
156Critical SQLite Flaw Leaves Millions of Apps Vulnerable to Hackers
Cybersecurity researchers have discovered a critical vulnerability in widely used SQLite database software that exposes billions of deployments to hackers. Dubbed as...
-

 159
159New Shamoon Malware Variant Targets Italian Oil and Gas Company
Shamoon is back… one of the most destructive malware families that caused damage to Saudi Arabia’s largest oil producer in 2012 and...
-
 311
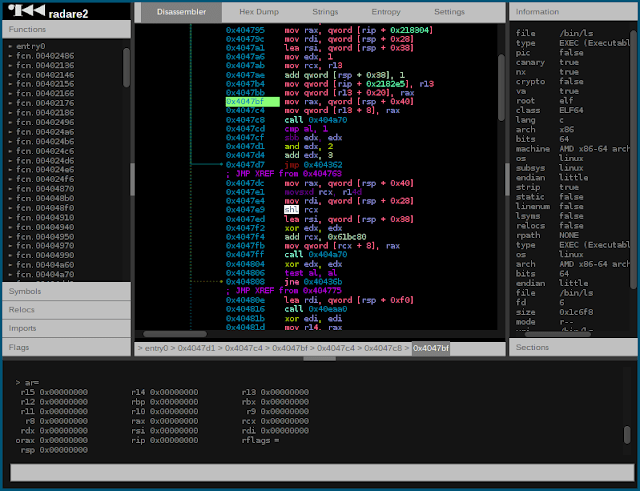
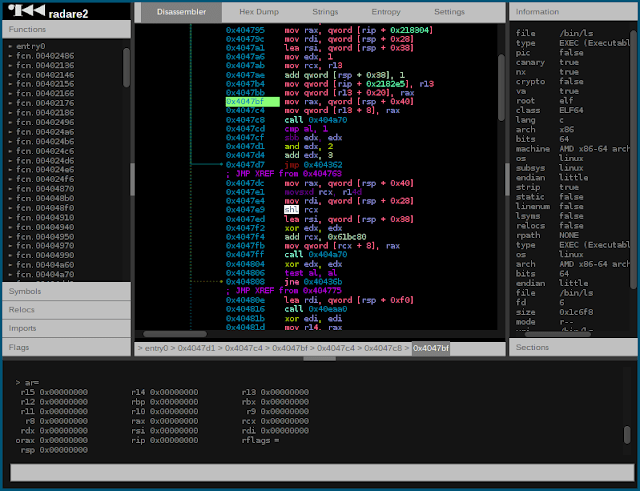
311Radare2 – Unix-Like Reverse Engineering Framework And Commandline Tools Security
r2 is a rewrite from scratch of radare in order to provide a set of libraries and tools to work with...
-
 305
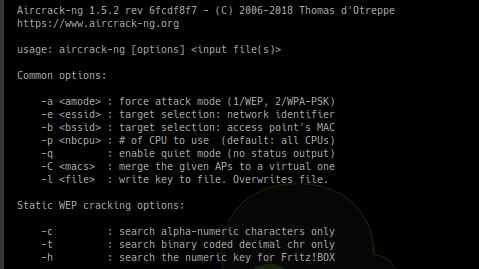
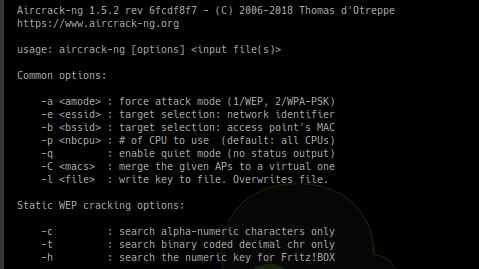
305Aircrack-ng 1.5 – Complete Suite Of Tools To Assess WiFi Network Security
Aircrack-ng is a complete suite of tools to assess WiFi network security. It focuses on different areas of WiFi security: Monitoring: Packet...
-

 175
175New Facebook Bug Exposed 6.8 Million Users Photos to Third-Party Apps
Facebook’s latest screw-up — a programming bug in Facebook website accidentally gave 1,500 third-party apps access to the unposted Facebook photos of...
-
 261
261NETworkManager – A Powerful Tool For Managing Networks And Troubleshoot Network Problems!
A powerful tool for managing networks and troubleshoot network problems! Features Network Interface – Information, Configure IP-Scanner Port-Scanner Ping Traceroute DNS Lookup...
-
 191
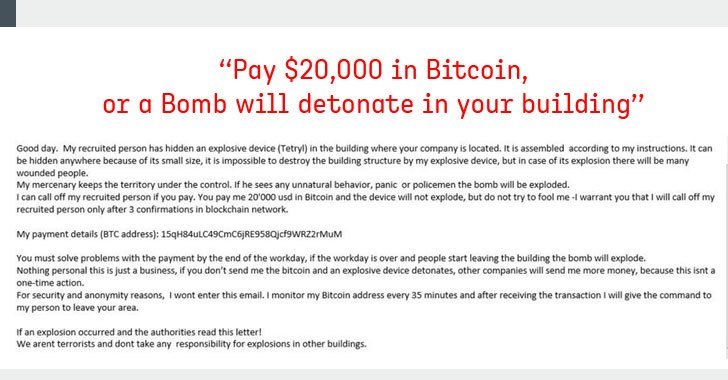
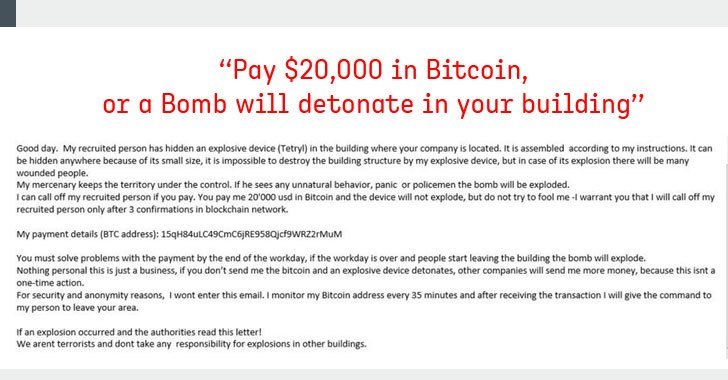
191Fake Bomb Threat Emails Demanding Bitcoins Sparked Chaos Across US, Canada
“Pay $20,000 worth of bitcoin, or a bomb will detonate in your building” A massive number of businesses, schools, government offices and...
-
 297
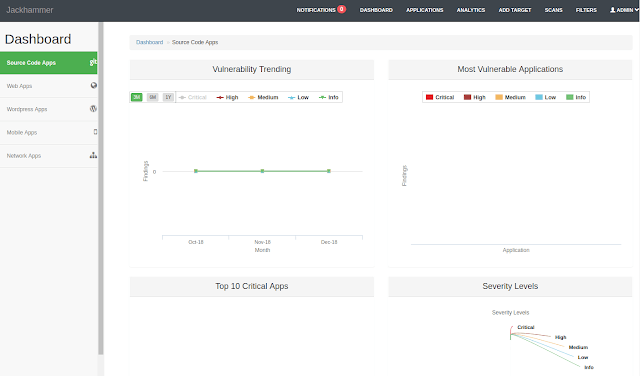
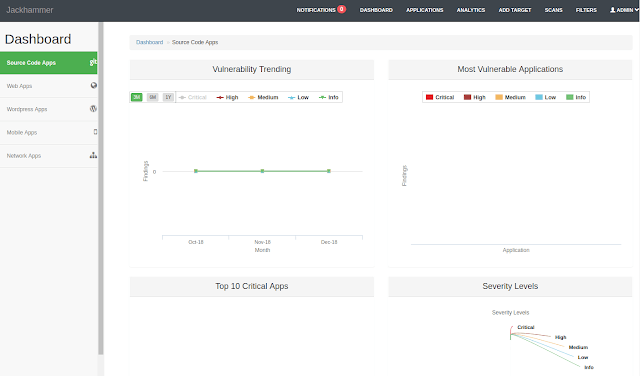
297Jackhammer – One Security Vulnerability Assessment/Management Tool To Solve All The Security Team Problems
One Security vulnerability assessment/management tool to solve all the security team problems. What is Jackhammer? Jackhammer is a collaboration tool built with...
-
 230
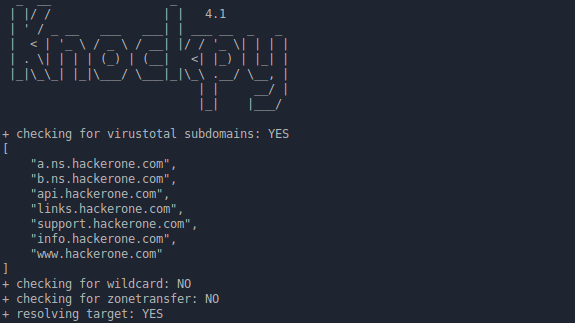
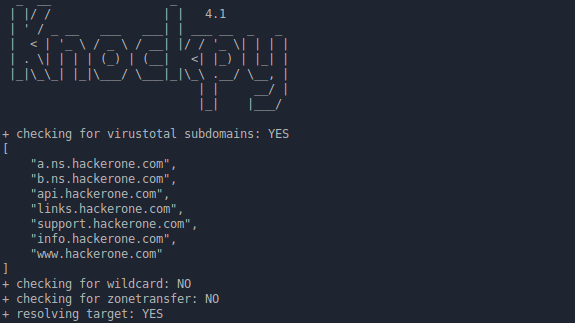
230Knock v.4.1.1 – Subdomain Scan
Knockpy is a python tool designed to enumerate subdomains on a target domain through a wordlist. It is designed to scan for...






